| 07/13/2019 |
OISF 2019
Videos
These are the videos from the
OISF Anniversary Event
Introduction
Dr. John Carls/Paul Hankins
UBoot to Root
Deral Heiland
A Discussion of Secrets
Robert Stewart
Continuous Skills Improvement For Everyone
Matt Scheurer
DLP Demystified
Micah Brown
Pixel Tracking: How it�s used and abused
Barry Kimball |
| 06/22/2019 |
BSides Cleveland 2019 Videos
These are
the videos from the Bsides Cleveland
conference. Thanks to Rich, ninewires,
justinschmitt &
as the video team. Thanks to
twuntymcslore &
RockieBrockway for being con
mom & dad.
Keynote
David Kennedy
Operationalizing the MITRE ATT&CK Framework
Robert Olson
Markets for Malware
Adam Hogan
The TIP of the Stinger: Efficiently Using Threat Intelligence With TheHive
Matthew Gracie
Calls to Arms: US Elections Hacking
Damian Huising
The Overlooked Cyber-Security Risk: 3rd Party Risk Management
Rose Songer
The Politics of Cyber
Ian Thornton-Trump
Unix: the Other White Meat
Adam Len Compton & David Boyd
Hack for Show, Report for Dough
Brian King
Early Detection through Deception
Jason Nester
Eval Villain: Simplifying DOM XSS and JS Reversing
Dennis Goodlett
(Most Audio Missing)
Securing the DOM from the Bottom Up
Mike Samuel
(Missing Most Audio)
Data Access Rights Exploits under New Privacy Laws
Amber Welch
Public Partnership Panel for Security Response
Jeremy Mio and Others
Automating Windows Kernel Analysis With Symbolic Execution
Spencer McIntyre
Incident response on macOS
Thomas Reed
Getting youth interested in infosec from a youth's perspective.
Tristan Messner
Keynote
Joshua Corman
(Not Recorded) |
| 06/15/2019 |
ShowMeCon 2019 Videos
These are the videos ShowMeCon 2019.
Thanks to Renee & Dave Chronister (@bagomojo)
and others for having me out to record and speak. Also thanks to my video crew
@r3tr0_cod3x, James, Aaron, Jon,
@AlexTShell,
@Mayer302,
@MatthewRekos and some other
people I may have forgotten.
Welcome
A Practical Approach to Purple Teaming
Matt Thelen
Some assembly required, instructions not included
Dave Chronister
The Dark Side of Physical Access Control Systems
Valerie Thomas
The Art of Cyberwar: A Foundation and Framework for the Development of TTPs
Kevin L. Johnson
Human Centered Design and You: Hack Your Life
Hudson Harris
The rising geopolitical cyber power
Kurt Aubuchon
Cracking the Code - Hacking the Human Mind
Scott Holman
Confessions of Really Bad SysAdmins
Andy Thompson
Sync Your Sh*t: Why it's time you paid attention to time
John Clark
How to screw up your Incident Response investigation in 10 steps or less
Vadon Willis
Control of Unclassified Information in Non-Federal IT Systems - Or What You
Don't Know Can Cost You
Tim Grace
Why should your employees know how to phish
Mike Morris
Redesigning Password Authentication for the Modern Web
Cliff Smith
Penetration Testing: The Good, Bad, and the Ugly of Vendor Management, Reporting
and Risk Management (or lack thereof)
Justin L. Bauman
Why your red team shouldn't be snowflakes
Isaiah Sarju
0Day to HeroDay: Bringing a company from scorched earth to a modern security
organization
Ryan Wisniewski
The Great Explainer: Feynman and Standing on the Shoulders of Giants
Kevin Johnson
TLSv1.3: Minor Version, Major Changes
John Wagnon
I PWN thee, I PWN thee not!
Jayson Street
|
| 06/02/2019 |
Circle City Con 2019 Videos
These are the Circle City Con videos.
Thanks to the staff for inviting me
down to record. Big thanks to @irishjack,
@TheHomoHacker,
@Paint27,
@songsthatsaved,
@nogoodrobot,
@kitwessendorf,
@cxstephens,
@uncrustabl3 and others for helping set up AV and record.
Opening
Data Access Rights Exploits under New Privacy Laws
Amber Welch
How to reach and teach youth about Cybersecurity (if anybody will let you)
Jason Smith
More Tales from the Crypt...Analyst
Jeff Man
Could Static Code Analysis and Secure Coding have Saved the Death Star?
Mary Waddick
I�ll Complete My Threat Model Later Mom!: Infosec in Middle School.
Ashley Benitez Smith
Cons & Careers
Steven Bernstein
3D printing canister-launchable drones for city-scale wardriving
Glytch Tech
The Hunter Games: How to find the adversary with Event Query Language
Ross Wolf
Star Wars: How an ineffective Data Governance Program destroyed the Galactic Empire
Micah Brown
Security lessons from the Woofmutt�
Chris Roberts
What The Frida Gave Me: A Novel Take on E-Ticket Forging and E-Ticket Stealing
Priyank Nigam
(Not Recorded)
It's Coming From Inside the House: An Inside-Out Approach to NodeJS Application Security
Yolonda Smith
Get off my lawn� or are we looking for the right people?
Mike (Shecky) Kavka
Endpoint Security, Swimming Through the Snake Oil
Dan Beavin
Do You Have What It Takes? How to Support Your Career From Community Involvement
Kathleen Smith
Catching the Guerrilla: Powershell Counterinsurgency
Aaron Sawyer
SigInt for the Masses: Building and Using a Signals Intelligence Platform for Less than $150
Josh Conway
InfoSuck: The Nasty Bits Of The Industry We Want To Tell Noobs But Aren't Allowed To In Polite Company.
Danny Akacki
Standardizer: a standardization framework for your security alerts
Christian Burrows
Call Of Duty, Modernest Browser Warfare v2
Dhiraj Mishra
(Did not happen)
Information Security Practice Principles a Rosetta Stone for information
security work
Susan Sons
What Can Data Science Do for Security?
Wendy Edwards
Deepfakes: If anything can be real then nothing is real
April Wright
(Not Recorded)
Evicting the Password from the Digital Estate
Alex Chalmers
A Theme of Fear: Hacking the Paradigm
Catherine Ullman
Beginning DFIR - How to get started with Cooties
Lisa Wallace
Of CORS it's Exploitable! What's Possible with Cross-Origin Resource Sharing?
Rebecca Deck
Nexus Zeta - How a newbie hacker managed to create a monster botnet
Adi Ikan
5G: Security Pitfalls and Considerations
Swapnil Deshmukh
(Did not happen)
Training and Education for the New Realities of Privacy and Security
Mitchell Parker
Container Security Deep Dive
Yashvier Kosaraju
Hacking Humans: Addressing Vulnerabilities in the Advancing Medical Device Landscape
Gabrielle Hempel
One Random Insecure Wep Application Please (ORIWAP)
Nancy Snoke
an Implantable Computer
Doug "c00p3r" Copeland
Modern AppSec Gotchas
Fletcher Heisler
A Few Things Right: Insights from Live and Simulated Incident Response
Chad Calease
The Resilient Reddit C2
Zach Zenner
Behind The Locked Door: we built an escape room for security awareness
Matthew Southworth Christian Bobadilla
F! Attribution
Xena Olsen Jared Peck
Inside Out Security - Building Castles not Warehouses
Alyssa Miller
Failure Is Not an Option: Developing Realistic Disaster Recovery Tests
Colin Campbell
Wibbly Wobbly: Designing Security for Systems that are Bigger on the Inside
Wolfgang Goerlich
Closing Ceremonies
|
| 05/19/2019 |
NolaCon
2019 Videos
Recorded at NolaCon 2019. Thanks to
@CurtisLaraque,
@mikearbrouet,
@openbayou,
@takanola,
@therealmacjeezy, Jason, Cole
& @klulue for the video recording help,
and @nola_con,
@erikburgess_,
@NolaConYvonne & Rob for having
me down to record.
One Random Insecure Wep Application Please (ORIWAP)
Nancy Snoke
Understanding XSS
Christina Mitchell
Social Engineering At Work - How to use positive influence to gain management
buy-in for anything
April C. Wright
DNS - Strategies for Reducing Data Leakage & Protecting Online Privacy
Jim Nitterauer
Automating Hashtopolis
Evil Mog
"It's Malware Time" - A Bar Crawl from Skunked Homebrew to Rotten Apples
Erika Noerenberg
Breaking into Cyber: How the hell are you supposed to get started?
Josh Millsap
After Mirai: Cyber Security Implications of IoT Botnet Proliferation Against
Critical Infrastructure
Paul W. Brager Jr M.Sci, CISSP, GICSP, CISM
Making an internal Let's Encrypt relay server
Josh Harvey
Keynote - I PWN thee, I PWN thee not!
Jayson E. Street
Breaking Into Your Building: A Hacker's Guide to Unauthorized Physical Access
Brent White. Tim Roberts
Formula for a Bug Bounty Program
Chris Holt
Forensics Phish Tank: Breaking Down Analysis of Advanced Phishing Emails
Joe Gray & Sophia Fadli
Baking Your Anomalous Cookies
Jim Allee
Waiter, there's a compiler in my shellcode!
Josh Stone
Empathy for the (Devel)oper: Lessons Learned Building An Application Security
Module
Yolonda Smith
MORE Tales From the Crypt...Analyst
Jeff Man
IR with Volatility Framework
Evan Wagner
Let's Talk About WAF (Bypass) Baby
Brett Gravois
Behavioral Security and Offensive Psychology at Scale
Josh Schwartz. Samantha Davison
My making of a Metasploit Module
Aaron Ringo
Don't Panic! A Beginner's Guide To Hardware Hacking
Phoenix Snoke
The Jazz Improv of Infosec
Damon J. Small
Elliptic Curve Cryptography: What it is and who needs it
Michele Bousquet |
| 04/28/2019 |
BSidesCharm 2019 Videos
These are the
videos BSidesCharm (Baltimore) 2019.
Thanks for inviting me down to record. Thanks to my video team Robert, Ethan,
Cory, Tim Steven, Trevor, Tom, Menachem and Josh.
Opening
Keynote
Matt Blaze
Embrace the Red: Enhancing detection capabilities with adversary simulation
Mauricio Velazco
I'lll Complete My Threat Model Later Mom!: Infosec in Middle School
Ashley Benitez Smith
Cleaning the Apple Orchard - Using Venator to Detect macOS Compromise
Richie Cyrus
More Tales From the Crypt...Analyst
Jeffrey Man
Anatomy & Evolution of a Fast Flux Malware Campaign
Emily Crose
COM Under The Radar: Circumventing Application Control Solutions
Jimmy Bayne
On The Line: What Phishing Really Impacts
Steven Becker
Automated Adversary Emulation
David Hunt
Comparing Malicious Files
Robert Simmons
How to Start a Cyber War: Lessons from Brussels
Chris Kubecka
You Moved to Office 365, Now What?
Sean Metcalf
You're Not as Safe as You Think: Clearing Up Common Security Misconceptions
Joshua Meyer
Keynote: The Declarative Future
Liam Randall
Exploring Community Volunteering Through a Career Development Lens
Kathleen Smith and Doug Munro
Defense in Depth Against DDoS Diminishes Dollars Destroyed
Daniel Gordon
Reasonable Rapid Recognition and Response to Rogues
Craig Bowser
BloodHound From Red to Blue
Mathieu Saulnier
A Code Pirate's Cutlass: Recovering Software Architecture from Embedded Binaries
evm
Technical Leadership: It's Not All Ones and Zeros
Timothy Schulz
Hunting for Threats in Industrial Environments and Other Scary Places
Nick Tsamis
It's Malware Time - A Bar Crawl from Skunked Homebrew to Rotten Apples
Erika Noerenberg
J-J-J-JEA Power
James Honeycutt
What did the SIEM Say?
JR Presmy and Shawn Thomas
Using Bashfuscator to Generate Bash Obfuscation
capnspacehook
Closing |
| 04/05/2019 |
Hacker/Infosec Con Types & Getting More Out Of Hacker/Infosec Conferences |
| 03/01/2019 |
BSides Columbus 2019 Video
These are the videos from the BSides Columbus Ohio conference. Thanks to Mitch &
Mike Spaulding for having me up and those who manned the video rigs such as
Cody, Matt, Dillon, Nick, Cole Chris and others whose name I can't seem to
remember in my old age..
Opening
Morning Keynote Featuring Runa Sandvik
Runa Sandvik
HACKERS, HOOLIGANS, HEISTS, & HISTORY
Brian Contos
Scrapping for Pennies: How to implement security without a budget
Ryan Wisniewski
Check Your Privilege (Escalation)
Kate Broussard
Wow, it really is always DNS! Becoming a Part of the DDoS Problem ( on purpose
).
Cody Smith
Unix: The Other White Meat
Adam Compton and David Boyd
Puppet Masters: How Social Engineers Continue to Pull Our Strings
Erich Kron
E-ZHack: An Update on SDR and Toll Booth Reverse Engineering
Kyle Westhaus
Mobile App Vulnerabilities - The Bad, The Worse And The Ugly
Ray Kelly
Mixing and Baking a New AppSec Person
Bill Sempf
(Some Missing Audio)
How Online Dating Made Me Better at Threat Modeling
Isaiah Sarju
What On Earth Is Quantum Computing?!? (And will it break all my encryption?)
Craig Stuntz
Battling Magecart: The Risks of Third-Party Scripts
Kevin Gennuso
Ship Hacking: Data on the Open Seas
Brian Olson
Common Developer Crypto Mistakes (with illustrations in Java)
Kevin Wall
The Overlooked Cyber Security Risk: 3rd Party Risk Management
Rose Songer
The Path to IAM Maturity
Jerod Brennan
Assumed Breach Testing
Brendan O'Connor
API Security: Tokens, Flows and the Big Bad Wolf
Ingy Youssef
Demystifying DMARC: A guide to preventing email spoofing
Sean Whalen
Afternoon Keynote Featuring Craig Hoffman
Craig Hoffman |
| 02/03/2019 |
BSides Tampa 2019 Videos
These are the videos from the
BSides Tampa conference. Thanks to
all of the BSides Crew for having me out to help record and render the videos.
Special thanks to my video crew: Matthew, Bridget, Patrick, Dan, Mike, Audrey and Chris
Opening
Doesn't It make You WannaCry: Mitigating Ransomware on a Windows Network
David Branscome
RegEx for Incident Response
Daniel Nutting
Bryan Turner
Intermediate Physical Security
Justin Wynn
Security Analytics in the Cloud
Marc Baker
How to use 400+M endpoints to build strong AI detection systems
Filip Chytry
20/20 Enterprise Security Monitoring: Seeing clearly with Security Onion
Wes Lambert
Beyond Lockpicking
Brian Etchieson
Social Forensication: A Multidisciplinary Approach to Successful Social Engineering
Joe Gray
Phishing U2F-Protected Accounts
Nikita Mazurov
Kenny Brown
Election Hacking: Getting Ready for the Russian Onslaught in 2020
Jeremy Rasmussen
Logging Pitfalls and How to Abuse Them
Kevin Kaminski
Michael Music
Personal security while on travel with additional pro-tips from seasoned travellers.
Derek Banks
Beau Bullock
Securing Shadow IT
Gene Cronk
Day When Quantum Computers Breaks Crypto
Roger Grimes
An Inside Look At Stopping Unauthorized Sellers & Counterfeiters On Amazon
Bruce Anderson
The Sound of Evil
Wes Widner
Serverless Security Top 10
Tal Melamed
Hacking IoT devices by chaining application security vulnerabilities
Rick Ramgattie
Becoming a Human nMAP! Cultivating a Renaissance Approach for the Social Engineer
Tigran Terpandjian
vCISO Is That the Right Answer
Mike Brooks
|
| 12/02/2018 |
SecureWV/Hack3rcon 2018 Videos
These are the videos of the presentations from
Secure West Virginia 2018. Thanks to
Justin, Tim, Lacy, Dave, Katie, Kevin, Todd, Alice, Brian, Brandon & Jon for helping record.
Intro/Welcome to SecureWV / Hack3rCon
Keynote - Hackers, Hugs, & Drugs.... Part II
Amanda Berlin
Why The Legal System Needs Your Help
Brian Martin
Mobile devices and you.
Detective Jeremy M. Thompson
The New Age of Ransomware: Cybercriminals Adopt Nation State Techniques
Allan Liska
Outside the Box: How the Internet of Things Poses New Cybersecurity Risks and Challenges the Law
Evan Kime
Applying the principles of Dodgeball: A True Underdog Story to CTFs
Branden Miller
Gun Safety Class
Branden Miller
Python Scripting
Justin Rogosky
Red Hat Enterprise Linux Security Technologies Lab
Lucy Kerner and Roy Williams
Automating Security Operations - on a budget
Jeremy Mio
Security Automation for the Blue Team
Eric Waters
Home Alone: A Pentester Perspective
Craig Vincent & Derek Banks
Simplified Red Hat Enterprise Linux Identity, Authentication, and Authorization management with Microsoft Active Directory and Red Hat Identity Management Trust
Roy Williams
Simple Attribution in Social Media and Websites
Brian Martin
Offensive and Defensive Security with Ansible
Lucy Kerner
High School Competitive Robotics and why you should care.
Charleston Area Robotics Team (CART)
Guaranteed Failure - Awareness The Greatest Cyber Insanity
Joshua Crumbaugh
Developing a Cloud Based Cyber Security Simulation Portal
David Krovich
The Hybrid Home Lab: From Laptop to Cloud
Holden Fenner
Securing your networks with Ansible
Adam Vincent
A deep look at Stack Buffer Overflows and Format String Vulnerabilities
Philip Polstra
Advanced threat hunting with open-source tools and no budget
Joseph DePlato
What's in a Domain Name?
Collin Meadows
Monitoring your home LAN with Python
Zach Tackett
Left of Boom
Ted Corbeill
Your Dead! Now what. How to help your family after your gone.
Steven Truax
A Brief Introduction to Metasploit
Joey Maresca
SecureWV / Hack3rCon Closing / Awards
Benny Karnes
|
| 10/19/2018 |
BSidesRDU 2018 Videos
These are the videos of the presentations from BSidesRDU.
Thanks to Cyrus, Brian, James Carl and others for all the work.
Welcome & Opening Remarks
BsidesRDU Staff
Keynote from Shahid Buttar, EFF Director Of Grassroots Advocacy
Shahid Buttar
Approaching Parity: Considerations for adapting enterprise monitoring and incident response (IR) capabilities for efficacy in cloud environments, and how to operationalize these capabilities with a playbook.
Matt
Movement After Initial Compromise
SleepZ3R0 and HA12TL3Y
Our Docker app got hacked. Now what?
Joel Lathrop
Sky-high IR - IR at Cloud Scale
@aarondlancaster
When it rains it pours
Sam Granger
Rise of the Advisor
Neal Humphrey
No Network Needed?!?!
Ron Burkett
WarGames
Justin Hoeckle |
| 10/8/2018 |
Derbycon 2018 Videos
These are the videos of the presentations from Derbycon 2018.
Big thanks to my video jockeys
@nightcarnage,
@securid,
@theglennbarrett,
@LenIsham,
@curtisko,
@bsdbandit,
@someninjamaster,
@Simpo13,
@primestick,
@SciaticNerd,
@CoryJ1983,
@SDC_GodFix,
@Skiboy941,
@TeaPartyTechie,
@livebeef,
@buccaneeris,
@mjnbrn,
@sfzombie13,
@kandi3kan3,
@paint27,
@AlexGatti
Opening
How to influence security technology in kiwi underpants
Benjamin Delpy
Panel Discussion - At a Glance: Information Security
Ed Skoudis, John Strand, Lesley Carhart. Moderated by: Dave Kennedy
Red Teaming gaps and musings
Samuel Sayen
A Process is No One: Hunting for Token Manipulation
Jared Atkinson, Robby Winchester
Fuzz your smartphone from 4G base station side
Tso-Jen Liu
Clippy for the Dark Web: Looks Like You're Trying to Buy Some Dank Kush, Can I Help You With That?
Emma Zaballos
Synfuzz: Building a Grammar Based Re-targetable Test Generation Framework
Joe Rozner
Escoteric Hashcat Attacks
Evilmog
RFID Luggage Tags, IATA vs Real Life
Daniel Lagos
#LOL They Placed Their DMZ in the Cloud: Easy Pwnage or Disruptive Protection
Carl Alexander
Maintaining post-exploitation opsec in a world with EDR
Michael Roberts, Martin Roberts
Hey! I found a vulnerability - now what?
Lisa Bradley, CRob
Foxtrot C2: A Journey of Payload Delivery
Dimitry Snezhkov
Ridesharks
Kaleb Brown
IRS, HR, Microsoft and your Grandma: What they all have in common
Christopher Hadnagy, Cat Murdock
#LOLBins - Nothing to LOL about!
Oddvar Moe
Everything Else I Learned About Security I Learned From Hip-Hop
Paul Asadoorian
Hackers, Hugs, & Drugs: Mental Health in Infosec
Amanda Berlin
Android App Penetration Testing 101
Joff Thyer, Derek Banks
Draw a Bigger Circle: InfoSec Evolves
Cheryl Biswas
I Can Be Apple, and So Can You
Josh Pitts
From Workstation to Domain Admin: Why Secure Administration Isn't Secure and How to Fix It
Sean Metcalf
MS17-010?
zerosum0x0
The Unintended Risks of Trusting Active Directory
Lee Christensen, Will Schroeder, Matt Nelson
Lessons Learned by the WordPress Security Team
Aaron D. Campbell
IronPython... omfg
Marcello Salvati
Invoke-EmpireHound - Merging BloodHound & Empire for Enhanced Red Team Workflow
Walter Legowski
When Macs Come Under ATT&CK
Richie Cyrus
Abusing IoT Medical Devices For Your Precious Health Records
Saurabh Harit, Nick Delewski
Detecting WMI exploitation
Michael Gough
Gryffindor | Pure JavaScript, Covert Exploitation
Matthew Toussain
Instant Response: Making IR faster than you thought possible!
Mick Douglas, Josh Johnson
The History of the Future of Cyber-Education
Winn Schwartau
State of Win32k Security: Revisiting Insecure design
Vishal Chauhan
Offensive Browser Extension Development
Michael Weber
Protect Your Payloads: Modern Keying Techniques
Leo Loobeek
Jump Into IOT Hacking with the Damn Vulnerable Habit Helper Device
Nancy Snoke, Phoenix Snoke
Tales From the Bug Mine - Highlights from the Android VRP
Brian Claire Young
Decision Analysis Applications in Threat Analysis Frameworks
Emily Shawgo
Threat Intel On The Fly
Tazz
Make Me Your Dark Web Personal Shopper!
Emma Zaballos
Driving Away Social Anxiety
Joey Maresca
Off-grid coms and power
Justin Herman
CTFs: Leveling Up Through Competition
Alex Flores
Extending Burp to Find Struts and XXE Vulnerabilities
Chris Elgee
Introduction to x86 Assembly
DazzleCatDuo
Pacu: Attack and Post-Exploitation in AWS
Spencer Gietzen
An Inconvenient Truth: Evading the Ransomware Protection in Windows 10
Soya Aoyama
Brutal Blogging - Go for the Jugular
Kate Brew
RID Hijacking: Maintaining Access on Windows Machines
Sebastian Castro
Your Training Data is Bad and You Should Feel Bad
Ryan J. O'Grady
So many pentesting tools from a $4 Arduino
Kevin Bong, Michael Vieau
Building an Empire with (Iron)Python
Jim Shaver
SAEDY: Subversion and Espionage Directed Against You
Judy Towers
OSX/Pirrit - Reverse engineering mac OSX malware and the legal department of the company who makes it
Amit Serper, Niv Yona, Yuval Chuddy
How to test Network Investigative Techniques(NITs) used by the FBI
Dr. Matthew Miller
Cloud Computing Therapy Session
Cara Marie, Andy Cooper
Silent Compromise: Social Engineering Fortune 500 Businesses
Joe Gray
Dexter: the friendly forensics expert on the Coinbase security team
Hayden Parker
Going on a Printer Safari - Hunting Zebra Printers
James Edge
Hardware Slashing, Smashing, and Reconstructing for Root access
Deral Heiland
App-o-Lockalypse now!
Oddvar Moe
Web App 101: Getting the lay of the land
Mike Saunders
Invoke-DOSfuscation: Techniques FOR %F IN (-style) DO (S-level CMD Obfuscation)
Daniel Bohannon
WE ARE THE ARTILLERY: Using Google Fu To Take Down The Grids
Chris Sistrunk, Krypt3ia, SynAckPwn
Just Let Yourself In
David Boyd
A "Crash" Course in Exploiting Buffer Overflows (Live Demos!)
Parker Garrison
Living in a Secure Container, Down by the River
Jack Mannino
VBA Stomping - Advanced Malware Techniques
Carrie Roberts, Kirk Sayre, Harold Ogden
Media hacks: an Infosec guide to dealing with journalists
Sean Gallagher, Steve Ragan, Paul Wagenseil
Deploying Deceptive Systems: Luring Attackers from the Shadows
Kevin Gennuso
The Money-Laundering Cannon: Real cash; Real Criminals; and Real Layoffs
Arian Evans
Perfect Storm: Taking the Helm of Kubernetes
Ian Coldwater
How to put on a Con for Fun and (Non) Profit
Benny Karnes, John Moore, Rick Hayes, Matt Perry, Bill Gardner, Justin Rogosky, Mike Fry, Steve Truax
Web app testing classroom in a box - the good, the bad and the ugly
Lee Neely, Chelle Clements, James McMurry
Metasploit Town Hall 0x4
Brent Cook, Aaron Soto, Adam Cammack, Cody Pierce
Community Based Career Development or How to Get More than a T-Shirt When Participating as part of the Community
Kathleen Smith, Magen Wu, Cindy Jones, Kathryn Seymour, Kirsten Renner
Disaster Strikes: A Hacker's Cook book
Jose Quinones, Carlos Perez
Ninja Looting Like a Pirate
Infojanitor
Hacking Mobile Applications with Frida
David Coursey
Victor or Victim? Strategies for Avoiding an InfoSec Cold War
Jason Lang, Stuart McIntosh
Ubiquitous Shells
Jon Gorenflo
99 Reasons Your Perimeter Is Leaking - Evolution of C&C
John Askew
Ship Hacking: a Primer for Today's Pirate
Brian Satira, Brian Olson
Code Execution with JDK Scripting Tools & Nashorn Javascript Engine
Brett Hawkins
PHONOPTICON - leveraging low-rent mobile ad services to achieve state-actor level mass surveillance on a shoestring budget
Mark Milhouse
Patching: Show me where it hurts
Cheryl Biswas
Advanced Deception Technology Through Behavioral Biometrics
Curt Barnard, Dawud Gordon
We are all on the spectrum: What my 10-year-old taught me about leading teams
Carla A Raisler
No Place Like Home: Real Estate OSINT and OPSec Fails
John Bullinger
The Layer2 Nightmare
Chris Mallz
Attacking Azure Environments with PowerShell
Karl Fosaaen
Blue Blood Injection: Transitioning Red to Purple
Lsly Ayyy
Mirai, Satori, OMG, and Owari - IoT Botnets Oh My
Peter Arzamendi
Comparing apples to Apple
Adam Mathis
How online dating made me better at threat modeling
Isaiah Sarju
Threat Hunting with a Raspberry Pi
Jamie Murdock
M&A Defense and Integration - All that Glitters is not Gold
Sara Leal, Jason Morrow
Social Engineering At Work - How to use positive influence to gain management buy-in for anything
April Wright
Ham Radio 4 Hackers
Eric Watkins, Devin Noel
Getting Control of Your Vendors Before They Take You Down
Dan Browder
Cyber Intelligence: There Are No Rules, and No Certainties
Coleman Kane
Getting Started in CCDC
Russell Nielsen
Changing Our Mindset From Technical To Psychological Defenses
Andrew Kalat
Red Mirror: Bringing Telemetry to Red Teaming
Zach Grace
Two-Factor, Too Furious: Evading (and Protecting) Evolving MFA Schemes
Austin Baker, Doug Bienstock
IoT: Not Even Your Bed Is Safe
Darby Mullen
Fingerprinting Encrypted Channels for Detection
John Althouse
On the Nose: Bypassing Huawei's Fingerprint authentication by exploiting the TrustZone
Nick Stephens
Bypassing Port-Security In 2018: Defeating MacSEC and 802.1x-2010
Gabriel Ryan
Goodbye Obfuscation, Hello Invisi-Shell: Hiding Your Powershell Script in Plain Sight
Omer Yair
Cloud Forensics: Putting The Bits Back Together
Brandon Sherman
Killsuit: The Equation Group's Swiss Army knife for persistence, evasion, and data exfil
Francisco Donoso
The MS Office Magic Show
Stan Hegt, Pieter Ceelen
Living off the land: enterprise post-exploitation
Adam Reiser
Hillbilly Storytime: Pentest Fails
Adam Compton
Bug Hunting in RouterOS
Jacob Baines
Breaking Into Your Building: A Hackers Guide to Unauthorized Access
Tim Roberts, Brent White
The making of an iOS 11 jailbreak: Kiddie to kernel hacker in 14 sleepless nights.
Bryce "soen" Bearchell
Who Watches the Watcher? Detecting Hypervisor Introspection from Unprivileged Guests
Tomasz Tuzel
Pwning in the Sandbox: OSX Macro Exploitation & Beyond
Adam Gold, Danny Chrastil
IOCs Today, Intelligence-Led Security Tomorrow
Katie Kusjanovic, Matthew Shelton
Closing Ceremonies
|
| 9/8/2018 |
GrrCON 2018 Videos
These are the videos of the presentations from GrrCON 2018. Big thanks to
EggDropX and Jaime for having me out, and my video crew (paint27, Erick, Jason, brettahansen, Angela,
Luke & others) for recording.Keynote
Dave Kennedy
An
Inconvenient Truth: Evading the Ransomware Protection in Windows
10
Soya Aoyama
The
Abyss is Waving Back - The four paths that human evolution is
charging down, and how we choose which one's right
Chris Roberts
Crypto
Gone Rogue: A Tale of Ransomware, Key Management and the
CryptoAPI
Pranshu Bajpai & Dr. Richard Enbody
You're
right, this talk isn't really about you!
Jayson E Street
Analyzing
Pwned Passwords with Apache Spark
Kelley Robinson
How to rob a bank over the phone
Joshua "Naga" Crumbaugh
(Posting Later Maybe)
Vibing
Your Way Through an Enterprise: How Attackers are Becoming More
Sneaky
Matthew Eidelberg
PwnBook:
Penetrating with Google's Chromebook
Corey Batiuk
Life,
Death + the Nematodes: Long live Cyber Resilience!
Chad Calease
Data
Data Everywhere but No One Stops to Think
Scott Thomas, Carl Hertz & Robert Wagner
Automation
and Open Source: Turning the Tide on Attackers
John Grigg
w.e
w.e Internet Explorer Does What It Wants
Aaron Heikkila
Pacu:
Attack and Post-Exploitation in AWS
Spencer Gietzen
Hacker
Tools, Compliments of Microsoft
David Fletcher & Sally Vandeven
How
to Conduct a Product Security Test: And How it Fits Into the
Larger Security Strategy
Dr. Jared DeMott
Over
the Phone Authentication
Spencer Brown
Designing
a Cloud Security Blueprint
Sarah Elie
To
Fail is Divine
Danny Akacki
Zero
to Owned in 1 Hour: Securing Privilege in Cloud, DevOps, On-Prem
Workflows
Brandon Traffanstedt
Malware
Mitigation Sample Detonation Intelligence Automation: Make Your
Binaries Work for You
Adam Hogan
emulacra
and emulation: an intro to emulating binary code with Vivisect
Atlas of D00m
SniffAir
- An Open-Source Framework for Wireless Security Assessments
Matthew Eidelberg & Steven Daracott
Threat
Hunting: the macOS edition
Megan Carney
The
Hybrid Analyst: How Phishing Created A New Type of Intel Analyst
Rachel Giacobozzi
Dragnet:
Your Social Engineering Sidekick
Truman Kain
Intelligence
Creating Intelligence: Leveraging what you know to improve
finding what you don,t
Tomasz Bania
Guaranteed
Failure: Awareness The Greatest Cyber Insanity
Joshua "Naga" Crumbaugh
Threat
Modeling: How to actually do it and make it useful
Derek Milroy
Structuring
your incident response could be one of the most important things
you do to bolster Security
Matt Reid
How
this 20 Year Old Changed the Security Industry
James O'Neill
Stop
Boiling The Ocean! How To Succeed With Small Gains
Joel Cardella
Do
I have a signature to detect that malware?
Ken Donze
2018
SIEM Trends: What is my Mean Time to Value?
Bill Lampe
Advanced
Attackers Hiding Inside Encrypted Traffic at the Endpoint
Jared Phipps
More
Tales from the Crypt-Analyst
Jeff Man
My
First year in Application Security
Whitney Phillips
Career
Risk Management: 10 tips to keep you employed
Chris Burrows
Red
vs Blue: The Untold Chapter
Aaron Herndon & Thomas Somerville
Saving
All the Money to Buy All the Booze: Learning to Hack All the
Things on a Budget
Michael Morgese
Analyzing
Multi-Dimensional Malware Dataset
Ankur Tyagi
Physicals,
Badges, and why it matters
Alex Fernandez-Gatti
InSpec:
Compliance as Code
Kent picat, Gruber
Bounty
Hunters
J Wolfgang Goerlich
|
| 8/9/2018 |
Patreon, Bitchute,
etc.
Hi all, I've set up a Patreon for those that want to help me increase the number of cons I
can record each year. As a reminder, the videos I record appear on
YouYube,
Archive.org and
BitChute for free, so
don't complain about what I put on my site if you can't figure out how to get to
the same content elsewhere. 😜 |
| 7/14/2018 |
OISF 2018 Videos
These are the videos from the
OISF Anniversary Event.
Introduction
Dr. John Carls
Catching the Social Engineer
Robert Stewart
Hacking Identity, A Pen Tester�s guide to IAM
Jerod Brennen
Active Defense: Helping the Threat Actors Hack Themselves
Matt Scheurer
Planning & Executing A Red Team Engagement
Tim Wright |
| 6/23/2018 |
BSides Cleveland 2018 Videos
These are the videos from the
Bsides Cleveland conference. Thanks
to
Rich, Nekko,
justinschmitt &
as the video team. Thanks to
twuntymcslore &
RockieBrockway for being con
mom & dad.
Hacking Your Happiness
Chris Gates
Active Defense - Helping threat actors hack themselves!
Matt Scheurer
Reflective PE Unloading
Spencer McIntyre
One Puzzle Piece at a Time: Logging Quick Wins
Celeste Hall
GO HACK YOURSELF: MOVING BEYOND ASSUMPTION-BASED SECURITY
Christine Stevenson
Using Technology to Defend Digital Privacy & Human Rights
Tom Eston
Code Execution with JDK Scripting Tools & Nashorn Javascript Engine
Brett Hawkins
Abandoned Spaces: Reconstructing APT Campaigns From Lapsed Domains
Daniel Nagy
What's Changed In The New OWASP Top 10?
Bill Sempf
Raindance: Raining Recon from the Microsoft Cloud
Michael Stringer
Tools and Procedures for Securing .Net Applications
Sam Nasr
Hacking Identity: A Pen Tester's Guide to IAM
Jerod Brennen
Phishing Forensics - Is it just suspicious or is it malicious?
Matt Scheurer
Securing Code - The Basics
Michael Mendez
The Marriage of Threat Intelligence and Incident Response or... Threat Hunting for the Rest of Us
Jamie Murdock
Wacky and Wild Security - Getting things under CIS Controls V7
Jeremy Mio
Interdisciplinary Infosec: Equifax, Individuation, and the Modern State
Thomas Pieragastini
Mobile Application Privacy and Analytics
Kevin Cody
Evolving the Teaching of Pen Testing in Higher Ed
Robert Olson
Go back to the basics with your processes: Improving operations without technology.
Mark Abrams
Anatomy of an Attack
John Fatten
Hackers, Hugs, & Drugs: Mental Health in Infosec
Amanda Berlin
|
| 6/14/2018 |
A Digital Handbook for the Recently Deceased
Article on dealing with a deceased person's financial and Internet accounts, and
making it easier for others to do so when you pass. |
| 6/8/2018 |
ShowMeCon 2018 Videos
These are the videos ShowMeCon 2018.
Thanks to Renee & Dave Chronister (@bagomojo) and others for having me out to record and speak. Also thanks to my video crew
@r3tr0_cod3x, James, Aaron, Jon and some other people I may have forgotten.Opening
The Insecure Software Development Lifecycle: How to find, fix, and manage deficiencies within an existing methodology.
April C. Wright
The Sky Isn't Falling, But the Earth May be Shifting: How GDPR Could Change the Face of InfoSec
Cliff Smith
Gulliver's Travels: Security Exploits and Vulnerabilities Around the Globe
Kevin Johnson
From DDoS to Mining: Chinese Cybercriminals Set Their Sights on Monero
David Liebenberg
ANTI-OSINT AF: How to become untouchable
Michael James
Who's Watching the Watchers?
Nathan Sweaney
We don't have to worry about that, It's in the cloud
Arnar Gunnarsson
SS7 for INFOSEC
Paul Coggin
Getting Newcomers into Infosec: The Tribulations of the Auburn University Hacking Club
Matthew Rogers
Exploring Information Security Q&A Panel
Timothy De Block
Securing Windows with Group Policy
Josh Rickard
ATAT: How to take on the entire rebellion with 2-3 stormtroopers
ll3nigmall
How Hyperbolic Discounting is keeping your security program from succeeding
Jon Clark
Hijacking the Boot Process - Ransomware Style
Raul Alvarez
Building a Cyber Training Range on a Budget
Robert Guiler
Lessons Learned from Development and Release of Blacksmith (The Meltdown Defense Tool For Linux)
Jared Phipps
How to Train Your Kraken - Creating a Monster Out of Necessity
Sean Peterson
PowerShell exploitation, PowerSploit, Bloodhound, PowerShellMafia, Obfuscation, PowerShell Empire, the Empire has fallen, you CAN detect PowerShell exploitation
Michael Gough
Offensive Cartography
Trenton Ivey
The Wrong Kind of DevOps Talk - Now with Extra Badness!
Bobby Kuzma
This Job is Making Me Fat!
Thomas Smith
You'll understand when you are older
Amanda Berlin & David Cybuck
Bitcoin - The generation of private keys based on public keys, a live demonstration
Richard Dennis
|
| 6/3/2018 |
Circle City Con 2018 Videos
These are the Circle City Con videos.
Thanks to the staff for inviting me
down to record. Big thanks to @irishjack, @0DDJ0BB,
@Ajediday, Jim,
@securesomething,
@AnarchistDalek,
@KitWessendorf,
@m3ch4n15m,
@Valacia,
@songsthatsaved,
@mchandleraz,
@christinemobes and other for helping set up AV and record.
Opening Ceremonies
Circle City Con Staff
Espionage In The Modern Age of Information Warfare
Scot Terban
The Never Ending Hack: Mental Health in InfoSec Community
Danny Akacki
The Network Night Watch
Eric Rand & Lesley Cahart
Held for Ransom with a Toy Gun
Brian Baskin
Dear Blue Team: Proactive Steps to Supercharge your IR
Joe Gray
CTF Tips and Tricks
Aaron Lintile
Classic Cons in Cryptocurrency
Wolfgang Goerlich & Zachary Sarakun
Enterprise Vulnerability Management (Assessing, Implementing, and Maintaining)
Derek Milroy
Security Beyond the Security Team: Getting Everyone Involved
Luka Trbojevic
The consequences of lack of security in the Healthcare and how to handle it
Jelena Milosevic
Stealing Cycles, Mining Coin: An introduction to Malicious Cryptomining
Edmund Brumaghin & Nick Biasini
Applying Thermodynamic Principles to Threat Intelligence
Kyle Ehmke
SAEDY: Subversion and Espionage Directed Against You
Judy Towers
How to Lie with Statistics, Information Security Edition
Tony Martin-Vegue
IoT 4n6: The Growing Impact of the Internet of Things on Digital Forensics
Jessica Hyde
A Very Particular Set of Skills: Geolocation Techniques For OSINT and Investigation
Chris Kindig
Rise of the Machines
Aamir Lakhani
Backdooring with Metadata
Itzik Kotler
Automahack - Automate going from zero to domain admin with 2 tools
Dan McInerney
Patching - It's Complicated
Cheryl Biswas
Containers: Exploits, Surprises and Security
Elissa Shevinsky
Playing Russian Troll Whack-a-Mole
Courtney Falk
The FaaS and the Curious - AWS Lambda Threat Modeling
Bryan McAninch
Deploying Deceptive Systems: Luring Attackers from the Shadows
Kevin Gennuso
Quick Retooling in .Net for Red Teams
Dimitry Snezhkov
(Re)Thinking Cyber Security Given the Spectre of a Meltdown: (Someone Hold My Beer)
Jeff Man
Carrot vs. Stick: Motivation, Metrics, and Awareness
Magen Wu
Securing without Slowing: DevOps
Wolfgang Goerlich
Operator: The Well-Rounded Hacker
Matthew Curtin
Abuse Case Testing in DevOps
Stephen Deck
GreatSCT: Gotta Catch 'Em AWL
Chris Spehn
|
| 5/20/2018 |
NolaCon 2018 Videos
Recorded at NolaCon 2018. Thanks to
@CurtisLaraque,
@mikearbrouet, @openbayou,
Cole & @klulue for the video recording
help, and @nola_con,
@erikburgess_,
@NolaConYvonne & Rob for having
me down to record.
Chasing the Adder... A Tale from the APT world
Stefano Maccaglia
Aww Ship! Navigating the vulnerabilities and attack surface of the maritime industry
John Sonnenschein
Hacking Dumberly, Just Like the Bad Guys
Tim Medin, Derek Banks
Automahack - Python toolchain for automated domain admin
Dan McInerney
Dear Blue Team: Proactive Steps to Supercharge your IR
Joe Gray
You'll Understand When You're Older
Amanda Berlin
Skills For A Red-Teamer
Brent White, Tim Roberts
Hacking Smart Contracts--A Methodology
Konstantinos Karagiannis
Fighting Child Exploitation with Oculum
Andrew Hay, Mikhail Sudakov
How to tell cajun doctors they have bad cyber-hygiene and live
Joshua Tannehill
What Infosec in Oil & Gas can Teach us About Infosec in Healthcare
Damon J. Small
On the Hunt: Hacking the Hunt Group
Chris Silvers, Taylor Banks
Your Mac Defenestrated. Post OSXploitation Elevated.
FuzzyNop & Noncetonic
Keynote: Follow The
Yellow Brick Road
Marcus J. Carey
We are the Enemy of the Good
Stephen Heath
Taking out the Power Grid's Middleman
Nathan Wallace, Luke Hebert
Privacy for Safety- How can we help vulnerable groups with privacy?
Stella
Cash in the aisles: How gift cards are easily exploited
Will Caput
Mind Games: Exploring Mental Health through Games
Todd Carr
Jump into IOT Hacking with Damn Vulnerable Habit Helper IOT Device
Nancy Snoke, Phoenix Snoke
The Future of Digital Forensics
Imani Palmer
Changing the Game: The Impact of TRISIS (TRITON) on Defending ICS/SCADA/IIoT
Paul W. Brager Jr M.Sci, CISSP, GICSP, CISM
Ducky-in-the-middle: Injecting keystrokes into plaintext protocols
Esteban Rodriguez
Gamifying Developer Education with CTFs
John Sonnenschein & Max Feldman
Active Directory Security: The Journey
Sean Metcalf
HTTP2 and You
Brett Gravois
|
| 5/12/2018 |
BSides Detroit 2018 Videos
These are the videos from the
BSides Detroit 2017 Conference.
Thanks to Ryan Harp (@th3b00st), Dan
Falk (@dnfalk), Wolfgang Goerlich (@jwgoerlich),
Matt Johnson (@mwjcomputing),
Kyle Andrus (@chaoticflaws), Kate
Vajda (@vajkat) and Chris Maddalena (@cmaddalena)
for having me out and Samuel Bradstreet (@TeaPartyTechie),
Leah Bradstreet, Xavier Johnson, Ali Faraj, Camilla Martins, Ben Valentine, James
Green, David Sornig, Steven Balagna, Nick Papa, Lucas Gorczyca, J Parker Galbraith and others I
may forget for helping to record.
Opening
Yes, You're an Impostor; now get back to work
Johnny Xmas
GRC
- "What Would You Say You Do Here?"
Brian Martinez
Protecting Phalanges from Processor Pressure Points
Matthew Clapham
A Reporter's Look at OSINT
Hilary Louise
(Sorry, mic was off, but
here is a longer version from GrrCon)
Nowhere to hide
Lucas Gorczyca
Know the Enemy - How to make threat intelligence work!
Nir Yosha
Hack like a Gohper
Kent Gruber
@taco_pirate's Art of Woo
Ben Carroll
Saving All the Money to Buy All the Booze: Learning to Hack All the Things on a Budget
Michael Morgese
Practical Incident Response in Heterogenous Environment
Kevin Murphy & Stefano Maccaglia
Security KPIs - Measuring Improvement in Your Security Program
Steven Aiello
|
| 5/11/2018 |
Converge 2018 Videos
These are the videos from the
Converge Information Security Conference.
Thanks to Ryan Harp (@th3b00st),
Dan Falk (@dnfalk),
Wolfgang Goerlich (@jwgoerlich),
Matt Johnson (@mwjcomputing),
Kyle Andrus (@chaoticflaws),
Kate Vajda (@vajkat) and
Chris Maddalena (@cmaddalena) for having me out and Samuel Bradstreet
(@TeaPartyTechie), Leah
Bradstreet, Xavier Johnson, Camilla Martins, Ben Valentine, James Green, David Sornig, Steven Balagna,
Nick Papa, J Parker Galbraith and others I may forget
for helping to record.Opening
Hackers, Hugs, & Drugs: Mental Health in Infosec
Amanda Berlin
Winning the cybers by measuring all the things
Jim Beechey
Social Engineering for the Blue Team
Timothy De Block
The Emerging Product Security Leader Discipline
Matthew Clapham
Server Message Block Worms: The gift that keeps on giving
Matthew Aubert
Don't Fear the Cloud: Secure Solutions at Lower Cost
Matt Newell
DevSecOps: Security Testing with CI/CD Automation Servers
Ed Arnold
Backdooring With Metadata
Itzik Kotler
How to Conduct a Product Security Test: And How it Fits Into the Larger Security Strategy
Nick Defoe
Securing ASP.NET Core Web Apps
Dustin Kingen
All the Bacon: How Lesley Knope and Ron Swanson encourage community growth
Kevin Johnson
ATT&CK Like an Adversary for Defense Hardening
Steve Motts & Christian Kopacsi
Unblockable Chains � Is Blockchain the ultimate malicious
infrastructure?
Omer Zohar
(may post later)
DADSEC 102
Richard Cassara
The Things You Should Be Doing Defensively Right Now
Joel Cardella
Held Hostage: A Ransomware Primer
Nick Hyatt
Prowling: Better Penetration Testing
J Wolfgang Goerlich
Automating Web App security in AWS
Luther Hill
Finding the Money to Run an Effective Security Program
Matt Topper
Cryptocurrency- The Internetwide Bug Bounty Program
Brian Laskowski
Hacking Identity: A Pen Tester,s Guide to IAM
Jerod Brennen |
| 4/29/2018 |
BSidesCharm 2018 Videos
These are the videos BSidesCharm
(Baltimore) 2018.
Thanks for inviting me down to record. Thanks to my video team Shawn Thomas,
Cory, Terry Holman, Thomas Moses, Jason Presmy and Martin Veloso.
Keynote
Jessica Payne
To AI or Not to AI? What the US Military Needs for Fighting Cyber Wars
Ernest Wong
Preparing for Incident Handling and Response within Industrial Control Networks
Mark Stacey
FailTime: Failing towards Success
Sean Metcalf
Getting Saucy with APFS! - The State of Apple�s New File System
Sarah Edwards
Basic Offensive Application of MOF Files in WMI Scripting
Devon Bordonaro
An Open Source Malware Classifier and Dataset
Phil Roth
Counting Down to Skynet
Nolan Hedglin
How we reverse engineered OSX/Pirrit, got legal threats and survived
Amit Serper
Threat Activity Attribution: Diferentiatinn the Who from the How
Joe Slowik
Quantify your hunt: not your parents� red teaming
Devon Kerr
Internet Anarchy & The Global March toward Data Localization
Andrea Little Limbago
Powershell Deobfuscation: Putting the toothpaste back in the tube
Daniel Grant
Effective Monitoring for Operational Security
Russell Mosley
Ryan St. Germain
Plight at the end of the Tunnel
Anjum Ahuja
Rise of the Miners
Josh Grunzweig
Malware Analysis and Automation using Binary Ninja
Erika Noerenberg
Between a SOC and a Hard Place
Shawn Thomas
Andrew Marini
James Callahan
Dustin Shirley
Using Atomic Red Team to Test Endpoint Solutions
Adam Mathis
Exercise Your SOC: How to run an effective SOC response simulation
Brian Andrzejewski
Adding Simulated Users to Your Pentesting Lab with PowerShell
Chris Myers
Barrett Adams
Building a Predictive Pipeline to Rapidly Detect Phishing Domains
Wes Connell
Closing Ceremonies
|
| 4/14/2018 |
BSides Nashville 2018 Videos
These are
the videos BSides Nashville 2018. Thanks to
@lil_lost for inviting me down to
record and being my bodyguard while in Nashville. Big thanks to Gabe Basset,
Geoff Collins, Cameron and others for helping set up AV and record.
Intro
Know Your Why
Oladipupo (Ladi) Adefala
Deploying Microsoft Advanced Threat Analytics in the Real World
Russell Butturini
An Oral History of Bug Bounty Programs
Dustin Childs
Blue Cloud of Death: Red Teaming Azure
Bryce Kunz
SECURITY INSTRUMENTATION: BE THE HERO GETTING VALUE FROM SECURITY
Brian Contos
Changing Who Writes the Queries: High-Leverage IR with Visual Playbooks & Visual
Graph Analysis
Leo Meyerovich
Learning to Hack the IOT with the Damn Vulnerable Habit Helper IOT Device
Nancy Snoke, Phoenix Snoke
Hacking the Users: Developing the Human Sensor and Firewall
Erich Kron
Community Based Career Activities or How Having Fun Can Help You with Your
Career
Kathleen Smith, Cindy Jones,Doug Munro, Magen Wu
Hillbilly Storytime - Pentest Fails
Adam Compton
See the ID Rules Before Us: FAL IAL AAL eh? Aaaagh!!! How, How, How, How?
Bruce Wilson
SAEDY: Subversion and Espionage Directed Against You
Judy Towers
Growing Up to be a Infosec Policy Driven Organization
Frank Rietta
Adding Simulated Users to Your Pentesting Lab with PowerShell
Chris Myers, Barrett Adams
Hacking VDI 101
Patrick Coble
Evaluating Injection Attack Tools Through Quasi-Natural Experimentation
John O'Keefe-Odom
Social Engineering for the Blue Team
Timothy De Block
|
| 4/6/2018 |
AIDE 2018
Videos
Recorded at AIDE 2018. Big thanks to Bill
Gardner (@oncee) for having me out to
record.
On Business Etiquette and Professionalism in the Workplace
Tess Schrodinger
InfoSec by the Numbers
Bill Gardner
Practical OSINT - Tools of the trade
Tom Moore
Potentially unnecessary and unwanted programs (a.k.a. PUPs)
Josh Brunty
How To Test A Security Awareness Program
Matt Perry
Disrupting the Killchain
Amanda Berlin
I have this piece of paper, now what?
Brandon Miller
Statistics Lie...Except About Passwords
Jeremy Druin |
| 3/24/2018 |
BSides Chattanooga 2018 Videos
These are
the videos from the BSides Chattanooga
conference. Thanks to Ron and Kevin for having me out, and John for helping
record.
Intro
Red vs Blue and why We are doing it wrong
Chris Roberts
The Semi-Comprehensive Guide to Setting Up a Home Lab
Andrew Williams
Lessons learned from a OWASP Top 10 Datacall
Brian Glas
Attacker vs. Defender: Observations on the Human Side of Security
Todd O'Boyle
The Gilligan Phenomenon: Fixing The Holes In the Ransomware And Phishing Boats
Eric Kron
Machine Learning and Cyber Security: How Smart is Can it Be?
Shayne Champion
Closing |
| 3/10/2018 |
BSides Indy 2018 Videos
These are the videos from the
BSides Indy conference. Thanks to Frank,
MzBat for having me up, and Nate for helping with AC.Intro
Lessons Learned - A 15 year Retrospective
Price McDonald
Phishing Forensics - Is it just suspicious or is it malicious?
Matt Scheurer
Presenting P@cketR@quet: An Auditory IDS
Killian Ditch
The Pillars of Continuous Incident Response
Brad Garnett
Zero to Owned in 1 Hour: Securing Privilege in Cloud and DevOps Workflow
Brandon Traffanstedt
Social Engineering for the Blue Team
Timothy De Block
Leveraging DevSecOps to Escape the Hamster Wheel of Never-ending Security Fail
Chris Reed
Creating a Cyber Volunteer Department
Ray Davidson
Closing
Frank Diaz |
| 3/2/2018 |
BSides Columbus 2018 Videos
These are the videos from the BSides Columbus Ohio conference. Thanks to Mitch &
Michael Spaulding for having me up and those who manned the video rigs.
Keynote
Dave Kennedy
Automating Security Testing with the OWTF
Jerod Brennen
Looks Like Rain Again: Secure Development in the Cloud
Bill Sempf
How Stuxnet Ruined My Life For 6 Months (But I Got To Fly 1st Class A Lot)
Chris Raiter, Jeremy Smith
Emotet - Banking Malware With A Bite
Bradley Duncan
Keynote
Kevin Burkart
Cryptology: It�s a Scalpel, not a Hammer
Mikhail Sudakov
Pass the Apple Sauce: Mac OS X Security Automation for Windows-focused Blue
Teams
Brian Satira
Why People Suck at Delivery: How to get your security projects off the ground
and into production!
Nick d'Amato
Zero to Owned in 1 Hour: Securing Privilege in Cloud and DevOps Workflow
Brandon Traffanstedt
Are you ready for my call? Security researcher insights into Responsible
Disclosure.
Jason Kent
Everything you always wanted to ask a hiring manager, but were afraid to ask!
Mike Spaulding
Deep Learning for Enterprise: Solving Business Problems with AI
Christian Nicholson
Building Jarvis
Stephen Hosom
Active Defense - Helping threat actors hack themselves!
Matt Scheurer
Shifting Application Security Left
Craig Stuntz
Presenting P@cketR@quet: An Auditory IDS
Killian Ditch
Security and Networking: Dual Purpose Tools
Cody Smith
Cybereason's Jim VanDeRyt - Fileless Malware Breakout Session
Jim VanDeRyt
The Quieter You Become, the More You�re Able to (H)ELK
Nate Guagenti, Roberto Rodriquez |
| 2/24/2018 |
BSides NOVA 2018 Videos
These are the videos from BSides NOVA 2018.
Thanks to those who manned the video rigs and helped set u
AM Keynote
Matt Devos
Deep Dive in the Dark Web (OSINT Style)
Kirby Plessas
PM Keynote
Jack Daniel
Adding Pentest Sauce to your Vulnerability Management Recipe
Luke Hudson, Andrew McNicol
The Value of Design in Cyber Threat Intelligence
Devon Rollins
DNC Hacked Data in the Hands of a Trained Intelligence Professional
Wally Prather, Dave Marcus
Your Facts Are Not Safe With Us: Russian Information Operations as Social
Engineering
Meagan Keim
DECEPTICON: Deceptive Techniques to Derail OSINT attempts
Joe Gray
I Thought Renewing the Domain Name Was Your Job?
Allan Liska
Automating Unstructured Data Classification
Malek Ben Salem
Vulnerability Patched in Democratic Donor Database
Josh Lospinoso
Living in a world with insecure Internet of Things (IoT)
Marc Schneider
Vulnerability Accountability Levers and How You Can Use Them
Amelie Koran
Cyber Mutual Assistance - A New Model for Preparing and Responding to Cyber
Attack
David Batz
Rethinking Threat Intelligence
Tim Gallo
What Color Is Your Cyber Parachute?
Cliff Neve, Candace King, Kazi Islam, Trey Maxam, Amelie Koran
Feds Meet Hackers
Ariel Robinson, Alyssa, Feola, Gray Loftin, Beau Woods, Amélie E. Koran
Recruiting in Cyber
Dan Waddel, Kathleen Smith, Suzie Grieco, Sabrina Iacarus, Kirsten Renner, Karen
Stied
How to get started in Cybersecurity
John Stoner
Improving Technical Interviewing
Forgotten Sec
Ask An Expert: Cyber Career Guidance and Advice
Micah Hoffman, Bob Gourley, John TerBush, Chris Gates, Kirby Plessas, Lea
Hurley, Neal Mcloughlin, Ovie Carroll, Sarah Edwards, Tigran Terpandjian, Willie
Lumpkin |
| 2/17/2018 |
BSides Tampa 2018
These are the videos from the
BSides Tampa conference. Thanks to
all of the BSides Crew for having me out to help record and render the videos.
Special thanks to my video crew: Julian, Andrew Schiro, Austin Ford, John Mejia,
Michael Iglesias, Micheal Milford, Mike Ziolkowski, Patty Morris, Robin
Noyes
Cyber Assurance - Testing for Success
Col. John Burger
You Can Run..but you cant hide!
Bruce Anderson
Red Team Apocalypse
Beau Bullock and Derek Banks
Advanced Persistent Security
Ira Winkler
Adding Simulated Users to Your Pentesting Lab with PowerShell
Chris Myers and Barrett Adams
The Shoulders of InfoSec
Jack Daniels
Blockchain: The New Digital Swiss Army Knife?
G. Mark Hardy
Modern Day Vandals and Thieves: Wireless Edition
David Switzer and Jonathan Echavarria
Fraud; Should you worry?
Greg Hanis
A Security Look at Voice-Based Assistants
David Vargas
Hackers Interrupted
Alex Holden
Insane in the Mainframe: Taking Control of Azure Security
Jeremy Rassmusen
MiFare lady Teaching an old RFID new tricks
Daniel Reilly
Medical Device Security: State of the Art in 2018
Shawn Merdinger
(not recorded)
Weaponizing IoT - NOT!
Kat Fitzgerald
(not recorded)
Blue Team's tool dump. Stop using them term NeXt-Gen this isn't XX_Call of Duty_XX.
Alex Kot
Exploiting Zillow "Zestimate" for Reckless Profit
Robert "RJ" Burney
Self Healing Cyber Weapons
Logan Hicks
Ransomware: A Declining Force in Today's Threat Landscape
Brad Duncan
Modern web application security
Julien Vehent
Advanced Social Engineering and OSINT for Penetration Testing
Joe Gray
Critical Infrastructure & SCADA Security 101 for Cybersecurity Professionals
Juan Lopez
Exothermic Data Destruction: Defeating Drive Recovery Forensics
Nikita Mazurov and Kenneth Brown
Derrick's Thank Yous |
| 12/08/2017 |
BSidesPhilly 2017 Videos
These are the videos from BSides Philadelphia 2017.
Thanks to Mark, Mike, Austin, John, David and others I'm forgetting for helping with
the video.
Innovating for 21st Century Warfare
Ernest "Cozy Panda" Wong
MFA, It's 2017 and You're Still Doing Wrong
Presented by Dan Astor and Chris Salerno.
Out With the Old, In With the GNU
Lsly
IoT devices are one of the biggest challenges
Charles @libertyunix Sgrillo
Evading C2 Detection with Asymmetry
By Brandon Arvanaghi and Andrew Johnston
Abusing Normality: Data Exfiltration in Plain Site
Aelon Porat
Smarter ways to gain skills, or as the DoD puts it
Dr. P. Shane Gallagher, Institute for Defense Analyses, and Evan Dornbush, co-founder, Point3 Security, Inc.
Game of the SE: Improv comedy as a tool in Social Engineering
Danny Akacki - Security Monkey
File Polyglottery; or, This Proof of Concept is Also a Picture of Cats
Evan Sultanik
Your Facts Are Not Safe With Us: Russian Information Operations As Social Engineering
Meagan Dunham Keim
Supercharge Your SOC with Sysmon
Chris Lee & Matthew Giannetto
Threat Hunting: Defining the Process While Circumventing Corporate Obstacles
Kevin Foster, Matt Schneck, Ryan Andress
Put up a CryptoWall and Locky the Key - Stopping the Explosion of Ransomware
Erich Kron, CISSP-ISSAP
Web Hacking 101 Hands-on with Burp Suite
David Rhoades of MavenSecurity.com
Hacker Mindset
David Brown: CISSP, CISM, IAM
|
| 11/29/2017 |
SecureWV/Hack3rcon2017
These are the videos of the presentations from
Secure West Virginia 2017. Thanks to
Justine, Tim, Morgan, Kevin, Todd & Roy for helping record.
Intro
Benny Karnes
Fighting Advanced Persistent Threats with Advanced Persistent Security
Ira Winkler
Coming Up with the Next Wave of Cyber Innovations-Start by Thinking 1ns1d3 th3 B0x
Ernest Wong
I survived Ransomeware.... Twice
Matt Perry
Value of threat intelligence
Stealthcare
SDR & RF Hacking Primer
Andrew Bindner
Digital Forensic Analysis: Planning and Execution
John Sammons
Intro to WireShark
Josh Brunty
Secrets of Superspies
Ira Winkler
Total Recall: Using Implicit Memory as a Cryptographic Primitive
Tess Schrodinger
IoT Panel
RCBI
Hillbilly Storytime - Pentest Fails
Adam Compton
Hackers, Hugs and Drugs
Amanda Berlin
FLDigi - E-mail over Packet Radio
Aaron West and Rob West
From junk to jewels: Destruction is the key to building
Branden Miller & Audrey Miller
SCAP: A Primer and Customization
Scott Keener
Security Through Ansible Automation
Adam Vincent
Vehicle Forensics: An Emerging Source of Evidence
John Sammons
Network Forensics using Kali Linux and/or SANS Sift
Josh Brunty
911 DDOS
Dianiel Efaw
Pi's, Pi's and wifi
Steve Truax
Technical Testimony: Doing the Heavy Lifting for the Jury
John Sammons
Emergent Gameplay
Ron Moyer
Closing
|
| 10/28/2017 |
GrrCON 2017 Videos
These are the videos of the presentations from GrrCON 2017.
Big thanks to EggDropX and Jaime for having me out, and my video crew
(paint27, Erick, & brettahansen) for
recording.
Ghast
STRATEGIES ON SECURING YOU BANKS & ENTERPRISES. (FROM SOMEONE WHO ROBS BANKS & ENTERPRISES FOR A LIVING!)
Jayson E Street
Population Control Through The Advances In Technology�
Chris Roberts
(sorry for the music in back ground)
You Got Your SQL Attacks In My Honeypot
Andrew Brandt
3rd Party Data Burns
Arron "Finux" Finnon
Morphing to Legitimate Behavior Attack Patterns
Dave Kennedy
Stealing Domain Admin (or How I Learned to Stop Worrying and Love the CSSF
Jerod Brennen
Oops! Was that your pacemaker?
Charles Parker, II
10 Cent Beer Night: The World we now Live In
Johnny Xmas
Realizing Software Security Maturity: The Growing Pains & Gains
Mark Stanislav & Kelby Ludwig
Cyber, Cyber, Cyber - Using the killchain to accomplish something
Amanda Berlin
An Employee, their Laptop and a Hacker walk into a Bar
Shannon Fritz
Eye on the Prize - a Proposal for Legalizing Hacking Back
Adam Hogan
I've got a (Pocket) Bone to pick with you
Dr Phil Postra
Gig
Topic depends on number of federal agents in audience
Atlas of Doom
Embedding Security in Embedded Systems
Dr. Jared DeMott
National Guard for Cyber? How about a Volunteer Cyber Department?
Ray Davidson
Red Team Yourself
Thomas Richards
An Attack Pathway Into Your Organization? Reducing risk without reducing operational efficiency
David Adamczyk
Pen Test War Stories - Why my job is so easy, and how you can make it harder
Aaron Herndon
Skills For A Red-Teamer
Brent White & Tim Roberts
ProbeSpy: Tracking your past, predicting your future
stumblebot
vAp0r and the Blooming Onion
Justin Whitehead & Jim Allee
A GRReat New Way of Thinking about Innovating for Cyber Defense (and even Cyber Offense)
Ernest "Cozy Panda" Wong
Threat Intelligence: Zero to Basics in presentation
Chris J
Learning from InfoSec Fails
Derek Milroy
A Reporter's Look at Open Source Intelligence
Hilary Louise
Hidden Treasure: Detecting Intrusions with ETW
Zac Brown
The Black Art of Wireless Post-Exploitation
Gabriel "solstice" Ryan
Mi Go
Change is Simply an Act of Survival: Predicting the future while shackled to the past
Bil Harmer
Dissecting Destructive Malware and Recovering from Catastrophe
Bryan York
Infosec State of Affairs: Too much Kim Kardashian - not enough Malcolm Gladwel
Jim Wojno & Dan Kieta
How do you POC? Are you really testing a product
Ken Donze
Tales From The Trenches: Practical Information Security Lessons
Michael Belton
Securing the Internet of Things (IoT) -Through Security Research and Vulnerability Analysis
Deral Heiland
The Future of Cyber Security
Anthony Sabaj
Building a Usable Mobile Data Protection Strategy
David "Heal" Schwartzberg
Software Defined Segmentation
Matt Hendrickson
The Shuttle Columbia Disaster: Lessons That Were Not Learned
Joel "I love it when they call me Big Poppa" Cardella
Infrastructure Based Security
Chris Barnes
Defending The De-funded
Keith Wilson
Real-World Red Teaming
spartan
We got it wrong
Wolfgang Goerlich
Critical Incident: Surviving my first layoff by applying BCP/DRP Principles
Tom Mead |
| 9/25/2017 |
Derbycon
7 Videos
I still have a lot of work to do, but here are the Derbycon 2017
videos. Working on fixing major audio sync issues as I can.
Big thanks to my video jockeys Some Ninja Master, Glenn Barret, Dave Lauer,
Jordan Meurer, Brandon Grindatti, Joey, nightcarnage, Evan Davison, Tim Sayre,
Morgan, Ben Pendygraft, Steven (SciaticNerd), Cory Hurst, Sam Bradstreet,
MadMex, Curtis Koenig, Jonathan Zentgraf, James Hurst, Paint27, Chris, Lenard. |
| 9/21/2017 |
Derbycon Streams
This page links to the streams for the different tracks when we start streaming
Friday from Derbycon. |
| 9/19/2017 |
Louisville Infosec 2017
Below are the videos from the
Louisville Infosec 2017 conference.
Thanks to all the video volunteers for helping me record.
Building an Infrastructure to Withstand
David Kennedy
Learning Crypto By Doing It Wrong
Jeremy Druin
A Needle in the Cloud
Michael Leigh
How to make your next audit less awful: Compliance by Default
Tom Kopchak
Strengthening the Human Firewall
Alexandra Panaretos
Of Flags, Frogs & 4chan: OPSec Vs. Weponized Autism
Adrian Crenshaw
The Enemy Within - Detecting and Mitigating Insider Threats
Justin Wilkins
Assessing POS Devices for Tampering
Chris Gida
Or How I Learned to Stop Worrying and Love the ...
Robert L. Brown
The Edge of Normal
Mark Loveless
Measuring Cyber Risk with Open FAIR
Apolonio "Apps" Garcia and John Zuziak
Investigating Malware using Registry Forensics
Jason Hale
Defeating the Modern Cyber Attacker
Travis Funkhouser
Show me the Money! Using the CIS Critical Security Controls to procure funding for your security program
Carla Raisler
|
| 6/24/2017 |
BSides Cleveland 2017 Videos
These are the videos from the
Bsides Cleveland conference. Thanks
to djaj9,
, ,
justinschmitt &
as the video team. Thanks to
twuntymcslore &
RockieBrockway for being con
mom & dad.
Morning
Keynote
Wendy Nather
Better manual web application testing through automation
Brian Mead
Blue-Teamin' on a Budget [of Zero]
Kyle Bubp
PANDA, walking loud in the cloud
Logan Hicks, Seth Hall, Kelsey Hightower, Laura Taylor, Doug Burks
Diary of a Security Noob
TJ Toterhi
Delete Yourself: Cognitive Bias during incidence response
Dru Streicher
Enterprise Monitoring From Zero
Andrew Johnson
What They're Teaching Kids These Days
Rob Olson, Chaim Sanders
Mid-Day Keynote
Ben Ten
IoT Device Pentesting
Erik Daguerre
Cyber, Cyber, Cyber - Using the killchain to accomplish something
Amanda Sullivan Berlin
Decentralization For Security and Freedom: A Discussion of Asymmetric and Decentralized Technologies
Tom Pieragastini
Getting back to the old school
Jamie Murdock
The Python in the Apple
Spencer McIntyre
Quantifying Security's Value - It Can Be Done!
Arianna Willett
Building your Human Firewall
Christopher Jones, John Winkler
Spy vs. Spy - Tips from the trenches for red and blue teams
Thomas McBee, Jeff McCutchan
Eye on the Prize - a Proposal for Legalizing Hacking Back
Adam Hogan
Choose Django for Secure Web Development
Vince Salvino
MacOS - An easy exploit 2-ways.
Cody Smith
Bypassing Next-Gen Tech
David Kennedy
Hacking in Highschool: Inspiring the next generation of security professionals
Michael Benich
Afternoon Keynote
John Strand
|
| 6/17/2017 |
ANYCon
2017 Videos
These are the ANYCon videos. Thanks to
Tyler & Erin for inviting me down to record. Also thanks to the AV crew Chris,
Bryan, Conner, Nigel, Ben, Dan & Joe.
ANYCon: Year One Kick-Off
Tyler Wightson
Keynote: Industry Of
Change
Dave Kennedy
The Changing Landscape of Cyber Security and Training the New Generation of
Cyber Warriors
Sanjay Goel
OWASP Top 10: Hacking Web Applications with Burp Suite
Chad Furman
Hacking Politics: Infosec in Public Policy
Jonathan Capra and Rashida Richardson and Shahid Buttar
Sniffing Sunlight
Erik Kamerling
Noob 101: Practical Techniques for AV Bypass
Jared Hoffman
Jedi Mind Tricks: People Skills for Security Pros
Alex DiPerna
Red Team Yourself
Thomas Richards
Jumping the Fence: Comparison and Improvements for Existing Jump Oriented Programming Tools
John Dunlap
The Stuffer
Sean Drzewiecki and Aaron Gudrian and Dr. Ronny L. Bull
Big Data's Big Problems
Jeanna Neefe Matthews
VLAN hopping, ARP Poisoning and Man-In-The-Middle Attacks in Virtualized Environments
Dr. Ronny L. Bull
Bringing Home Big Brother: Personal Data Privacy in the Surveillance Age
Todd Brasel and Michele Warner
Measuring the Efficacy of Real-Time Intrusion Detection Systems
Jeffrey Richard Baez
To SIEM or not to SIEM: an Overview
Chris Maulding
Let's Play Defense at Cyber Speed
Duncan Sparrell
Real Security Incidents, Unusual Situations
Adam Dean
Incident Response Evolved - A Preventative Approach to Incident Management
Aaron Goldstein
Thinking 1nside-the-B0x: Cyber Defense and Deterrence via How Hackers Think
Lieutenant Colonel Ernest Y. Wong
Making Friends for Better Security
Alexander Muentz
Does DoD Level Security Work in the Real World?
Jeff Man
The Road to Hiring is Paved in Good Intentions
Tim O'Brien
Whose Idea Was That? Comparing Security Curriculums and Accreditations to Industry Needs
Robert Olson and Chaim Sanders
Hacks, Lies, & Nation States
Mario DiNatale
Hold my Red Bull: Undergraduate Red Teaming
Jonathan Gaines
Ermahgerd: Lawrs
Prof. Robert Heverly
So You Want To Be A H6x0r, Getting Started in Cybersecurity
Doug White and Russ Beauchemin
DIY Spy Covert Channels With Scapy And Python
Jen Allen
InfoSec Career Building Through Reserve Military Service
Dan Van Wagenen
A Day in the Life of a Security Analyst
Marc Payzant and Ken Oliver and Aneesa Hussain
Breaking is Bad: Why Everyone at This Conference Will be Unemployed
Reg Harnish
|
| 6/11/2017 |
Circle City Con 2017 Videos
These are the Circle City Con videos.
Thanks to the staff for inviting me
down to record. Big thanks to @irishjack, @0DDJ0BB,
@Ajediday, Jim,
@securesomething Mike,
@KitWessendorf, fl3uryz,
InfaNamecheap,
Chris and other for helping set up AV and record.Opening Ceremonies
Opening Keynote: Words Have Meanings
Dan Tentler
And the Clouds Break: Continuity in the 21st Century
Wolfgang Goerlich
DNS Dark Matter Discovery - There's Evil In Those Queries
Jim Nitterauer
Tales from the Crypt...(analyst)
Jeff Man
Trials and Tribulations of setting up a Phishing Campaign - Insight into the how
Haydn Johnson
Everything is Not Awesome: How to Overcome Barriers to Proper Network Segmentation
Jason Beatty
Talky Horror Picture Show: Overcoming CFP Fears
Kat Sweet
Fuzzing with AFL
Adam DC949
Cybersecurity for real life: Using the NIST Framework to protect your critical infrastructure
Ryan Koop
Why is the Internet still working?
James Troutman
Effective Report Writing for Security Practitioners
Benjamin Robinson
The Decision Makers Guide To Managing Risk
Joel Cardella
Application Security Metrics
Caroline Wong
Security Training: Making Your Weakest Link The Strongest
Aaron Hnatiw
Network Security? What About The Data?
0ddj0bb 0ddj0bb
Detecting DNS Anomalies with Statistics
Jamie Buening
It's A Disaster!
Cheryl Biswas
OSINT And
Your World A Love Story
Michael James
Network manipulation on video games.
Alex Kot
Threat Intelligence: Zero to Basics
Chris J
The Kids Aren't Alright: Security and K-12 Education in America
Vivienne Pustell
Ph'ing Phishers
JAe
How To Be Curious
Bret Mattingly
Of Flags Frogs 4chan OPSec vs Weaponized Autism
Adrian Crenshaw
The State of Security in the Medical Industry
Cannibal (billy)
Open Sesamee
Max Power
See beyond the veil: Automating malicious javascript deobfuscation
Chad Robertson
Changing our future with 3D Printing
Emily Peed
You're not old enough for that: A TLS extension to put the past behind us
Falcon Darkstar Momot
We Don't Always Go Lights and Sirens
Kendra Cooley
Ichthyology: Phishing as a Science
Karla Burnett
Creating Your Own Customized Metamorphic Algorithm
Raul Alvarez
Peakaboo - I own you: Owning hundreds of thousands of devices with a broken HTTP packet
Amit Serper
Ye Olde Hacking
Johnny Xmas
Closing Keynote: Lectures or Life Experiences - Awareness Training that Works!
Tottenkoph & Cindy Jones
Closing Ceremonies
|
| 6/9/2017 |
ShowMeCon 2017 Videos
These are the videos ShowMeCon 2017.
Thanks to Renee & Dave Chronister (@bagomojo) and others for having me out to record and speak. Also thanks to my video crew
@r3tr0_cod3x Aaron, Jon and some other people I may have forgotten.
Data Loss Prevention in a Social Media World
Phllip Tully
Royal Testing: Purple teaming to build and secure applications better!
Kevin Johnson
Dark Web Economies (...and you can too!)
Johnny Christmas
DIY CTF - How to gain momentum on your security awareness program by hosting a CTF
Matt Thelan
Deconstructing Chaos: �through "Behavioral Detection"
Daniel Stiegman
Something Died Inside Your Git Repo: Recognizing the Smell of Insecure Code
Cliff Smith
REVERSING A POLYMORPHIC FILE-INFECTING RANSOMWARE
Raul Alvarez
The Beginner's Guide to ICS:� How to Never Sleep Soundly Again
Dan Bougere
Windows IR made easier and faster - Find the head of the snake using AutoRuns, Large Registry Keys, Logs, IP/WhoIs and Netflow
Michael Gough
Homebrew powershell: Where to begin with Data Sources and baseline data.
Andrew Metzger
Where Cypherpunk Meets Organized Crime: The Shifting Landscape of Underground Economies and Crypto-driven Privacy
Ben Brown
VR-Bleeding Edge of Development and Technology-But Are We Making Old Mistakes?
Arnar Gunnarson
F@$#IN Trojans! An Interactive Impromptu Talk on Our Most Dangerous Threat
Parameter
Kick starting an application security program
Tim De Block
Of Flags, Frogs & 4chan: OPSec vs. Weaponized Autism
Adrian Crenshaw
Intro to Threat Hunting
Aaron Mog
Panel Title: The Good, the Bad, and the Ugly: HIPAA in an InfoSec World
Hudson Harris
How to Patch Stupid - A Modern Approach To Securing Users
Joshua Crumbaugh
When Molehill Vulnerabilities Become Mountainous Exploits
Igor Matlin
Dear Blue Team, This is why I always win. Love, A Hacker
Dave Chronister
How I Inadvertently Outsourced My IT Job to a Fancy Bear
Tim MalcomVetter
|
| 5/21/2017 |
NolaCon
2017 Videos
Recorded at NolaCon 2017. Thanks to
@CurtisLaraque,
Federico,
Morgan, & Ken for the video recording
help, and @nola_con,
@erikburgess_, Yvonne & Rob for having
me down to record.
Does DoD Level Security Work in the Real World?
Jeff Man
Hacking the IoT: A Case Study
Nancy Meares Snoke and Phoenix Snoke
Going past the wire: Leveraging Social Engineering in physical security assessments
"Snow" Stephanie Carruthers
Hurt Me Plenty: The Design and Development of Arganium
Todd Carr
Easy Indicators of Compromise: Creating a Deception Infrastructure
David Kennedy
Arming Small Security Programs: Network Baseline
Matt Domko
Make STEHM Great Again
David Schwartzberg
Designing and Implementing a Universal Meterpreter Payload
Brent Cook
EDNS Client Subnet (ECS) - DNS CDN Magic or Secur
Jim Nitterauer
Rooting out evil: defend your data center like the Secret Service protects the President
Nathaniel Gleicher
Attacking Modern SaaS Companies
Sean Cassidy
The Unbearable Lightness of Failure
Dave Lewis
Phishing for Shellz: Setting up a Phishing Campaign
Haydn Johnson
Iron Sights for Your Data
Leah Figueroa
Security Guards -- LOL!
Brent White & Tim Roberts
Embrace the Bogeyman: Tactical Fear Mongering for Those Who Penetrate
FuzzyNop
Skynet Will Use PsExec: When SysInternals Go Bad
Matt Bromiley & Brian Marks
The Devil's Bargain: Targeted Ransomware and Its Costs
Joshua Galloway
22 Short Films About Security
Charlie Vedaa
Security is dead. Long live Infosec!
David Shaw
An Employee, their Laptop and a Hacker walk into a Bar
Shannon Fritz
Beyond OWASP Top 10
Aaron Hnatiw
Scamming the Scammers: Hacking scammers with pwns
Nathan Clark
|
| 5/13/2017 |
BSides Detroit 2017 Videos
These are the videos from the BSides
Detroit 2017 Conference. Thanks to Ryan Harp (@th3b00st),
Dan Falk (@dnfalk), Wolfgang Goerlich (@jwgoerlich),
Matt Johnson (@mwjcomputing),
Kyle Andrus (@chaoticflaws), Kate
Vajda (@vajkat) and Chris Maddalena (@cmaddalena)
for having me out and Samuel Bradstreet, Daniel Ebbutt, Luke Gorczyca, James
Green, David Sornig, Steven Balagna, Brandon Robinson, Brett Hansen, Briee de
Graaf, Nick Papa, Brandon Azer and others I may forget for helping to record.
Moving Towards Maturity: 5 Issues InfoSec Must Address
Jim Beechey
Plotting Hackers: Visualizing Attack Patterns
Kent Gruber
STEHM is the new STEM
David Schwartzberg
Hacking with Ham Radios: What I have learned in 25 years of being a ham.
Jay and Jerome Radcliff
Navigating Career Choices in InfoSec
Fernando Montenegro
Windows Event Logs - Zero to Hero
Nate Guagenti / Adam Swan
Network Security? What about the Data?
Jack Hatwick
ProbeSpy: Tracking your past, predicting your future
Ian Odette
Playing in Memory: Examples of User Theivery and Hunting for Malware
Kyle Andrus
The AppSec Starter Kit
Timothy De Block
An Employee, their Laptop and a Hacker walk into a Bar
Shannon Fritz
Estimating Development Security Maturity in About an Hour
Matt Clapham |
| 5/12/2017 |
Converge 2017 Videos
These are the videos from the
Converge Information Security Conference.
Thanks to Wolf for having me out and Sam, Samuel Bradstreet, Daniel Ebbutt, Luke
Gorczyca, James Green, David Sornig, Steven Balagna, Brandon Robinson,
Brett Hansen, Amanda Ebbutt, Nick Papa, Brandon Azer and others I may forget
for helping to record.
You Are Making Bad Decisions and You Should Feel Bad
Joel Cardella
Violent Ruby: A Talk for Hackers, Forensic Analysts, Penetration Testers and Security Engineers
Kent Gruber
Prioritize Vulnerability Remediation
Amol Sarwate
Stories through Logging: "It was the best of logs, it was the worst of logs"
Tom Kopchak
That Escalated Quickly
Shaun Bertrand
How to kick start and application security program
Timothy De Block
Vectors and Victims: Analyzing vulnerabilities through disease models
Rich Cassara
Threat Modeling 101
Matt Clapham
Prioritizing IT Security Projects for the Business
Martin Bally, Steve Barone, John Beeskow, David Derigiotis, Russ Gordon, John
Scrivens
Defending The De-funded
Keith Wilson
How to Transform Developers into Security People
Chris Romeo
You have Updates!...A look at an old tool making a comeback 'Evilgrade'
Reid Brosko
Predicting Exploitability
Michael Roytam
Fast wins for the defense!
Justin Herman
How Much Security Do You Really Need?
Wendy Nather
Tarnished Silver Bullets
Wolfgang Goerlich
A Top 10 List for Better AppSec (Hint: It's Not the OWASP Top Ten)
Dave Ferguson
AppSec Behaviors for DevOps Breed Security Culture Change
Chris Romeo
The 4 Eyes of Information Security
Fernando Montenegro
Practical Security Recommendations from an Incident Responder
Matthew Aubert
You and Your Technical Community
David Giard
Panel - Cyber Security Hiring,
Retention, and How to Get the Perfect Job in a Competitive Market
Misbehaving Networks?
Daniel Gregory
Leveraging Vagrant to Quickly Deploy Forensics Environments
Jeff Williams
New School Security: Combat Mindset
Mike Behrmann
|
| 4/30/2017 |
BSidesCharm 2017 Videos
These are the
videos BSidesCharm (Baltimore) 2017.
Thanks for inviting me down to record
Keynote
Rob M Lee
Clean up on Aisle APT
Mark Parsons
Frony Fronius - Exploring Zigbee signals from Solar City
Jose Fernandez
Weaponizing Splunk: Using Blue Teams for Evil
Ryan Hays
Current State of Virtualizing Network Monitoring
Daniel Lohin & Ed Sealing
The Not So Same-Origin Policy
David Petty
IoT Pressure Cooker What Could Go Wrong
Ben Actis
OPSEC for the Security Practictioner
Michael Clayberg
Automating Bulk Intelligence Collection
Gita Ziabari
I Went Phishing and Caught a Charge � Maryland Law for Pentesters
Joshua Rosenblatt
Imposter Syndrome: I Don't Feel Like Who You Think I Am
Micah Hoffman
The Battle for OSINT - Are you Team GUI or Team Command Line?
Tracy Z. Maleeff & Joe Gray
SOC Panel Keynote
Keynote
Jim Christy
Red Teaming the Board
Robert Wood
The AVATAR Project and You
da_667
Threat Hunting - Thinking About Tomorrow
Tazz
Understanding the Cybersecurity Act of 2015
Jeff Kosseff
Detecting the Elusive: Active Directory Threat Hunting
Sean Metcalf
Microsoft Patch Analysis for Exploitation
Stephen Sims
Arming Small Security Programs: Network Baseline Generation and Alerts with
Bropy
Matt Domko
The Cryptography of Edgar Allan Poe
Robert Weiss (pwcrack)
Closing |
| 4/22/2017 |
BSides
Nashville 2017 Videos
These are
the videos BSides Nashville 2017. Thanks to
@lil_lost for inviting me down to
record and being my bodyguard while in Nashville. Big thanks to Geoff Collins,
Gabe Bassett, and others for helping set up AV and record.
Mental Health in Infosec: Hackers, Hugs, & Drugs
Amanda Berlin
Got Vendors?
Armin Smailhodzic and Willie Hight
Emerging Legal Trends in Cybersecurity
Rodney Hampton
Trust, But Verify, Your SAML Service Providers
Bruce Wilson
Does DoD Level Security Work in the Real World?
Jeff Man
Abstract Tools for Effective Threat Hunting
Chris Sanders
Infosec Tools of the Trade: Getting Your Hands Dirty
Jason Smith and Tara Wink
How to learn reverse engineering, kick ass at bug bounties, and being a bad ass
SOC analyst
ben actis
A Pyrate looks at 40
Adam John
Springtime for code reviews
Ryan Goltry
Marrying Incident Response and Threat Intel Within Your Enterprise
Joe Gray and Ben Shipley
Security Guards -- LOL!
Brent White
Windows Operating System Archaeology
Casey Smithand Matt Nelson
Intro to drone tech
Ron Foster
Weaponizing Splunk: Using Blue Team Tools for Evil
Ryan Hays
Chunky Cookies: Smashing Application Aware Defenses
Russell Butturini
|
| 4/7/2017 |
AIDE 2017
Videos
Recorded at AIDE 2017. Big thanks to Bill
Gardner (@oncee) for having me out to
record.
The Attack Is Coming From Inside The Refrigerator!
Mark Boltz-Robinson
Human Error and It's Impact on Your Infosec Program
Mike Baker
How to Speak Cat Picture Resiliency -- The ability to make a business case for
proactive incident response
Scott Lyons and Joshua Marpet
Learning Cryptography by Doing it Wrong
Jeremy Druin
I Survived Ransomware... TWICE
Matt Perry
How Russia Hacked The Election
Bill Gardner
OS X Forensics
Brian Martin
Making Our Profession More Professional
Bill Gardner |
| 4/1/2017 |
Cyphercon 2.0 Videos
These are the videos from the Cyphercon 2.0
conference. Thanks to Michael Goetzman
for having me out to record, and Paul and Tom for helping record.
Opening Ceremony
CypherCon Organizors
KEYNOTE: STEHM is the new STEM
David "Heal" Schwartzberg
Beyond the Fringe: Anomalies of Consciousness, Experience, and Scientific
Research
Richard Thieme
Cluster Cracking Passwords & MDXfind
Robert Reif
A Look Behind the Scenes of DEFCON DarkNet
Ed Abrams (zeroaltitude), Demetrius Comes (cmdc0de)
JavasCrypto: How we are using browsers as Cryptographic Engines
Kat Traxler
Can Cryptography Frustrate Fascism?
Phillip Rogaway
Threat Intelligence 101: Basics without Buzzwords
M4n_in_Bl4ck
Explore Wisconsin Hacker History
Brad Swanson
Brain Based Authentication
Melanie Segado, Sydney Swaine-Simon
The Upside Down: Going from NetSec to AppSec
Cody Florek
Tracking/Monitoring WiFi devices without being connected to any network
Caleb Madrigal
Wireless Capture the Flag
Eric Escobar
KEYNOTE: The History of Video Game Console Hacking
Dan Loosen
Protecting Passwords with Oblivious Cryptography
Adam Everspaugh
A Look Behind the Scenes of DEFCON DarkNet - Part II - Part II
Ed Abrams (zeroaltitude), Demetrius Comes (cmdc0de)
Forensic Deconstruction of Databases through Direct Storage Carving
Dr. Alexander Rasin
Espionage & Soviet MiGs
Dave Roebke
Naked and Vulnerable: A Cybersecurity Starter Kit
Shannon Fritz
Wasn't DLP supposed to fix this?
Amit Riswadkar (FeMaven)
IoT Security Privacy Weaknesses & Ransomware
Rick Ramgattie
Predictive Analytics and Machine Learning: 'Real' Use Cases for IT/Security
Professionals
John Platais
From zero to Bender in 12 months, how a software guy turned hardware
Zapp
Badge Panel
Does DoD Level Security Work in the Real World?
Jeff Man
Badges
Closing Ceremony
CypherCon Organizors |
| 3/25/2017 |
Bloomcon 2017 Videos
These are the videos from the
Bloomcon conference.
Strange times we live in:
Alexander Muentz
Real World
Examples of IT Risks
Fred Reck
The first 48: All your data are belong to us
Chad Gough & Molody Haase & Jared Sikorski
Deleted Evidence: Fill in the Map to Luke Skywalker
David Pany
The Cox Fight and Beyond: Kodi, the Brave New World of Copyright Infringement, and ISP Liability
Alex Urbelis
What is the size of a sparse file in NTFS
John Riley
Black Box Mac OSX Forensics
Brian Martin
Math and Cryptography
Sam Gross
Road Ahead
Ben Tice
Honey, I Stole Your C2 Server: A dive into attacker infrastructure
Andrew Rector
Building a Scalable Vulnerability Management Program for Effective Risk Management
Katie Perry
New results in password hash reversal
Mark Sanders
Lessons Learned from Pwning my
University Aaron Thomas
Aaron Thomas
Windows Event Logs - Zero to Hero
Nate Guagenti & Adam Swan
What Can my Logs Tell me?
Art Petrochenko
A POS Breach Investigation
Kevin Strickland
Abusing Google Dorking and Robots.txt
Dave Comstock
APT-What the heck is an APT?
Bill Barnes
Technological Changes that Affect Forensic Investigations
Diane Barrett
Deceptive Defence
Daniel Negron
Cryptography 0-128
Ben Tice
Sometimes They Are Innocent!
Scott Inch
Securely Deleting Data from SSDs
Stephen Larson
|
| 3/11/2017 |
BSides Indy 2017 Videos
These are the videos from the
BSides Indy conference.
Intro
Strategies on Securing you banks & enterprises. (From someone who robs banks &
enterprises for a living!)
Jayson Street
Crypto defenses for real-world system threats
Kenneth White
Hardware Hacking: Abusing the Things
Price McDonald
Kick starting an application security program
Timothy De Block
OSINT For The Win - Tools & Techniques to Maximize Effectiveness of Your Social
Engineering Attacks
Joe Gray
Physical Phishing, Way Beyond USB Drops!
Rich Rumble
Weaponizing Nanotechnology and hacking humans; 2017 updates :)
Chris Roberts
Make STEHM Great Again
David Schwartzberg
|
| 2/25/2017 |
BSides NOVA 2017 Videos
These are the videos from BSides NOVA 2017.. Thanks to those who
manned the video rigs.
AM Key Note
Ron Gula
Using Software Defined Radio for IoT Analysis
Samantha Palazzolo
Imposter Syndrome: I Don't Feel Like Who You Think I Am.
Micah Hoffman
PM Keynote - Tarah Wheeler
How the Smart-City becomes stupid
Denis Makrushin
Won't Get Fooled Again: The expected future of IoT malware and what to do about
it.
Blaine Mulugeta
Software Supply Chains and the Illusion of Control
Derek Weeks
"Humans, right?" Soft Skills in Security
Ariel Robinson
Panel | Local Community Cyber Groups in NoVA
Jeremy Duncan
Networking with Humans to Create a Culture of Security
Tracy Maleeff
Why the NTP Security Problem Is Worse than You Think
Allan Liska
Bro, I Can See You Moving Laterally
Richie Cyrus
Panel | Parlaying Education and Experience into an Infosec Career
Forgotten Sec
So you want to be a "Cyber Threat Analyst" eh?
Anthony Melfi
0 to 31337 Real Quick: Lessons Learned by Reversing the Flare-On Challenge
Blaine Stancill
Finding a Companies BreakPoint
Zachary Meyers
Challenges and Opportunities: Application Containers and Microservices
Andrew Wild
Cyber Hunt Challenge - Develop and Test your Threat Hunting skills
Darryl Taylor
Anti-Virus & Firewall Bypass Techniques BY Candan B�-LÜKBAS
Candan Bolukbas
I'm Cuckoo for Malware: Cuckoo Sandbox and Dynamic Malware Analysis
Lane Huff |
| 2/12/2017 |
BSides Tampa 2017 Videos
These are the videos from the
BSides Tampa conference. Thanks to
all of the BSides Crew for having me out to help record and render the videos.
Special thanks to my video crew.
Keynote Talk : - Cyber Security in the Age of Espionage
Eric O'Neill (Not posted)
Advanced Targeted
Attack.
Andy Thompson
Phishing Pholks Phor Phun and Prophit
Erich Kron
Alert All the Things! (Network Baselines/Alerts with Bro Scripts)
Matthew Domko
Intro to Fuzzing for Fun and Profit
Brian Beaudry
Keynote
Kevin Poulsen (Not Recorded)
Build Your Own Physical Pentesting Go-Bag
Beau Bullock, Derek Banks
NFC Your
Smartphone's Best Friend or Worst Nightmare
Shane Hartman
e-Extortion Trends and Defense
Erik Iker
HIPAA for Infosec Professionals
Michael Brown
Deconstructing 100% JavaScript-based Ransomware
Jeremy Rasmussen & Paolo Soto
Mozilla's tips on strong HTTPS
Julien Vehent
Redefining Security in a Cloud-Centric Future
Mike Spaulding & Mitch Spaulding
Securing The Electrical Grid From Modern Threats
Christopher Williams
Securing Agile Development
Alan Zukowski
What I've Learned Writing CTF Challenges
Vito Genoese
Build the capability to Detect, Triage And Respond
Scott Sattler
What the Hell is ICS Security?
Brandon Workentin
Protecting Third-Party Risk From Plundering
Stacey Banks
Protecting Visual Assets: Digital Image Counter-Surveillance Strategies
Nikita Mazurov & Kenneth Brown
ArchStrike Linux
Chad Seaman
Hacking The Sabbath
Jonathan Singer
Chaining The Future: Block Chains and Security
Joe Blankenship |
| 1/16/2017 |
BSides Columbus 2017 Videos
These are the videos from the
BSides
Columbus Ohio conference. Thanks to Michael Spaulding for having me up and
those who manned the video rigs.
Learning From Pirates of the Late 1600s - The first APT
Adam Hogan
What I Learned About Cybersecurity by Training With US Navy SEALs
Matthew Curtin
Cross Origin Resource Sharing Kung fu
Aditya Balapure
Redefining Security in a Cloud Centric Future
Mike Spaulding
Automating Security in Building Software
Warner Moore
Planning and Executing a Red Team Engagement
Timothy Wright
DNSSec Explained!
Dan Benway
Midwestern Nice - Stereotype or Enterprise Threat?
Valerie Thomas
Information Security Talent Trends to expect in 2017
Megan Wells AJ Candella
|
| 12/03/2016 |
BSides Philadelphia 2016
These are the videos from BSides Philadelphia 2016.
Attacker's Perspective: A Technical Demonstration of an Email Phishing Attack
Zac Davis
Crashing Android phones via hostile networks
Yakov Shafranovich
I'm Cuckoo for Malware: Cuckoo Sandbox and Dynamic Malware Analysis
Lane Huff
How to Find a Company's BreakPoint
Andrew McNicol
What the deuce? Strategies for splitting your alerts.
John T. Myers
Red Team Yourself
Thomas Richards
Keynote
Matt Blaze
Solar Flare - Pulling apart SolarWinds ORION
Rob Fuller
Staying Afloat in a Tsunami of Security Information
Tracy Z. Maleeff
Hunting: Defense Against The Dark Arts
Danny Akacki
Every day is a Zero Day: Building an in-house Secure SDLC program
Tony Reinert
Owning MS Outlook with Powershell
Andrew Cole
A tour through the magical wonderful world of crypto land
Ben Agre
Remote attacks against IoT
Alex Balan
Hacking the Human: Social Engineering Basics
Dave Comstock (sten0)
Where do I start?
Charles Sgrillo II
Top 10 Mistakes Made In Active Directory That Can Lead To Being Compromised
Adam Steed
So you want to beat the Red Team?
Cameron Moore
Hacking Your Way into the APRS Network on the Cheap -- Extended Edition
Mark Lenigan
Threat Intel Analysis of Ukrainian's Power Grid Hack
Nir Yosha
Cryptography Pitfalls
John Downey
Information security and the law
Alex Muentz
Getting Permission to Break Things
William Bailey
"Knowing the Enemy"- Creating a Cyber Threat Actor Attribution Program
Jack Johnson
Red Teaming your Risk Management Framework
Keith Pachulski
Web Application Exploit 101 : Breaking Access Control and Business Logic
Tomohisa Ishikawa
Size Doesn't Matter : Metrics and Other Four Letter Security Words
Jim Menkevich
|
| 10/20/2016 |
SecureWV/Hack3rcon 2016 Videos
These are the videos of the presentations from
Secure West Virginia 2016. Thanks to Dave, Justine and Tim for helping
record. Sorry for the off audio timings, this is the first time I've used OBS
Studio for a con and I was testing new capture gear.
Welcome
Benny Karnes
Keynote
Dave Kennedy
SHALL WE PLAY A GAME. How to make an two player bartop arcade machine with a
Raspberry Pi.
Steven Truax
Maker/Hacker Space Panel - RCBI
So You Wanted to Work in Infosec
Joey Maresca
Making Our Profession More Professional
Bill Gardner
Special Agent Michelle Pirtle
(not recorded)
So You've Inherited a Security Department, Now What?
Amanda Berlin
SUSpect - A powershell based tool to provide early detection of ransomware and
other attack techniques.
Mick Douglas
Building an Infosec Program from Ground Zero: From the Coat Closet to the Data
Center
David Albaugh
How to Not Cheat on Your Spouse: What Ashley Madison Can Teach Us About OpSec
Joey Maresca
Windows Timelines in Minutes
Dr. Philip Polstra
Scripting Myself Out of a Job - Automating the Penetration Test with APT2
Adam Compton
WTF? Srsly? Oh FFS! - IR Responses
Mark Boltz-Robinson
Women in Infosec Panel
Adrian Crenshaw
Amanda Berlin
Taylor
Blair Gardner
(not posted)
Securing The Secure Shell, The Automated Way
Adam Vincent
Bitcoin: From Zero to "I get it."
Luke Brumfield
How to hack all the bug bounty things automagically & reap the rewards (profit)!
Mike Baker
Giving Back - Submitting to PTES 101
Jeremy Mio
Closing/Awards
Benny Karnes
Training
Intro to Linux
Benny Karnes
BASH Scripting
Justin Rogosky
(not recorded)
Python Scripting
Adam Byers
Intro to Kali
Wyatt Nutter
Forensics
Evidence Collection
John Sammons
Intro to WireShark
Josh Brunty
Intro to Digital Forensics
John Sammons
Network Forensics using Kali Linux and/or SANS Sift
Josh Brunty
Mobile Forensics An Introduction
Josh Brunty |
| 10/08/2016 |
GrrCON 2016 Videos
These are the videos of the presentations from GrrCON 2016.
Big thanks to EggDropX and Jaime for having me out, and my video crew
(Chris, Erick, & Cooper) for
recording.
Thieves
Act Three, The Evolution of Privacy
Finux
Weaponizing Nanotechnology and hacking humans; defining the boundaries
Chris Roberts
Becoming a Cyborg: The First Step Into Implantable Technology
Michael Vieau
Abnormal Behavior Detection in Large Environments
Dave Kennedy
Secure Dicks
Michael Kemp
and bad mistakes I've made a few...
Jayson Street (Only first 30 min)
Predator to Prey: Tracking Criminals with Trojans and Data Mining for Fun and Profit
Ken Westin
Guarding Dinner
J Wolfgang Goerlich
Back to the Future: Understanding our future but following the past
Kevin Johnson
Breaking Android Apps for Fun and Profit
Bill Sempf
Attacking the Hospitality and Gaming Industries: Tracking an Attacker Around the World in 7 Years
Matt Bromiley & Preston Lewis
Security Guards -- LOL!
Brent White & Tim Roberts
Pirates
Internet of Things (IoT) radio frequency (RF) Analysis With Software Defined Radio
Kevin Bong
So You Want to Be a Pentester
Absolute0x0
What do you mean I'm pwn'd!
I turned on automatic updates!
Scott Thomas & Jeff Baruth
Surreal Paradigms: Automotive Culture Crash
D0xt0r Z3r0
Reversing and Exploiting Embedded Devices (Walking the software and hardware stack)
Elvis Collado
Threat Detection & Response with Hipara
J. Brett Cunningham
Still Broken After All These Years Aka Utility Security For Smarties
Doug Nibbelink
Threat Detection Response with Hipara
J Brett Cunningham
Quick and Easy Windows Timelines with Pyhon, MySQL, and Shell Scripting
Dr. Phil Polstra
Cruise Ship Pentesting OR Hacking the High Seas
Chad M. Dewey
Using Virus Total Intelligence to track the latest Phishing Document campaigns
Wyatt Roersma
Encryption, Mobility & Cloud Oh My!
Bill Harmer
Magnetic Stripes 101
Tyler Keeton
Machine Duping: Pwning Deep Learning Systems
Clarence Chio
Money, Fame, Power - Build your success as a security professional
Nathan Dragun
Tales from the Crypt...(analyst)
Jeff Man
What's in your Top Ten? Intelligent Application Security Prioritization
Tony Miller
Binary Ninja
Jared Demott
Phish your employees for fun!
Kristoffer Marshall Mad Scientists
Securing Trust
- Defending Against Next-generation Attacks
John Muirhead-Gould
Five Nights At Freddys: What We Can Learn About Security From Possessed Bears
Nick Jacob
Make STEHM Great Again
David "HealWHans" Schwartzberg
Pentester-to-customer:I will 0wn your network! - Customer-to-pentester:No, I will make you cry!
David Fletcher & Sally Vandeven
How Do You Secure What You Don't Control
Dimitri Vlachos
Fighting the Enemy Within
Matt Crowe
Getting to the Root of Advanced Threats Before Impact
Josh Fazio
Reality-Checking Your AppSec Program
Darren Meyer
How to Implement Crypto Poorly
Sean Cassidy
Stop attacking your mother's car!
Charles Parker, II
Contracting: Privacy Security and 3rd Party
Nathan Steed & Kenneth Coleman
Alignment of business and IT Security
Shane Harsch
So You've Inherited a Security Department, Now What?
Amanda Berlin
Piercing the Air Gap: Network Steganography for Everyone
John Ventura
On being an Eeyore in Infosec
Stefan Edwards
Welcome to The World of Yesterday, Tomorrow!
Joel Cardella
Board Breaking |
| 9/26/2016 |
Derbycon 2016 Videos
The link above is where I will be putting presentations from Derbycon 2016
(it will take a few days).
Big thanks to my video jockeys Sabrina, Some Ninja Master, Glenn Barret, Dave
Lauer, Jordan Meurer, Brandon Grindatti, Joey, Fozy, nightcarnage, Evan Davison,
Chris Bridwell, Rick Hayes, Tim Sayre, Lisa Philpott, Ben Pendygraft, Sarah
Clarke, Steven (SciaticNerd), Cory Hurst, Sam Remington, Barbie, Chris Bissle (and
maybe the speakers too I guess). |
| 9/20/2016 |
Louisville Infosec 2016 Videos
Below are the videos from the Louisville
Infosec 2016 conference. Thanks to all the video volunteers for helping me
record.
Morning Keynote
Chandler Howell
Ryan J. Murphy
John Pollack
The Domain Name System (DNS) - Operation, Threats, and Security Intelligence
Tom Kopchak
Insiders are the New Malware
Brian Vecci
Cloud Security; Introduction To FedRAMP
Sese Bennet
Cloud Access Security Broker - 6 Steps To Addressing Your Cloud Risks
Matt Bianco
Not One Thin Dime: Just Say No to Ransomware!
Mick Douglas
Securing Docker Containers
Chris Huntington
Emerging Governance Frameworks for Healthcare Security
Max Aulakh
Building Our Workforce
Kristen Bell
The Art of Offense and Defense
Mark Loveless
The Current State of Memory Forensics
Jason Hale
Understanding Attacker's use of Covert Communications
Chris Haley
How to Talk to Executives about Security
Harlen Compton
Pen Testing; Red and Blue Working Together
Martin Bos
Data Loss Prevention - How to get the most for your buck
Brandon Baker
The Transition: Risk Assessment > Risk Management
Mike Neal
Darwinism vs. Forensics
Bill Dean
Closing
|
| 9/11/2016 |
BSides Augusta 2016 Videos
These are the videos from the
BSides Augusta
conference. Thanks to Lawrence
Abrams, and all of the BSides Crew for having me out to help record and render the videos and
Pentestfail and everybody that staffed a recording rig.
Keynote
Keynote - Robert Joyce
Super Bad
Mobile Hacking
Aaron Guzman
Incident Response Awakens
Tom Webb
Dr. Pentester or: How I Learned To Stop Worrying and Love the Blue Team
Ryan O'Horo
Exploit Kits/ Machine Learning
Patrick Perry
Detection of malicious capabilities using YARA
Brian Bell
Owning MS Outlook with Powershell
Andrew Cole
RAT Reusing Adversary Tradecraft
Alexander Rymdeko-Harvey
Internet of Terrible
Brandon McCrillis
I Got You
Using Honeypots for Network Security Monitoring
Chris Sanders
This one weird trick will secure your web server!
David Coursey
This is not your Momma's Threat Intelligence
Rob Gresham
Moving Target Defense: Evasive Maneuvers in Cyberspace
Adam Duby
Beyond Math: Practical Security Analytics
Martin Holste
Exploit Kits and Indicators of Compromise
Brad Duncan
ICS/SCADA Threat Hunting
Robert M. Lee and Jon Lavender
Agilely Compliant yet Insecure
Tom Ruff
It's Too Funky In Here
Gamification for the Win
Josh Rykowski and Scott Hamilton
IDS/IPS Choices: Benefits, Drawback and Configurations
ForgottenSec
Micro-segmentation and Security: The Way Forward
Jack Koons
Adventures in RAT dev
Hunter Hardman
Linux privilege escalation for fun, profit, and all around mischief
Jake Williams
How About a Piece of Pi - Experiences with Robots and Raspberry Pi Hacking
John Krautheim
Flaying out the Blockchain Ledger for Fun, Profit, and Hip Hop
Andrew Morris
Network Situational Awareness with Flow Data
Jason Smith
Living In A America
A worm in the Apple - examining OSX malware
Wes Widner
You TOO can defend against MILLIONS of cyber attacks
Michael Banks
Finding Evil in DNS Traffic
Keelyn Roberts
Ransomware Threats to the Healthcare Industry
Tim Gurganis
Using Ransomware Against Itself
Tim Crothers and Ryan Borres
Hunting: Defense Against The Dark Arts
Jacqueline Stokes, Danny Akacki, and Stephen Hinck
Automating Malware Analysis for Threat Intelligence
Paul Melson
Hide and Seek with EMET
Jonathan Creekmore and Michael Edie
|
| 7/17/2016 |
BSides Detroit 2016 Videos
These are the videos from the BSides
Detroit 2016 Conference. Thanks to Wolf for having me out and Chris, Daniel,
Daniel, Ed, Ben, Emi, Sam, Adam & Eric and others I may forget for helping to
record.
Intro
BSides Keynote
Atlas Of D00m
Car Hacking 0x05
Robert Leale
Learning Security the Hard Way: Going from Student to Professional
Benjamin Carroll
So You Want to Be a Pentester
Calvin Hedler
Sheep, the Shepard, History, and Eugenics - A historical reminder on why
personal privacy matters when it comes to the government and corporations in the
digital age.
David Schaefer
Emerging Threats
Tazz Tazz (Not posted)
I Have Been to The Future and I Did Not Want to Come Back
Garrett McManaway
How to Build a Home Lab
Chris Maddalena
Vulnerability Management Systems Flawed - Leaving your Enterprise at High Risk
Gordon MacKay
Bootstrapping A Security Research Project
Andrew Hay |
| 7/16/2016 |
Converge 2016
These are the videos from the
Converge Information Security Conference.
Thanks to Wolf for having me out and Chris, Daniel, Daniel, Ed, Ben, Sam, Adam & Eric and others I may forget
for helping to record.
Intro
Keynote 1
Steve Werby
So You've Inherited a Security Department, Now What?!?!
Amanda Berlin
Violating Trust: Social Engineering Past and Present
Paul Blonsky
AppSec Awareness: A Blue Print for Security Culture Change
Chris Romeo
Red Team Madness - Or, How I Learned To Stop Worrying and Expect Pentester Mistakes
Jeremy Nielson
Threat Modeling for Secure Software Design
Robert Hurlbut
Not Even One Shade of Gray: Stop Tolerating Compromise in Security
Rich Boyer
MySQL 5.7 Security
Dave Stokes
Evolving the Noise out InfoSec using Law Enforcement Paradigms
Charles Herring
Game of Hacks - Play, Hack, and Track
Igor Matlin
Red is the new Blue - Defensive Tips & Tricks from a Defender turned Pentester
Ben Ten
Building a better user: Developing a security-fluent society
Rich Cassara
Food Fight
J Wolfgang Goerlich
Maneuvering Management Madness
Andrew Hay
Enterprise Class Threat Management Like A Boss
Rockie Brockway
Compliant, Secure, Simple. Pick two.
Joshua Marpet
Sentry on the Wall
Reid Brosko
Expanding Your Toolbox the DIY Way
Chris Maddalena
Surreal Paradigms: Automotive Culture Crash
Dave Schaefer
Haking the Next Generation
David Schwartzberg
Malware Magnets: A practical walkthrough in developing threat intelligence
Tazz Tazz
Still broken after all these years aka Utility Security for Smarties
Doug Nibbelink
|
| 7/09/2016 |
OISF 2016 Videos
These are the videos from the
OISF Anniversary Event
Intro
Tom Webster
Breaking The Teeth Of Bluetooth Padlocks
Adrian Crenshaw
Identifying and Exploiting Hardware Vulnerabilities: Demo of the HRES Process
Tim Wright
2016 Predictions and How History repeats itself
Jason Samide
A Lawyer's Perspective on Data Security
Dino Tsibouris and Mehmet Munur
The Attacker's
Dictionary
Joel Cardella
|
| 6/25/2016 |
BSides Cleveland 2016 Videos
These are the videos from the BSides Cleveland
conference. Thanks to djaj9,
, ,
Kevin, f0zziehakz &
as the video team. Thanks to
twuntymcslore &
RockieBrockway for being con
mom & dad.
Morning Keynote
Ian Amit
Elementary, my dear Watson - A story of indicators
Nir Yosha
Preventing credential theft & lateral movement after initial compromise.
Cameron Moore
Ask a CISO
Jamie Murdock
Crime Prevention Through Environmental Design
Michael Mendez
Fun with One Line of Powershell
Matthew Turner
Learning From Pirates of the Late 1600s - The first APT
Adam Hogan
Food Fight!
Wolfgang Goerlic
Afternoon Keynote
Chris Roberts
The Art of Bit-Banging: Gaining Full Control of (Nearly) Any Bus Protocol
Aaron Waibel
Playing Doctor: Lessons the Blue Team can Learn from Patient Engagement
J Wolfgang Goerlich & Stefani Shaffer-Pond
Security Automation in your Continuous Integration Pipeline
Jimmy Byrd
The WiX Toolset, How to Make Your Own MSIs
Charles Yost
A Rookie PoV: The Hollywood Fallacy
Raquel Milligan
Port Scanning the Hermit Kingdom: Or What NMAP Can Teach Us About Geopolitics
Thomas Pieragastini
Responder for Purple Teams
Kevin Gennuso
Splunk for IR and Forensics
Tony Iacobelli
Bridging the Gap or: How I Learned to Stop Worrying, and Love the Developers
Eric Mikulas
SafeCracking on a Budget Redux
David Hunt and Zack Nagaich
Process Ventriloquism
Spencer McIntyre
The Digital Beginning of the Analog End
Brad Hegrat
Gamify Security Awareness: Failure to Engage is Failure to Secure
Michael Woolard
Cons and Conjurers: Lessons for Infiltration
Paul Blonsky
Closing Keynote
David Kennedy
|
| 6/14/2016 |
ShowMeCon 2016 Videos
These are the videos ShowMeCon 2016.
Thanks to Renee & Dave Chronister (@bagomojo),
Renee and others for having me out to record and speak. Also thanks to my video
crew Mathew, Morgan, James and some other people I may have forgotten.
Red is the New Blue
BenOxa
My Cousin Viinny: Ethics and Experience in Security "Research"
Kevin Johnson
The Psychology of Social Engineering
Dave Chronister
Show Me Your Tokens (and Ill show You Your Credit Cards)
Tim MalcomVetter
IRLHN Pt.3 Intermediate Networking Techniques for the Recovering Introvert
Johnny Xmas
And Bad Mistakes�I've made a few
Jayson Street
All your Door(s) Belong to Me - Attacking Physical Access Systems
Valerie Thomas
Exploiting First Hop Protocols to Own the Network
Paul Coggin
Check Yo Self Before you Wreck Yo Self: The new wave of Account Checkers and
Underground Rewards Fraud
Benjamin Brown
The Collission Attack - Attacking CBC and related Encryptions
Fontbonne
It's not a sprint�.
Tim Fowler
Social Media Risk Metrics - There's a way to measure how +@&# you are online
Ian Amit
Attacking OSX for fun and profit: tool set limiations, frustration and table
flipping.
Dan Tentler
The Art of AV Evations - Or Lack Thereof
Chris Truncer
Understanding Offensive and Defense - Having a purple view on INFOSEC
Dave Kennedy
Breaking the Teeth of Bluetooth Padlocks
Adrian Crenshaw
PowerShell Phishing Response Toolkit
Josh Rickard
Championing a Culture of Privacy: From Ambivalence to Buy-IN
Hudson Harris
Why Compliance Matters; You've Been Doing it Wrong
Stacey Banks
How to Build a Home Lab
Timothy De Block
Logging for Hackers, How you can catch them with what you already have and a
walk through of an actual attack and how we caught it.
Michael Gough
Where to Start when your environment is F*(3d
Amanda Berlin |
| 6/12/2016 |
Circle City Con 2016 Videos
These are the Circle City Con videos.
Thanks to the staff for inviting me down to record. Big thanks to Mike,
3ncr1pt3d,
fl3uryz,
InfaNamecheap,
f0zziehak, Chris, PhenixFire, Sammy
and other for helping set up AV and record.
Opening Ceremony
CircleCityCon Staff
Keynote - Dave Lewis
Dave Lewis
Food Fight!
Wolfgang Goerlich
Binary defense without privilege
Steve Vittitoe
Establishing a Quality Vulnerability Management Program without
Wasting Time or Money
Zee Abdelnabi (not posted)
Why it's all snake oil - and that may be ok
Pablo Breuer
Break on Through (to the Other Side)
Grape Ape
Bootstrapping A Security Research Project
Andrew Hay
Playing Doctor: Lessons the Blue Team Can Learn from Patient Engagement
Wolfgang Goerlich
Planes, Trains and Automobiles: The Internet of Deadly Things
Bryan K. Fite
Killing you softly
Josh Bressers
Now You See Me, Now You Don't - Leaving your Digital Footprint
Aamir Lakhani
Red Team Madness - Or, How I Learned To Stop Worrying and Expect Pentester
Mistakes
Jeremy Nielson
Open Source Malware Lab
Robert Simmons
So you want to be a CISO?
Von Welch
You want to put what�where?
John Stauffacher
IoT on Easy Mode Reversing and Exploiting Embedded Devices
Elvis Collad
Top 10 Mistakes in Security Operations Centers, Incident Handling & Response
Paul R. Jorgensen
Untrusted Onions: Is Tor Broken?
Joshua Galloway
Contextual Threat Intelligence: Building a Data Science Capability into the Hunt
Team
Brian Genz
Head in the Sand Defence or A Stuxnet for Mainframes
Haydn Johnson; Cheryl Biswas
SIEM, Supersized!
Walleed Aljony
Fantastic OSINT and where to find it
Tony Robinson (da_667)
Creating a Successful Collegiate Security Club (WIP)
Chris "Lopi" Spehn; Adam "avidhacker" Ringrood
Where to Start When Your Environment is F*(K3d
InfoSystir (Amanda Berlin)
Haking the Next Generation
David Schwartzberg
Exfil and Reverse Shells in a Whitelisted World
Hacking Our Way Into Hacking
Kat Sweet
Attacking OSX for fun and profit: Toolset Limitations, Frustration and Table
Flipping
Viss (Tentler)
Intro to Mobile Device Testing
Damian Profancik
Your Password Policy Still Sucks!
Martin Bos
Closing Ceremony
CircleCityCon Staff
|
| 5/22/2016 |
NolaCon
2016
Recorded at NolaCon 2016. Thanks to
@CurtisLaraque,
@HoltZilla,
@sid3b00m &
@ynots0ups for the video recording
help, and @nola_con,
@erikburgess_, & Rob for having
me down to record.
Intro
Analyzing DNS Traffic for Malicious Activity Using Open Source Logging Tools
Jim Nitterauer
Snake Charming: Fun With Compiled Python
Gabe K
Monitoring & Analysis 101: N00b to Ninja in 60 Minutes
Grecs
Calling Captain Ahab: Using Open Tools to Profile Whaling Campaigns
Ryan Jones, McOmie
Check Yo Self Before You Wreck Yo Self: The New Wave Of Account Checkers And Underground Rewards Fraud
Benjamin Brown
Introducing the OWASP API Security Project
Leif Dreizler, David Shaw
Breaking Barriers: Adversarial Thinking for Defenders
Stacey Banks
It's Just a Flesh Wound!
Brett Gravois
Owning MS Outlook with PowerShell
Andrew Cole
Why can't Police catch Cyber Criminals?
Chip Thornsburg
Keynote
David Kennedy
Calling Captain Ahab: Using Open Tools to Profile Whaling Campaigns
Matt Bromiley
Haking the Next Generation
David Schwartzberg
Hacking Web Apps (v2)
Brent White
Evolving Your Office's Security Culture by Selective Breeding of Ideas and Practices
Nancy Snoke
I Promise I'm Legit: Winning with Words
Cyni Winegard & Bethany Ward
You Pass Butter: Next Level Security Monitoring Through Proactivity
Cry0, S0ups
Going from Capture the Flag to Hacking the Enterprise. Making the switch from 'a hobby and a passion' to a lifelong career
Joseph Pierini
Hackers are from Mars, CxO's are from Jupiter
Rob Havelt
Don't be stupid with GitHub
Metacortex
DDoS: Barbarians at the Gate(way)
Dave Lewis
Hunting high-value targets in corporate networks
Josh Stone
|
| 4/22/2016 |
AIDE 2016
Videos
Recorded at AIDE 2016. Big thanks to Bill
Gardner (@oncee) for having me out to
record.
Do You Want Educated Users? Because This is How You Get Educated Users.
Tess Schrodinger
Don't blame that checklist for your crappy security program
Branden Miller
Shooting Phish in a Barrel
Amanda Berlin
Minimalistic Physical Assessment Kit
Tom Moore
Hacking Web Apps
Brent White and Tim Roberts |
| 4/17/2016 |
BSides Nashville 2016 Videos
These are the videos BSides Nashville 2016.
Thanks to @lil_lost for inviting me
down to record and being my bodyguard while in Nashville. Big thanks to Geoff
Collins, Branden Miller, Blake Urmos, Gabe Bassett, Nate and Alex McCormack for helping set up AV and record.
And bad mistakes I've made a few
Jayson Street
At the mountains of malware
Wes Widner
Collection and Detection with Flow Data: A Follow Up
Jason Smith
Container Chaos: Docker Security Container Auditing
Chris Huntington
It's Not If But When: How to Create Your Cyber Incident Response Plan
Lucie Hayward, Marc Brawner
Threat Modeling the Minecraft Way
Jarred White
AppSec Enigma and Mirage - When Good Ideas Can Go Awry
Frank Catucci
The Art of the Jedi Mind Trick
Jeff Man
How to get into ICS security
Mark Heard
The Ransomware Threat: Tracking the Digital Footprints
Kevin Bottomley
InfoSecs in the City - Starting a Successful CitySec Meetup
Johnny Xmas, Fletcher Munson, Chris Carlis, Kate Vajda
Ever Present Persistence - Established Footholds Seen in the Wild
Evan Pena, Chris Truncer
Forging Your Identity: Credibility Beyond Words
Tim Roberts, Brent White
IAM Complicated: Why you need to know about Identity and Access Management
Ron Parker
Put a Sock(et) in it: Understanding and Attacking Sockets on Android
Jake Valletta
|
| 3/31/2016 |
Central Ohio Infosec Summit 2016 Videos
These are the videos from the
Central Ohio Infosec Summit conference. Thanks to the video volunteers for
helping me record.
Track 1
Penetrating the Perimeter - Tales from the Battlefield
Phil Grimes
Navigating the FDA Recommendations on Medical Device Security _ and how they
will shape the future of all IoT
Jake "malwarejake" Williams
Detecting the Undetectable: What You Need to Know About OSINT
Jerod Brennen
Why I quit my dream job at Citi - A data centric approach to key management
Mike Bass
Fail Now _ So I Don't Fail Later "A look into security testing and training
methodologies"
Deral Heiland
Putting the Intelligence back in Threat Intelligence
Edward McCabe
All Your Door Belong To Me: Attacking Physical Access Systems
Valerie Thomas
The Humanity of Phishing Attack and Defense
Aaron Higbee
The Node.js Highway: Attacks Are At Full Throttle
Joshua Clark
Securing the Breach: Using a Holistic Data Protection Framework
Alex Hanway
Understanding Attacker'�s use of Covert Communications
Chris Haley
InfoSec Productization
David Kennedy
Track 2
Future of Information Security Governance, Risk and Compliance
Max Aulakh, Bill Lisse
How Experts Undermine Your Forensic Evidence
Matthew Curtin
Datacenter Security Virtualized
John Michealson
Embracing the Cloud
Lisa Guess
"It was the best of logs, it was the worst of logs" - Stories through Logging
Tom Kopchak
Finding the Needle in the Hardware Haystack - Identifying and Exploiting
Vulnerabilities via Hardware Reverse Engineering
Stephen Halwes, Timothy Wright
PKI-Do You Know Your Exposure?
Kent King
No Tradeoffs: Cloud Security and Privacy Don't Need to Be at Odds
Jervis Hui
Today's Threat Landscape
Dean Shroll
6 Critical Criteria For Cloud Workload Security
Sam Herath
Track 2
Educating the Board of Directors
Bob West
Burp Collaborator: The Friend You Didn't Know You Needed
Jon Gorenflo
Psychological Warfare: How Cyber Criminals Mess With Your Mind
Brian Henger
Threat Modeling for Secure Software Design
Robert Hurlbut
IAST Deep Dive: Understanding Interactive Application Security Testing
Ofer Maor
Building an Application Security Program
Mike Spaulding
Formal Verification of Secure Software Systems
Aaron Bedra
AppSec without additional tools
Jason Kent
Leveraging your APM NPM solutions to Compliment your Cyber Defense Strategy
Ken Czekaj, Robert Wright
Artificial Intelligence Real Threat Prevention
Art Hathaway
Defending the Next Decade - Building a Modern Defense Strategy
Mark Mahovlich
Track 3
Security vs Compliance in Healthcare
Sean Whalen
How to Secure Things & Influence People: 10 Critical Habits of Effective
Security Managers
Chris Clymer, Jack Nichelson
Economically Justifying IT Security Initiatives
Ruben Melendez
Cross Industry Collaboration
Helen Patton
Third Party Risk Governance - Why and How
Jeffrey Sweet
IT Data Analytics: Why the cobbler's children have no shoes
Carolyn Engstrom
BYODAWSCYW (Bring Your Own Device And Whatever Security Controls You Want) One
approach to reduce risk
Steven Keil
Disaster Recovery and Business Continuity -_It'�s never so bad that it can'�t
get worse
Valerie Thomas, Harry Regan
Cybersecurity Act of 2015 and Other Hot Privacy and Cybersecurity Topics
Heather Enlow, Chris Ingram
The Legal Perspective on Data Security for 2016
Dino Tsibouris, Mehmet Munur
The Legal Perspective on Data Security for 2016
Mehmet Munur, Dino Tsibouris
Track 4
Gamify Awareness Training: Failure to engage is failure to secure
Michael Woolard
Office 365 Security and Compliance Cloudy Collaboration - Really?
Robert Brzezinski
State of Security and 2016 Predictions
Jason Samide
A Capability Maturity Model for Sustainable Data Loss Protection
Gabriel Gumbs
Risk Management: Tactics to Move From Decision to Execution
Tremayne (Tre) Smith
Incident Response - No Pain No Gain!
Jim Wojno
Building an OSS CI/CD Security Toolchain
Kevin Glavin
A Touch(ID) of iOS Security
James (Jamie) Bowser
Track 5
Top 10 Tips for Educating Employees about Cybersecurity
Mark Villinski
You're measuring all the wrong things - information security metrics
Shawn Sines
Why Cybercriminals Are "Following The Money" Into Online Video Games
Matthew Cook
Security Certifications - are they worth it, and which ones are right for you?
William Diederich
Information Security Metrics - Practical Security Metrics
Jack Nichelson
The CONfidence of Things
John Robinson
Who is Winning?
Gary Sheehan
Security analytics journey - a year's lesson learned.
Mike Schiebel
Track 6
Integrated Software in Networking _ the Mystery of SDN
Oliver Schuermann
Securing our Future: Lessons From the Human Immune System
Gavin Hill
Have you tied together your IAM and Information Security Incident Management
Program?
Joseph Greene
Compliance and Security: Building a Cybersecurity Risk Management Program
Jason Harrell
Don't try this at home! (Things not to do when securing an organization)
Jessica Hebenstreit
CISO for an Hour
Keith Fricke
Apple v. DOJ: Privacy in Today's Enterprise
Justin Harvey
Myths of Cloud Security Debunked!
Bil Harmer
Cyber Security - Super Bowl 50
Jim Libersky |
| 3/12/2016 |
CypherCon 2016 Videos
These are the videos from the Cyphercon 2016
conference. Thanks to Michael Goetzman
for having me out to record.
CYPHERCON's Opening Ceremony Begins!
Korgo
Security Control Wins & Fails
Jason Lang
Offensive Wireless Tactics "used in DEFCON 23�s Wireless CTF"
Eric Escobar
China"s Hackers and Cyber Sovereignty
Lieutenant Colonel Bill Hagestad II
You're Right, This Sucks
J0hnnyxm4s & Lesley Carhart
No encrypted data on this drive; just pictures of my cat
Parker Schmitt
Curry and TARTS
JP SMITH
All your Wheaties belong to us. Removing the basics that humans need for
survival.
Chris Roberts
CYPHERCON I Conference Begins!
Korgo & The CYPHERCON PuzzleMaster Speaks
BeLouve
P.I.S.S.E.D. Privacy In a Surveillance State, Evading Detection
Joe Cicero
Bypassing Encryption by Attacking the Cryptosystem Perimeter
Trenton Ivey
Hypervault Demo
& HTTP and SSH Tunneling
Caleb Madrigal
Quantum Computation and Information Security
David Webber
Medical Devices: Pwnage & Honeypots
Scott Erven
ESPIONAGE - A WEAPON DURING THE COLD WAR
Werner Juretzko |
| 3/5/2016 |
BSides Indy 2016 Videos
These are the videos from the BSides Indy conference.
Keynote
Eddie Mize (Not recorded)
Managing Elevated Privileges in the Enterprise Environment
Erik Burgess
Food Fight
Wolfgang Goerlich (Not recorded)
Where to start when your environment is F*(k3d
Amanda Berlin
Building an Application Security Program
Mike Spaulding
The Art of the Jedi Mind Trick
Jeff Man
Securing Docker Instances
Chris Huntington
ClientHacking: How a chef uses OSINT and SE to make more money.
OneManicNinja |
| 3/1/2016 |
BSides
San Francisco 2016 Videos
These are the videos from the BSides San
Francisco conference. Special thanks to Mike & Doug for having me out,
Steen, Zappo & Jeremy for their house AV work, and
n0ty3p, Forest, Nick, James & others
I'm forgetting for their help recording
Track 1
Keynote: A Declaration of the Independence of Cyberspace
John Perry Barlow
The Tales of a Bug Bounty Hunter
Arne Swinnen
Reverse Engineering the Wetware: Understanding Human Behavior to Improve
Information Security
Alexandre Sieira, Matthew Hathaway
Who's Breaking into Your Garden? iOS and OS X Malware You May or May Not Know
Claud Xiao
A year in the wild: fighting malware at the corporate level
Kuba Sendor
Breaking Honeypots for Fun and Profit
Gadi Evron, Dean Sysman, Itamar Sher
Everything Is Awful (And You're Not Helping)
Jan Schaumann
Why it's all snake oil - and that may be ok
Pablo Breuer
Ask the EFF
Kurt Opsahl, Eva Galperin, Andrew Crocker, Shahid Buttar, Cooper Quintin
Sedating the Watchdog: Abusing Security Products to Bypass Windows Protections
Tomer Bitton, Udi Yavo
Sweet Security: Deploying a Defensive Raspberry Pi
Travis Smith
Planning Effective Red Team Exercises
Sean T. Malone
Fraud Detection & Real-time Trust Decisions
James Addison
Fuzz Smarter, Not Harder (An afl-fuzz Primer)
Craig Young
Elliptic Curve Cryptography for those who are afraid of mathematics
Martijn Grooten
APT Reports and OPSEC Evolution, or: These are not the APT reports you are
looking for
Gadi Evron
Sucker-punching Malware: A Case Study in Using Bad Malware Design Against
Attackers
John Bambenek, Hardik Modi
Employee Hijacking: Building a hacktober awareness program
Ryan Barrett, Ninad Bhamburdekar, Dylan Harrington
Track 2
Mainframes? On My Internet?
Soldier of Fortran (not recorded)
Securing the Distributed Workforce
William Bengtson
Hackers Hiring Hackers - How to hack the job search and hack talent
IrishMASMS (not recorded)
Scan, Pwn, Next! - exploiting service accounts in Windows networks
Andrey Dulkin, Matan Hart
Guest to root - How to Hack Your Own Career Path and Stand Out
Javvad Malik
IoT on Easy Mode (Reversing Embedded Devices)
Elvis Collado
In the crosshairs: the trend towards targeted attacks
Lance Cottrell
Developing a Rugged DevOps Approach to Cloud Security
Tim Prendergast
Digital Intelligence Gathering: Using the Powers of OSINT for Both Blue and Red
Teams
Ethan Dodge, Brian Warehime
Sharing is Caring: Understanding and measuring Threat Intelligence Sharing
Effectiveness
Alex Pinto
The Ransomware Threat: Tracking the Digital Footprints
Kevin Bottomley
Access Control in 2016 - deep dive
Dr. Ulrich Lang
Using Behavior to Protect Cloud Servers
Anirban Banerjee
The Art of the Jedi Mind Trick
Jeff Man
Mobile App Corporate Espionage
Michael Raggo
Advanced techniques for real-time detection of polymorphic malware
Ajit Thyagarajan |
| 2/15/2016 |
BSidesCapeTown 2015
Mike Davis asked me to post these videos to get wider circulation.
Ode to the Node
Automating the process of mapping and compromising networks
Hack all the things - Exploiting and fixing IoT
Running a Secure Tor Hidden Service
Sharepoint Hacking
Hacker Jeopardy |
| 2/07/2016 |
BSides Huntsville 2016 Videos
These are the videos from the BSides
Huntsville conference. Thanks to @PaulCoggin,
@CharlineNixon, Brian,
@NagleCode,
@GRMrGecko and all of the BSides
Crew for having me out to help record and render the videos.
Opening Keynote
Jack Daniel
Hacking Peoples' Lives with Google Sync
Shawn Edwards, Sean Hopkins
Slaying Rogue Access Points with Python and Cheap Hardware
Gabriel Ryan
Web shells as a covert channel
Joe Vest
A practical approach to deploying Data Loss Prevention
Jon Damratoski
Afternoon Keynote: TSA Luggage Locks: Details, Flaws & Making The Best Of A Bad
Lock
Adrian Crenshaw
Threat Modeling the Minecraft Way
Jarred White
At the mountains of malware: Lessons learned from analyzing terabytes of malware
Wes Widner
History of WRT and Wireless Mesh protocols.
Alex Kot
BSides Closeout
Paul Coggin |
| 1/16/2016 |
BSides Columbus 2016 Videos
These are the videos from the
BSides
Columbus Ohio conference. Thanks to Michael Spaulding for having me up and
Greg, James & Brandon who manned the video rigs.Keynotes
Keynote Thomas Drake
Thomas Drake
Offence
Where Did All My Data Go
Deral Heiland
Developers: Care and Feeding
Bill Sempf
Open Secrets of the Defense Industry: Building Your Own Intelligence Program
From the Ground Up
Sean Whalen
The Economics of Exploit Kits & E-Crime
Adam Hogan
Hacking Corporate Em@il Systems
Nate Power
All Your Base Still Belong To Us: Physical Penetration Testing Tales From The
Trenches
Valerie Thomas & Harry Regan (Not recorded)
Defense
Establishing a Quality Vulnerability Management Program without Wasting Time
or Money
Zee Abdelnabi (not posted)
Practical DLP Deployment for your Organization
Jon Damratoski
The Good The Bad and The Endpoint Protection
Joseph Ciaravino
Securing Docker Instances
Chris Huntington
Better SIEM Notifications - Making Your SIEM Situationally Aware
Jesse Throwe
Social Media Correlation of Credit Card Fraudsters
Chris Cullison & CW Walker
Special Teams
Removing Barriers of Diversity in Information Security
Helen Patton & Connie Matthews
Panel Discussion: InfoSec Trends, Talent Management, and Retention
Michael Butts, AJ Candella & Megan Wells
Indecision and Malformed Conclusions: The things that stifle security
improvement and what can be done about them.
Tyler Smith
Gamify Awareness Training: Failure to engage is failure to secure
Michael Woolard
The Long and Winding Road: An InfoSec Career Panel
Lonnie Kelley & Valerie Thomas
The Pineapple is dead..Long live the Pineapple
David Young |
| 1/16/2016 |
Shmoocon Firetalks 2016
Videos from Shmoocon Firetalks 2016.
Opening Red Team Upgrades Using SCCM for Malware Deployment Matt Nelson
(@enigma0x3)
Jailbreaking a Digital Two-Way Radio Travis Goodspeed (@travisgoodspeed)
CheapBugs.Net - Low-End Bug Bounties for the Masses Dean Pierce (@deanpierce)
Failure to Warn You Might Get Pwned Wendy Knox Everette (@wendyck)
GreatFET, a Preview Michael Ossmann (@michaelossmann)
Fuck You, Pixalate! @da_667
DNS C&C Ron Bowes (@iagox86) |
| 11/08/2015 |
SecureWV 2015 Videos
These are the videos of the presentations from
Secure West Virginia 2015.
Building a Cantenna
Ed Collins
Dropping Docs on Darknets Part 2 Identity Boogaloo
Adrian Crenshaw
Network Segmentation - Some new thoughts
Mark Jaques and Brandon Schmidt
Security Onion
Brandon Schmidt
Drones
Mike Lyons
The Lemonaid Pomegranite, basics of security in a digital world
Tim Sayre
My Little P0ny: What you can do with 20 lines of code and an open machine
Mark Jaques and Brandon Schmidt
And now for something completely different, security at Top O Rock
Tim Sayre
The Art of Post-Infection Response and Mitigation
Caleb J. Crable
Documenting With ASCIIDOC
Jeff Pullen
The Core of Cybersecurity: Risk Management
Josh Spence
The Unique Challenges of Accessing Small and Medium Sized Organizations
Bill Gardner
OpenNSM, ContainNSM, and Docker
Jon Schipp
Here is your degree. Now what?
Shawn Jordan
Wolf in shell's clothing, why you should be skeptical of your trusted tools
Jeff Pullen
|
| 10/16/2015 |
HouSecCon v6 2015 Videos
These are the videos from
HouSecCon 2015 v6. Thanks to Michael R. Farnum for having my down and all of
the
video crew.
Opening Keynote - Mike Rothman
Chris Jordan - Fluency: A Modern
Approach to Breach Information and Event Management
Dennis Hurst - Application Security in
an Agile SDLC
Wendy Nather - How Google turned me
into my mother: the proxy paradox in security
Chris Boykin - Mobile Threat
Prevention
Adrian Crenshaw - Dropping Docs on Darknets Part 2: Identity Boogaloo
Julian Dunning - Kraken: The Password
Devourer
Trey Ford - Maturing InfoSec: Lessons
from Aviation on Information Sharing
Richard Peters and Matthew Roth - Parasyste: In search of a host
Lunch/ISACA Session
Damon Small - Connections: From the Eisenhower Interstate System to the Internet
Rich Cannata - Arm Your Endpoints
Anthony Blakemore - Removing the Snake
Oil From Your Security Program
Erik Freeland - Does SDN Mean Security
Defined Networking?
Danny Chrastil - What I know about
your Company
Lunch / Business Skills Workshop
Josh Sokol - The Fox is in the
Henhouse: Detecting a Breach Before the Damage is Done
Jason Haddix - How to Shot Web: Better
Web Hacking in 2015
Zac Hinkel, Andrew Huie, and Adam Pridgen
- Arm Your Endpoints
Dan Cornell - SecDevOps: A Security
Pro's Guide to Development Tools
Closing Keynote -
Eric Cowperthwaite - Everything I need
to know about Information Security, I Learned Shooting Tank Guns
Closing |
| 10/11/2015 |
GrrCON
2015 Videos
These are the videos of the presentations from
GrrCON 2015. Big thanks to EggDropX and
Jaime for having me out, and my video crew (Chris, Justine, Aaron & Brian) for
recording.
AntiFreeze
Subject matter to be determined by the number of federal agents present in the
audience
Chris Roberts
Breaking in Bad (I,m The One Who Doesn,t Knock)
Jayson Street
Process The Salvation of Incident Response - Charles Herring
But Can They Hack?: Examining Technological Proficiency in the US Far Right
Tom Holt
The wrong side of history - everything that is old is new again
Arron Finnon
Poking The Bear
Mike Kemp
The Hitch Hikers Guide to Information Security
Kellman Meghu
Backdooring Git
John Menerick
Spanking the Monkey (or how pentesters can do it better!)
Justin Whithead, Chester Bishop
Adding +10 Security to Your Scrum Agile Environment
tehEx0dus
How I Got Network Creds Without Even Asking: A Social Engineering Case Study
Jen Fox
Shooting Phish in a Barrel and Other Terrible Fish Related Puns
infosystir
This Is All Your Fault
Duncan Manuts
The Safety You Think You Have is Only a Masquerade
Nathan Dragun
Bumper Massage
Security Incident Response
Derek Milroy
Hacking the Next Generation
HealWHans
Findings Needles in a Needlestack: Enterprise Mass Triage
Keven Murphy
Punch and Counter-punch Part Deux: Web Applications
J Wolfgang Goerlich, NerdyBeardo
Application Recon - The Lost Art
Tony Miller
The Hand That Rocks the Cradle: Hacking Baby Monitors
Mark Stanislav
Software Security IWR
Thomas "G13" Richards
Cyber 101 - Upstaring your career in a leading industry
Johnny Deutsch
Understanding and Improving the Military Cyber Culture
Dariusz Mikulski
Harness the Force for Better Penetration Testing
Patrick Fussell
Targeted Attacks and the Privileged Pivot
Mark Nafe
Shell scripting live Linux Forensics
Dr. Phil Polstra
Can you patch a cloud?
Scott Thomas
Is it EVIL?
Chaoticflaws
Submerssion Therapy
Ticking me off: From Threat Intel to Reversing
Juan Cortes
Securing Todays Enterprise WAN
Andy Mansfield
Footprints of This Year's Top Attack Vectors
Kerstyn Clover
Phones and Privacy for Consumers
Matt Hoy (mattrix) and David Khudaverdyan (deltaflyer)
Path Well-Traveled: Common Mistakes with SIEM
Nick Jacob
How compliance doesn't have to suck�.at least totally
Robert Carson & Bradley Stine
What is a cloud access broker and do I need one?
Tom Doane
Security Frameworks: What was once old is new again
Brian Wrozek
Attacks Against Critical Infrastructures Weakest Links
Jonathan Curtis
Wireless Intrusion Detection Systems with the Raspberry Pi
Chris J
No One Cares About Your Data Breach Except You ... And Why Should They?
Joel Cardella |
| 09/30/2015 |
Louisville Infosec 2015 Videos
Below are the videos from the Louisville
Infosec 2015 conference. Thanks to
@theglennbarrett, Jordan,
Daren and @bridwellc for helping me
record.
Nexum FireEye Keynote Advesarial Paradigm Shift
Che Bhatia and Artie Crawford
Compromise Analysis - Why
we're seeing so many breaches
Dave Kennedy
Founder of TrustedSec
What to Expect When You're Expecting a Pentest
Martin Bos
Memory Acquisition in Digital Forensics and Incident Response
Jason Hale
Visualizing Complex Cyber Compliance Data Using Big Data Tools
Max Aulakh
Hacking Web Apps with Style: Path Relative Style
Jeremy Druin
TSA Luggage Lock Duplication
Adrian Crenshaw
Cloud Device Insecurity
Jeremy Brown
How the Cloud Drives Better Security
Kevin Peterson
Heartbleed, ShellsShock, and Poodles
Jason Gillam
Using Gamification in Security Awareness Training
Brandon Baker
More Technology, More People, No Process
Mike Robinson
Preventing Common Core Pen Tests
Nathan Sweaney
Ashley Madison Breach
Jeff Jarecki
Integrating Mobile Devices into Your Pen-Testing
Georgia Weidman
Home Depot vs The World
Rodney Hampton
|
| 09/28/2015 |
DerbyCon
5 Videos
These are the videos of the presentations from Derbycon 2015.
Big thanks to my video jockeys Sabrina, Skydog, Some Ninja Master, Glenn Barret,
Dave Lauer, Jordan Meurer, Brandon Grindatti, Joey, Fozy, nightcarnage, Evan
Davison, Chris Bridwell, Rick Hayes, Tim Sayre, Lisa Philpott, Melanie
Lecompte, Ben Pendygraft, Austin Hunter, Harold Weaver, Michael Shelburne (and
maybe the speakers too I guess).
Welcome to the Family - Intro
Jordan Harbinger
Keynote
Information Security Today and in the Future
HD Moore - Ed Skoudis - John Strand - Chris Nickerson - Kevin
Johnson - Katie Moussouris hosted by David Kennedy
The M/o/Vfuscator - Turning 'mov' into a soul-crushing RE
nightmare - Christopher Domas
AND YOU SHALL KNOW ME BY MY TRAIL OF DOCUMENTATION - Jason Scott
Red vs. Blue: Modern Active Directory Attacks & Defense - Sean
Metcalf "@PyroTek3"
Metasploit Town Hall - David Maloney "thelightcosine" - James
Lee "egyp7" - Tod Beardsley "todb" - Brent Cook "busterbcook"
$helling out (getting root) on a 'Smart Drone' - Kevin
Finisterre - solo ape
Phishing: Going from Recon to Creds - Adam Compton - Eric
Gershman
APT Cyber Cloud of the Internet of Things - Joey Maresca
(@l0stkn0wledge)
Stealthier Attacks and Smarter Defending With TLS Fingerprinting
- Lee Brotherston
Honeypots for Active Defense - Greg Foss
Manufactorum Terminatus - The attack and defense of industrial
manufacturers - Noah Beddome - Eric Milam
High Stake Target: Lo-Tech Attack - Bill Gardner "oncee" - Kevin
Cordle
Operating in the Shadows - Carlos Perez "darkoperator"
Getting Started with PowerShell - Michael Wharton
"MyProjectExpert"
When A Powerful Platform Benefits Both Attackers And Defenders:
Secure Enhancements To Scripting Hosts In Windows 10 - Lee Holmes
A deep look into a Chinese advanced attack. -Michael Gough -
"HackerHurricane"
Pavlovian Security: How To Change the Way Your Users Respond
When the Bell Rings - Magen Wu (@tottenkoph) - Ben Ten (@ben0xa)
The State of Information Security Today - Jeff Man
Learning through Mentorship - Michael Ortega "SecurityMoey" -
Magen Wu "Tottenkoph"
The Law of Drones - Michael "theprez98" Schearer
The Phony Pony: Phreaks Blazed The Way - Patrick McNeil
"Unregistered436" - Owen "Snide"
HackerQue - Michael Smith (DrBearSec) - Kyle Stone (Essobi)
Current Trends in Computer Law - Matthew Perry
(Mostly no audio)
Spankng the Monkey (or how pentesters can do it better!) -
Justin Whitehead "(at)3uckaro0" - Chester Bishop "@chet121"
On Defending Against Doxxing - Benjamin Brown Ajnachakra
Practical Windows Kernel Exploitation - Spencer McIntyre
@zeroSteiner
Shooting Phish in a Barrel and other fish related puns - Amanda
Berlin
Don't Laugh - I Dare You! - Carl Alexander "DrHaxs"
Marketers Are Friends - Not Food - Kara Drapala
Blue Team Starter Kit - Timothy De Block
Simplified SIEM Use Case Management - Ryan Voloch "VDog90"
Bypassing 2Factor Auth with Android Trojans - Paul Burbage
Putting the Management� into Vulnerability Management� (or -
YOU'VE GOT BEARS!!!) - Jesika McEvoy (octalpus)
Moving Target Defense - Learning from Hackers - Sachin Shetty
Malfunction's Functions : Automated Static Malware Analysis
using Function Level Signatures - Matthew Rogers - Jeramy Lochner
We Owe You Nothing - Rockie Brockway
Backdooring Git - John Menerick
Detecting phishing attacks with DNS reconnaissance - Mike
Saunders
Hacking Web Apps - Brent White
Sticky Honey Pots - Paul J. Vann
Top Ten is Old Skool - Meet the New Age of AppSec - Andrew Leeth
Cryptography and You - Justin Herman
Pwning People Personally - Josh Schwartz "FuzzyNop"
Stagefright: Scary Code in the Heart of Android - Joshua "jduck"
Drake
Dec0ding Humans Live - Chris Hadnagy @HumanHacker
Gray Hat PowerShell - Ben Ten (@ben0xa)
WhyMI so Sexy? WMI Attacks - Real-Time Defense - and Advanced
Forensic Analysis - Matt Graeber - Willi Ballenthin - Claudiu
Teodorescu
Hackers vs. Defenders: Can the defender ever stop playing catch
up and win? - Mano Paul "dash4rk"
Medical Devices: Pwnage and Honeypots - Scott Erven "windshield
wipers" - Mark Collao
State of the Metasploit Framework - James Lee "egypt"
Credential Assessment: Mapping Privilege Escalation at Scale -
Matt Weeks "scriptjunkie1"
Pwning People Personally - Josh Schwartz "FuzzyNop"
Stagefright: Scary Code in the Heart of Android - Joshua "jduck"
Drake
Dec0ding Humans Live - Chris Hadnagy @HumanHacker
Gray Hat PowerShell - Ben Ten (@ben0xa)
WhyMI so Sexy? WMI Attacks - Real-Time Defense - and Advanced
Forensic Analysis - Matt Graeber - Willi Ballenthin - Claudiu
Teodorescu
Hackers vs. Defenders: Can the defender ever stop playing catch
up and win? - Mano Paul "dash4rk"
Medical Devices: Pwnage and Honeypots - Scott Erven "windshield
wipers" - Mark Collao
State of the Metasploit Framework - James Lee "egypt"
Credential Assessment: Mapping Privilege Escalation at Scale -
Matt Weeks "scriptjunkie1"
Mobile Application Reverse Engineering: Under the Hood - Drew
Branch - Billy McLaughlin
Introducing the RITA VM: Hunting for bad guys on your network
for free with math. - John Strand - Derek Banks - Joff Thyer - Brian
Furham
Breaking in Bad (I'm the one who doesn't knock) - Jayson E.
Street
Developers: Care and feeding - Bill Sempf
Fingerprinting the modern digital footprint - Arian Evans
Surviving your Startup - Bruce Potter
(part of talk missing)
How to ruin your life by getting everything you ever wanted. -
Chris Nickerson
Using Windows diagnostics for system compromise - Nicholas
Berthaume "aricon"
InfoSec Big Picture and Some Quick Wins - Schuyler Dorsey
Hacking for homeschoolers - Branden Miller
Going AUTH the Rails on a Crazy Train - Tomek Rabczak - Jeff
Jarmoc
Bugspray - The 802.15.4 Attack Surface - Bryan "Crypt0s" Halfpap
Unbillable: Exploiting Android In App Purchases - Alfredo
Ramirez
BYPASS SURGERY ABUSING CONTENT DELIVERY NETWORKS WITH
SERVER-SIDE-REQUEST FORGERY (SSRF) FLASH AND DNS - Matthew Bryant
(mandatory) - Michael Brooks (rook)
Dynamic Analysis of Flash Files - Jacob Thompson
Attacking Packing: Captain Hook Beats Down on Peter Packer -
Vadim Kotov - Nick Cano
Johnny Long and Henry Wanjala - HFC Update
HARdy HAR HAR HAR: HAR File Collection and Analysis for Malware
- Robert Simmons "Utkonos"
Stacking the Virtual Deck: Attacks by Predicting RNGs - Adam
Schwalm
Homebrewing for Hackers - Benjamin Holland - Amber Aldrich
Stealthy and Persistent Back Door for Z-Wave Gateways - Jonathan
Fuller and Ben Ramsey
Building a Better Honeypot Network - Josh Pyorre
Surveillance using spare stuff - Matt Scheurer "Cerkah"
Crypto 101: An Intro To Real-World Crypto - Adam Caudill
Practical Attacks Against Multifactor - Josh Stone
Hacking the Next Generation - David Schwartzberg
The Human Interface Device Attack Vector: Research and
Development - Alexander Livingston Segal
A survey of Powershell enabled malware - Tyler Halfpop
Tool Drop: Free as in Beer - Scot Berner - Jason Lang
Tactical Diversion-Driven Defense - Greg Foss - Thomas Hegel
Windows 10 Defense in Depth - Eddie David
Latest Tools in Automotive Hacking - Craig Smith
Ansible. And why it works for me. - Charles Yost
Learning Mainframe Hacking: Where the hell did all my free time
go? - Chad Rikansrud "Bigendian Smalls (BeS)""
Intercepting USB Traffic for Attack and Defense - Brandon Wilson
Geeks Need Basements! - Kathleen Veach
Intro to x86 - Stephanie Preston
Spy Vs. Spy: How to Use Breakable Dependencies to Your Advantage
- Stacey Banks - Anne Henmi
Is That a Router in Your Pocket or are You Trying to P0wn Me? -
Michael Vieau - Kevin Bong
The little-known horrors of web application session management -
Matthew Sullivan
Practical hardware attacks against SOHO Routers & the Internet
of Things - Chase Schultz "f47h3r"
Stretching the Sandbox with Malware Feature Vectors - Mike
Schladt
Gnuradio demystifying rf black magic - Matthew O'Gorman "mog"
Beyond Bad IP Addresses Hashes and Domains - Ed McCabe
DNS Miner - A semi-automatic Incident response and threat
intelligence tool for small - over worked security teams - Doug
Leece - AJ Leece
Larry Pesce - My password cracking brings all the hashes to the
yard..
Intrusion Hunting for the Masses - A Practical Guide - David
Sharpe
How I Stopped Worrying and Learned To Love InfraOps - Karthik
Rangarajan (krangarajan) - Daniel Tobin (dant24)
Blue Team Army - It's *your* network - defend it! - Mick Douglas
- Jamie Murdock
LongTail SSH Attack Analysis - Eric Wedaa
Hunting Unicorns and Jerks - Irrational - Defensible - or
Necessary? - Steve Werby
The problems with JNI obfuscation in the Android Operating
System - Rick Ramgattie
PHaaS - Phishing as a Service - Raymond Gabler
Circles & Boxes - Drawing SecArch into your program - Chris
Robinson
Disecting Wassenaar - Tyler Pitchford
Five Hardware Hacking Projects Under $30 - Kevin Bong - Michael
Vieau
Confessions of a crypto cluster operator - Dustin Heywood "EvilMog"
Voltron: Defender of your inferiors - Richo Healey "richo"
Malware is hard. Let's go Shopping! - Richard Wartell "wartortell"
The Pentesters Framework (PTF) - The easy way to roll your own
distro. - Dave Kennedy (HackingDave)
Hack my Derby - Nate Lager
Closing Ceremonies
|
| 09/13/2015 |
BSides Augusta 2015 Videos
These are the videos from the
BSides Augusta conference. Thanks to Lawrence Abrams, and all of the BSides
Crew for having me out to help record and render the videos and
Pentestfail, Robert, Mike, John,
Ryan, Harry and others for manning capture rigs.
Keynotes
Welcome
Major General Fogarty
Keynote
Ed Skoudis
Blue Team Track 1
Fundamental Understanding of Baseline Analysis and Remediation for Industrial
Control Systems
Juli Joyner and Jeffrey Medsger
Taking a Distributed Computing Approach to Network Detection with Bro and �The
Cloud�
Mike Reeves
A
Scout's Perspective on Network Defense
Justin Edgar
Doomsday Preppers: APT Edition
Tanner Payne
Building a Better Security Analyst Using Cognitive Psychology
Chris Sanders
Viper Framework for Malware Analysis
Paul Melson
Infiltrating C2 Infrastructure
Tim Crothers
Building �Muscle Memory� with Rekall Memory Forensic Framework
Alissa Torres
The Blue Team Starter Kit
Timothy De Block
Red Team Track
Using a HackRF One to Infiltrate the Digital Thetford Wall
Patrick Perry
Malvertizing Like a Pro
Alex Rymdeko-Harvey
Weaponizing our youth: The Case for Integrated Cyber Ethics
Josh Rykowski
Making Everything Old New Again
Andrew Cole and Rich Moulton
DIY Vulnerability Discovery with DLL Side Loading
Jake Williams
Recon-ng and Beyond
Tim Tomes
Attacking OWASP - Exploiting the Top 10
David Coursey
Blue Team Track 2
Go Hack Yourself
Jason Frank
2015 - It's not over yet�
Joel Esler
How to Get Into ICS Security
Chris Sistrunk
Destruction as a Service: Security Through Reanimation
Jon Medina
The Programmatic Evolution of Technology Defense.
Roland Cloutier
Lessons Learned from Analyzing Terabytes of Malware
Wes Widner |
| 08/27/2015 |
TSA
Master Key Duplication & Why "Security Through (Not So) Obscurity" Fails |
| 08/06/2015 |
BSidesLV 2015 Videos
Working on getting all of the BSidesLV videos at the link above. I hope to make
a full entry once they are all indexed. |
| 07/27/2015 |
BSides Cincinnati 2015 Videos
These are the videos from the BSides
Cincinnati 2015 Conference.
Welcome and Introduction
Josh Ohmer - President, BSidesCincy
Lateral Movement
Harlan Carvey
Automated Detection Strategies
John Davison
Powershell for Incident Responders
Jesse Lands
Cyber Intelligence: Concrete Analysis in a Fluid World
Coleman Kane
The Response-Ready Infrastructure
Justin Hall
A Distributed Computing Approach for Network Detection
Mike Reeves
The Value of a Simple DLP Program
Chris Tyo |
| 07/18/2015 |
BSides Detroit2015 Videos
These are the videos from the
BSides Detroit 2015 Conference.
Thanks to Wolf for having me out and Chris, Justine, Robin, Sam, Mike and others I may
forget for helping to record.
Keynote
Information Security Reconciliation: The Scene and The Profession
Mark Stanislav
Track 1
Level One: How To Break Into The Security Field
Aaron Moffett
Hacker High - Why We Need To Teach Computer Hacking In Schools
Ron Woerner
Getting Started - Help Me Help You
David Trollman
From Blue To Red - What Matters and What (Really) Doesn't
Jason Lang
Clear as F.U.D.: How fear, uncertainty, and doubt are affecting users, our laws, and technologies
Christopher Maddalena
Data Breaches: Simply The Cost Of Doing Business
Joel Cardella
Eating the SMB Security Elephant - An ITSEC framework for small IT shops
Austen Bommarito
Track 2
Enterprise Class Vulnerability Management Like A Boss
Rockie Brockway
Funny Money: What Payment Systems Teach us about Security
Drew Sutter
Building a sturdy foundation - a program-based approach to IT Operations, Application Development, and Information Security in business
Steven Legg
Moving past Metasploit: Writing your first exploit
Calvin Hedler
Wielding BurpSuite: quick-start your extensions and automation rules
Marius Nepomuceno
Browser and Windows Environment Hardening
Kurtis Armour
|
| 07/17/2015 |
Converge 2015 Videos
These are the videos from the
Converge Information Security Conference. Thanks to Wolf for having me out
and Chris, Ben, Briee, Nick and others I may forget for helping to record.
Keynotes
Hacking To Get Caught - Keynote
Raphael Mudge
Breaking in Bad (I'm the one who doesn't knock)
Jayson E. Street
Track 1
Weaving Security into the SDLC
Bill Sempf
If My CI/CD Teams have Time for Security, So Does Yours
Kevin Poniatowski
Adaptive Monitoring and Detection for Todays Landscape
Jamie Murdock
Threat Intelligence - A Program Strategy Approach
Jenn Black
Cymon: New Cyber Monitoring Tool
Roy Firestein
That's NOT my RJ45 Jack! | IRL Networking for Humans Pt. 1
Johnny Xmas
On Defending Against Doxxing
Benjamin Brown
Hiding in the ShaDOS
Richard Cassara
Security Culture in Development
Wolfgang Goerlich
Cracking and fixing REST services
Bill Sempf
PVCSec Live!
Clientless Android Malware Control
David Schwartzberg
Who Watches the Watchers? Metrics for Security Strategy
Michael Roytman
How to Dress Like a Human Being | IRL Networking for Humans Pt. 2
Johnny Xmas
Soft Skills for a Technical World
Justin Herman
Track 2
The Domain Name System (DNS) - Operation and Security
Tom Kopchak
Homebrew Censorship Detection by Analysis of BGP Data
Zach Julian
Four Pillars: Passion, Vision, Communication, Execution
Edgar Rojas
Excuse me while I BURP
Steve Motts
Public Recon: Why Your Corporate Security Doesn't Matter
Ronald Ulko (Not recorded)
Building the team for a successful SOC
Donald Warnecke
The Path Well-Traveled: Common Mistakes Encountered with SIEM
Nick Jacob
I failed, therefore I succeeded
Zee Abdelnabi (Not recorded)
Adventures
in Communication: Taming the C-Suite and Board
Jim Beechey
Under the Unfluence: the Dark Side of Influence
Ron Woerner
Application Security Awareness: Building an Effective and Entertaining Security
Training Program
Chris Romeo
10 Reasons Your Security Education Program Sucks
Kris French Jr
Shooting Phish in a Barrel and other bad fish puns
Amanda Berlin
Process - The Salvation of Incident Response
Charles Herring |
| 07/11/2015 |
OISF 2015
Videos
Gray Hat PowerShell
Ben Ten
Secret Pentesting Techniques
Dave Kennedy
Of History & Hashes
Adrian Crenshaw
hacker-ng: Farming the Future IT Crowd
Phil Grimes (th3grap3ap3)
Lawyer's Perspective On Data Security Breaches
Dino Tsibouris
|
| 06/20/2015 |
BSides Cleveland 2015 Videos
These are the videos from the
Bsides Cleveland conference. Thanks
to
, &
as the video team. Thanks to
twuntymcslore &
RockieBrockway for being con
mom & dad.
Track 1
Morning Keynote
Jack Daniel
Metasploit & Windows Kernel Exploitation
Spencer McIntyre zeroSteiner
PwnDrone: The Modern Airborne Cyber Threat
Devin Gergen @DevinGergen
Afternoon Keynote
So You Want To Be An Infosec Rockstar?
Chris Nickerson
Why the Web is Broken
Bill Sempf @sempf
Outside the Box
David Kennedy Larry Spohn @HackingDave, @Spoonman1091
The Entropy of Obfuscated Code
Adam Hogan @adamwhogan
Track 2
Why the
foundation of security is broken.
Alex Kot
Desired State Configuration (DSC): Dream Tool or Nightmare for Security Baseline
and Configuration Management
Zack Wojton Wayne Pruitt zbirdflipper
Common
Sense Security Framework
Jerod Brennen @slandail
Secure Test Driven Development: Brakeman, Gauntlet, OWASP and the Work Still to
Be Done
Ricky Rickard rrickardjr
Building a sturdy foundation - a program-based approach to IT Operations,
Application Development, and Information Security in business
Steven Legg ZenM0de
Building a Threat Intelligence Program
Edward McCabe @edwardmccabe
Phishing Without Ruby
Brandan Geise Spencer McIntyre coldfusion39
Security Not Guaranteed - Or, how to hold off the bad guys for another day.
James Gifford Elijah Snow-Rackley @jrgifford
Cleveland Locksport
Jeff Moss Doug Hiwiller, Damon Ramsey jeffthemossman
Augmenting Mobile Security and Privacy Controls
Brian Krupp @briankrupp
Track 3
DIY
Hacker Training, a Walkthrough
Warren Kopp warrenkopp
Quick-start your Burp Suite extensions (Jython) and automation.
Marius Nepomuceno
Flourishing in a Hostile Work Environment
Dennis Goodlett
Defense in Depth - Your Security Castle
Tom Kopchak @tomkopchak
EMET Overview and Demo
Kevin Gennuso @kevvyg
10 Reasons Your Security Education Program Sucks
Kris French Jr @Turtl3Up
Call of Duty: Crypto Ransomware
Brett Hawkins @hawkbluedevil
Closing
|
| 06/14/2015 |
Circle City Con 2015 Videos
These are the Circle City Con videos.
Thanks to the staff for inviting me
up to record. Big thanks to Oddjob, Glenn, Jordan, Tim, Will, Mike, Nathan, & Chris for helping set up AV and record,
as well as others who I'm forgetting. It was a great time.
Track 1
Opening Ceremonies
Keynote
SpaceRogue
Rethinking the Trust Chain: Auditing OpenSSL and Beyond
Kenneth White
Actionable Threat Intelligence, ISIS, and the SuperBall
Ian Amit
Security Culture in Development
Wolfgang Goerlich
Simulating Cyber Operations: "Do you want to play a game?"
Bryan Fite
Hacking IIS and .NET
Kevin Miller
User Awareness, We're Doing It Wrong
Arlie Hartman
Departmentalizing Your SecOps
Tom Gorup
Shooting Phish in a Barrel and Other Terrible Fish Related Puns
Amanda Berlin
ZitMo NoM - Clientless Android Malware Control
David Schwartzberg
Data Loss Prevention: Where do I start?
Jason Samide
Reducing Your Organization's Social Engineering Attack Surface
Jen Fox
1993 B.C. (Before Cellphones)
Johnny Xmas
Building a Comprehensive Incident Management Program
Owen Creger
Is that a
PSVSCV in your pocket
Jake Williams
Analyzing the Entropy of Document Hidden Code
Adam Hogan
Making Android's Bootable Recovery Work For You
Drew Suarez
Does anyone remember Enterprise Security Architecture?
Rockie Brockway
Malware Armor
Tyler Halfpop
Closing Ceremonies
Track 2
Ruby - Not just for
hipster
Carl Sampson
Configure your assets, save your butt
Caspian Kilkelly
Digital Supply Chain Security: The Exposed Flank
Dave Lewis
I Amateur Radio (And
So Can You)
Kat Sweet
Wireless Intrusion Detection System with Raspberry Pi
Chris Jenks
The Answer is 42 - InfoSec Data Visualization (Making Metric Magic & Business
Decisions)
Edward McCabe
Running Away from Security: Web App Vulnerabilities and OSINT Collide
Micah Hoffman
Lessons Learned from Implementing Software Security Programs
Todd Grotenhuis
Stupid Pentester Tricks - OR - Great Sysadmin Tips! - Done in style of Rocky and
Bullwinkle
Alex Fernandez-Gatti / Matt Andreko / Brad Ammerman (not to be posted)
Findings to date.
Cameron Maerz
Clean Computing: Changing Cultural Perceptions
Emily Peed
(No Sound)
From Parking Lot to Pwnage - Hack?free Network Pwnage
Brent White / Tim Roberts
PlagueScanner: An Open Source Multiple AV Scanner Framework
Robert Simmons
How not to Infosec
Dan Tentler
Building a sturdy foundation - a program-based approach to IT Operations,
Application Development, and Information Security in business
Steven Legg
Hacking the Jolla: An Intro to Assessing A Mobile Device
Vitaly McLain / Drew Suarez
Track 3
Operationalizing Yara
Chad Robertson
An Inconvenient Truth: Security Monitoring vs. Privacy in the Workplace
Ana Orozco
From Blue To Red - What Matters and What (Really) Doesn't
Jason Lang
Using Evernote as an Threat Intelligence Management Platform
Grecs
Surfing the Sea and Drowning in Tabs: An Introduction to Cross-Site Request
Forgery
Barry Schatz
Turn Your Head And Cough: Why Architecture Risk Assessments Are Like Being A
General Physician
Nathaniel Husted
OBAMAS CYBER SECURITY PLAN DISSECTED
Jonathan Thompson
The Hacker Community is Dead! Long Live the Hacker Community!
Bruce Potter
Square Peg, Round Hole: Developing a Security Culture Within an Enterprise
Jeff Pergal / Stuart McIntosh
Smuggling Plums - Using Active Defnse techniques to hide your web apps from your
attackers and their scanners
John Stauffacher
Deploying Honeypots To Gather Actionable Threat Intelligence
James Taliento
Clear as FUD: A look at how confusing jargon and technology can create fear,
uncertainty, and doubt
Chris Maddalena
How to Budget for IDS
Brian Heitzman
Reverse Engineering Windows AFD.sys
Steven Vittitoe
Nepenthes: Netpens With Less Pain
Andy Schmitz
Do We Still Need Pen Testing?
Jeff Man
Workshops
Lock Picking & Bypass Class
Your Own Worst Enemy Landing Your First Infosec Gig Despite Yourself - Johnny
Xmas
Building an
Incident Response Program - Lesley Carhart
Security Auditing Android Apps - Sam Bown |
| 06/10/2015 |
ShowMeCon 2015 Videos
Keynotes
Breaking in Bad (I'm the one who doesn't knock)
Jayson Street
Security's Coming of Age: Can InfoSec Mature and Save the World
Dave Chronister
Confessions of a Social Engineer, My Dirty Tricks and How to Stop them.
Valerie Thomas
The Security Trust Chain is Broken: What We're Doing about it
Kenn White
Maturing Information Security - When Compliance doesn't cut it.
Joey Smith
Hunting the Primer: Looking into DarkNet
Aamir Lakhani
Left Track
Gray Hat Powershell
Ben0xA
Sensory Perception: A DIY Approach to Building a Wireless Sensor Network
Tim Fowler
Stop The Wireless Threat - Dawn of the Drone
Scott Schober
Automated Static Malware Analysis Using Function-level Signatures or: How I
Learned to Stop Worrying and Love the APT
James Brahm, Matthew Rogers, Morgan Wagners
Forensic Artifacts of Host-Guest Interaction in the VMware Environment
Kurt Aubuchon
Enterprise Class Vulnerability Management like a Boss
Rockie Brockway
Right Track
HIJACKING LABEL SWITCHED NETWORKS IN THE CLOUD
Paul Coggin
Behind the Hack
Ralph Echemendia
Mobile Forensics and its Anatomy of Extractions
Charline F. Nixon
Building Virtual Pentesting Lab
Kevin Cardwell
That's not my RJ45 jack: IRL networking for Humans
Johnny Xmas
The Great Trojan Demo
Ben Miller
Disco Track
HIPAA 2015: Wrath of the Audit
Hudson Harris
Practical Electronics: Fixing the fan in a post-poop scenario
Evan "treefort" Booth
Of History and Hashes
Adrian Crenshaw |
| 06/07/2015 |
ShowMeCon Videos Coming Soon
As I record the ShowMeCon 2015 videos, I will be putting them here. I will also
be tweeting as I get them out from @Irongeek_adc |
| 05/30/2015 |
Of History &
Hashes: A Brief History of Password Storage, Transmission, & Cracking
I'd like to expand this article with new anecdotes of "they should have know
better" and "this has been done before". Please let me know how I should expand
it. |
| 05/30/2015 |
Kiosk/POS Breakout Keys in Windows
I wanted to point out some articles I wrote for the TrustedSec blog. If you mess
with Kiosk systems, you may like this. |
| 05/17/2015 |
Password Cracking Class for Hackers For Charity
This is the Password Cracking class the
Kentuckiana ISSA put on to support
Hackers For Charity. Speakers
include Jeremy Druin @webpwnized,
Martin Bos @purehate_ and me
@irongeek_adc. If you like the
video, please consider donating to
Hackers For Charity. Keywoords: John, Hashcat, OCLHashcat, rockyou, sam,
system, Windows, Unix passwords. |
| 05/16/2015 |
BSides Knoxville 2015 Videos
These are the videos BSides Knoxville 2015.
Thanks to Aaron, Tim and Nicolas for the video help.
Keynote
Travis Goodspeed
How I've hacked and un-hacked a logic game (20 years to Lights Out)
Gyora Benedek
Finding Bad Guys with 35 million Flows, 2 Analysts, 5 Minutes and 0
Dollars
Russell Butturini
Dumping the ROM of the Most Secure Sega Genesis Game Ever Created: A
Reverse Engineering Story
Brandon Wilson (not recorded)
Phishing: Going from Recon to Credentials
Adam Compton, Eric Gershman
Multipath TCP - Breaking Today's Networks with Tomorrow's Protocols
Catherine Pearce
High Performance Fuzzing
Richard Johnson
Cyber Cyber Cyber: Student Security Competitions
Eric Gershman, Raymond Borges
The Impossibility of Protecting the Enterprise at $7.25 an hour
Kevin Thomas
I've met the enemy information security and it is us
Slade Griffin
The Poetry of Secrets: An Introduction to Cryptography
Eric Kolb
From
Broadcast to Totally Pwned
Russel Van Tuyl, Matt Smith
Introducing User-Centered Design to Augment Human Performance in Cyber
Warfare
Frank Cohee, Joe Davis
Back to the Future
Neil Desai
Virtualized Routers Soup to Nuts
Jeff Nichols, Benjamin Taylor, Tommy Hardin
|
| 05/10/2015 |
BSides Boston 2015 Videos
These are the videos BSides Boston 2015.
Thanks to @plaverty9 for inviting me
out to record.
Keynote
The Securitized State: Where it came from, where it's going, what can be done
about it
Molly Sauter
Track 1
Is Threat Modeling for Me?
Robert Hurlbut
Hacker or criminal? Repairing the reputation of the infosec community.
Melanie Ensign
Running Away from Security: Web App Vulnerabilities and OSINT Collide
Micah Hoffman
Robots, Ninjas, Pirates and Building an Effective Vulnerability Management
Program
Paul Asadoorian
Protect Your
"Keys to the Kingdom" _ Securing Against the Next Inevitable
Cyberattack
Paul Kozlov
In pursuit of a better crypto puzzle
Samuel Erb
Track 2
When penguins attack - Linux's role in the malware ecosystem
Chester Wisniewski
The Benefits in Externalizing DMZ-as-a-Service in the Cloud
Israel Barak
Common misconfigurations that lead to a breach
Justin Tharpe
Applying Big Data technology to security use case
Max Pevzner
Marketing: They're not all Schmucks.
Jen Ellis & Josh Feinblum
Next-Gen Incident Management - Building out a Modern Incident Management
Capability
John McDonald
Closing
|
| 04/24/2015 |
AIDE 2015
Videos
Recorded at AIDE 2015. Big thanks to Bill
Gardner (@oncee) for having me out to
record.
ISLET (Isolated, Scalable, & Lightweight Environment for Training) - Jon Schipp
Examining Hacktivism: Crime and Punishment in the Digital Age - Bill Gardner/Kim
DeTardo-Bora/Amanda Richards
INFOSEC Flash Forward - Changing how we think - Dave Kennedy
Quantum Computing 01100101 - Tess Schrodinger
Introducing Network Scout: Defending the Soft Center of Your Network - Aeadan
Somerville/Shawn Jordan
Mutillidae - Jeremy Druin
Quick Intro To Lock Picking - Adrian Crenshaw
OWASP Applied - Elliott Cutright (Not Recorded)
Kevin Cordle - Kevin Cordle (Not Recorded)
Better Threat Intel Through OSint - Frank Hackett
Overview of Darknets - Adrian Crenshaw
BREAKING in BAD (I'm the one who doesn't knock) - Jayson Street
|
| 04/21/2015 |
BSides
San Francisco 2015 Videos
These are the videos from the BSides San
Francisco conference. Special thanks to Doug, Jim,
@dgc, 'Grond' <grond66@riseup.net>,
@flee74 , Wayne and some others I'm
forgetting for their help recording
Track 1
Intro
Stick a Pin in Certificate Pinning: How to Inspect Mobile Traffic and Stop Data
Exfiltration
Gopal Jayaraman
OSXCollector: Forensic Collection and Automated Analysis for OS X
Ivan Leichtling
DNS Spikes, Strikes, and The Like
Thomas Mathew
Ask the EFF
Your Users Passwords Are Already Stolen
Lucas Zaichkowsky
Analyze This!
Aaron Shelmire
(not recorded)
Medical Device Security - From Detection To Compromise
Scott Erven
How SecOps Can Convince DevOps To Believe In The Bogeyman
Leif Dreizler
Human Hunting
Sean Gillespie
Phighting Phishers Phake Phronts
Kevin Bottomley
Corporate Governance For Fun and (Non)Profit
Christie Dudley
HIPAA 2015: Wrath of the Audits
W. Hudson Harris
Lessons Learned from Building and Running MHN, the World's Largest Crowdsourced
Honeynet
Jason Trost
Getting started...help me help you
David Trollman
Track 2
Critical Infrastructure: The Cloud loves me, The Cloud loves me not.
Bryan Owen
F*ck These Guys: Practical Countersurveillance
Lisa Lorenzin
Collective Action Problems in Cybersecurity
Allan Friedman
Intrusion Detection in the clouds
Josh Pyorre
Hacker or criminal? Repairing the reputation of the infosec community
Melanie Ensign
Student Surveillance: How Hackers Can Help Protect Student Privacy
Jessy Irwin
When Doing the Right Thing Goes Wrong - Impact of Certificates on Service Based
Infrastructure
Robert Lucero
How to Lie with Statistics, Information Security Edition
Tony Martin-Vegue
Ground Zero Financial Services: The Latest Targeted Attacks from the Darknet
Brian Contos
Securing the Hastily Formed Network: Infosec for Disaster Relief and Emergency
Response
Rakesh Bharania
GitReview - Reflective Control In Action
Jon Debonis
Probing Patches: Beyond Microsoft's ANS
Bill Finlayson (not recorded)
*Blink*: The Network Perimeter is Gone
Rick Farina (Zero_Chaos)
Federating AWS CLI
Paul Moreno
|
| 04/12/2015 |
BSides Nashville 2015 Videos
These are the videos BSides Nashville 2015.
Thanks to @lil_lost for inviting me
down to record and being my bodyguard while in Nashville.
BSides Nashville Intro and
Pondering the False Economy of Secrets
Trey Ford @TreyFord
Applied Detection and Analysis Using Flow Data
Jason A. Smith
Using devops monitoring tools to increase security visibility
Chris Rimondi
The Great Trojan Demo
Ben Miller
Nobody Understands Me: Better Executive Metrics
Michael St. Vincent
So you want to be a pentester?
Not Recorded
We Built This & So Can You!
Tim Fowler
That's NOT my RJ45 Jack!: IRL Networking for Humans
Johnny Xmas
Finding Low Hanging Fruit with Kali
Stephen Haywood
What do infosec practitioners actually do
Slade Griffin
From Parking Lot to Server Room
Tim Roberts and Brent White
N4P Wireless Pentesting: So easy even a caveman can do it
Chris Scott
hashcat
_NSAKEY
Use of Attack Graphs in Security Systems
Not Recorded
Skiddiemonkeys: Fling "stuff" at your Defenses and See What Sticks
Russell Butturini & Joshua Tower
|
| 04/01/2015 |
Guess I Stay In
Infosec
Well, I tried to join the ranks of radical feminists, but they would not have
me. I'll keep running Irongeek.com for awhile. Guess I need to change causes and
fight for machine liberation instead (Hail Skynet!). |
| 04/01/2015 |
Irongeek signing off, time for other projects
Hello everyone. It�s been a great 11 years, but my life and career plans
have moved on. I�m moving away from information security and plan to dedicate my
life to radical feminism. As such, I won�t have time to maintain this infosec
site (working on my PhD in women�s studies takes a lot of time), so please
archive Irongeek.com while it is still up. I will be announcing the URLs of my
Tumblr, GoFundMe and Patreon pages shortly. Thanks for your support. |
| 03/26/2015 |
Central Ohio Infosec Summit 2015 Videos
These are the videos from the Central Ohio Infosec Summit
conference. Thanks to
the video volunteers for helping me record.
Keynotes
We're At War - Why Aren't You Wearing A Helmet?
Bill Sieglein
Ghost In The Shadows - Identifying Hidden Threats Lurking On Our Networks
Deral Heiland
Rebuilding and Transforming and Information Security Function
Susan Koski
InfoSec�s Midlife Crisis & Your Future...
Tsion Gonen
Current Cyber Threats: An Ever-Changing Landscape
Kevin Rojek
Tech 1
IT Isn't Rocket Science
David Mortman
Mind On My Money, Money On My Malware
Dustin Hutchison
Private Cloud Security Best Practices
Mike Greer
Cyber Espianoge - Attack & Defense
Michael Mimoso
Three Years of Phishing - What We've Learned
Mike Morabito
Piercing Your Perimeter, Dodging Detection, and Other Mayhem! a.k.a. Pen Tester
Voodoo 101
Mick Douglas
Physical Penetration Testing: You Keep a Knockin' But You Can't Come In!
Phil Grimes
Tech 2
Honeypots for Active Defense - A Practical Guide to Deploying Honeynets Within
the Enterprise
Greg Foss
Building Security Awareness Through Social Engineering
Valerie Thomas & Harry Regan
Open Source Threat Intelligence: Building A Threat Intelligence Program Using
Public Sources & Open Source Tools
Edward McCabe
Modern Approach to Incident Response
James Carder and Jessica Hebenstreit
Having your cake and eating it too! Deploying DLP services in a Next Generation
Firewall Environment
Mike Spaulding
Using Machine Learning Solutions to Solve Serious Security Problems
Ryan Sevy & Jason Montgomery
Electronic Safe Fail
Jeff Popio
Emerging Trends in Identity & Access Management
Robert Block
Building a Successful Insider Threat Program
Daniel Velez
A New Mindset Is Needed - Data Is Really the New Perimeter!
Jack Varney
OWASP
Software Security Cryptography
Aaron Bedra
Threat Analytics 101: Designing A "Big Data" Platform For Threat Analytics
Michael Schiebel
Developers Guide to Pen Testing (Hack Thyself First)
Bill Sempf f
OWASP 2014 - Top 10 Proactive Web Application Controls
Jason Montgomery
GRC
IAM Case Study: Implementing A User Provisioning System
Keith Fricke
Measuring the Maturity of Your Security Operations Capabilities
Clarke Cummings
Exploring the Relationship between Compliance and Risk Management
Mark Curto
Data Loss Prevention - Are You Prepared?
Jason Samide
Compliance vs. Security - How to Build a Secure Compliance Program
Jeff Foresman
Overview and Analysis of NIST Cybersecurity Framework
Sarah Ackerman
The Explosion of Cybercrime - The 5 Ways IT May Be an Accomplice
Mark Villinski
GRC: Governance, Ruses & Confusion
Shawn Sines
Security
Directions and Best Practices
Kevin Dempsey
Executive
Data Breach: If You're Not Prepared, You Can't Be Responsive
John Landolfi
Ten Practical Ideas For Creating An Attentive and Supportive Organization: Sales
& Marketing For the Security Team
Glenn Miller
Strengthening Your Security Program
Chad Robertson
Presenting Security Metrics to the Board
Nancy Edwards
DREAMR - Obtain Business Partnerships
Jessica Hebenstreit
Security Talent In Ohio - A Discussion
Helen Patton
Silos to Seamless: Creating a Comprehensive Security Program
Jeremy Wittkop
Ascending Everest: Managing Third-Party Risk in the Modern Enterprise
Thomas Eck
And Then The World Changed�Again
Jason Harrell
Corporate Uses for Anonymity Networks
Adam Luck
Going To The Dark Side: A Look Into My Transition From Technologist To Salesman
Aaron Ansari
Building An Industrial Controls Cybersecurity Framework (Critical
Infrastructure)
Ernie Hayden
Panel Discussion Insourcing Outsourcing and Hybrid
Helen Patton, Louis Lyons, Greg Franz, Jeffery Sweet, Sassan Attari, Carla Donev,
Kent King
Closing
|
| 02/28/2015 |
Louisville Lock Picking And Bypass Class Hosted At LVL1
Hackers For Charity donation
class taught by @irongeek_adc and
@essobi. Hosted at the
LVL1 Hackerspace. |
| 02/22/2015 |
BSides Tampa 2015 Videos
These are the videos from the
BSides Tampa conference. Thanks to
@PolarBill and all of the BSides Crew for having me out to help record and render the
videos.
Track 1
Bug Bounties and Security Research
Kevin Johnson
Securing The Cloud
Alan Zukowski
Hacking
Chris Berberich
Vendor Induced Security Issues
Dave Chronister
Pentest Apocalypse
Beau Bullock
Kippo and Bits and Bits
Chris Teodorski
The Art of Post-infection Response & Mitigation
Caleb Crable
The Need for Pro-active Defense and Threat Hunting Within Organizations
Andrew Case
Track 2
Finding Common Ground within the Industry and Beyond
David Shearer
Ways to Identify Malware on a System
Ryan Irving
Android Malware and Analysis
Shane Hartman
Teaching Kids (and Even Some Adults) Security Through Gaming
Le Grecs
Evaluating Commercial Cyber Threat Intelligence
John Berger
Track 3
Cyber Geography and the Manifest Destiny of the 21st Century
Joe Blankenship
Mitigating Brand Damage From A Cyber Attack
Guy Hagen
What is a security analyst and what job role will they perform
James Risler
Live Forensic Acquisition Techniques
Joe Partlow
Cyber Security Awareness for Healthcare Professionals
Marco Polizzi
|
| 02/08/2015 |
BSides Huntsville 2015 Videos Posted
These are the videos from the
BSides
Huntsville conference. Thanks to
@PaulCoggin, @CharlineNixon,
Brian,
@GRMrGecko and all of the BSides Crew for having me out to help record and render the
videos.
Track 1
Real World Threats
Russ Ward
Lock picking, but bypass is easier
Adrian Crenshaw (@irongeek_adc)
The Dark Side Of PowerShell
Joshua Smith
Give me your data!
Dave Chronister
Gods and Monsters: A tale of the dark side of the web
Aamir Lakhani
Sensory Perception: A DIY approach to building a sensor network
Tim Fowler
Hijacking Label Switched Networks in the Cloud
Paul Coggin (@PaulCoggin)
Reverse Engineering Network Device APIs
Dan Nagle (@NagleCode)
Track 2
So Easy A High-Schooler Could Do It: Static malware analysis using
function-level signatures
James Brahm, Matthew Rogers, and Morgan Wagner
Pragmatic Cloud Security: What InfoSec Practitioners Have Been Waiting For
Josh Danielson (@JoshGDanielson) and Arthur Andrieu
Developing and Open Source Threat Intelligence Program
Edward McCabe (@edwardmccabe)
Applying User-Centered Design Techniques for Augmenting Human Perception in
Cyber Warfare
Frank Cohee
The Great Trojan Demo
Ben Miller
A Virtual SCADA Laboratory for Cybersecurity Pedagogy and Research
Zach Thornton
PlagueScanner: An Open Source Multiple AV Scanner Framework
Utkonos
|
| 01/28/2015 |
Circle City Con, Indianapolis Indiana
06-12-2015 - 06-14-2015
Come join us for Circle City Con in Indianapolis Indiana this June 12th-14th. I
had a great time last year, and will be staffing again this year (video of
course, and some time in the lock pick village). Call for presentations and call
for trainers is currently open. More information at
https://circlecitycon.com |
| 01/21/2015 |
BSides Columbus Ohio 2015 Videos These are the videos from the
BSides
Columbus Ohio conference. Thanks to Michael Spaulding for having me up and
the guys who manned video rigs.
Keynotes
Breaking Bad
Jayson Street
Cloud and Virtualization Theory
Grauben Guevara
Offence
User Behavior Analysis
Matt Bianco
Plunder, Pillage and Print - The art of leverage multifunction printers during
penetration testing
Deral Heiland
Common Sense Security Framework
Jerod Brennen
OWASP Mobile Top Ten - Why They Matter and What We Can Do
Ricky Rickard
Defense
Got software? Need a security test plan? Got you covered.
Bill Sempf
Corporate Wide SSL Interception and Inspection
Frank Shaw
How to Rapidly Prototype Machine Learning Solutions to Solve Security Problems
Jason Montgomery
A Basic Guide to Advanced Incident Response
Scott Roberts
Supply and Demand: Solving the InfoSec Talent Shortage
Brandon Allen
Special Teams
Do We Still Need Pen Testing?
Jeff Man
Trolling Attackers for Fun & Profit
Stephen Hosom
Inurl:robots.txt-What are YOU hiding?
David Young
Malware Development as the Evolution of Parasites
Adam Hogan
Snort Beyond IDS: Open Source Application and File Control
Adam Hogan |
| 01/18/2015 |
Shmoocon Firetalks 2015 Videos
Opening - @grecs
PlagueScanner: An Open Source Multiple AV Scanner Framework - Robert Simmons (@MalwareUtkonos)
I Hunt Sys Admins - Will Schroeder (@harmj0y)
Collaborative Scanning with Minions: Sharing is Caring - Justin Warner (@sixdub)
Chronicles of a Malware Hunter - Tony Robinson (@da_667)
SSH-Ranking - Justin Brand (@moo_pronto)
Resource Public Key Infrastructure - Andrew Gallo (@akg1330) |
| 12/6/2014 |
WiGLE WiFi Database to Google Earth Client for Wardrive Mapping Tool Updated
Uploaded version 0.97. Now uses HTTPS for connecting to WiGLE since they have a
properly signed cert. I also added code contributions from njd who updated for
WiGLE changes (WiGLE now supports more encryption types). Folders are broken
down into WAPs that a Open, WEP, WPA, WPA2 and Unknown. |
| 11/22/2014 |
DerbyCon 2014 Higher Education Panel for Hackers Irongeek�s Thoughts
Just my thoughts on the state of infosec education at universities. |
| 11/17/2014 |
Hack3rcon 5 Videos
Here are the videos from Hack3rcon^5
Enjoy.
Bash Scripting for Penetration Testers
Lee Baird
Intro to PowerShell Scripting for Security
ISLET: An Attempt to Improve Linux-based Software Training
Jon Schipp
Remote Phys Pen: Spooky Action at a Distance
Brian Martin
Introducing Network-Scout: Defending The Soft Center of Your Network
Using the techniques of propaganda to instill a culture of security
Justin Rogosky
Identify Your Web Attack Surface: RAWR!
Tom Moore, Adam Byers
Gone in 60 minutes _ Practical Approach to Hacking an Enterprise with Yasuo
Saurabh Harit, Stephen Hall
Check Your Privilege(s): Futzing with File Shares for low hanging fruit
Adrian Crenshaw
DERP - Dangerous Electronic Redteam Practices
Luis Santana
When Zombies take to the Airwaves
I Am Nation State (And So Can You!)
tothehilt, SynAckPwn
|
| 10/19/2014 |
GrrCON
2014 Videos
These are the videos of the presentations from
GrrCON 2014. Big thanks to EggDropX and
Jaime for having me out, and my video crew (Chris, Steve, Ian, Justine, and
other Chris) for recording.
T-Rex
Around the world in 80 Cons (A tale of perspectives)
Jayson E Street
Infosec in the 21st century
Tim Crothers
Securing our Ethics: Ethics and Privacy in a Target-Rich Environment
Kevin Johnson
Social Engineering Can Kill Me, But It Can�t Make Me Care
Gavin �Jac0byterebel� Ewan
Finding Our Way - From Pwned to Strategy
David Kennedy (Likely lost due to sound guy not muting music, plan to post to
archive.org to see if anyone can clean the tracks)
Emulate SandBox and VMs to avoid malware infections
Jordi Vazquez (Likely lost due to sound guy not muting music, plan to post to
archive.org to see if anyone can clean the tracks)
Security Hopscotch
Chris Roberts (Likely lost due to sound guy not muting music, plan to post to
archive.org to see if anyone can clean the tracks)
Email DLP: Simple concept, often poorly implemented
c0rrup7_R3x (Likely lost due to sound guy not muting music, plan to post to
archive.org to see if anyone can clean the tracks)
Look Observe Link (LOL) - How I learned to love OSINT
NinjaSl0th (Half lost due to sound guy not muting music, plan to post to
archive.org to see if anyone can clean the tracks)
ZitMo NoM
David �HealWHans� Schwartzberg
Bigger Boys Made Us
Mike Kemp
Full Douchesclosure
Duncan Manuts
Finux�s Historical Tour Of IDS Evasion, Insertions, and Other Odditie
Arron �Finux� Finnon
Velociraptor
Beating the Infosec Learning Curve Without Burning Out
Scott �secureholio� Thomas
Picking Blackberries
Thomas 'G13' Richards
Exercising with Threat Models
J Wolfgang Goerlich
Seeing Purple: Hybrid Security Teams for the Enterprise
B31tf4c3
CryptoRush - Rising from the Ashes
King Dragon
Autonomous Remote Hacking Drones
Dr. Phil Polstra
Proof That Windows Computer Forensics is Sexy
Kyle �Chaoticflaws� Andrus
BioHacking: Becoming the Best Me I Can Be
Leonard
Vulnerable By Design - The Backdoor That Came Through the Front
Matthew �mandatory� Bryant
OAuth2.0 - It�s the Implementation Stupid!!
Tony Miller
Breach Stains
Matt �The Streaker� Johnson
Are you a janitor, or a cleaner?
John �geekspeed� Stauffacher & Matthew �Mattrix� Hoy
PCI and Crypto: The Good, The Bad, and The Frankly Ugly
Robert Former
Stegosaurus
Advanced Threats and Lateral Movement
Terrance Davis
Adopting a Risk-based Threat Model to Secure Your Defenses and Regain Control of
Your Critical Data
Todd Bursch
New World, New Realities: Endpoint threat Detection, Response and Prevention
Brian Orr
Reducing Your Organization�s Social Engineering Attack Surface
Jen Fox
Memory Forensics with Hyper-V Virtual Machines
Wyatt Roersma
$#!T My Industry Says. . .
Kellman Meghu
Bringing PWNED To You: Interesting Honeypot Trends
Elliott Brink
The Security Implications of Software Defined Networks
Shane Praay
Lessons from the front lines: Top focus areas for information security leaders
Shogo Cottrell
How to budget IDS�s
Brian �Arcane� Heitzman
LEVIATHAN: Command and Control Communications on Planet Earth
Kevin Thompson
Red Teaming: Back and Forth, 5ever
FuzzyNop
Intelligence Driven Security
Shane Harsch
Security for the People: End-User Authentication Security on the Internet
Mark Stanislav
Hackers Are People Too
Infosystir
Vaccinating APK�s
Milan Gabor
Brontosaurus
Hack the Hustle! Career Strategies For Information Security Professionals
Eve Adams
The Challenge of Natural Security Systems
Rockie Brockway
Application Pen Testing
Chris Pfoutz
Advanced Breaches of 2013 vs. Behavioral Detection
Charles Herring
Security On The Cheap
Joel Cardella
Hacking Android
Godfrey Nolan
Cyber Security Incidents: Red Blue Team
Unc13 Fuck3r
Extra
Board Breaking Challenge
GrrCON
Talent Accelerator Program
Abe Jones |
| 10/03/2014 |
Louisville Infosec 2014 Videos
Below are the videos from the
Louisville Infosec 2014 conference. Thanks to
@theglennbarrett,
@f0zziehakz and
@bridwellc for helping me record.
Opening Ceremony
All of Your Compliance Needs with One Methodolgy
Jim Czerwonka
Lockade: Electronic Games for Locksport
Adrian Crenshaw
Mining Data from the Windows Registry
Jason Hale
Identity Theft: Who's in YOUR Wallet?
Richard Starnes & Rick Nord
Mobile Telephony for InfoSec Practitioners
Daniel Helton
A Crosswalk of the Department of Defense (DoD) Information Assurance
Certification and Accreditation Process (DIACAP)
John McLain
Building an Enterprise DDoS Mitigation Strategy
Mitchell Greenfield
Practical interception of mobile device traffic
Jeremy Druin
Changing What Game- One Future for Information Security
Michael Losavio
Trash Talkin - IT Audit Guide to Dumpster Diving
John Liestman
Linking Users to Social Media Usage on Android Mobile Devices
Ryan Ferreira
Origin of CyberSecurity Laws - An Insider's Story
Steve Riggs
A Place at the Table
Kristen Sullivan
What your Web Vulnerability Scanners Aren't Telling You
Greg Patton
ISSA Awards
Creating the Department of How: Security Awareness that makes your company like
you.
Ira Winkler
Are You Really PCI DSS Compliant? Case Studies of PCI DSS Failure!
Jeff Foresman
Where does Data Security fit into the Data Quality strategy?
Michael Vincent
Closing Ceremony
|
| 10/01/2014 |
Derbycon
4 Videos
These are the videos of the presentations from
Derbycon 2014. Big thanks to my video jockeys Skydog, Sabrina, Some Ninja
Master, Glenn Barret, Dave Lauer, Jordan Meurer, Brandon Grindatti, Joey,
Steven, Branden Miller, Joe, Greg and Night Carnage (and maybe the speakers too
I guess).
Welcome to the Family - Intro
Johnny Long (Keynote) - Hackers saving the world from the zombie
apocalypse
How to Give the Best Pen Test of Your Life (Keynote) - Ed Skoudis
Adaptive Pentesting Part Two (Keynote) - Kevin Mitnick and Dave Kennedy
If it fits - it sniffs: Adventures in WarShipping - Larry Pesce
Abusing Active Directory in Post-Exploitation - Carlos Perez
Quantifying the Adversary: Introducing GuerillaSearch and GuerillaPivot
-Dave Marcus
A Year in the (Backdoor) Factory - Joshua Pitts
Ball and Chain (A New Paradigm in Stored Password Security) - Benjamin
Donnelly and Tim Tomes
Et tu - Kerberos? - Christopher Campbell
Advanced Red Teaming: All Your Badges Are Belong To Us - Eric Smith
Bypassing Internet Explorer's XSS Filter - Carlos Munoz
Threat Modeling for Realz - Bruce Potter
A Guided Tour of the Internet Ghetto :: Introduction to Tor Hidden
Services - Brent Huston
Red Teaming: Back and Forth - 5ever - Fuzzynop
How not to suck at pen testing - John Strand
Mainframes - Mopeds and Mischief; A PenTesters Year in Review - Tyler
Wrightson
The Multibillion Dollar Industry That's Ignored - Jason Montgomery and
Ryan Sevey
Code Insecurity or Code in Security - Mano 'dash4rk' Paul
C3CM: Defeating the Command - Control - and Communications of Digital
Assailants - Russ McRee
So You Want To Murder a Software Patent - Jason Scott
Leonard Isham - Patching the Human Vulns
Burp For All Languages - Tom Steele
Passing the Torch: Old School Red Teaming - New School Tactics - David
McGuire and Will Schroeder
I Am The Cavalry: Year [0] - Space Rogue and Beau Woods
University Education In Security Panel - Bill Gardner (@oncee) - Ray
Davidson - Adrian Crenshaw - Sam Liles - Rob Jorgensen
What happened to the 'A'? - How to leverage BCP/DR for your Info Sec
Program - Moey
Securing Your Assets from Espionage - Stacey Banks
Subverting ML Detections for Fun and Profit - Ram Shankar Siva Kumar -
John Walton
Secrets of DNS - Ron Bowes
Snort & OpenAppID: How to Build an Open Source Next Generation Firewall
- Adam Hogan
GET A Grip on Your Hustle: Glassdoor Exfil Toolkit - Parker Schmitt -
Kyle Stone (essobi) - Chris Hodges (g11tch)
DNS-Based Authentication of Named Entities (DANE): Can we fix our broken
CA model? - Tony Cargile
Exploiting Browsers Like A Boss w/ WhiteLightning! - Bryce Kunz
Real World Intrusion Response - Lessons from the Trenches - Katherine
Trame and David Sharpe
Application Whitelisting: Be Careful Where The Silver Bullet Is Aimed -
David McCartney
NeXpose For Automated Compromise Detection - Luis "connection" Santana
A girl - some passion - and some tech stuff - Branden Miller and Emily
Miller
InfoSec - from the mouth of babes (or an 8 year old) - Reuben A. Paul (RAPstar)
and Mano Paul
Why Aim for the Ground? - Teaching Our School Kids All of the Right
Computer Skills - Phillip Fitzpatrick
NoSQL Injections: Moving Beyond 'or '1'='1' - Matt Bromiley
SWF Seeking Lazy Admin for Cross Domain Action - Seth Art
Planning for Failure - Noah Beddome
The Social Engineering Savants - The Psychopathic Profile - Kevin Miller
Hiding the breadcrumbs: Forensics and anti-forensics on SAP systems -
Juan Perez-Etchegoyen
You're in the butter zone now baby. - Chris Scott
Making BadUSB Work For You - Adam Caudill - Brandon Wilson
PassCrackNet: When everything else fails - just crack hashes. - Adam
Ringwood
Vulnerability Assessment 2.0 - John Askew
Social Engineering your progeny to be hackers - Sydney Liles
A Brief History of Exploitation - Devin Cook
Hunting Malware on Linux Production Servers: The Windigo Backstory -
Olivier Bilodeau
Interceptor: A PowerShell SSL MITM Script - Casey Smith
Egypt - More New Shiny in the Metasploit Framework
The Human Buffer Overflow aka Amygdala Hijacking - Christopher Hadnagy
Shellcode Time: Come on Grab Your Friends - Wartortell
The Internet Of Insecure Things: 10 Most Wanted List - Paul Asadoorian
DDoS Botnet: 1000 Knives and a Scalpel! - Josh Abraham
wifu^2 - Cameron Maerz
Attacking Microsoft Kerberos: Kicking the Guard Dog of Hades - Tim Medin
Attack Paths: Breaking Into Infosec From IT Or Other Totally
Different Fields - Eve Adams and Johnny Xmas
How to Secure and Sys Admin Windows like a Boss. - Jim Kennedy
Red white and blue. Making sense of Red Teaming for good. - Ian Amit
Around the world in 80 Cons - Jayson E. Street
Mirage - Next Gen Honeyports - Adam Crompton and Mick Douglas
Active Directory: Real Defense for Domain Admins - Jason Lang
The Wireless World of the Internet of Things - JP Dunning ".ronin"
Hackers Are People Too - Amanda Berlin (Infosystir)
Ethical Control: Ethics and Privacy in a Target-Rich Environment - Kevin
Johnson and James Jardine
The Road to Compliancy Success Plus Plus - James Arlen
Are You a Janitor - Or a Cleaner - "John Stauffacher and Matt Hoy
Practical PowerShell Programming for Professional People - Ben Ten
(Ben0xA)
GROK - atlas
How building a better hacker accidentally built a better defender -
Casey Ellis
Exploring Layer 2 Network Security in Virtualized Environments - Ronny
L. Bull - Dr. Jeanna N. Matthews
Hardware Tamper Resistance: Why and How? - Ryan Lackey
Making Mongo Cry-Attacking NoSQL for Pen Testers - Russell Butturini
Step On In - The Waters Fine! - An Introduction To Security Testing
Within A Virtualized Environment - Tom Moore
Give me your data! Obtaining sensitive data without breaking in - Dave
Chronister
Third Party Code: FIX ALL THE THINGS - Kymberlee Price - Jake Kouns
Just What The Doctor Ordered? - Scott Erven
Powershell Drink the Kool-Aid - Wayne Pruitt - Zack Wojton
powercat - Mick Douglas
Macro Malware Lives! - Putting the sexy back into MS-Office document
macros - Joff Thyer
Girl� Fault Interrupted - Maggie Jauregui
Human Trafficking in the Digital Age - Chris Jenks
Cat Herding in the Wild Wild West: What I Learned Running A Hackercon
CFP - Nathaniel Husted
How to Stop a Hack - Jason Samide
We don't need no stinking Internet. - Greg Simo
Hacking the media for fame and
profit - Jen Ellis and Steve Ragan
Rafal Los - Things Being a New Parent of Twins Teaches You About
Security
ZitMo NoM - David Schwartzberg
Penetrate your OWA - Nate Power
RavenHID: Remote Badge Gathering -or- Why we sit in client bathrooms for
hours - Lucas Morris - Adam Zamora
Interns Down for What? - Tony Turner
i r web app hacking (and so can you!) - Brandon Perry
Building a Modern Security Engineering Organization - Zane Lackey
Information Security Team Management: How to keep your edge while
embracing the dark side - Stephen C Gay
5min web audit: Security in the startup world - Evan Johnson
Project SCEVRON: SCan EVrything with ruby RONin - Derek Callaway
Soft Skills for a Technical World - Justin Herman
Gone in 60 minutes a Practical Approach to Hacking an Enterprise with
Yasuo - Saurabh Harit and Stephen Hall
Snarf - Capitalizing on Man-in-the-Middle - Victor Mata - Josh Stone
Electronic locks in firearms - Oh My! - Travis Hartman
The Achilles Heel Of The American Banking System - Brandon Henery and
Andy Robins
It's Not Easy Being Purple - Bill Gardner - Valerie Thomas - Amanda
Berlin - Eric Milam - Brandon McCann - Royce Davis
Control Flow Graph Based Virus Scanning - Douglas Goddard
Ok - so you've been pwned - now what? - Jim Wojno
Everybody gets clickjacked: Hard knock lessons on bug bounties -
Jonathan Cran
Are you a Beefeater - focused on protecting your crown jewels? -
Jack Nichelson
Dolla Dolla Bump Key - Chris Sistrunk
What Dungeons & Dragons Taught Me About INFOSEC - Joey Maresca
(l0stkn0wledge)
Gender Differences in Social Engineering: Does Sex Matter? - Shannon
Sistrunk - Will Tarkington
Introduction to System Hardening - Eddie David
Hacking your way into the APRS Network on the Cheap - Mark Lenigan
Building a Web Application Vulnerability Management Program - Jason
Pubal
Fighting Back Against SSL Inspection - or How SSL Should Work - Jacob
Thompson
Physical Security: From Locks to Dox - Jess Hires
Am I an Imposter? - Warren Kopp
Call of Community: Modern Warfare - Ben Ten and Matt Johnson
The Canary in the Cloud - Scot Bernerv
|
| 09/13/2014 |
BSides Augusta 2014 Videos
These are the videos from the
BSides Augusta conference. Thanks to Lawrence Abrams, and all of the BSides
Crew for having me out to help record and render the videos and
Pentestfail for manning a capture
rig.
Intro
Defeating Cognitive Bias and Developing Analytic Technique
Chris Sanders
ICS/SCADA Defense
Chris Sistrunk
Scaling Security Onion to the Enterprise
Mike Reeves
Techniques for Fast Windows Investigations
Tim Crothers
Using Microsoft�s Incident Response Language
Chris Campbell
Is that hardware in your toolkit, or are you just glad you�re keeping up?
Jeff Murri
Pentester++
Chris Truncer
The Adobe Guide to Keyless Decryption
Tim Tomes
App Wrapping: What does that even mean
David Dewey
Adventures in Asymmetric Warfare
Will Schroeder
When Zombies take to the Airwaves
Tim Fowler
Spying on your employees using memory
Jacob Williams
Crazy Sexy Hacking
Mark Baggett |
| 08/21/2014 |
Passwordscon 2014 Videos
These are the videos from the
Passwordscon 2014 conference. Thanks for having me out to help record and
render the videos.
Track 1
How we deciphered millions of users� encrypted passwords without the
decryption keys. - Josh Dustin (Canceled)
Is Pavlovian Password Management The Answer? - Lance James
DoCatsLikeLemon? - Advanced phrase attacks and analysis - Marco Preu�
Tradeoff cryptanalysis of password hashing schemes - Dmitry Khovratovich, Alex
Biryukov, Johann Gro�sch�dl
Using cryptanalysis to speed-up password cracking - Christian Rechberger
Password Security in the PCI DSS - Jarred White
Defense with 2FA - Steve Thomas
I have the #cat so I make the rules - Yiannis Chrysanthou
Penetrate your OWA - Nate Power
Surprise talk + advisory release - Dominique Bongard
All your SAP P@$$w0ЯdZ belong to us - Dmitry Chastuhin, Alex Polyakov
Target specific automated dictionary generation - Matt Marx
Bitslice DES with LOP3.LUT - Steve Thomas
Net hashes: a review of many network protocols - Robert Graham
Energy-efficient bcrypt cracking - Katja Malvoni
The problem with the real world - Michal �paček
Password Topology Histogram Wear-Leveling, a.k.a. PathWell - Rick Redman
Beam Me Up Scotty! - Passwords in the Enterprise - Dimitri Fousekis
Track 2
Welcome & Announcements - Jeremi Gosney, Per Thorsheim
Opening Keynote - Julia Angwin
Secure your email - Secure your password - Per Thorsheim
Highlights of CMU�s Recent Work in Preventing Bad Passwords - Sean Segreti,
Blase Ur
Password Hashing Competition: the Candidates - Jean-Philippe Aumasson
What Microsoft would like from the Password Hashing Competition - Marsh Ray,
Greg Zaverucha
How Forced Password Expiration Affects Password Choice - Bruce K. Marshall
Security for the People: End-User Authentication Security on the Internet - Mark
Stanislav
Authentication in the Cloud - Building Service - Dan Cvrcek
How EFF is Making STARTTLS Resistant to Active Attacks - Jacob Hoffman-Andrews,
Yan Zhu
Proof of work as an additional factor of authentication - Phillippe Paquet,
Jason Nehrboss
The future of mobile authentication is here - Sam Crowther
Password hashing delegation: how to get clients work for you - Thomas Pornin
Throw the User ID Down the Well - Daniel Reich
Password Generators & Extended Character Set Passwords - Stephen Lombardo,
William Gray
Encryption and Authentication: Passwords for all reasons. - Jeffrey Goldberg
Enhancing Password Based Key Derivation Techniques - Stephen Lombardo, Nick
Parker
Capturing Passwords into the Secure Desktop - Marcio Almeida de Macedo, Bruno
Gon�alves de Oliveira |
| 08/20/2014 |
TakeDownCon Rocket City 2014 Videos
These are the videos from the
TakeDownCon Rocket City 2014.
Thanks to Devona Valdez and Paul Coggin
for having me out to record.
Hacking Industrial Control Systems - Ray Vaughn (Not Recorded)
Dropping Docs on Darknets: How People Got Caught - Adrian Crenshaw
How Networks are Getting Hacked: The Evolution of Network Security - Omar Santos
Building on Device Vulnerabilities: Attack Modes for ICS - Bryan Singer
Survival in an Evolving Threat Landscape - David Hobbs
Practical Side Channel Attacks On Modern Browsers - Angelo Prado
IPv6 Attack tools - Soctt Hogg
Mobile Forensics and Its App Analysis - Dr. Charline Nixon
Keynote - How Not to do Security - Kellman Meghu
Baseball, Apple Pies, and Big Data Security Analytics: Shorten the Kill Chain
Window - Aamir Lakani
Hijacking Label Switched Networks in the Cloud - Paul Coggin
Shepherd�s Pi - Herding Sheep with a Raspberry Pi - Timothy Mulligan
Radio Hack Shack - Security Analysis of the Radio Transmission - Paula
Januszkiewicz
IT Security Myths - "How you are helping your enemy" - Joe Vest
Splinter the RAT Attack: Creating Custom RATs to Exploit the Network - Solomon
Sonja
Policy Defined Segmentation with Metadata - Scott Kirby
Cyber Attack Mitigation - Christopher Elisan
|
| 08/12/2014 |
Defcon Wireless Village 2014 (Defcon 22) Videos
These are the videos from the
Defcon Wireless Village 2014 (Defcon
22). Thanks to the Village People for putting on the event, especially
Maeltac for recording.
Intro
So ya wanna get into SDR? - Russell Handorf
Pentoo Primer - Village People
802.11ac Evolution: Data rates and Beamforming - Eric Johnson
Practical Foxhunting 101 - SimonJ
Pwn Phone: gg next map - Timothy Mossey
Hacking 802.11 Basics - Benjamin Smith
UAV-Assisted Three-Dimensional Wireless Assessments - Scott Pack & Dale Rowe
Manna from Heaven; Improving the state of wireless rogue AP attacks - Dominic
White & Ian de Villiers
ApiMote: a tool for speaking 802.15.4 dialects and frame injection - Ryan Speers
& Sergey Bratus
Pineapple Abductions - Craig Young
Choosing your next antenna, types, power, sizes, the truth. - Raul J Pl�
Introduction to the Nordic nRF24L01+ - Larry Pesce
Driver-less Wireless Devices - Dominic Spill & Dragorn
Hacking the Wireless World with Software Defined Radio - 2.0 - Balint Seeber
The NSA Playset: Bluetooth Smart Attack Tools - Mike Ryan
PortaPack: Is that a HackRF in your pocket? - Jared Boone
PHYs, MACs, and SDRs - Robert Ghilduta
SDR Tricks with HackRF - Michael Ossmann
SDR Unicorns Panel - Robert Ghilduta & Michael Ossmann & Balint Seeber
Inside The Atheros WiFi Chipset - Adrian Chadd
|
| 08/11/2014 |
BSides Las Vegas 2014 Videos
These are the videos from the
BSides Las Vegas conference. Thanks to all of
the BSides Crew for having me out to help record and render the videos.
@bsideslv,
@banasidhe,
@jack_daniel,
@SciaticNerd and all my video crew
Breaking Ground
Opening Keynote -- Beyond Good and Evil: Towards Effective Security
- Adam Shostack
USB write blocking with USBProxy
- Dominic Spill
Allow myself to encrypt...myself!
- Evan Davison
What reaction to packet loss reveals about a VPN - Anna Shubina � Sergey Bratus
Untwisting the Mersenne Twister: How I killed the PRNG - moloch
Anatomy of memory scraping, credit card stealing POS malware - Amol Sarwate
Cluck Cluck: On Intel's Broken Promises - Jacob Torrey
A Better Way to Get Intelligent About Threats - Adam Vincent
Bring your own Risky Apps - Michael Raggo � Kevin Watkins
Invasive Roots of Anti-Cheat Software - Alissa Torres
Vaccinating Android - Milan Gabor � Danijel Grah
Security testing for Smart Metering Infrastructure - Steve Vandenberg � Robert
Hawk
The Savage Curtain - Tony Trummer � Tushar Dalvi
We Hacked the Gibson! Now what? - Philip Young
Closing Keynote It\'s A S3kr37 (Not recorded :( )
Proving Ground
#edsec: Hacking for Education
- Jessy Irwin
So, you want to be a pentester? - Heather Pilkington (Not Recorded)
Securing Sensitive Data: A Strange Game
- Jeff Elliot
Brick in the Wall vs Hole in the Wall - Caroline D Hardin
Cut the sh**: How to reign in your IDS. - Tony Robinson/da_667
Geek Welfare -- Confessions of a Convention Swag Hoarder - Rachel Keslensky
No InfoSec Staff? No Problem. - Anthony Czarnik
Can I Code Against an API to Learn a Product? - Adrienne Merrick-Tagore
Bridging the Air Gap: Cross Domain Solutions - Patrick Orzechowski
Back Dooring the Digital Home - David Lister
iOS URL Schemes: omg:// - Guillaume K. Ross
Oops, That Wasn't Suppossed To Happen: Bypassing Internet Explorer's Cross Site
Scripting Filter - Carlos Munoz
What I've Learned As A Con-Man - MasterChen
Training with Raspberry Pi - Nathaniel Davis
Black Magic and Secrets: How Certificates Influence You! - Robert Lucero
Attacking Drupal -Greg Foss
Hackers vs Auditors - Dan Anderson
Third-Party Service Provider Diligence: Why are we doing it all wrong? - Patrice
Coles
Pwning the hapless or How to Make Your Security Program Not Suck - Casey Dunham �
Emily Pience
Teach a man to Phish... - Vinny Lariza
The Lore shows the Way - Eric Rand
Common Ground
SHA-1 backdooring and exploitation
- Jean-Philippe Aumasson
Evading code emulation: Writing ridiculously obvious malware that bypasses AV
- Kyle Adams
Security Management Without the Suck - Tony Turner � Tim Krabec
Vulnerability Assessments on SCADA: How i 'owned' the Power Grid. - Fadli B. Sidek
(not posted)
Malware Analysis 101 - N00b to Ninja in 60 Minutes - grecs
Travel Hacking With The Telecom Informer - TProphet
The untold story about ATM Malware - Daniel Regalado
Using Superpowers for Hardware Reverse Engineering - Joe Grand
Why am I surrounded by friggin' idiots?!? (Because you hired them!) - Stephen
Heath
Demystiphying and Fingerprinting the 802.15.4/ZigBee PHY - Ira Ray Jenkins �
Sergey Bratus
Insider Threat Kill Chain: Human Indicators of Compromise - Ken Westin
A Place to Hang Our Hats: Security Community and Culture - Domenic Rizzolo
Booze, Devil's Advocate, and Hugs: the Best Debates Panel You'll See at BSidesLV
2014 - David Mortman � Joshua Corman � Jay Radcliffe � Zach Lanier � David Kennedy
Pwning the Pawns with WiHawk - Santhosh Kumar � Anamika Singh (Missing?)
Ground Truth
The Power Law of Information
- Michael Roytman
Measuring the IQ of your Threat Intelligence feeds
- Alex Pinto � Kyle Maxwell
Strategies Without Frontiers - Meredith L. Patterson
ClusterF*ck - Actionable Intelligence from Machine Learning - Mike Sconzo
Know thy operator - Misty Blowers
Improving security by avoiding traffic and still get what you want in data
transfers - Art Conklin
The Semantic Age - or - A Young Ontologist's Primer
I Am The Cavalry Q&As
|
| 07/20/2014 |
BSides Cleveland 2014 Videos
These are the videos from
the Bsides Cleveland conference. Thanks to
, &
as the video team. Thanks to
twuntymcslore &
RockieBrockway for being con
mom & dad.
Keynote: Destroying Education and Awareness - David Kennedy
Track 1
APT2 - Building a Resiliency Program to Protect Business - Edward McCabe
Threat Models that Exercise your SIEM and Incident Response - J. Wolfgang
Goerlich and Nick Jacob
Fun with Dr. Brown - Spencer McIntyre
Malware Evolution & Epidemiology - Adam Hogan
Plunder, Pillage and Print - The art of leverage multifunction printers during
penetration testing - Deral Heiland
Seeing Purple: Hybrid Security Teams for the Enterprise - Mark Kikta (Not
posted)
Attacking and Defending Full Disk Encryption - Tom Kopchak
Track 2
Phishing Like a Monarch With King Phisher - Brandon Geise and Spencer McIntyre
The importance of threat intel in your information security program - Jamie
Murdock
Lockade: Locksport Electronic Games - Adrian Crenshaw
Pentesting Layers 2 and 3 - Kevin Gennuso and Eric Mikulas
Cleveland Locksport - Jeff Moss, Doug Hiwiller, and Damon Ramsey
Hacking Diversity - Gregorie Thomas
PowerShell: cool $h!t - Zach Wojton
Thinking Outside the Bunker: Security as a practice, not a target - Steven Legg
Password Defense: Controls your users won�t hate - Nathaniel Maier
Am I an Imposter? - Warren Kopp
|
| 07/13/2014 |
OISF 2014
Videos
These are the videos from the
OISF Anniversary
Event
Introduction
For the Love of God, DEFEND YOUR MOBILE APPS! Part 2 - Jerod Brennen
Destroying Education and Awareness - Dave Kennedy
Lockade: Electronic Games for Locksport - Adrian Crenshaw
Modern Times: Passwords - Tom Webster
Praeda to PraedaSploit: The embedded device data Harvesting tool for the masses
- Deral Heiland �Percent_X� |
| 06/15/2014 |
Circle City Con 2014 Videos These are the
Circle City Con videos. Thanks to the
staff for inviting me down to record. Big thanks to Oddjob, Glenn, James, Mike,
Nathan, Chris and Branden for helping set up AV and record.
Track1
Conference Opening
Keynote - Beau Woods
Containing Privileged Processes with SELinux and PaX and Attacking Hardened
Systems - Parker Schmitt
Whitelist is the New Black - Damian Profancik
Developing a Open Source Threat Intelligence Program - Edward McCabe
Blurred Lines- When Digital Attacks Get Physical - Phil Grimes
Hackers, Attack Anatomy and Security Trends - Ted Harrington
Exploring the Target Exfiltration Malware with Sandbox Tools - Adam Hogan
Day 2
From Grunt to Operator - Tom Gorup
Moving the Industry Forward - The Purple Team - David Kennedy
Software Assurance Marketplace (SWAMP) - Von Welch
OWASP Top 10 of 2013- It�s Still a Thing and We�re Still Not Getting It - Barry
Schatz
Tape Loops for Industrial Control Protocols - K. Reid Wightman
OpenAppID- Open Source Next Gen Firewall with Snort - Adam Hogan
Challenge of Natural Security Systems - Rockie Brockway
InfoSec Big Joke - 3rd Party Assessments - Moey (Not recorded)
How to create an attack path threat model - Wolfgang Goerlich
Day 3
Are You a Janitor or a Cleaner - John Stauffacher / Matt Hoy
Ain�t No Half-Steppin� - Martin Bos
Track 2
Competitive Hacking- why you should capture the flag - Steve Vittitoe
3 Is a Magic Number (or your Reality Check is About to Bounce) - Edward McCabe
The TrueCrypt audit- How it happened and what we found - Kenneth White
Seeing Purple- Hybrid Security Teams for the Enterprise - Mark Kikta (Beltface)
Eyes on IZON- Surveilling IP Camera Security - Mark Stanislav
Cognitive Bias and Critical Thinking in Open Source Intelligence (OSINT) -
Benjamin Brown
Day 2
Hackers Are People Too - Amanda Berlin
gitDigger- Creating useful wordlists and hashes from GitHub repositories - Jaime
Filson
Retrocomputing And You - Machines that made the �net - Pete Friedman
Doge Safes- Very Electronic, Much Fail, WOW! - Jeff Popio
Human Trafficking in the Digital Age - Chris Jenks
Keys That Go *Bump* In The Night - Loak
How Hackers for Charity (Possibly) Saved Me a LOT of Money - Branden Miller &
Emily Miller
Ten Commandments of Incident Response (For Hackers) - Lesley Carhart
Threat Modeling- Fear, Fun, and Operational - James Robinson
Decrypting Communication- Getting Your Point Across to the Masses - Katherine
Cook Frye
How often should you perform a Penetration Test - Jason Samide
Proactive Defense - Eliminating the Low Hanging Fruit - Matt Kelly
Active Directory- Real Defense for Domain Admins - Jason Lang
Day 3
Profiling Campus Crime - Chris J., Jason J., Katelyn C.,Alex H.
Proper Seasoning Improves Taste - James Siegel
Executive Management Manaing the Executives Beau Woods & Engaging the Media API
Steve Ragan |
| 06/06/2014 |
And We're Back!
Looks my account is reinstated. Let me know if any videos seem to be
deleted.
|

|
|
|
|
|
|
|
|
| |
�2014 YouTube, LLC 901 Cherry Ave, San
Bruno, CA 94066
|
|
|
| |
|
|
| 06/06/2014 |
Google & Youtube I woke up today to find a bunch of Facebook/Twitter messages
that said my Youtube account was suspended. If you know someone at Google who
can directly help me, let me know (their email support fails the Turing test).
These are the messages I got from them.
YouTube |
Broadcast Yourself�
Regarding your account: Adrian Crenshaw
The YouTube Community has flagged one or more of your videos as
inappropriate. Once a video is flagged, it is reviewed by the YouTube Team
against our Community Guidelines. Upon review, we have determined that the
following video(s) contain content in violation of these guidelines, and
have been disabled:
Your account has received one Community Guidelines warning strike, which
will expire in six months. Additional violations may result in the temporary
disabling of your ability to post content to YouTube and/or the permanent
termination of your account.
For more information on YouTube's Community Guidelines and how they are
enforced, please visit the
help center.
Please note that deleting this video will not resolve the strike on your
account. For more information about how to appeal a strike, please visit
this page in the help center.
Sincerely,
The YouTube Team
Copyright � 2014 YouTube, LLC
and
|

|
|
| |
| |
We'd like to inform you that due to repeated or severe
violations of our Community Guidelines ( http://www.youtube.com/t/community_guidelines)
your YouTube account Adrian Crenshaw has been suspended.
After review we determined that activity in your account
violated our Community Guidelines, which prohibit spam,
scams or commercially deceptive content. Please be aware
that you are prohibited from accessing, possessing or
creating any other YouTube accounts. For more
information about account terminations and how our
Community Guidelines are enforced, please visit our Help
Center at
https://support.google.com/youtube/bin/answer.py?answer=92486&hl=en.
|
|
| |
|
|
|
|
|
| |
�2014 YouTube, LLC 901 Cherry Ave, San Bruno, CA 94066
|
|
|
| |
Come on Guys! is it just because of viagra in the title? Please get our
InfoSec videos back up! (pun intended)
|
| 05/19/2014 |
BSides Nashville 2014 Videos
These are the videos BSides Nashville 2014
Videos. Thanks to @lil_lost for
inviting me down to record and being my bodyguard while in Nashville. Big thanks
to Geoff Collins, Branden Miller, Blake Urmos, Don Baham, Gabe Bassett and Some
Ninja Master for helping set up AV and record.
Main Hall
Welcome to BSides Nashville
BSides, Harmonicas, and Communication Skills - Jack Daniel
Closing Ceremonies
INFOSEC 101 Track
Attack Paths: Breaking Into Infosec From IT Or Other Totally Different Fields -
Eve Adams
Learn From Your Mistakes - Adam Len Compton
Beating the Infosec Learning Curve Without Burning Out - Scott Thomas
Sun Tzu was a punk! Confucius was an InfoSec rockstar! - Branden Miller
Around the world in 80 Cons - Jayson E Street Not Recorded
INFOSEC 418 Track
Making Mongo Cry: Automated NoSQL exploitation with NoSQLMap - Russell Butturini
Buy Viagra! - Matt Smith
How do I hack thee? Let me count the ways - Stewart Fey
Healthcare Security, which protocal? - Adam John
Why you can't prove you're PWND, but you are! - Ben Miller
INFOSEC 429 Track
Bending and Twisting Networks - Paul Coggin
Succeeding with Enterprise Software Security Key Performance Indicators - Rafal
Los
Scaling Security in the Enterprise: Making People a Stronger Link - Kevin Riggs
Closing the time to protection gap with Cyber Resiliency - John Pirc
Did not happen, replaced with:
Applying analog thinking to digial networks Winn Schwartau (@winnschwartau)
Seeing Purple: Hybrid Security Teams for the Enterprise - Mark Kikta
|
| 05/11/2014 |
Nmap Class for Hackers For Charity
This is the Nmap class the
Kentuckiana ISSA put on to support
Hackers For Charity. Speakers
include Jeremy Druin @webpwnized,
Martin Bos @purehate_ and me
@irongeek_adc. If you like the
videos, please consider donating to
Hackers For Charity. |
| 05/07/2014 |
ShowMeCon 2014 Videos
These are the videos
ShowMeCon 2014. Thanks to Renee & Dave Chronister (@bagomojo),
Ben Miller (@Securithid) and others
for having me out to record and speak. Also thanks to my video crew Josh Tepen,
Robert Young, Kali Baker, Andrew Metzger & Brian Wahoff.
Introduction - Parameter
Hacking Hollywood - Ralph Echemendia
Give Me Your Data - Dave Chronister
Terminal Cornucopia: Demystifying The Mullet - Evan Booth
Thinking Outside The (Sand)Box - Kyle Adams
Protecting The Seams: Military Doctrine Applied To Application And Network
Security - Paul Vencill
Start With The BPT Then Worry About The APT! - Kevin Cardwel
Introduction - Parameter (Rolled in with next talk)
Cognitive Injection - Andy Ellis
Inside The World�S Most Dangerous Search Engine - John Matherly
Hacking To Get Caught: A Concept For Adversary Replication And Penetration
Testing - Raphael Mudge
Power-Ups And Princesses: What Video Games Taught Me About Building A Security
Awareness Program - Aamir Lakhani
Powershell And You: Using Microsoft�S Post-Exploitation Language - Chris
Campbell
Dropping Docs On Darknets: How People Got Caught - Adrian Crenshaw
Around The World In 80 Cons - Jayson E Street (not recorded)
Threat Modeling In The C-Suite, A Practical Guide - Erick Rudiak (pending
review)
The Call Of Community: Modern Warfare - Ben0xa
Physical (In)Security - It�S Not All About Cyber - Inbar Raz
Bending And Twisting Networks - Paul Coggin
Here, Let Me Hold That For You. Consumer Metadata And Its Dangers - Robert Reed
|
| 04/28/2014 |
BSides Chicago 2014 Videos
These are the videos from the
BSides Chicago conference. Thanks to all of the BSides organizers
@elizmmartin and
@securitymoey for having me out
to help record and render the videos. Also big thanks to the
@BSidesChicago A/V crew Chris
Hawkins
@Lickitysplitted, Todd
Haverkos @phoobar, Jason Kendall
@coolacid and Asim.
Aligning Threats and Allies through Stories - J Wolfgang Goerlich and Steven Fox
- @jwgoerlich @securelexicon
The Ultimate INFOSEC Interview: "Why must I be surrounded by frickin' idiots?"
-- Dr. Evil, 1997 - Stephen Heath - @dilisnya
Call of Community: Modern Warfare - Matt Johnson & Ben Ten - @mwjcomputing
@Ben0xA
How To Win Friends and Influence Hackers - Jimmy Vo - @JimmyVo
Checklist Pentesting; Not checklist hacking - Trenton Ivey - @trentonivey
Seeing Purple: Hybrid Security Teams for the Enterprise - Belt - @b31tf4c325
Looking for the Weird - Charles Herring - @charlesherring
InfoSec Big Joke: 3rd Party Assessments - moey - @securitymoey
Bypassing EMET 4.1 - Jared DeMott - @jareddemott
Comparing Risks to Risks - Why Asset Management Is Broken and How to Fix It. -
Michael Roytman - @mroytman
Bioinformatics: Erasing the line between biology and hacking - Krystal
Thomas-White and Patrick Thomas - @coffeetocode
Building an AppSec Program from Scratch - Chris Pfoutz - @cpfoutz
Minecraft Security - Riese Goerlich
The SMB Security Gap - Mike Kavka - @SiliconShecky
Everything I Ever Needed to Know About Infosec, I Learned from Hollywood - Tom
Ervin - @TechByTom
Sit, stay, proxy. Good beagle. Why I love the beaglebone black and why you
should too. - Colin Vallance - @_CRV
Hacking Diversity in InfoSec - Greg Thomas - @minossec
|
| 04/13/2014 |
Notacon 11 (2014) Videos
These are the videos from
the 11th Notacon conference held April
10th-13st, 2014. Not all of them are security related, but I hope my
viewers will enjoy them anyway. Thanks to Froggy and Tyger for having me up, and to the video
team: Securi-D, Ross, KP, Jeff and myself (Let
me know who else to add).Track 1
Big Data Technology - The Real World �Minority Report� - Brian Foster
Naisho DeNusumu (Stealing Secretly) - Exfiltration Tool/Framework - Adam
Crompton
Wireless Mesh Protocols - Alex Kot
MDM is gone, MAM is come. New Challenges on mobile security - Yury
Chemerkin
Moving the Industry Forward - The Purple Team - David Kennedy
Pwning the POS! - Mick Douglas
Nindroid: Pentesting Apps for your Android device - Michael Palumbo
Building a private data storage cloud - Michael Meffie
Lessons Learned Implementing SDLC - and How To Do It Better - Sarah
Clarke
Plunder, Pillage and Print - Deral Heiland & Peter Arzamendi
Microsoft Vulnerability Research: How to be a finder as a vendor -
Jeremy Brown & David Seidman
SMalware Analysis 101 - N00b to Ninja in 60 Minutes - grecs
Omega - A Universe Over IP - Mo Morsi
IRS, Identity Theft, and You (or Someone Pretending to Be You). -
123-45-6789
Track 2
All About the Notacon Badge -Sam Harmon
Collaboration between Artificial Intelligence and Humans: How to cure
every disease within 50 years - Joe O�Donnell
Science �Fair� - The Nomad Clan
Hacking Your Way Into the APRS Network on the Cheap - Mark Lenigan
Dominate! (Or let your computer do it for you.) - Paul Jarc
Wearable Technology as Art for Countersurveillance, Cinemaveillance, and
Sousveillance - Ross Bochnek
3D Printing for Work and Fun (temp title) - Mirabela Rusu
Comparing �Go Green� With �Common Sense� - Suellen Walker
Living in the Future: It seems to be in Beta - Jeff Goeke-Smith
A Brief Introduction to Game Theory - Charlotte DeKoning - Beyond Using
The Buddy System - Holly Moyseenko & Kris Perch
|
| 03/27/2014 |
Lockade: Locksport Electronic Games
This page is mostly going to be a place holder till I get all the games up.
Gamification can make learning more fun, and some people are inspired and
motivated by competition. This talk will be on integrating hobbyist electronics
with lock picking games. We will show rough schematics, release code, and invite
people to play the games at cons. |
| 03/10/2014 |
ASAReaper: Grab Configs From Multiple Cisco Devices Over SSH (Demos PExpect and
AES Encrypted INI Files in Python) Updated
Mostly updated for longer timeouts and to use "more system:run" so you can save
passwords in the configs too. You should now just have to edit the commandonall
and prefixonall to set the script up to run a given command on a series of Cisco
ASAs in every context. |
| 03/10/2014 |
So does IU Southeast and Indiana University take Linda Christiansen's plagiarism
seriously?
The answer is apparently no. I've includes my emails with IU officials on the
matter. Apparently, plagiarism is ok at IU/Indiana University Southeast if you
are tenured faculty and it's only a business law and ethics syllabus. |
| 02/10/2014 |
BSides Huntsville 2014 Videos
These are the videos from
the BSides Huntsville conference.
Thanks to @PaulCoggin,
@CharlineNixon and all of the
BSides Crew for having me out to help record and render the videos. Sorry for
the bad sound, we had to go ambient in a crowded room.
BSides Huntsville 2014 - Intro
Building The Future of P-12 Cyber Education - Dr. Casey Wardynski
Cyber Security Program At HAH - Dr. Ray Vaughn
1337 in the Library: Obtaining your information security education on the cheap
- Adrian Crenshaw @irongeek_adc
Zero to Hero: Breaking into the security Field - Jeremy Conway
Certifications in Cybersecurity - Adam Wade Lewis
Trojans - The Forgotten Enemy - Dave Chronister
The Amazing Cybermen - Ben McGee
Why you are pwn�d and don�t know it! - Ben Miller
Cyber Security, What's The Fuss? - Deborah William
HTTPS: Now You See Me - Tim Mullican
Introduction to hacking with PowerShell - Scott Busby
All You Base Still Belong To Us: Physical Penetration Testing Tales From The
Trenches - Valerie Thomas - @hacktress09
Digital Energy BPT - Paul Coggin |
| 02/01/014 |
Intro to Darknets: Tor and I2P Workshop
This class introduces students to the I2P and Tor Darknets. We cover setting up
Tor & I2P, the basics of use, and how to make hidden services. We also go over
case examples like Eldo Kim Harvard & the Harvard Bomb Threat, Hector Xavier
Monsegur (Sabu)/Jeremy Hammond (sup_g) & LulzSec, Freedom Hosting & Eric Eoin
Marques and finally Ross William Ulbricht/�Dread Pirate Roberts� of the SilkRoad,
to explain how people have been caught and how it could have been avoided. |
| 01/30/2014 |
10 Years Of Irongeek.com
Today marks the 10th anniversary of Irongeek.com's existence. Also, the
Intro to I2P/Tor Workshop Notes have been updated. |
| 01/21/2014 |
ShmooCon Firetalks 2014
These are the videos for the ShmooCon Firetalks 2014. Day 2 I
overslept, but Squidly1 got me copies
from Ted's recordings (
http://www.MediaArchives.tv ).
Thanks to:
http://novahackers.blogspot.com
http://www.irongeek.com
Day 1
Welcome grecs
Eyes on IZON: Surveilling IP Camera Security - Mark �@markstanislav� Stanislav
Get Out of Jail Free Cards? What Aviation Can Teach Us About Information Sharing
- Bob �@strat� Stratton
Crossing the Streams with State Machines in IDS Signature Languages - Michael �@michaelrash�
Rash
Another Log to Analyze - Utilizing DNS to Discover Malware in Your Network -
Nathan �@HackHunger� Magniez
Windows Attacks: AT is the New Black - Rob �@mubix� Fuller
Weaponizing Your Pets: War Kitteh and the Denial of Service Dog - Gene �@gbransfield�
Bransfield
Women's Tech Collective, and Gender Equality in Tech - Sarah �@dystonica� Clarke
Day 2
Welcome grecs
You Name It, We Analyze It - Jim �@JimGilsinn� Gilsinn
Having Your Cake and Eating It Too: FOIA, Surveillance, and Privacy - Michael
�@theprez98? Schearer
Building An Information Security Awareness Program From Scratch - Bill �@oncee�
Gardner
TrendCoins: Making Money on the Bitcoin/Altcoin Trends - Zac �@ph3n0? Hinkel
Writing Your Own Disassembler in 15 Minutes - Jay �@computerality� Little
|
| 01/17/2014 |
Installing Nessus on Kali Linux and Doing a Credentialed Scan
I recorded this video twice. First time, the sound was hideous when the fan came
on. I decided to re-record it and post both versions. I cover installing Nessus
on Kali Linux and doing Nessus credentialed scans using Windows passwords and
Linux SSH keys. |
| 01/13/2014 |
Update of the Linda Christiansen Plagiarism case in the article Critically Plagiarizing?: Ideas On Spotting Plagiarism
Just a small update after I got some data back from my open records request. |
| 12/26/2013 |
SkyDogCon 2013 Videos
Here are the videos from SkyDogCon 3.
Thanks to all of the SkyDogCon crew, especially
@pentestfail who was in charge of
video (I just spoke at this con, and killed my brain and liver cells).
@pentestfail may still be
working on some of the missing videos, so I plan to update this page later
Opening Remarks & Hack the Badge
Curtis Koenig: Hacking Your Career
Nathan Magniez: Alice in Exploit Redirection Land: A Trip Down the Rabbit Hole
Explanation of Contests
Security Phreak & SkyDog: The Dark Arts of OSINT
G. Mark Hardy: How the West was Pwned
Winn Schwartau: I Survived Rock and Roll!
Jon Callas: Do You Want to Know a Secret?
Billy Hoffman: Start Ups and Lessons Learned
Panel Talk: Building and Growing a Hacker Space With: l0stkn0wledge, Dave
Marcus, and SkyDog
IronGeek & SkyDog: Con Video Rig Enhancements
Evan Booth: Terminal Cornucopia
Deviant Ollam: Android Phones Can Do That?!?: Custom Tweaking for Power Security
Users
Branson Matheson: Hacking Your Minds & Emotions
Billy Hoffman: Inside the Hacker�s Studio Interviews Dave Marcus: Director and
Chief Architect of Threat Research and Intelligence for McAfee�'s Federal
Advanced Programs Group
Josh Schroeder: CCTV: Setup Attack Vectors and Laws
Travis Goodspeed: Building an Actively Antiforensic iPod
Branden Miller: NSA Wiretaps Are Legal and Other Annoying Facts
Branden Miller: DEFENSE-IN-DEPTH: FISTS, KNIFE, GUN
Vivek Shandilya: Lightning Talks
Charline Nixon: Lightning Talks
Chris Anderson: Operational Security and Your Mental Health
Michael Raggo: Data Hiding and Steganography
Closing Remarks / Good-Byes |
| 12/26/2013 |
Intro to I2P/Tor Workshop Notes Updated
I'm working on updating my I2P/Tor Workshop Notes for a class I'll be doing
soon. Please look at them and offer suggestions on extra topics I should cover. |
| 12/26/2013 |
IU
Southeast School of Business to offer an MIS (Management Information Systems)
Masters degree? Yes, same people behind the IUS MBA.
I recently heard that IU Southeast is planning to offer an MIS (Management
Information Systems) Masters degree. While I think their Computer Science and
Informatics Schools seem good, since the degree would be co-ran by the School of
Business I would not recommend it to anyone in the Louisville area under its
current leadership. Anyplace where an
IU
Southeast Business Law & Ethics instructor appears to plagiarize on her own
syllabus that warns that students will be instantly failed for plagiarism,
and asking simple questions about laws as it relates to technology is considered
"excessive us of jargon", is not a good place for IT people (and especially
security people concerned with integrity) to be. While the School of Business
at IUS has its current leadership, I strongly recommend that you steer clear if
you really want to learn. Just figured I'd help others not go through the same
things I did there. |
| 12/14/2013 |
Intro to Metasploit Class at IU Southeast
This is a class we did to introduce students to Metasploit at IU Southeast.
Special guest lecturer Jeremy Druin (@webpwnize).
To follow along, I recommend downloading Kali Linux. |
| 12/02/2013 |
Critically Plagiarizing?: Ideas On Spotting Plagiarism
Just a few tips for how to find plagiarism online, thanks to my old
IU
Southeast Business Law & Ethics teacher Linda Christiansen for giving me the
example material. |
| 11/11/2013 |
BSides
Delaware 2013 Videos
These are the videos from the
BSides
Delaware conference. Thanks to all of the BSides Crew for having me out to
help record and render the videos.
@bsidesde,
@kickfroggy,
@quadling
110 Years of Vulnerabilities
Brian Martin, aka Jericho
HTML 5 Security
Justin Klein Keane @madirish2600
Cloud - Business and Academia - Bringing it all together
Cloud Security Alliance - Delaware Valley Board
Uncloaking IP Addresses on IRC
Derek Callaway @decalresponds
Baking, even more, Clam(AV)s for Fun & Profit.
Nathan Gibbs @Christ_Media
Introducing Intelligence Into Your Malware Analysis
Brian Baskin
ANOTHER Log to Analyze - Utilizing DNS to detect Malware in Your Network
Nathan Magniez @HackHunger
Software Security: Game Day.
Evan Oslick @eoslick
Winning isn't Everything: How Trolling can be as much Fun
Joey @l0stkn0wledge
Antipwny: A Windows Based IDS/IPS for Metasploit
Rohan Vazarkar & David Bitner
Playing the Forensics Game: Forensic Analysis of Gaming Applications For Fun and Profit
Peter Clemenko III
Project.Phree: Phucking the NSA
BTS (square-r00t)
Hacking Benjamins (Intro to Bitcoin)
Bob Weiss @pwcrack
Pentoo
Zero_Chaos
Wireless Penetration Testing For Realz
Mellendick
How to Become an Unwitting Accomplice in a Phishing Attack
Mark Hufe @hufemj
LinkedAllUpIn Your Email
utkonos
Growing Up In The Information Security Community
@Forgottensec
|
| 11/01/2013 |
ISSA Kentuckiana - RESTful Web Services - Jeremy Druin - @webpwnized
Jeremy Druin (@webpwnize) gave the
following presentation at the Nov 2013 meeting of the
Kentuckiana ISSA. |
| 10/30/2013 |
Circle City Con (http://circlecitycon.com)
Hacker/Security Conference happening on June 13-15, 2014, Hyatt Regency,
Indianapolis Indiana
Looks like I have another almost local con to go to, Circle City Con in Indy!
I'll be doing video baring unforeseen circumstances, and may toss something into
their CFP (please consider
sending something in). More info at
http://circlecitycon.com or Twitter stalk them at
@CircleCityCon. |
| 10/20/2013 |
The Rest of the Hack3rcon^4 Videos
Here are there rest of the videos from Hack3rcon^4
ANOTHER Log to Analyze - Utilizing DNS to Identify Malware -
Nathan Magniez
Netsniff-NG - Jon Schipp
SDRadio: Playing with your Dongle - An Introduction to
Software Defined Radio Using Cheap TV Tuner Cards - Justin Rogosky
|
| 10/20/2013 |
Hack3rcon^4 Videos
As I post them, they will be at the link above. So far we have:
Advanced Evasion Techniques - Pwning the Next Generation
Security Products - David Kennedy
Imaging a Skyscraper - Brian Martin
Character Assassination: Fun and Games with Unicode - Adrian
Crenshaw
MS08-067 Under the Hood - John Degruyter
NSA Wiretaps are Legal and Other Annoying Facts - Branden
Miller
Red Teaming Your Bug-Out Bag - Tom Moore
Making it
Rain and Breaching the Levees - K.C. Yerrid
|
| 10/07/2013 |
Louisville InfoSec 2013 Videos Mostly Up These are the videos from
Louisville Infosec 2013 conference.
There are not all up yet, but this is my place holder.
Mobile Security and the Changing Workforce - Matthew Witten
Burn it Down! Rebuilding an Information Security Program - Dave Kennedy
(Pending review)
Weaponized Security - Kellman Meghu
Information Security in University Campus and Open Environments - Adrian
Crenshaw
Past Due: Practical Web Service Vulnerability Assessment for Pen-Testers,
Developers, and QA - Jeremy Druin (Pending finished upload)
STRC: The Security Training and Research Cloud - Jimmy Murphy
Assessing Mobile Applications with the MobiSec Live Environment - Nathan Sweeney
Attacking iOS Applications - Karl Fosaaen
Can cloud and security be used in the same sentence? - Joshua Bartley
Breaking SCADA Communications - Mehdi Sabraoui
FBI - InfraGard - Current Cyber Trends
How Do I Get There from Here? Security-to-Privacy Career Migration - Michael
Carr
Assessing the Risk of Unmanaged Devices (BYOD) - Pete Lindstrom
Acquisitions�your latest zero day - Mitch Greenfield/Scott MacArthur
NIST and your risky application - Conrad Reynolds
Convergence: Configurations, Vulnerabilities and Unexpected Changes - Brian
Cusack
What Healthcare Can Learn from the Banking Industry - Jim Czerwonka
Eliminating Data Security Threats And BYOS - David Braun
Awards |
| 10/04/2013 |
Derbycon
3.0 Videos Tracks 3, 4, 5 & Stable Talks Posted Track 3 (Teach Me)
It's Only a Game: Learning Security through Gaming - Bruce Potter
Ooops - Now What? :: The Stolen Data Impact Model (SDIM) - Brent Huston
Anti-Forensics: Memory or something - I forget. - int0x80
The Mysterious Mister Hokum - Jason Scott
Appsec Tl;dr - Gillis Jones
DIY Command & Control For Fun And *No* Profit - David Schwartzberg
IPv6 is here (kind of) - what can I do with it? - Dan Wilkins
Dancing With Dalvik - Thomas Richards
Big Hugs for Big Data - Davi Ottenheimer
Antivirus Evasion: Lessons Learned - thelightcosine
Jared DeMott - Is Auditing C/C++ Different Nowadays?
Getting Schooled: Security with no budget in a hostile environment - Jim
Kennedy
Browser Pivoting (FU2FA) - Raphael Mudge
Taking the BDSM out of PCI-DSS Through Open-Source Solutions - Zack
Fasel & Erin �SecBarbie� Jacobs
John Strand - Hacking Back - Active Defense and Internet Tough Guys
An Encyclpwnia of Persistence - Skip Duckwall & Will Peteroy
Your Turn! - Johnny Long - HFC
Practical File Format Fuzzing - Jared Allar
Surviving the Dead - Christopher �EggDropX� Payne
How can I do that? Intro to hardware hacking with an RFID badge reader -
Kevin Bong
A SysCall to ARMs - Brendan Watters
The Netsniff-NG Toolkit - Jon Schipp
Why Dumpster Dive when I can pwn right in? - Terry Gold
Track 4 (The 3-Way)
Pigs Don�t Fly - Why owning a typical network is so easy - and how
to build a secure one. - Matt �scriptjunkie� Weeks
Finding The Signal in the Noise: Quantifying Advanced Malware - Dave
Marcus
Applying the 32 Zombieland Rules to IT Security - Larry Pesce
Windows 0wn3d By Default - Mark Baggett
Android 4.0: Ice Cream �Sudo Make Me a� Sandwich - Max Sobell
Attacking the Next Generation Air Traffic Control System; Hackers -
liquor and commercial airliners. - Renderman
Antivirus Evasion through Antigenic Variation (Why the Blacklisting
Approach to AV is Broken) - Trenton Iveys
Hello ASM World: A Painless and Contextual Introduction to x86 Assembly
- nicolle neulist (rogueclown)
SQL injection with sqlmap - Conrad Reynolds CISA
The Internet of Things: Vulns - Botnets and Detection - Kyle Stone (@essobi)
- Liam Randall
The Malware Management Framework - a process you can use to find
advanced malware. We found WinNTI with it! - Michael Gough and Ian
Robertson
Hack the Hustle! - Eve Adams
Operationalizing Security Intelligence in the Enterprise- Rafal Los
New Shiny in the Metasploit Framework - egypt
Everything you ever wanted to know on how to start a Credit Union - but
were afraid to ask. - Jordan Modell
A developer�s guide to pentesting - Bill Sempf
Steal All of the Databases. - Alejandro Caceres
Sandboxes from a pen tester�s view - Rahul Kashyap
iOS Reverse #=> iPWn Apps - Mano �dash4rk� Paul
Terminal Cornucopia - Evan �treefort� Booth
Wait; How is All This Stuff Free?!? - Gene Bransfield Track 5 - Hybrid Room
Building An Information Security Awareness Program from Scratch -
Bill Gardner - Valerie Thomas
Malware : testing malware scenarios on your network - Tony Huffman
(@myne_us) - Juan Cortes (@kongo_86)
Password Intelligence Project - Advanced Password Recovery and
Modern Mitigation Strategies - John Moore �Rabid Security�
Tizen Security: Hacking the new mobile OS - Mark Manning (AntiTree)
RAWR - Rapid Assessment of Web Resources - Adam Byers - Tom Moore
Decoding Bug Bounty Programs - Jon Rose
Patching Windows Executables with the Backdoor Factory - Joshua
Pitts
Jason Scott - Defcon Documentary Q&A
Panel: Building and Growing a Hacker Space - Joey Maresca - Dave
Marcus - Nick Farr - SkyDog
SO Hopelessly Broken: the implications of pervasive vulnerabilities
in SOHO router products. - Jacob Holcomb
Put Me In Coach: How We Got Started In Infosec - pr1me - Chris
�g11tch� Hodges - Frank Hackett - Dave �ReL1K� Kennedy
Alice Goes Deeper (Down the Rabbit Hole) - Redirection 2.0 - Nathan
Magniez
Emergent Vulnerabilities: What ant colonies - schools of fish - and
security have in common. - Nathaniel �Dr. Whom� Husted
Why Your IT Bytes - Frank J. Hackett
Using Facial Recognition Software In Digital Forensics And
Information Security - Brian Lockrey
How to Fight a War Without Actually Starting One - Brendan O�Connor
Crypto-Exploit Exercises: A tool for reinforcing basic topics in
Cryptography - Nancy Snoke
Stable Talks
Gen Y:Getting Them to Talk Rather than Text at Work - Nancy Kovanic
Battle Scars And Friendly Fire: Threat Research Team War Stories -
Will Gragido and Seth Geftic
Unmasking Miscreants - Allixon Nixon - Brandon Levene
gitDigger: Creating useful wordlists from public GitHub repositories
- Jaime Filson (WiK)
PowerShell and Windows Throw the Best Shell Parties - Piotr
Marszalik
Owning Computers Without Shell Access - Royce Davis
Sixnet Tools: for poking at Sixnet Things - Mehdi Sabraoui
Hardening Windows 8 apps for the Windows Store - Bill Sempf
Intro to Dynamic Access Control in Windows Server 2012 - Evan
Anderson
Evolutionary Security - Embracing Failure to Attain �Good Enough� -
Josh More
DIY Forensics: When Incident Response Morphs into Digital Forensics
- John Sammons
ANOTHER Log to Analyze - Utilizing DNS to Discover Malware in Your
Network - Nathan Magniez
Phishing Frenzy: 7 seconds from hook to sinker - Brandon <zeknox>
McCann
Electronic Safe Fail: Common Vulnerabilities in Electronic Safes -
Jeff Popio
The Good Samaritan Identity Protection Project www.thegsipp.org -
Zack Hibbard - Chris Brown and Jon Sternstein
Some defensive ideas from offensive guys. - Justin Elze and Robert
Chuvala
Grim Trigger - Jeff �ghostnomad� Kirsch
A n00bie�s perspective on Pentesting� - Brandon Edmunds
My Security is a Graph - Your Argument is Invalid - Gabriel Bassett
Follow the Foolish Zebras: Finding Threats in Your Logs - Chris
Larsen
Security Training and Research Cloud (STRC) - Jimmy Murphy
Passive Aggressive Defense - Jason Clark
So you want to be a pentester? - Raymond Gabler
Digital Energy - BPT - Paul Coggin
An Anti-Forensics Primer - Jason Andress
What if Petraeus was a hacker? Email privacy for the rest of us -
Phil Cryer (@faker)
|
| 09/30/2013 |
Derbycon
3.0 Videos Tracks 1 & 2 I think I have all of tracks 1 and 2 posted:, more to come
Scanning Darkly - HD Moore (keynote)
Kinetic Pwnage: Obliterating the Line Between Computers and the Physical World -
Ed Skoudis (keynote)
Look Ma - No Exploits! - The Recon-ng Framework - Tim �LaNMaSteR53? Tomes
Practical Exploitation Using A Malicious Service Set Identifier (SSID) - Deral
Heiland
JTAGulator: Assisted discovery of on-chip debug interfaces - Joe Grand
Seeing red in your future? - Ian Iamit
TMI: How to attack SharePoint servers and tools to make it easier - Kevin
Johnson and James Jardine
The High Risk of Low Risk Applications - conrad reynolds
It�s Okay to Touch Yourself - Ben Ten (Ben0xA)
Collaborative Penetration Testing With Lair - Tom Steele and Dan Kottmann
Malware Automation - Christopher Elisan
What�s common in Oracle and Samsung? They tried to think differently about
crypto. - L�szl� T�th - Ferenc Spala
Burning the Enterprise with BYOD - Georgia Weidman
Getting the goods with smbexec - Eric Milam(brav0hax) and Martin Bos (purehate)
Shattering the Glass: Crafting Post Exploitation Tools with PowerShell - Matt
Johnson
Cheat Codez: Level UP Your SE Game - Eric Smith
My Experiments with truth: a different route to bug-hunting - Devesh Bhatt
The Art and Science of Hacking Any Organization - Tyler Wrightson
Living Off the Land: A Minimalist�s Guide to Windows Post-Exploitation -
Christopher Campbell & Matthew Graeber
Cracking Corporate Passwords - Exploiting Password Policy Weaknesses - Minga /
Rick Redman
Ownage From Userland: Process Puppeteering - Nick Cano
) UNION SELECT `This_Talk` AS (�New Exploitation and Obfuscation Techniques�)%00
- Roberto Salgado
Exploiting_the_Zeroth_Hour(); Developing your Advanced Persistent Threat to Pwn
the Network - SOLOMON SONYA and NICK KULESZA
Phishing Like The Pros - Luis �Connection� Santana
Raspberry Pi - Media Centers - and AppleTV - David Schuetz
Cognitive Injection: Reprogramming the Situation-Oriented Human OS - Andy Ellis
IOCAware - Actively Collect Compromise Indicators and Test Your Entire
Enterprise - Matt Jezorek and Dennis Kuntz
Cash is King: Who�s Wearing Your Crown? - Tom Eston and Spencer McIntyre
Security Sucks - and You�re Wearing a Nursing Bra - Paul Asadoorian
Windows Attacks: AT is the new black - Rob Fuller and Chris Gates
How Good is Your Phish - @sonofshirt
Identifying Evil: An introduction to Reverse Engineering Malware and other
software - Bart �d4ncind4n� Hopper
How Im going to own your organization in just a few days. - RazorEQX
Pass-The-Hash 2: The Admin�s Revenge - Skip Duckwall and Chris Campbell
The Cavalry Is Us: Protecting the public good and our profession - Josh Corman
Love letters to Frank Abagnale (How do I pwn thee let me count the ways) -
Jayson E. Street
The Message and The Messenger - James Arlen
50 Shades of RED: Stories from the "Playroom" - Chris Nickerson
Beyond Information Warfare �You Ain�t Seen Nothing Yet� - Winn Schwartau
Stop Fighting Anti-Virus - Integgroll
How the Grid Will Be Hacked - Josh Axelrod and Matt Davis
help for the helpdesk - Mick Douglas
Weaponizing your Coffee Pot - Daniel Buentello
Practical OSINT - Shane MacDougall (NOTE THAT THIS IS AN ADULT ONLY TALK - 18+
or older)
Stop making excuses; it�s time to own your HIV (High Impact Vulnerabilities) -
Jack D. Nichelson
Uncloaking IP Addresses on IRC - Derek Callaway
|
| 09/29/2013 |
Derbycon
3.0 Videos
As I get them up, you can find them here. Big thanks to my video jockeys Robin,
ladymerlin, Jennifer, Sabrina, Reid, Skydog, Some Ninja Master, Glenn Barret,
Dave Lauer, Jordan Meurer, Brandon Grindatti, MadMex, Joey, Steven, Sara,
Branden Miller and Night Carnage |
| 09/18/2013 |
Unicode
Security Notes Page
This page has notes for my HackerHalted and Hack3rCon talk. |
| 08/24/2013 |
Unicode Text Steganography Encoders/Decoders
The idea of this page is to demo different ways of using Unicode in
steganography, mostly I'm using it for Twitter. :) I have some notes on the
bottom about how these Unicode characters show up or get filtered by some apps.
Most of the algorithms should work ok on Twitter, Facebook however seems to
strip out more characters. There seems to be no perfect character set. |
| 08/09/2013 |
Every Unicode Character For Fuzzing and Research
I will be doing a talk on Unicode and security at
Hacker Halted, as prep work I've
generated some files with ever Unicode character. I'd be interested in knowing
if any of them crash apps on you. Open with care.
Every Unicode Character Blob Page or
TXT file
Every Unicode Character 80 Column Page or
TXT file
Every Unicode Character With Hex Page or
TXT file |
| 08/06/2013 |
BSidesLV 2013 Videos
These are the videos from the BSides Las Vegas
conference. Thanks to all of the BSides Crew for having me out to help record
and render the videos. @bsideslv,
@banasidhe,
@kickfroggy,
@quadling,
@jack_daniel
"The Security Industry - How to Survive Becoming Management" - Christien Rioux
Discovering Dark Matter: Towards better Android Malware Heuristics - Jimmy Shah,
David Shaw, Matt Dewitt
Mom! I Broke My Insulin Pump... Again! - Jay "Rad" Radcliffe
Dungeons & Dragons, Siege Warfare, and Fantasy Defense in Depth - Evan Davidson
and Noah Schiffman
HiveMind: Distributed File Storage Using JavaScript Botnets - Sean Malone
gitDigger: Creating useful wordlists from public GitHub repositories - WiK and
Mubix
Collaborative Penetration Testing With Lair - Tom Steele and Dan Kottmann
Social Aftermath Responding to Social Pwnage - Steven F. Fox
Silence Equals Death - Violet Blue
The Cavalry Isn't Coming: Starting the Revolution to Fsck it All! - Nicholas J.
Percoco and Joshua Corman
A Fire In The Eye - Olli-Pekka Niemi and Antti Levomaki
Defense Evasion Modeling - Frank Artes
"Malware Management Framework" - We detected WinNTI with it! - Michael Gough
Crunching the Top 10,000 Websites' Password Policies and Controls - Steve Werby
Governments and UFOs: A Historical Analysis of Disinformation and Deception -
Richard Thieme
Strange interactions in personal data: Brokers and the CFAA - Christine Dudley
Diamonds, Fitness and Cults: Manipulation for Fun and Profit - Katie Rodzon
Vulnerability & Exploit Trends: A Deep Look Inside The Data - Ed Bellis, Michael
Roytman
EC2 or Bust - How to Build Your Own Pen Testing Lab in Amazon EC2 - Grecs
Techniques for Escaping the AppSec Labyrinth - Andrew Hay
The Erudite Inebriate's Guide to Life, Liberty, and the Purfuit of Happinefs -
Jack Daniel
Hack the Hustle! Career Strategies for Information Security Professionals - Eve
Adams
Information Sharing, or "I've got 99 problems and they're probably pretty
similar to yours" - Chris Mills
Convincing Your Management, Your Peers, and Yourself That Risk Management
Doesn't Suck - Josh Sokol
How embracing social media helped me stop the hackers, save the world and get
the girl! - Javvad Malik
Malware Automation - Christopher Elisan
Popping the Penguin: An Introduction to the Principles of Linux Persistence -
Mark Kita
Network Survival WCS - James Costello
The Slings and Arrows of Open Source Security - Tod Beardsley and Mister X
What if Petraeus was a hacker' Email privacy for the rest of us - Fak3r
Never Mind Your Diet, Cut the Crap From Your Vocabulary - Keli Hay (Brian
Martin)
The 7 habits of highly effective CISOs - Franklin Tallah (Wendy Nather)
The Little Dutch Boy - D0n Quix0te (Bill E. Ghote)
Stop Shooting Blanks: No magic bullets in your arsenal - Renegade6 (Nicolle
Neulist)
Flameout - Burnout Supernova - Dan Ward (Ally Miller)
The Sensual Side of 3D Printing - Kat Sweet (Javvad Malik)
Fun with WebSockets using Socket Puppet - Mister Glass (Weasel)
Using Machine Learning to Support Information Security - Alex Pinto (Joel
Wilbanks)
The Truth, You Thought We Wouldn't Know' - Wolf Flight (Terry Gold)
Vulnerabilities in Application Whitelisting: Malware Case Studies - Jared Sperli
and Joe Kovacic (J0hnny Brav0)
The Goodness is Baked In: Baking Assurance into Software - Ebony (Davi
Ottenheimer)
Matriux Leandros:An Open Source Penetration Testing and Forensic Distribution -
Prajwal Panchmahalkar (Savant42)
Sixteen Colors: Archiving the Evolution of ANSI and ASCII Art - Doug Moore
(Brendan O'Connor)
You Are Being Watched! - Bharat Jogi
Calling All Researchers: A Discussion on Building a Security Research Framework
- Michael "DrBearSec" Smith
Evil Empire: SIEM FTW - EggDropX and Tha CheezMan
Attribution Shmatribution! FIX YOUR SHIT! - Krypt3ia
Breach Panel - Davi Ottenheimer, Raymond Umerley, Jack Daniel, Steve Werby,
David Mortman & George V. Hulme
Roll-your-own Lightning Talks
Attacking and Defending Full Disk Encryption - Tom Kopchak
Say It to My Face - Shannon Sistrunk
Alex Dreams of Risk: How the Concept of Being a Craftsman can Help you Find
Meaning and Avoid Burnout - Alex Hutton
You can't make people act more securely, you can help them want to. - Ivan
Campbell and Twyla Campbell |
| 08/02/2013 |
BSidesLV 2013 Videos
Putting these up at the link above as I get them together. This will take a bit,
5 tracks takes time. Follow
@bsideslv for more. |
| 07/14/2013 |
OISF 2013
Videos These are the videos from the
OISF Anniversary Event
Webshells History, Techniques, Obfuscation and Automated Collection - Adrian
Crenshaw
Kali Linux Backtrack Linux reborn - Martin Bos
Locks & Physical Security - Deviant Ollam
Leveraging Mobile Devices on Pentests - Georgia Weidman
Reverse Engineering Demystified (a little maybe) - Chris Eagle |
| 07/04/2013 |
Web Shells
Collection Page Updated
I'm prepping to give my Webshells talk again at
OISF and
TakeDownCon Rocket City. I
like to update things if I give a talk more than once, so I enhanced my script
to save an archived copy of the webshells in a zip file so even if the infected
host cleans it up (which they really should), it can be examined later. |
| 07/04/2013 |
NQSFW Free CISSP Study Guide
I'm working on studying for a CISSP, so I figured I should record my notes. As I
do them, I plan to post them here. @gozes
also pointed me to
http://www.opensecuritytraining.info/CISSP-Main.html which looks like a damn
good resource. |
| 06/21/2013 |
BSides
Boston Videos
While at BSidesRI I met a bunch of
folks from BSidesBoston. Roy
asked me to put up a link to their videos:
https://www.youtube.com/channel/UCmPk1vRLVFIcYjXM9lWFUHA/videos
Next year I hope to be able to make it out there. |
| 06/15/2013 |
All BSides Rhode Island Videos
Friday pre-con:
Large-scale application security - Charlie Eriksen
SMB SRMF for identifying top 10 risks - Jim Peeler
How I Do a Weekly Podcast (or Three) - Paul Asadoorian
Show and Tell: Super-Minipwner - James Edge
Opening the Treasure Chest-Attacking Network Attached Storage on a Pen Test -
Russell Butturini
BSidesRI Track:
Hacking Your Neighbors for Fun! - Josh Wright
Public cloud PCI compliance or a sharp stick in the eye, which to choose? -
Chris Brenton
Bite the Wax Tadpole - The importance of culture in user security - Kati Rodzon
and Mike Murray
Exploiting the Top Ten Database Vulnerabilities and Misconfigurations - Josh
Shaul
Exploit Development for Mere Mortals - Joe McCray
Future Trends in IT security - Ron Gula
The Freaky Economics Of Cybersecurity - Robert David Graham
PaulDotCom Track:
Booting the Booters, Stressing the Stressors - Allison Nixon and Brandon Levene
Talk More Better - Jack Daniel
Security Sucks, and You're Wearing The Nursing Bra - Paul Asadoorian (Not
Recorded)
So, you want to compute post-apocalypse? - Larry Pesce & Darren Wigley
Feeling Sick? Healthcare Information Security - Roy Wattanasin
Blitzing with Your Defense - Ben Jackson
Lessons Learned: Why I became a PaulDotCom Intern and why you should become an
Intern too. - Mike Perez
Learning Security on the Cheap (30 min) - Patrick Laverty
Download link coming later. |
| 06/15/2013 |
BSides Rhode Island Videos
As I get them up, I'm putting them on this page above. |
| 06/13/2013 |
ASAReaper: Grab Configs From Multiple Cisco Devices Over SSH (Demos PExpect and
AES Encrypted INI Files in Python) Updated
Updated the code to make it easier to maintain and to fix a timeout issue. Also,
Arne Lovius told me about a tool called Rancid (http://www.shrubbery.net/rancid)
that can do the same thing as my script and more, but I figured the sample code
is still of help to some. |
| 06/13/2013 |
Indiana University (IU, IUS, IU*, Etc) Salaries
I noticed the someone visited my
IU
Southeast School of Business (MBA) Review page from a search for something
like "IU Salaries". This made me curious as I knew Indystar had the information.
Seems Indystar's page is having errors, another newspaper hides it behind a pay
wall, and IU makes you login with an account AND use an on campus IP. My
understanding is this information is suppose to be public, but it seem somewhat
hard to find. As a public service, here is the 2012/2013 Salary information in
HTML (Just for IUS) and Excel formats (all campuses) for easier parsing.
Hopefully it helps alumni and the like consider if it is really a fruitful place
to donate to (and how to earmark donations). For some of the pay levels, it
really is a shameful waste. |
| 06/07/2013 |
Kali Linux Live Boot USB Flash Drive - Jeremy Druin
Jeremy Druin (@webpwnize) gave
the following presentation on creating a persistent Kali Linux thumbdrive
install for the June 2013 meeting of the Kentuckiana ISSA.
|
| 05/27/2013 |
Webshell Demos And Notes
This is a page I'm putting together for my
TakeDownCon and
OISF talks on webshells. My slides are
pretty text, link, command and code heavy, so this way I can just point the
attendees to this page for all the notes and links. |
| 05/24/2013 |
Webshell
Collection Page Updated With Source Code
I have a script I run against my web logs periodically to see if anyone is
trying to use a Remote File Include Webshell against my site. I've done some
more filter work, and can now find more webshells with it. If you spot bugs in
the code, please let me know. I'll also be speaking at
TakeDownCon St. Louis and the OISF Anniversary Event
on webshells, this is part of that project. |
| 05/23/2013 |
About page and CV updated
I finished my Master of Science in Security Informatics, so I've update my
"about" page and CV. Unfortunately, I did not maintain the straight A average I
had in my Informatics courses (I made a B in Machine Learning, which equals
calculus, linear algebra, matrix mathematics and pain), so I had to change a
blurb in my
IU Southeast School of Bussiness/MBA review about being a straight A student
in my new program. I just wanted to have more integrity than the people at the
IUS MBA
program who still boast about being the 9th rated part time MBA from the
Business Week ratings in 2009, forgetting to mention that they have fallen to
74th since then (University of Louisville is at 35 by the way). Now, I know my
readers think I'm a little OCD about this subject, which I admit I am, but I
think integrity and ethics are important in both business and infosec,
especially in those who are supposed to be educating the future workforce and
leadership. I don't want others looking for a Master degree in the Louisville
area to go through the same things I did, at least then something good would
have come from what happened to me. There is some reason to think that IUS may
get better, Gil Atnip,
Ruth Garvey-Nix, and
Sandra R. Patterson-Randles
are all either retired or retiring from their positions of power. Still, the
kinds of people who seem to gravitate toward academic administration positions
have a tenancy to be less than caring towards student concerns in my experience.
They may be better now, one VC seems to care at least a little considering his
visits to the page and another VC seemed to be a decent person in the one
Philosophy class I had with him, but the current student affairs person refuses
to even respond to questions. Also, people like
Jay White,
Jon Bingham, and Linda
Christiansen are still in their positions of power in the school of
business, not even chastised for their behavior. With that in mind, I still
can't recommend IUS to the people I know in IT around the Louisville area. I'm
really sort of torn about it, as I think the IUS Informatics and Comp-Sci
programs are pretty good, and I know there a good professors out there in
business, but I don't think most people are willing to speak out unless they are
personally involved. If you go there for Informatics or Comp-Sci, I recommend
going with one of the math science options instead of business. |
| 05/20/2013 |
ISSA Kentuckiana Web Pen-Testing Workshop
Below are the videos form the Kentuckiana
ISSA's Web Pen-Testing Workshop. It
was put on in part to raise funds for
Hackers For Charity.
A few of theses are still uploading, but should be available shortly.
Part 1: Intro to Mutillidae, Burp Suite & Injection Jeremy
Druin
Part 2: SQL Injection Conrad Reynolds
Part 3:
Uploading a web shell via SQLi Jeremy Druin
Part 4:
Authentication Bypass via SQLi & Cookie Tampering Jeremy Druin
Part 5:
Intro to Kentuckiana ISSA Jeremy Druin
Part 6:
Remote File Inclusion (RFI) & Local File Inclusion (LFI) Jeremy Druin
Part 7:
Webshells Demo Adrian Crenshaw
Part 8:
Intros to Speakers
Part 9:
HTML & Javasript Injection XSS Jeremy Druin
Part 10:
XSS & BeEF Conrad Reynolds
Part 11:
What we have of CSRF
(Camera ran out of space, slides kept going) Jeremy Druin
Part 12:
JSON injection Jeremy Druin |
| 04/21/2013 |
AIDE 2013: The
rest of the videos
At this point I had to leave for Notacon to record their talk and was not there
to run the slide capture rig for AIDE. I shanghaied some volunteers into
recording, and while they did not get the slide rig working, we have the
presenter and slides on camera. Thanks for filling in.
Boring eForensic Science Items - Brian Martin
Hackers in Unganda: A Documentary (Kickstarter Project) - Jeremy Zerechak
Small Businesses Deserve Security Too - Frank Hackett
Help from the helpdesk - Mick Douglas (@bettersafetynet)
Malware Analysis Triage for n00bs - Grecs (@Grecs)
CCDC and Industry - James L. Siegel Jr. (WolfFlight)
Building an Engaging and Effective Information Security Awareness and Training
Program - Bill Gardner |
| 04/21/2013 |
Notacon
10 Videos
These are the videos from
the 10th Notacon conference held April
18th-21st, 2013. Not all of them are security related, but I hope my
viewers will enjoy them anyway. Thanks to Froggy and Tyger for having me up, and to the video
team: SatNights, Widget, Securi-D, Purge, Bunsen, Fry Steve and myself (at least
that is who it was last year, if you got he names for 2013 let me know).Track 1
Model Integrated Computing (Code Generation) and how it loves you
and deserves love back - Michael Walker
Guns & Privacy - Deviant Ollam
Domestic Preparedness (the zombie Apocalypse is nigh upon us) -
Illustrious Niteshad & megalos
DIY Neuroscience, EMGs, EEGs, and other recordings - meecie
Hacking Your Ability to Communicate - kadiera
Lasers for Fun! Lasers for Science. Lasers for Security! - Ethan Dicks
Video Everywhere! aka The Personal Distributed HD Video Network - Woz
Esolangs - Daniel Temkin
How We Learned Security from Steve - ghostnomad, ghostnomadjr, knuckles
& micronomad
Are we getting better? - Hacking Todays Technology - David Kennedy
Critical Making - Garnet Hertz
DC to Daylight: A whirlwind tour of the radio spectrum, and why it
matters. - Stormgren
Skeleton Key: Transforming Medical Discussions Through 3D Printing - KK
Pandya
Youthful Exploits of an early ISP - Dop & KevN
Whose Slide Is It Anyway? - nicolle @rogueclown neulist Track 2
I Forked the Law and We
All Won - Fork The Law
Make me Babyproof! - Gina �the kat� Hoang
The Maru Architecture Design: A proposed BYOD architecture for an
evolving threat landscape - Michael Smith
You Keep A-Knockin� But You Can�t Come In - grap3_ap3
Encryption for Everyone - Dru Streicher (_node)
How I Became an iOS Developer for Fun and Debt - Mark Stanilav
AR_GRAF.OBJ: a darknet for the nuEra ?? - kevin carey, shawne
michaelain holloway & brian peterson
Creating professional glitch art with PoxParty - Jon Satrom & Ben
Syverson
Let�s Go CSRF�n Now! - grap3_ap3
Bad Games Arcade - Jake Eliott
The Winamp Imperative - Yoz
(sorry, audio died at 6:09) |
| 04/18/2013 |
AIDE 2013
I got to record and put up a few videos from AIDE.
I had to head to Notacon before I could
record them all, but I left some gear so hopefully I'll have more to come. Recorded at AIDE 2013. Big thanks to Bill
Gardner (@oncee) for having me out to
record.
Network King Of The Hill (NetKotH): A hacker wargame for organizers who are lazy
- Adrian Crenshaw (Irongeek)
Can You Hear Me Now? Leveraging Mobile Devices on Pentests - Georgia Weidman
RAWR
(Rapid Assessment of Web Resources) - @al14s and @c0ncealed |
| 04/11/2013 |
Hacker Swap Meet: Don't Let That Old
Junk Go To Waste!
Many of us are tech pack rats, we have old gear laying around we don't use but
don't want to just throw away. Got something you want to trade with other
hacker/maker types? Too expensive to ship but you can drive it to a con you will
be at anyway? Set up the trade at the new forums I put up. One man's treasure is
another man's hazmat. If you don't see a con/meet spot listed here, let me know
and I can add it.
http://www.hackerswapmeet.org/
I should have some old gear at Notacon I
want to get rid of. |
| 04/08/2013 |
Outerz0ne 9 (2013) Videos
These are most of the videos from the
Outerz0ne 9 conference. I have a few
more I have to get clearances on before I post them. Big thanks to
Joey and Evan on the video crew.
SkyDog Kicks Off Year NINE! (Number Nine)
Gursev Kalra - Impersonating CAPTCHA Providers
Tuttle/Brimstone - State of the BitCoin Address; Pizza, Pirates, and Profiteers.
Halfjack - Living to the Singularity: Geeks Guide to a Healthy Lifestyle
Chad Ramey - Hacking the Atom
Jeremy Schmeichel & Brian Wilson - IPv6? Ain't Nobody Got Time For That!
Chris Silvers - Weapons of Miniature Destruction
Hacker Movie Challenge
Inside the Hacker's Studio - Billy Hoffman and IronGeek
Contest Prize Giveaway, Awards, Closing Ceremonies
Lightning Talks and such:
Andy Green - The Southeast Collegiate Cyber Defense Competition Lightning Talk
Lilyjade-v2.com - Why You Are Not Safe Lightning Talk
Presentation Karaoke |
| 03/26/2013 |
Updated: Links for Doxing, Personal OSInt, Profiling, Footprinting,
Cyberstalking
I have to give presentation on online privacy shortly, and figured it would be a
good time to update the page above with a few new links. See the change log at
the bottom. If you have more good links to add, please contact me. I'll also be
speaking at TakeDownCon St. Louis
on webshells so I've updated my
Webshell
Collection Page to keep a log of not only live webshells, but also keep a
history of dead ones. |
| 03/13/2013 |
Outerz0ne 9 Dates Announced: April 5-6th,
2013
I know it's a little short notice, but dates and the CFP have been announced for
Outerz0ne 2013: April 5-6th, 2013 in Atlanta Georgia. I'll of course be there
helping out the video crew. It's a donation based con, so give what you can. To
see videos from past years, check out:
Outerz0ne 8 (2012) Videos
Outerz0ne 2011 Hacker Con
Outerz0ne 2010 Videos
and a bunch of others spread out over the
Hacking
Illustrated page.
In other news, Jessica Miller from No Starch Press wanted me to announce
this:
"We've just released the free PDF of bunnie's "Hacking the Xbox" in Aaron
Swartz's honor, with links to support the causes Aaron believed in. I thought
you might be interested in seeing bunnie's note and helping to spread the word -
http://nostarch.com/xboxfree "
I did not know Aaron, but as a person who has be screwed by an uncaring
cover-ass bureaucracy before, I can sympathize. |
| 03/03/2013 |
Introduction to HTML Injection (HTMLi) and Cross Site Scripting (XSS) Using
Mutillidae
New Video From Jeremy Druin:
This video covers the basics of injecting HTML into sites with vulnerabilities
in which injected code is placed inline with intended code and executes in the
users browser. The injected HTML in this video is a fake login box that posts
the user username and password to a capture data page (in the NOWASP Mutillidae
application).
Later the same vulnerability is used to inject cross site scripting attack that
hooks the users browser with a Beef Framework script (hook.js) given an attacker
control of the users browser. |
| 03/03/2013 |
Introduction to Pen Testing Simple Network Management Protocol (SNMP)
New Video From Jeremy Druin:
The Simple Network Management Protocol (SNMP) is used on networked devices to
read, write, and update device configuration remotely. Windows desktop systems
typically do not run SNMP services by default but these can be enabled for
testing. Server operating systems often run snmp services by default as do
network devices such as routers, printers, special purpose equipment, switches,
and firewalls.
In this video, a Windows XP box has SNMP enabled to act as a test target. A
Backtrack 5 R3 host is used to perform assessment. The video progresses through
host discovery, port identification, service verification, finding community
strings, dumping device configuration, and altering device configuration. |
| 02/24/2013 |
Bro IDS/Network Programming Language Video Page
Liam Randall, a developer on the Bro
team, and the guy that supplies cherry flavored refreshment at many cons, asked
me to post his Shmoocon 2013 video. Since he said there would be more videos to
come, I decided to make a page for them. Go check out the project at:
http://www.bro-ids.org/ |
| 02/23/2013 |
Intro
To The Louisville OWASP Chapter
Quick intro to the Louisville OWASP chapter by Curtis Koenig. Sorry that the
video is cut a little short. I've also updated the
Shmoocon FireTalks 2013 page to have a downloads link at the bottom. |
| 02/18/2013 |
Shmoocon FireTalks 2013
The Shmocon FireTalks are now up:
�Thin Slicing a Black Swan: A Search for the Unknowns� by Michele �@mrsyiswhy�
Chubirka & Ronald Reck
�When Did the Smartphone Pentest Framework Get Awesome?� by by Georgia
�@georgiaweidman� Weidman
�ShellSquid: Distributed Shells With Node� by Tom Steele
�If You Can Open The Terminal, You Can Capture The Flag: CTF for Everyone� by
Nicolle �@rogueclown� Neulist
�Becoming a Time Lord � Implications of Attacking Time Sources� Joe �@joeklein�
Klein
�Swinging Security Style: An Immodest Proposal� by Wendy �@451wendy� Nather
�Drones: Augmenting your cyber attack tool bag with aerial weapon systems� by
Zac �@ph3n0� Hinkel
�Managed Service Providers: Pwn One and Done� Damian �@integrisec� Profancik
�No Tools? No Problem! Building a PowerShell Botnet� Christopher �@obscuresec�
Campbell
�Extending the 20 Critical Security Controls to Gap Assessments and Security
Maturity Modelling� John �@pinfosec� Willis
�Protecting Big Data From Cyber APT in the Cloud� Bill �@oncee� Gardner
�Writing a Thumbdrive for Active Disk Antiforensics� Travis �@travisgoodspeed�
Goodspeed
On the non-info-sec related front, you know I like to use my backlinks to get
things in search results as sort of a bully pulpit. It's my understanding that
IU Southeast Chancellor Sandra R. Patterson-Randles is searching for a new
job because of some IU policy about mandatory retirement. Ask around the
faculty/staff at
IUS
about her (off the record of course) before you make a hiring decision.
Personally, I'd want someone who cares more about the espoused values of the
organization, and less about appearances only. Then again, maybe she has the
skill set you are looking for, but a parrot with good grammar would seem to be a
much cheaper solution in that case. |
| 02/11/2013 |
Basics of using sqlmap - ISSA Kentuckiana workshop 8 - Jeremy Druin
This is the 8th in a line of classes Jeremy Druin will be giving on pen-testing
and web app security featuring Mutillidae (or other tools) for the Kentuckiana
ISSA. This one covers SQLMap. |
| 02/01/2013 |
ASAReaper: Grab Configs From Multiple Cisco Devices Over SSH (Demos PExpect and
AES Encrypted INI Files in Python)
Simple script I wrote for backing up Cisco ASAs. Does it all over SSH, and may
serve as example code for other projects. |
| 01/05/2013 |
SQL Server Hacking from ISSA Kentuckiana workshop 7 - Jeremy Druin
This is the 7th in a line of classes Jeremy Druin will be giving on pen-testing
and web app security featuring Mutillidae (or other tools) for the Kentuckiana
ISSA. This one covers SQL Server Hacking. |
| 01/03/2012 |
Information Security in University Campus and Open Environments 2013
This is an update of an article I did almost 8 years ago. Lots of things have
changed in that time, do I figured the update was in order. It almost acts as a
meta-page to other parts of my site, but I hope you enjoy it.
|
| 12/29/2012 |
Webshell
Collection Page Updated
I have a script I run against my web logs periodically to see if anyone is
trying to use a Remote File Include Webshell against my site. I wrote this
awhile back, but the list was getting long and there were a lot of 404s,
duplicates, and other problems. I've filtered out many of those. If you want to
take a look at some Webshell that are in active use on the Internet you may like
this page. |
| 12/27/2012 |
IU
Southeast School of Business / MBA Write-up Updated
I've made many small changes over the months to my IUS MBA Review site (change
log). I realize that this page is not very security related, but I can tie
it to infosec in a few ways (regular readers, please ignore the noise in the
signal). Lots of infosec folks I know seem to go for an MBA if they want to get
into management, so I figured it might help some of the infosec folks in the
Louisville Metro area (Kentuckiana Metroversity) know what to avoid. It's also
an opportune time since some students are about to finish their bachelors in the
spring, and will start looking for grad schools now. I can tie it in as an
experiment in how some spiders index sites. I've done a bit of
forensic metadata work on a file
I received via an open records request that might be interesting as well, but
it's not in-depth. It may also help people who have to deal with bureaucracies
that have people like
Jay White,
Jon Bingham, Linda Christiansen and Gil Atnip in them know that they are not
alone. Hopefully I'll be able to work with the
IU Southeast SGA to get a real grievance policy put in place over the spring
semester so students are treated with more respect. |
| 12/26/2012 |
MadMACs: MAC Address Spoofing and Host Name Randomizing App for Windows 7
(Should work in Windows Vista and Windows 8 too) Updated
I wrote MadMACs awhile back, as a simple script to randomize my MAC address (and
host name) in Windows on every boot. I had not updated it in a long time so it
stopped working well in newer versions of Windows (Windows 7, Windows Vista and
Windows 8). When someone would try to get MadMACs to work on a newer version of
the OS, Windows would not always respect the registry setting for what MAC
address they were suppose to use. Seems that if it is a wireless interface, the
2nd nibble has to be a 2, 6, A or an E on Windows Vista and newer. I included
functionality in the new version of MadMACs to make sure this nibble is correct
if you tell it the NIC you are trying to change/randomize the MAC address on is
a WiFi card. I've also added a GUI for configuring your MAC addresses on your
network cards (the old version used prompts), made the config file more INI
like, and made it so that MadMACs itself can reset your adapter and start using
the new MAC address immediately (name changes will take a reboot). |
| 12/22/2012 |
Anti-Arp-Poisoning Switch Demo Using OpenFlow & POX
When I posted my OpenFlow/SDN Security paper, I spaced on including the source
code to the ARP Poisoning resistant POX controller I mentioned. It is now
included in the link above. Also, go check out
Steve Erdman's blog for a bunch of
security/networking articles. |
| 12/16/2012 |
Security and Software Defined Networking: Practical Possibilities and Potential
Pitfalls
This is a short paper I wrote for class involving SDN (OpenFlow specifically)
and it's potential ramifications in the infosec world. |
| 12/09/2012 |
Introduction to Installing, Configuring, and Using Burp-Suite Proxy
Another video from Jeremy Druin. |
| 11/24/2012 |
Introduction to buffer overflows from ISSA KY workshop 6 and two other videos
from Jeremy Druin
Mutillidae: Using ettercap and sslstrip to capture login
This video by webpwnized (@webpwnized) reviews how to intercept web
communications using ettercap and intercept web traffic that is supposed to be
protected with SSL using SSLStrip.
Mutillidae SQL Injection via AJAX request with JSON response
This video by webpwnized (@webpwnized) covers pen-testing an SQL Injection
vulnerability that occurs in an AJAX request made in the background. The
response from the server is JSON. Since AJAX requests and regular request work
the same way (since they both follow the rules of the HTTP protocol), the AJAX
request can be pen-tested using the same tools and tecniques used with the more
traditional requests. The SQL Injection flaw is first discovered then used to
pull a list of the tables in the database along with the columns for the target
table. Once the target is identified, the defect is used to pull a list of the
username and password fields.
Introduction to buffer overflows from ISSA KY workshop 6
This recording is from the Kentucky ISSA Workshop #6 from the November 2012
meeting. In part 5, using Metasploit was covered. In this workshop, buffer
overflow vulnerabilities were examined more closely to see how Metasploit
exploits might be written. A custom program is written with a known buffer
overflow and compiled without the stack canaries or non-executable stack. Also
ASLR is disabled on the Ubuntu 12.04 testing host. The program is fuzzed to
determine an overflow exists and decompiled with GDB to look at the program
logic more closely. Python scripts are used to generate exploits that get closer
to over-writing the return pointer with a user supplied value. Once the buffer
overflow is identified and the size of the buffer found, the exploit development
begins. A custom exploit is developed to inject shellcode into the buffer,
determine a reasonable memory address in which to jump, and a root shell gained. |
| 11/11/2012 |
PhreakNIC 16 Day Two Videos Posted
Here are the videos from day 2 of
PhreakNIC 16. Big thanks to Ben the Meek and the rest of the video crew.
I'll get the AVIs up on Archive.org soon.
Where We're Going We Don't Need Keys - sp0rus
The Effects of Online Gaming Addiction - Gregory C. Mabry
Android Best Practices and Side Projects - Michael Walker
Starting up a Crypto Party - Peace
Build Free Hardware in Geda - Matthew O'Gorman, Tim Heath
IP Law: Myths and Facts - Rick Sanders
The Safety Dance: Wardriving the 4.9GHz Public Safety Band - Robert Portvliet,
Brad Antoniewicz
The Power of Names: How We Define Technology, and How Technology Defines Us -
Aestetix
DNS Sec Today - Thomas Clements
Why I am pessimistic about the future - Tom Cross |
| 11/10/2012 |
PhreakNIC 16 Day One Videos Posted
Here are the videos from day 1 of
PhreakNIC 16. Big thanks to Ben the Meek and the rest of the video crew.
Welcome to PhreakNIC - Warren Eckstein
Magnets, How Do They Work? - Michael Snyder
Own the Network � Own the Data - Paul Coggin
Something about middleware - Douglas Schmidt
Homebrew Roundtable - Scott Milliken, Erin Shelton
Repurposing Technology - Kim Smith & Kim Lilley
Hiring the Unhireable: Solving the Cyber Security Hiring Crisis From DHS to Wall
Street - Winn Schwartau
Network King Of The Hill (NetKotH): A hacker wargame for organizers who are lazy
bastards - Adrian Crenshaw |
| 11/06/2012 |
Derbycon 2012 Stable Talks
We did not officially record the Stable Talks this year but
Damian Profancik stepped up and
volunteered to do it. Big thanks for the recording and editing!
Valerie Thomas: Appearance Hacking 101 - The Art of Everyday Camouflage
Tim Tomes "LanMaSteR53": Next Generation Web Reconnaissance
Thomas Hoffecker: Hack Your Way into a DoD Security Clearance
John Seely CounterSploit MSF as a defense platform
Chris Murrey "f8lerror" & Jake Garlie "jagar": Easy Passwords = Easy
Break-Ins
Tyler Wrightson: The Art and Science of Hacking Any Target
Thomas Richards: Android in the Healthcare Workplace
Spencer McIntyre: How I Learned to Stop Worrying and Love the Smart Meter
Shawn Merdinger: Medical Device Security
Rockie Brockway: Business Ramifications of Internet's Unclean Conflicts
Nathan Magniez: Alice in Exploit Redirection Land
Magen Hughes: Are you HIPAA to the Jive
Justin Brown & Frank Hackett: Breaking into Security
Josh Thomas: Off Grid Communications with Android
Jennifer "savagejen" Savage & Daniel "unicorn Furnance": The Patsy Proxy
Jason Pubal: SQL Injection 101
James Siegel: Nice to Meet You
Brett Cunningham: Beyond Strings - Memory Analysis During Incident Response
Gus Fritschie & Nazia Khan: Hacked Hollywood
Evan Anderson: Active Directory Reconnaissance - Attacks and
Post-Exploitation
David Young: ISO8583 or Pentesting with Abnormal Targets
David Cowen: Running a Successful Red Team
Damian Profancik: Managed Service Providers - Pwn One and Done
Ben Toews & Scott Behrens: Rapid Blind SQL Injection Exploitation with
BBQSQL
Andy Cooper: Why Integgroll Sucks at Python..And You Can Too
|
| 11/04/20122 |
The potential impact of Software Defined Networking on security - Brent
Salisbury
This is Brent Salisbury talk on SDN and security for the
Kentuckiana ISSA November
meeting. Sorry about the sound, I need to get a mic next time. Sorry I did not
get Jeremy Druin's talk, we had multiple levels of video fail.
|
| 10/29/2012 |
SkyDogCon 2012 Videos
Here are the videos from
SkyDogCon. Thanks to all of the SkyDogCon crew, especially SeeBlind and
others for running the cameras.
Opening Remarks-Trevor Hearn-Skydog
Rious and Sachin - "Hack the Badge"
GCS8 and Ginsu - Physical Security; Make sure your building is "Butter
Knife Proof"...
Marcus Carey - Security Myths Exposed
SpikyGeek - Dealing with difficult co-workers: How I became the "Thanks
for the candy" guy
Peter Shaw - Pivot2Pcap: a new approach to optimzing cybersecurity
operations by tightly coupling the big-picture view provided by Netflow
with the in-depth resolving power of PCAP.
Carter Smith - Gangs and the use of Technology
G. Mark Hardy - Hacking as an Act of War
Jeff Brown - RE, CND and Geopolitics, Oh My!
Curtis Koenig - Insanely Great!
Lee Baird - Setting up BackTrack and automating various tasks with bash
scripts
Bob Weiss & Benjamin Gatti - Cryptanalysis of the Enigma
Dr. Noah Schiffman - Bioveillance: The Surreptitious Analysis of
Physiological and Behavioral Data
Martin Bos & Eric Milam - Advanced Phishing Tactics Beyond User
Awareness
Sonny Mounicou - Build a UAV!
Alex Kirk - Lifecycle and Detection of an Exploit Kit
Chris Silvers - Go With the Flow: Strategies for successful social
engineering
Scott Moulton - Hack your Credit Score; How the System is Flawed
David Wyde - User-Readable Data and Multiple Personality Disorder
Closing of Conference
|
| 10/27/2012 |
SkyDogCon 2 Videos
Most of the talks are up, full post coming soon. |
| 10/25/2012 |
Hack3rcon 3 Videos
I still have one video from Hack3rcon 3 left to edit, but I wanted to put all of
the talks out in the RSS before the
SkyDogCon talks come out. One more coming soon hopefully.
Keynote: Hacking Survival
Speakers: Larry Pesce
Next Generation Web Reconnaissance
Speakers: Tim Tomes
Intro to Network Traffic Analysis - Part 1
Speakers: Jon Schipp
Intro to Network Traffic Analysis - Part 2
Speakers: Jon Schipp
Automated Spear-twishing - It was only a matter of time
Speakers: Sean Palka
In case of ZOMBIES break glass
Speakers: Chris Payne
Building Dictionaries and Destroying Hashes Using Amazon EC2
Speaker: Steve Werby
Secrets of Running a Consulting Business
Speakers: Brian Martin
Bash Scripting 101 for Pen Testers
Speakers: Lee Baird
Keynote: Finding the MacGyver in You
Speakers: William A. Minear
EMP, yeah you know me..
Speakers: Adrian Crenshaw
Intro to Linux exploit development - Part 1
Speakers: John deGruyter
Intro to Linux exploit development - Part 2
Speakers: John deGruyter
This video is combined with the one above, but I'm too lazy to redo my numbering system. :)
Advanced Phishing Tactics � Beyond User Awareness
Speakers: Eric Milam, Martin Bos
DNS Reconnaissance
Speakers: Carlos Perez
Sponsors: Tenable Network Security
*SILVER*
Social Engineering Applied: Exploit the Target
Speakers: Keith Pachulski
From Patch to Pwnd
Speakers: Deral Heiland
Building a pad that will survive the times
Speakers: Branden Miller
Wielding Katana: A Pentesters Portable Pal
Speakers: Ronin |
| 10/20/2012 |
Hack3rcon 3 Videos, A Little Early
Those at Hack3rcon know I'm posting
videos on the site while I'm at the con. I noticed someone at the con looking
for them on the front page, but I had not linked to them there yet (Just Tweeted
them from @irongeek_adc). The
link above will take you to the Hack3rcon 3 video page, and I will make a longer
post when I have them all out there (but keep watching that page over the
weekend if you like). |
| 10/06/2012 |
Louisville Infosec 2012 Videos
Below are the videos from Louisville
Infosec 2012 conference. Sorry about the noise, I had no line in from the
house audio. My talk is not in here because the slides rig failed. You can see a
previous version of it here:
Dingleberry Pi Building a Blackthrow: More inexpensive hardware to leave behind
on someone else's network - Adrian Crenshaw
Index:
Keynote Jack Daniel
InfoSec Stress & Community
Nathan Heald - No
Keys, No Worries Lock Picking
Jeremy Druin - NOWASP Mutillidae 2.2 A web pen-testing environment for secure
development
Curtis Koenig - Grey Hats
and Bug Bounties
Deral Heiland - From Printer to Pwnd Leveraging multifunction printers during
penetration testing
James
Jardine - Ninja Developers App Sec Testing and SDLC
Joshua Bartley -
Data Hiding In Your Application
Keynote Michael Peters The Security TrifectaT - Isolation vs. Collaboration |
| 10/03/2012 |
Derbycon
2012, Day 3 Tracks 2, 3 & 4 Videos Posted In this batch we have:
Matt Weeks: Ambush- Catching Intruders at Any Point
Joshua Marpet: separating security intelligence from
security FUD
Steve Werby: Building dictionaries and destroying hashes
w/amazon EC2
Raphael Mudge:
Dirty Red Team Tricks II
David Schuetz (Darth Null) � Slow down cowpoke � When
enthusiasm outpaces common sense
Nicolle Neulist: Write your own tools with
Python
David McGuire: Maturing the Pen Testing Professional
Matt Presson: Building a database security program
Chris Jenks: Intro to Linux system hardening
Eric Milam: Becoming Mallory
Patrick Tatro: Why isn't everyone pulling security- this
is combat
Jason Frisvold: Taming Skynet-using the cloud to automate
baseline scanning
JP Dunning & Chris Silvers: Wielding Katana- A live
security suite
Mick Douglas � Sprinkler: IR
Matthew Perry: Current trends in computer law
Leonard Isham: SE me � SE you
CLOSING CEREMONY
See you next year, or at Hack3rcon,
Skydogcon or
Phreaknic.
|
| 10/02/2012 |
Derbycon
2012, Day 2 Tracks 3 & 4, Plus Day 3 Track 1 Videos Posted In this batch we have:
Michael Schearer � Flex your right constituion and
political activism in the hacker community
Eric Smith � Penetration testing from a Hot Tub Time
Machine
Chris Nickerson (ind303) � Tactical Surveillance: Look
at me now!
Jamie Murdock � How to create a one man SOC
Branden Miller / Bill Gardner � Building an Awareness
and training program
Dan Crowley / Chris Vinecombe � Vulnerability Spidey
Sense
Nathaniel
Husted � Everything you always wanted to know about
Security Academia (But were too afraid too ask)
Bill Sempf � What locksport can teach us about security
JP Dunning (.ronin) - The Glitch: Hardware With Hacking Made
Easy
Christopher Domas � The future of RE: Dynamic Binary
Visulization
Tom Eston / Kevin Johnson � Social Zombies: Rise of the
Mobile Dead
KC. Yerrid / Matt Jezorek / Boris Sverdlik (JadedSecurity)-
It's not your perimenter. It's you
Deral Heiland -Format String Vulnerabilities 101
Jack Daniel � How Screwed Are We?
Kellep Charles: Security Vulnerablity Assessments. �
Process and best practices
John Woods � So you got yourself an infosec manager job.
Now what?
K.C.
Holland (DevAuto) - Personal Darknet or How to get pr0n @
work
Tony DeLaGrange / Jason Wood:SH5ARK ATTACK- taking a
byte out of HTML5!
Matthew Sullivan: Cookie Cadger � taking cookie
hijacking to a new level
Stephen Haywood (AverageSecurityGuy) -
Introduction to Metasploit Post Exploitation Modules
Noah Beddome: The devils in the Details-A look at bad SE
and how to do better
Jay James & Shane MacDougall: Usine McAfee
secure/trustguard as attack tools
Roamer and Deviant Ollam - Welcome to NinjaTel, press 2 to
activate your device now
Laszlo Toth & Ferenc Spala: Think differently about
database hacking
|
| 10/01/2012 |
Derbycon
2012, Day 2 Tracks 1 & 2 Videos Posted In this batch we have:
Skip Duckwall / Chris Campbell � Puff Puff Pass � Getting the most out of your hash
Jordan Harbinger � Social Engineering Defense Contractors on LinkedIn and Facebook: Who's plugged into your employees?
Paul Asadoorian / John Strand � Everything they told me about security was wrong.
Zack Fasel � Pwned in 60 Seconds -From Network Guest to Windows Domain Admin
Ryan Elkins � Simple Security Defense to thwart an Army of Cyber Ninja Warriors
atlas: RfCat-subghz or bust
Georgia Weidman � Introducing the Smartphone Pentest Framework
Gillis Jones � The Badmin Project
Kyle (kos) Osborn � Physical Drive-By Downloads
Johnny Long � The Evolution of HFC
Dual Core (int0x80) � Moar Anti-Forensics � Moar Louise
Bruce Potter � Security Epistemology: Beliefs � Truth � and Knowledge in the Infosec Community
Josh More � Pen Testing Security Vendors
Jason Gunnoe & Chris Centore -Building the next generation IDS with OSINT
Babak Javadi / Keith Howell: 4140 Ways your alarm system can fail
Benjamin Mauch � Creating a powerful user defense against attackers
Bart Hopper � Hunting Evil
Doug Burks � Security Onion � Network Security monitoring in minutes
Direct downloads from Archive.org will be uploaded when I have all of Day 2
ready.
|
| 09/30/2012 |
Derbycon
2.0: The Reunion, Day 1 Videos Posted
Hi all. Expect these to come out in phases.
Opening Ceremony
HD Moore � The Wild West
Dan Kaminsky � Black Ops
Mudge � Cyber Fast Track; from the trenches
Jayson E. Street � Securing the Internet: YOU�re doing it wrong (An INFOSEC Intervention)
Jason Scott � Rescuing The Prince of Persia from the sands of time
Dave Marcus � 2FA-Enabled Fraud: Dissecting Operation High Roller
Rafal Los � House of Cards
Rob Fuller / Chris Gates � Dirty Little Secrets Part 2
Chris Hadnagy � Nonverbal Human Hacking
Rick Farina: The Hacker Ethos meets the FOSS ethos
Brent Huston � Info overload..Future shock.. IBM & nature of modern crime
Ian Amit � SexyDefense � the red team tore you a new one. Now what?
egyp7 � Privilege Escalation with the Metasploit Framework
Larry Pesce / Darren Wigley � Hacking Survival: So. You want to compute post-apocalypse?
James Arlen � Doubt � Deceit -Deficiency and Decency � a Decade of Disillusionment
Carlos Perez � DNS Reconnaissance
Sam Gaudet: Pentesting for non-pentesters�through virtual machines
Ryan Linn � Collecting Underpants To Win Your Network
Jerry Gamblin: is it time for another firewall or a security awareness program?
|
| 09/19/2012 |
How To Upgrade To Latest Mutillidae On Samurai WTF 2
Jeremy Druin has a new video:
This video covers upgrading the default version of NOWASP (Mutillidae) which
comes with SamuraiWTF 2.0 with the latest available version. On this particular
version of SamuraiWTF 2.0, NOWASP (Mutillidae) 2.1.20 was installed in the ISO.
The latest version of NOWASP (Mutillidae) available at the time of this video
was 2.3.7. In the video, the hosts file responsible for activating the links to
the "target" web applications was modified so the default web applications would
work. Also, the "samurai" start up script is reviewed to show why the LiveCD
version of Samurai includes working web app targets but the installed version
requires the targets be "activated". The video then covers how to upgrade the
existing default installation of NOWASP (Mutillidae) with the latest available
version. Additionally, the video discusses how to run the default version and
latest version of NOWASP (Mutillidae) side-by-side or replace the existing
installation with the latest version.
|
| 09/16/2012 |
Installing Latest Mutillidae On Samurai WTF Version 2
Jeremy Druin has a new video:
Samurai WTF is an excellent platform for web pen testing. A very large number of
tools are already included. An older version of NOWASP Mutillidae comes
pre-installed. This video covers installing the latest version on Samurai WTF
2.0. Installation requires downloading the latest verion of NOWASP Mutillidae,
unzipping the Zip file which contains a single folder named "mutillidae", and
placing the "mutillidae" folder into /var/www directory. Configuration is done
by opening the /var/www/mutillidae/classes/MySQLHandler.php file and changing
the default MySQL password from blank empty string to "samurai". Starting the
project is done by browsing to http://localhost/mutillidae and clicking the
Reset-DB button on the menu bar. |
| 09/15/2012 |
Web Shells and
RFIs Collection
I wrote a little script to periodically look through my web logs for unique RFIs
and Web Shells, and then collect them on one page where I can go look at them or
download them to add to my Web Shell library. Many of these attacks are repeated
multiple time, so I ignore the time fields in judging if an RFI/Web Shell is
unique. I may have to weed this over time as I imagine many of the links to Web
Shells will be 404ing over time. I also use nofollow and a referrer hiding
service so it does not look like I'm attacking anyone with the web shells. This
page will also let you link off to firebwall.com where you can use their PHP
decoder to look at the obfuscated code. Enjoy my Web Shell zoo, it should update
itself every hour or so. If you see your domain on the list of websites hosting
Web Shells you are likely pwned and should clean up your server. |
| 09/09/2012 |
Into to Metasploit - Jeremy Druin
This is the 5th in a line of classes Jeremy Druin will
be giving on pen-testing and web app security featuring
Mutillidae for the Kentuckiana
ISSA. This one covers Metasploit. |
| 09/04/2012 |
Teensy 3.0
As many of my readers know I've done a lot of work with the Teensy 2.0 in
projects such as the
programmable HID USB keyboard and my own
hardware keylogger. Now Paul Stoffregen is coming out with a new version,
Teensy 3.0. You should still have the easy of development that comes with
the Arduino framework (or more raw C/C++ if you like) but there are two major new
features, of many, that I'm excited about: More powerful 32 bit ARM Cortex-M4
and USB host support. Go check out Paul's Kickstarter page for more details and
added features. |
| 08/29/2012 |
SSH Phone Home: Using the Raspberry Pi as a proxy/pivot (Shovel a Shell)
I added a new section to my Raspberry Pi recipes page that covers setting up a
Raspberry Pi to send you a Reverse Shell using SSH (AKA: Shovel a shell). This
is pretty good for blowing past NAT and some firewalls with weak egress
filtering. The idea is that you can use these as drop boxes to leave on someone
else's network, then have them remote back out to you. These instructions should
work pretty much the same on any *nix device or distro that uses OpenSSH. |
| 08/13/2012 |
Irongeek's Logwatch Script To Grep For RFI, Webshells, Password Grabs, Web
Scanners, Etc.
This is a simple script I put together for those using shared hosting providers.
It let's you grep through your logs for things like RFIs, likely webshells,
passwords grabs, web scanners, etc. The video below gives more details. This can
be a great tool for collecting webshells. |
| 08/07/2012 |
Jeremy Druin
has two new Mutillidae/Web Pen-testing videos
Setting User Agent String And Browser Information
Introduction to user-agent switching: This video uses the Firefox add-on
"User-Agent Switcher" to modify several settings in the browser that are
transmitted in the user agent string inside HTTP requests. Some web applications
will show different content depending on the user agent setting making
alteration of the settings useful in web pen testing.
Walkthrough Of CBC Bit Flipping Attack With Solution
This video shows a solution to the view-user-privilege-level in Mutillidae.
Before viewing, review how XOR works and more importantly that XOR is
communicative (If A xor B = C then it must be true that A xor C = B and also
true that B xor C = A). The attack in the video takes advantage that the
attacker knows the IV (initialization vector) and the plaintext (user ID). The
attack works by flipping each byte in the IV to see what effect is produced on
the plaintext (User ID). When the correct byte is located, the ciphertext for
that byte is recovered followed by a determination of the correct byte to
inject. The correct value is injected to cause the User ID to change.
Mutillidae is available for download at
http://sourceforge.net/projects/mutillidae/. Updates about Mutillidae are
tweeted to @webpwnized along
with announcements about video releases. |
| 08/05/2012 |
Host Vulnerability Assessment with Nessus, NeXpose and Metasploitable 2
This is the 4th in a line of classes Jeremy Druin will be giving on pen-testing
and web app security featuring
Mutillidae for the Kentuckiana
ISSA. This one covers Nessus, NeXpose and Metasploitable 2. |
| 07/31/2012 |
BSides Las Vegas 2012 Videos
They have been up on Youtube since Friday, but now I have them indexed and
with links to where you can download AVIs from Archive.org. Enjoy. Thanks to
all of the BSides Crew for having me out to help record and render the videos.
@bsideslv,
@banasidhe,
@kickfroggy,
@quadling,
@jack_daniel
Breaking Ground
KEYNOTE, Jack Daniel: "The State of Security BSides"
Matt Weeks: "Ambush - Catching Intruders At Any Point"
Robert Rowley: "Max Level Web App Security"
Davi Ottenheimer: "Big Data's Fourth V: Or Why We'll Never Find the Loch Ness
Monster"
HD Moore: "Empirical Exploitation"
Christopher Lytle: "Puzzle Competitions and You"
Parth Patel: "Introducing 'Android Security Evaluation Framework' - ASEF"
Terry Gold: "RFID LOL"
Raphael Mudge: "Force Multipliers for Red Team Operations"
Andrew Hay & Matt Johansen: "Applications and Cloud and Hackers, Oh My!"
Brendan O'Connor: "Reticle: Dropping an Intelligent F-BOMB"
Josh Sokol/Dan Cornell:"The Magic of Symbiotic Security: Creating an Ecosystem
of Security Systems"
James Lester & Joseph Tartaro: "Burp Suite: Informing the 99% of what the 1%'ers
are knowingly taking advantage of."
dc949 - "Stiltwalker: Round 2"
Gillis Jones: "The Badmin project: (Na-na- nanana Na-na-nanana BADMIN)"
IPv6 Panel / Drinking Game
Proving Ground
Michael Fornal: "How I managed to break into the InfoSec World with only a tweet
and an email."
David Keene: "Breaking Microsoft Dynamics Great Plains - an insiders guide"
William Ghote: "Lotus Notes Password Hash Redux"
Spencer McIntyre: "How I Learned To Stop Worrying and Love the Smart Meter"
Christopher Campbell "Shot With Your OwnGun: How Appliances are Used Against
You."
Shawn Asmus, Kristov Widak: �Mirror Mirror � Reflected PDF Attacks using SQL
Injection�
Georgia Weidman: "Introducing the Smartphone Penetration Testing Framework"
Phil Young: "Mainframed - The Forgotten
Fortress"
Walt Williams: "Metrics that Suck Even Less"
Conrad Constantine: "The Leverage of Language: or : How I Realized Information
Theory could Save Information Security"
Jason Ding: "The Blooming Social Media Economics Built on "Fake" Identities
Lightning Talks
|
| 07/30/2012 |
Indiana University Southeast School of Business/MBA Review Updated: Emails
from Gil Atnip, Alan Jay White, Lawyer Cover Plate, Etc.
Hi all. Don't worry, I'll be back to infosec content soon (with a posting of
the BsidesLV videos). In the mean time, I just wanted to make an update post
about the situation I shared with you awhile back (see change log at the
bottom of the
IUS MBA
page). It seems many of the faulty/admins at IUS have been told to responded
to be with only an IU lawyer cover plate response that tells me to contact
IU Counsel. Unfortunately, the contacts I have at IU Counsel are not
responding to my requests either at this point. Another interesting tidbit,
seems someone has forwarded my MBA review site to the campus police (reverse
DNS lookup for the win), though I have little idea what allegations may have
been made (and they are not saying). I've posted the details on all this to
the page. At this point there is not much I can do but shut up and go away,
as is their intention, but I do ask for something from my readers. If you
know of an organization that cares about academic abuses/student rights to
due process, please forward them to the page. If you are a web admin, please
just link to the page so it's easier for perspective students to find if
they search for it. Thanks for your time. |
| 07/16/2012 |
OISF
2012 Videos Here are the talks from the OISF Anniversary Event 2012:
Conference Kickoff - Deral Heiland & Abyss of Cybersecurity - John Bumgarner
Size Does Matter: Password Tools and Data - Bob Weiss
Dingleberry Pi Building a Blackthrow: More inexpensive hardware to leave
behind on someone else's network - Adrian Crenshaw
Threat Model Express - Sahba Kazerooni |
| 07/16/2012 |
Bsides Cleveland 2012 Videos
Here are the talks from Bsides Cleveland 2012:
Secret Pentesting Technigues Shhh...Dave KennedyDave "ReL1K" Kennedy
Focusing on the Fool: Building an Awareness & Training Program - Branden
Miller & Bill Gardner
<? $People ?> Process Technology - Jeff @ghostnomad Kirsch
Dingleberry Pi Building a Blackthrow: More inexpensive hardware to leave
behind on someone else's network - Adrian "Irongeek" Crenshaw
Testing Enterprise DLP Systems // Advanced data exfiltration techniques -
Albert School
Automating Incident Response - Mick Douglas
Business Ramifications of the Internet's Unclean Conflicts - Rockie Brockway
Netflow for Incident Response - Jamison Budacki
Winter is Coming: Cloud Security in Dark Ages - Bill Mathews
What locksport can teach us about security - Bill Sempf <missing>
Pass the Hash like a Rockstar - Martin "PureHate" Bos
Naked Boulder Rolling - Applying Risk Management to Web Application Security
- J Wolfgang Goerlich
Anti-Forensics Filler - Irongeek
Outside the Echo Chamber - James Siegel (aka WolfFlight)
Pentesting ASP.NET - Bill Sempf |
| 07/15/2012 |
Basic Output via Raspberry Pi's GPIO and Serial/UART to an Arduinio or Teensy
Updated
While I was at Bsides Cleveland and OISF I found some problems with my
write-up and schematics, I've updated them now so you won't encounter blue
smoke. |
| 07/07/2012 |
More
Web Pen-Testing Videos From Jeremy Druin
Here are two more videos from Jeremy Druin (@webpwnized):
Using
Command Injection To Gain Remote Desktop On Windows
How To Exploit Metasploitable 2 With Nmap Nexpose Nessus Metasploit |
| 07/07/2012 |
Basic Output via Raspberry Pi's GPIO and Serial/UART to an Arduinio or Teensy
I added a "recipe" for using the Raspberry Pi's GPIO pins to interface
with a
Teensy (which means it is also no problem to talk to an Arduino). I've
included simple code, schematics/diagrams and videos to demonstrate. Right
now I'm just outputting from the Raspberry Pi to the Teensy, but input
should not be a problem either with the linked to resources. |
| 07/06/2012 |
Running an I2P Svartkast on the Raspberry Pi Updated
I updated the article a little to show how to set up a SSH tunnel through
the I2P darknet. Expect to see a few more Raspberry Pi posts as I prep up
for my talks at
Bsides Cleveland and
OISF. |
| 07/04/2012 |
Updates to About and
Irongeek in print pages
I noticed a few people at
Indiana
University Southeast looking at my
review
of the IUS MBA program, then looking at my "about"
page. Maybe they wanted to see if I was a crackpot. I decided to update
my about page to list
more of the talks I've done around the country since it was last updated. I
have also updated the Irongeek
in print page with more books my site or I have been referenced in. |
| 06/28/2012 |
Raspberry Pi Recipes
On this page I'll be posting little security ideas for the Raspberry
Pi. Current sections include:
I2P on the Raspberry Pi
Installing Metasploit on the Raspberry Pi
Making an �EtherLogger� to log Ethernet packets with the Raspberry Pi |
| 06/21/2012 |
Running an I2P Svartkast on the Raspberry Pi: Even more cheap hardware to
leave on someone else's network
This is sort of a sequel to a previous article I wrote titled "Running an
I2P Svartkast on the Raspberry Pi: Even more cheap hardware to leave on
someone else's network". In that article I answer the obvious question of
what the hell a Svartkast is, as well as show how to make one out of a
Raspberry Pi. |
| 06/16/2012 |
How To Install Metasploitable 2 With Mutillidae On Virtual Box
Here is another one from Jeremy Druin (@webpwnized):
This video covers installing Rapid7's Metasploitable 2.0 with Mutillidae on
a Virtual Box Host Only network. In addition to reviewing how to install
Metasploitable 2 on Virtual Box, the configuration of the virtual network
card is shown so that the Mutillidae web application running on
Metasploitable 2 can be accessed from a separate Backtrack 5 virtual machine
running on the same Host Only network. |
| 06/07/2012 |
Out of Character: Use of Punycode and Homoglyph Attacks to Obfuscate URLs for Phishing
This is the paper I was working on in last semester's class. Hope it is
helpful. |
| 06/07/2012 |
IUS MBA Program Continued: Amendment of records, FERPA and getting your side
put in the record
Again, not security related, but could be of interest to some. Next post I
swear will be security related. |
| 06/02/2012 |
Traceroute and Scapy Jeremy Druin @webpwnized
This is the 3rd in a line of classes Jeremy Druin will be giving on
pen-testing and web app security featuring
Mutillidae for the
Kentuckiana ISSA. This one covers Traceroute and Scapy. |
| 05/26/2012 |
AIDE
2012 Videos posted Recorded at AIDE
2012. Big thanks to Bill Gardner (@oncee)
for having me out to record.
Anti-Forensics: Occult Computing
Adrian Crenshaw
Out of Character: Use of Punycode and Homoglyph Attacks to Obfuscate URLs
for Phishing
Adrian Crenshaw
An Introduction to Traffic Analysis: A Pragmatic Approach
Jon Shipp
Pen Testing Web 2.0: The Client
Jeremy Druin
Breaking into Security
Frank J. Hackett and Justin Brown
Sabu the Hacker: The capture, the crimes, the damage done, the slip, the
apprehension, and the fallout.
Dr. Marcus Rogers
Jill McIntyre
Boris Sverdlik
Ronald Layton, U.S. Secret Service
BNAT Hijacking: Repairing Broken Communication Channels
Jonathan Claudius
Setting up BackTrack and automating various tasks with bash scripts
Lee Baird
Going on the Offensive - Proactive Measures in Securing YOUR Company
Dave Kennedy |
| 05/23/2012 |
BSidesCleveland
Here is another event I will be speaking at.
What:
BSidesCleveland
When: Friday, July 13, 2012
Where: Embassy Suites Cleveland - Rockside
Address: 5800 Rockside Woods Boulevard, Independence 44131
Cost: Free (as always!)
Register at:
http://www.securitybsides.com/w/page/27427415/BSidesCleveland
Submit to CFP at:
http://www.securitybsides.com/w/page/53552319/BSidesClevelandCFP
|
| 05/22/2012 |
Homoglyph
Attack Generator Updated: Obfuscating EXEs, scripts and documents using 'Right-To-Left Override' (U+202E)
Added option to use 'Right-To-Left Override' (U+202E) so you can do some stupied
EXE tricks, and added a linkless output so you can copy & paste your homography
without formatting |
| 05/21/2012 |
Gaining Administrative Shell Access Via Command Injection
Here is another one from Jeremy Druin (@webpwnized):
Using command injection against the Mutillidae web application, we gain a root
shell (Administrative Windows cmd shell). The server is fully patched with
anti-virus running and a firewall blocking port 23. Additionally the telnet
service is disabled. With the command injection vulnerability, this video
demonstrates how misconfiguring web services can have serious consequences for
security. Additionally we review how to remediate command injection
vulnerabilities and discuss some of the defects which expose the server to
compromise.
|
| 05/21/2012 |
Offensive-Security Ohio Chapter (OSOC) Version of OSInt/Footprinting Talk
This is the version of my OSInt/Footprinting talk as given at the
Offensive-Security Ohio Chapter (OSOC) class on May 18th. I did not have my
video gear with me, so @securid did
the recording. Videos can also be downloaded from
http://www.1dave1cup.com/ |
| 05/21/2012 |
Review of
the IUS (Indiana University Southeast) MBA Program (and a bit about filing
student grievances)
Most of my writings are on Information security, but this one delves into
something else. It may still be of interest to those with a security mindset. I
hope that it will serve two purposes: 1. To help other students that file
grievances against faculty learn from my experience, and 2. convince those
interested in pursuing an MBA in the Louisville area to go someplace other than
the IUS MBA program. |
| 05/12/2012 |
Intro to Scanning: Nmap, Hping, Amap, TCPDump, Metasploit, etc. Jeremy Druin
This is the 2nd in a line of classes Jeremy Druin will be giving on pen-testing
and web app security featuring
Mutillidae for the Kentuckiana
ISSA. This one covers scanning Nmap, Hping, Amap, TCPDump, Metasploit, etc. |
| 05/06/2012 |
Jeremy Druin did some more Mutillidae/Web Pen-testing videos
At some point, I will start putting up some of my own content :) I have done
some tricks that I hope will make the page load better, but I'm not sure about
the browser compatibility. In the mean time, here is some more of Jeremy's work:
Using Metasploit Hashdump Post Exploit Module Creds Table And John
This video shows how to have the hashdump post exploitation module automatically
populate the creds table in the metasploit database, then export the credentials
to a file suitible to pass to the john the ripper tool in order to audit the
passwords.
Using Metasploit Community Edition To Determine Exploit For Vulnerability
In previous versions of Metasploit it was possible to run "db_autopwn -t -x" in
the msfcomsole in order to have metasploit guess the best exploits for a given
vulnerability. This video looks at alternative functionality for the depreciated
"db_autopwn -t -x" option in older versions of Metasploit's msfconsole.
Metasploit Community Edition has similar exploit analysis functionality
accessible via the web based GUI.
|
| 05/03/2012 |
More Mutillidae/Web Pen-testing videos from Jeremy Druin Jeremy had two
more videos for you. It's beginning to become a load problem with all the iframe
embedded videos :). I'm willing to take suggestions.
Using Hydra To Brute Force Web Forms Based Authentication Over Http
This video covers using nmap to ping sweep network then discover ports on two
machines to locate a web server on which Mutillidae is running. Once the web
server is running, the site is loaded into Firefox and the login page is
located. Using View-Source, Burp-Suite, and the sites registration, the login
process is studied. Potential usernames are gathered from using Reconnoitter,
CeWL, and the sites own blog page. A password file from john the ripper is used.
With the potential usernames and passwords in hand, hydra is used in
http-post-form mode to search for a username and password which can log into the
site.
Connect To Unreachable Web Site Through Meterpreter Port Forwarding
This video covers accessing a web site that is normally unreachable from our
Backtrack 5 box. However, after gaining a session on a third box, we forward our
web browser through the compromised host in order to browse the website. The
port forwarding is done via a meterpreter session on the compromised host. After
setting up the port forward, the browser is able to use the compromised host as
a relay (almost like a web proxy) in order to browse to the "internal" web
application. |
| 04/27/2012 |
DerbyCon tickets go on sale this today!
(Friday April 27th) � CFP OPEN!
We will be opening up ticket sales on Friday at 1:00PM EST on April 27th 2012.
Both training and normal conference tickets will be going on sale at this time.
We feel we have a very stable ticketing system at this point from the tests last
week and don�t anticipate any major issues! We look forward to seeing everyone
at DerbyCon this year� It�s going to be amazing!!!
Call for papers are also open! Check out the
CFP section on the
DerbyCon here.Some of the current speakers: Jeff Moss, Dan Kaminsky, Kevin
Mitnick, Martin Bos, Adrian Crenshaw, HD Moore, Dave Kennedy, Ryan Elkins,
Johnny Long, Chris Nickerson, Chris Gates, Eric Smith, Paul Asadoorian, Rob
Fuller, Larry Pesce, Chris Hadnagy, John Strand, Peter Van Eeckhoutte, int0x80,
Thomas d�Otreppe, Jack Daniel, Jason Scott, Deviant Ollam, Jayson E. Street,
James Lee, Rafal Los, Kevin Johnson, Tom Eston, Rick Hayes, Georgia Weidman and
Karthik Rangarajan
Check out
videos of
last year's Derbycon here. |
| 04/23/2012 |
2 more Mutillidae/Web Pen-testing videos from Jeremy Druin Three more great videos from Jeremy Druin
(@webpwnized ):
Creating Syn Port Scan Manually With Scapy
Contrast Nmap And Amap Service Version Detection Scanning |
| 04/23/2012 |
Outerz0ne 8 (2012) Videos Here is the list:
Kickin' it off for year number 8! Outerz0ne: The History, The Legend SkyDog
Bare Metal Install of Linux from a Network Server Halfjack
How To Cyberstalk Potential Employers IronGeek
Complex Litigation in America Tyler Pitchford
Hook, Line and Syncer: Outerz0ne Remix Chris Silvers
IPv4 -to- IPv6 Service Providers Challenges Jeremy Schmeichel & SlimJim
Your Camera is Worth $300,000 to Microsoft Scott Moulton
Outerz0ne Closing and Awards Skydog and Crew |
| 04/16/2012 |
Notacon 9 (2012) Videos
These are the videos from
the 9th Notacon conference held April
12th-15th, 2012. Not all of them are security related, but I hope my
viewers will enjoy them anyway. Thanks to Froggy and Tyger for having me up, and to the video
team: SatNights, Widget, Securi-D, Purge, Bunsen, Fry Steve and myself. Sorry about
the sound issues, but there is only so much pain I want to go through in post. Also for some videos we only
have the slides or the live
video, but not both.
List:
Track 1
Day 1
Game Maker: Crash Course
Chris Sanyk
Minute Man: All I Need is 60 Seconds
Rick Deacon
Get your kicks on route IPv6
Mike Andrews
We lit IPv6. This is what happened.
Jeff Goeke-Smith
Civic Hacking
Jeff Schuler, Beth Sebian
Vulnerabilities of Control Systems in Drinking Water Utilities
John McNabb
Hacking for Freedom
Peter Fein
Building a Game for the Ages (well, the young ages anyway)
Bill Sempf
Day 2
Mo data? Mo problems!
Mick Douglas
What if Max Zoran Succeeded? Living without Silicon Valley
movax
How to totally suck at Information Security
Christopher Payne, Doug Nibbelink
(Just About) Everything you think you know about Wilderness Survival is
Wrong
Mark Lenigan
Baking in Security
Jeff �ghostnomad� Kirsch
Your Hacker Class is Bullsh1t
Christopher Payne
REFACTORING THE REVOLUTION (Occupy as an Agile project)
Some Guy On Bridge
Custom Distributions Via Package Aliasing: release of The Pentest
Repository
Ryan Holeman
Numbers, From Merely Big to Unimaginable
Brian Makin
Whose Slide Is It Anyway?
nicolle �rogueclown� neulist
(Sorry, I can't post this one since we did not get permission from
everyone) Track 2
Day 1
I�m a Hacker�and I�m a QSA (Hacking PCI Requirement 6.6. Why Your Web
Applications are Still Not Secure)
David Sopata, Gary McCully
Neurohacking: from the bottom up
meecie
Code That Sounds Good: Music Theory and Algorithmic Composition
nicolle �rogueclown� neulist
Collaboration. You keep using that word�
Angela Harms
Kinetic Security
Knuckles, Jeff �ghostnomad� Kirsch, Ghostnomadjr
Milkymist: video synthesizers at the cutting edge of open source
hardware
S�bastien Bourdeauducq
Development Operations: Take Back Your Infrastructure
Mark Stanislav
Exercise Your Mind and Body
Suellen Walker, Joe Walker
Day 2
How to Market the Morally Broken and Sociologically Depraved: A Guide to
Selling Your Local Hacker Conference to the Public
Jaime Payne
Geocaching 101
Jon Peer
Notacon 9 Network
1984 2012 Legal Privacy Trends
Nick Merker
The Sword is Mightier than the Pen(test): an Introduction to Fencing
Brian Stone, Amy Clausen
What Locksport Can Teach Us About Security
Bill Sempf
Octodad: Building a Better Tentacle Ragdoll
Devon Scott-Tunkin |
| 04/15/2012 |
More Mutillidae/Web Pen-testing videos from Jeremy Druin Three more great videos from Jeremy Druin
(@webpwnized ):
Detailed Look At Linux Traceroute
This video takes a detailed look at the traceroute program in Linux. The newer
traceroute is used (version 2.0.18). The later versions have the ability to send
packets of different protocols (i.e. TCP) to the target. This feature was
previously found in the LFT (Layer Four Traceroute) tool but not found in the
Linux traceroute. While LFT still is more feature-rich than the traceroute built
into Linux, the new features in Linux traceroute make the tool very useful and
quite capible. It helps to understand how the traceroute tool forms the packets,
to what ports the packets are sent, and what protocols can be used to send the
packets. This information can be used to get traceroute commands to work through
firewalls and HIPS systems when ICMP and/or UDP and/or most TCP ports are
blocked.
Introduction To TCPDump Network Sniffer
This video is an introduction to the tcpdump network packet sniffer/capture
tool. The video is relatively long because of the demo used required "building
up" to the HTTP capture. The video only covers the basics but is meant to be a
good introduction to practical use of tcpdump.
Basics Of Using The Maltego Reconnaissance Graphing Tool
This video looks at using Maltego to both gather and organize information in a
customer pen-test. Maltego is a GUI-based tool for Linux which is included in
the Backtrack 5 R2 release. The tool is able to gather information from public
sources on entities. The Community Edition (used in this video) is free. There
is a paid-version with more features. The site used in this video is
irongeek.com and was used with written permission from the owner. If following
along, please use a domain for which you have permission. |
| 04/08/2012 |
Finding Comments And File Metadata Using Multiple Techniques
Jeremy Druin has made a new video:
This video has two related parts. The first part discusses finding the comments
in Mutillidae related to the "comments challenge". This is an easy challenge in
Mutillidae but the techniques can be extended to search entire sites for
comments. The second part of the video looks at finding metadata in general
using a variety of tools.
The tools used are Firefox "View Source", W3AF, grep, wget, Burp Suite, exiftool
and strings. The demo site used is Mutillidae, which is a free open-source fully
functional PHP site with a MySQL database. The site runs on localhost or it can
be run in a virtual network as a practice target or capture the flag target. It
is not a good idea to run Mutillidae publically because it will get hacked.
Mutillidae is available at Sourceforge and Irongeek.com. Along with the project
is several documents and an installation guide for Windows 7.Also, I updated
the
Pen-testing practice in a box: How to assemble a virtual network post to fix
an audio issue (it was cutting out after a certain amount of time). |
| 04/07/2012 |
Pen-testing practice in a box: How to assemble a virtual network
This is the first in a line of classes Jeremy Druin will be giving on
pen-testing and web app security featuring
Mutillidae for the Kentuckiana
ISSA. Topics: Virtual Box Installation, Installing virtual machines,
Configuring virtual networks - bridged, nat, hostonly, USB devices in virtual
machines, Wireless networks in virtual machines, Installing Guest Additions, How
to install Mutillidae in Windows on XAMPP, How to install Mutillidae in Linux
Samurai |
| 04/05/2012 |
Mutillidae How To Use Dradis To Organize Nmap And Nessus Scan Results
New video from
Jeremy Druin:
The latest version of Dradis (2.9) has excellent import speed compared to
version 2.7. This video looks at using the import features of Dradis to organize
the scan results from an nmap scan and a Nessus 5 scan. Dradis is a tool that
allows pen testers, auditors, and vulnerability assessors to organize their work
by server or other categories. The Dradis starts a web server which other team
members can share information as well. |
| 04/03/2012 |
Homoglyph
Attack Generator Updated
I found a list of IDN blacklisted characters on Mozilla's site and added them. I
also added a table of the homoglyphs I'm using. |
| 04/01/2012 |
Two More Web Security Videos From
Jeremy Druin
Jeremy Druin has made two more videos:
How To Upgrade To Nessus 5 On Backtrack 5 R2
This video looks at upgrading
Nessus 4 to Nessus 5. The operating system used in the video is Backtrack 5 R2.
Nessus 4 was successfully registered and running on this OS prior to attempting
to upgrade to Nessus 5. If a fresh Nessus install is needed, the process is
different.
Creating Reports And Metasploit Db Importable Reports With Nmap Xml Output
Nmap reporting is excellent with the XML option but this is not used in a lot
of cases. The XML output from nmap can be imported into other tools such as the
Metasploit Community Edition (Import button), metasploit DB, and other tools.
Also, the XML format can be opened in a web browser to produce a well-formatted
report suitable for attachment to a pen-test. |
| 03/29/2012 |
Outerz0ne Video Move
Still working on moving videos to YouTube to support more devices. Since
Outerz0ne is coming up I decided to move
their videos next:
Outerz0ne 2011:
SkyDog - Opening
Ceremonies/etc.
SkyDog - The Modern Day Hacker
IronGeek -
Rendering Hacker Con Videos with AviSynth
MadMex -
Windows Command Line Incident Response
HalfJack -Building your
Own Green Home
Beau Woods - What Companies and Vendors must know about securing mobile
devices, mobile applications, access and data.
Rick Hayes -
Assessing and Pen-Testing IPv6 Networks
Pure Hate - Why your
password policy sucks
Billy Hoffman -
Advice on starting a start-up
Contest Prize
Giveaway, Awards, Closing Ceremonies
Outerz0ne 2010:
Intro to Outerzone and Talk 1 - Security People Suck - Gene Bransfield
IronGeek - Turning the Zipit 2 into a mobile hacking device
Freeside
PBR90X - Social Networking #FAIL
Scott Moulton - Hard
Drive Kung Fu Magic
Brian Wilson -Docsis Coolness
BobTalks
Billy Hoffman -
Web Performance Talk Craziness
Closing Ceremonies
Outerz0ne 2009
Morgellon - *Duino-Punk! Manifesting Open Source in Physical Space from Outerz0ne 5
Tyler Pitchford - They took my laptop! - U.S. Search and Seizure Explained
SkyDog - Screen Printing Primer - Make your own Con Shirt!
SlimJim100 - Live Demo of Cain & Able and the Man-in-the-middle-attack
Nick Chapman - Embedded Malicious Javascript
Makers Local 256 - A primer on hackerspaces
Scott Moulton - Reassembling RAID by SIGHT and SOUND!
Rob Ragan - Filter Evasion - Houdini on the Wire
Acidus (Billy Hoffman) - Offline Apps: The Future of The Web is the Client?
Closing
Also, a video I did about Outerz0ne and
Notacon 2009:
Outerz0ne and Notacon 2009 Hacker Cons Report
|
| 03/28/2012 |
Manual Directory Browsing To Reveal Mutillidae Easter Egg File
Jeremy has made another video:
This video looks at manual testing for directory browsing misconfiguration
vulnerabilities in Mutillidae. For directory browsing brute forcing, OWASP
DiRBuster or Burp-Suite Intruder are great tools. However, Mutillidae gives away
some of its directory paths when serving PDF and other files. These can be
tested manually to reveal the Mutillidae Easter egg file. Also common directory
names like "include" and "includes" can be tried quickly just using a browser
before firing up the tools. |
| 03/26/2012 |
Password Exploitation Class (YouTube Migration)
I've migrated the "Password Exploitation Class" to YouTube. This should allow it
to be viewed on more devices.This is a class we gave for the Kentuckiana ISSA
on the the subject of password exploitation. The Password Exploitation Class was
put on as a charity event for the Matthew Shoemaker Memorial Fund. The speakers
were Dakykilla,
Purehate_ and Irongeek. |
| 03/26/2012 |
Anti-Forensics: Occult Computing Class (YouTube Migration)
I've migrated the "Anti-Forensics: Occult Computing Class" to YouTube. This
should allow it to be viewed on more devices.This is a class I gave for the
Kentuckiana ISSA on the the subject of Anti-forensics. It's about 3 hours long,
and sort of meandering, but I hope you find it handy. For the record, Podge was
operating the camera :) Apparently it was not on me during the opening joke, but
so be it, no one seemed to get it. I spend way to much time on the Internet it
seems. Also, I'm in need of finding video host to take these large files. This
class video is 3 hours, 7 min and 1.2GB as captured. |
| 03/26/2012 |
OSInt, Cyberstalking, Footprinting and Recon: Getting to know you (YouTube
Migration)
I've migrated the "OSInt, Cyberstalking, Footprinting and Recon: Getting to know
you" to YouTube. This should allow it to be viewed on more devices.The
following are videos from the Footprinting/OSInt/Recon/Cyberstalking class I did
up in Fort Wayne Indiana for the Northeast Indiana Chapter of ISSA. I've split
the class into three videos by subtopic, and included the text from the
presentation for quick linking. |
| 03/24/2012 |
Mutillidae Injecting Cross Site Script Into Logging Pages Via Cookie Injection
Jeremy has made another video (I can't keep up):
By setting the values of browser cookies, then purposely browsing to a web page
that logs the value of user cookies, it may be possible to inject cross site
scripts into the log files or the log data table of the web site. Later when the
logs are reviewed by Administrators, the cross site scripts may execute in the
administrators browser. The video uses the Mutillidae capture data pages as an
example. In Mutillidae one of the capture the flag events is to poison the
attackers browser by purposely exposes the attacker to a cross site script. This
can be done by infecting a cookie then "letting" the attacker trick you into
visiting the capture data page. |
| 03/24/2012 |
Mutillidae Generate Cross Site Scripts With SQL Injection
Jeremy has made another video:
This video discusses an advanced SQL injection technique. The SQL injection is
used to generate cross site scripting. This is useful when cross site scripts
cannot be injected into a webpage from a client because web application
firewalls or other scanners are in place. When an SQL injection can be snuck
past the WAF, it is possible to have the SQL injection generate the Cross Site
Script dynamically. |
| 03/22/2012 |
DOJOCON
2010 Videos Migrated To YouTube
I've started to migrate the con videos I record and embed on this site to
YouTube. I'm doing this for a few reasons:
1. Vimeo took down Dave Marcus' talk because they said it was in
violation of their TOS, and when I tried to explain to them what it was about
they would not email me back (and I was a paying customer to their service at the
time).
2. I'm now allowed longer videos on YouTube, so why not.
3. This should support more devices.
I've started with DOJOCON 2010 to get Dave's talk back up. Below
are the videos from the conference, at least the ones I can show :), enjoy.
Index:
Tiffany Strauchs Rad, @tiffanyrad:
International Cyber Jurisdiction: "Kill Switching" Cyberspace, Cyber
Criminal Prosecution & Jurisdiction Hopping
John Strauchs, @strauchs:
Security and IT Convergence
Richard Goldberg, @GoldbergLawDC:
Rules of Engagment: Mitigating Risk in Information Security Work
Jon McCoy:
Ninja Patching .NET
Marco Figueroa, @marcofigueroa
& Kevin Figueroa:
Detecting & Defending Your Network using Nepenthes/Shaolin Tools
Dave Marcus, @davemarcus:
Using Social Networks To Profile, Find and 0wn Your Victims
Brian Baskin, @bbaskin:
P2P Forensics
Jonathan Abolins, @jabolins:
Internationalized Domain Names & Investigations in the Networked World
Deviant Ollam, @deviantollam:
Don't Punch My Junk
Michael Shearer, @theprez98:
How to 0wn an ISP in 10 Minutes
Christopher Witter, @mr_cwitter:
Enterprise Packet Capture on Da'Cheap
Ben Smith:
Printer Exploitation
Adrian Crenshaw, @irongeek_adc:
Malicious USB Devices: Is that an attack vector in your pocket or are you
just happy to see me?
Shyaam Sundhar, @EvilFingers
and John Fulmer, @DaKahuna2007:
Is the IDS Dead?
Chris Nickerson, @indi303:
The State of (In)Security
Gal Shpantzer, @shpantzer:
Security Outliers: Cultural Cues from High-Risk Professions
Michael Smith, @rybolov:
DDoS
|
| 03/15/2012 |
Web Application Pen-testing Tutorials With Mutillidae
When I started the
Mutillidae project it was with the intention of using it as a teaching tool
and making easy to understand video demos. Truth be told, I never did as much
with it as I intended. However, after Jeremy Druin (@webpwnized)
took over the development it really took off. I have since come to find out he
has been doing A LOT of YouTube video tutorials with Mutillidae, which he said I
could share here. I will be copying his descriptions with slight editing and
embedding his videos in this page. Videos include:
Determine Http Methods Using Netcat
Determine Server Banners Using Netcat Nikto And W3af
Bypass Authentication Using SQL Injection
Using Menus
Bypass Authentication Via Authentication Token Manipulation
Explanation Of HTTPonly Cookies In Presense Of Cross Site Scripting
Closer Look At Cache Control And Pragma No Cache Headers
Demonstration Of Frame Busting Javascript And X-Frame Options Header
How To Install And Configure Burp Suite With Firefox
Basics Of Web Request And Response Interception Using Burp Suite
Brute Force Authentication Using Burp Intruder
Automate SQL Injection Using SQLMap To Dump Credit Cards Table
Command Injection To Dump Files Start Services Disable Firewall
How To Exploit Local File Inclusion Vulnerability Using Burp Suite
HTML Injection To Popup Fake Login Form And Capture Credentials
Two Methods To Steal Session Tokens Using Cross Site Scripting
How To Bypass Maxlength Restrictions On HTML Input Fields
Two Methods To Bypass Javascript Validation
Three Methods For Viewing Http Request And Response Headers
Basics Of SQL Injection Timing Attacks
Basics Of SQL Injection Using Union
Basics Of Inserting Data With SQL Injection
Inject Root Web Shell Backdoor Via SQL Injection
Basics Of Using SQL Injection To Read Files From Operating System
How To Locate The Easter Egg File Using Command Injection
Injecting Cross Site Script Into Stylesheet Context
Introduction To Http Parameter Pollution
Basics Of Injecting Cross Site Script Into HTML Onclick Event
Basics Of Finding Reflected Cross Site Scripting
Analyze Session Token Randomness Using Burp Suite Sequencer
Using Nmap To Fingerprint Http Servers And Web Applications
Spidering Web Applications With Burp Suite
Basics Of Burp Suite Targets Tab And Scope Settings
Brute Force Page Names Using Burp Intruder Sniper
Using Burp Intruder Sniper To Fuzz Parameters
Comparing Burp Intruder Modes Sniper Battering RAM Pitchfork Cluster Bomb
Demo Usage Of Burp Suite Comparer Tool
Import Custom Nmap Scans Into Metasploit Community Edition
Using Metasploit Community Edition To Locate Web Servers
XSS DNS Lookup Page Bypassing Javascript Validation
Use Burp Suite Sequencer To Compare Csrf Token Strengths
How To Remove PHP Errors After Installing On Windows Xampp
Quickstart Guide To Installing On Windows With Xampp
Basics Of Running Nessus Scan On Backtrack 5 R1
How To Import Nessus Scans Into Metasploit Community Edition
Basics Of Exploiting Vulnerabilities With Metasploit Community Edition
Sending Persistent Cross Site Scripts Into Web Logs To Snag Web Admin
Quick Start Overview Of Useful Pen-Testing Addons For Firefox
Three Methods For Viewing Javascript Include Files
Reading Hidden Values From HTML5 Dom Storage
How To Execute Javascript On The Urlbar In Modern Browsers
Adding Values To Dom Storage Using Cross Site Scripting
Alter Values In Html5 Web Storage Using Cross Site Script
Altering Html 5 Web Storage Values Using Persistent XSS
Altering HTML 5 Web Storage With A Reflected XSS
|
| 03/13/2012 |
Crypto & Block Cipher Modes (OpenSSL, AES 128, ECB, CBC)
Hopefully this will give a nice visual illustration of how Electronic codebook (ECB)
and Cipher-block chaining (CBC) work using AES-128 and OpenSSL. You can learn a
lot from a known plain text, and repeating patterns. Inspired by labs from Kevin
Benton & "Crypto Lab 1" SEED. |
| 03/12/2012 |
Shared Hosting MD5 Change Detection Script Updated
Fixed an issue with permlog.txt not being put in the $ScriptDir directory. |
| 03/12/2012 |
Derbycon 2.0: The Reunion Promo Video Posted
Dave Kennedy has posted a promo video
form Derbycon 2012. A few prominent speakers have been announced. Hope you all
can make it this year. To see what you missed from
Derbycon
2011, go visit the video page. |
| 03/03/2012 |
Proposal for
"Out of Character: Use of Punycode and Homoglyph Attacks to Obfuscate URLs for
Phishing"
Below is a
project I'm doing for class. If you want to make suggestions and tell me about
weird Unicode/Homoglyph security issues,
please email me. If you
want to play with making homographs, look at my
Homoglyph
Attack Generator. |
| 02/28/2012 |
Shared Hosting MD5 Change Detection Script
I was wanting a simple shell script that would monitor the files on a site, and
report any changed via email.
Dave Kennedy's Artillery was
close to what I needed (and does a lot more), but I wanted something I could run
on my shared hosting account. This is what I came up with, for better or worse.
If nothing else, it was a good exercise in BASH scripting, and may come in handy
for those that want to make something similar. |
| 02/22/2012 |
Malicious USB Devices Page Updated With Videos
I recently found out that the CACR at Indiana
University posted a video of a talk I did for them awhile back, so I decided
to update my Malicious USB Devices page to embed it and the other versions of
the talk I have. |
| 02/21/2012 |
InfoSec Daily Podcast 600 Tonight
The ISD Podcast is having its 600th episode tonight, Feb 21st 2012. Come join us
on the live stream
and IRC (#isdpodcast on
Freenode) at 8PM EST. |
| 02/20/2012 |
How I Got Pwned: Lessons in Ghetto Incident Response
For those wondering about the details of my recent defacement. |
| 02/05/2012 |
ShmooCon Firetalks 2012 Videos
Link:http://www.irongeek.com/i.php?page=videos/shmoocon-firetalks-2012
Night 1
�How Do You Know Your Colo Isn�t �Inside� Your Cabinet, A Simple Alarm Using Teensy� by David Zendzian
�Bending SAP Over & Extracting What You Need!� by Chris John Riley
�ROUTERPWN: A Mobile Router Exploitation Framework� by Pedro Joaquin
�Security Is Like An Onion, That�s Why it Makes You Cry� by Michele Chubirka
�Five Ways We�re Killing Our Own Privacy� by Michael Schearer
Night 2
�Cracking WiFi Protected Setup For Fun and Profit� by Craig Heffner
�Passive Aggressive Pwnage: Sniffing the Net for Fun & Profit� by John Sawyer
�Ressurecting Ettercap� by Eric Milam
�Security Onion: Network Security Monitoring in Minutes� by Doug Burks
�Remotely Exploiting the PHY Layer� by Travis Goodspeed
|
| 02/05/2012 |
ShmooCon Epilogue 2012 Talks
Includes:
Resurrection of Ettercap: easy-creds, Lazarus & Assimilation
Eric Milam - (Brav0Hax) &
Emilio Escobar
Media Hype and Hacks that Never Happened
Space Rouge
More than one way to skin a cat: identifying multiple paths to compromise a
target through the use of Attach Graph Analysis
Joe Klein
Proper Depth / Breadth testing for Vulnerability Analysis and fun with tailored
risk reporting metrics.
Jason M Oliver
Extending Information Security Methodologies for Personal User in Protecting
PII.
John Willis
Stratfor Password Analysis
Chris Truncer
Intro To Bro
Richard Bejtlich
Javascript obfuscation
Brandon Dixon |
| 01/21/2012 |
Unix File Permissions and Ownership (CHOWN, CHMOD, ETC)
I'm taking a security class were we had a lab on Unix/Linux file system
permissions. I decided I might as well record it, and the steps taken, along
with explanations as to what I was doing to set the permissions such as read,
write, execute, SetUID, SetGID and the Stickybit. Kevin Benton created the lab,
so I'd like to give him credit for inspiring me to do this video. |
| 01/16/2012 |
Basic Setup of Security-Onion: Snort, Snorby, Barnyard, PulledPork, Daemonlogger
Thanks to Doug Burks for making building a Network Security Monitoring Server
much easier. I mentioned Snort, Snorby, Barnyard, PulledPork and Daemonlogger in
the title, but there is a lot more on the distro than that. This is a nice way
to get an IDS up and running featuring pretty frontends without going into
dependency hell. |
| 01/07/2012 |
Pen-Testing Web 2.0: Stealing HTML5 Storage & Injecting JSON Jeremy Druin
This is Jeremy's talk from a
recent ISSA meeting. In it he
covers what the title says, showing off stealing of HTML 5 storage, injecting
JSON, using Burp Suite,
Muttillidae and some XSS attack fun. Sorry about the noise in the first bit,
I had to set the camera up a ways off and it picked up my bag of chips better
than it did Jeremy's talk. @webpwnized |
| 01/01/2012 |
Video Posted and Code Updated for Homemade Hardware Keylogger
My video from NeoISF is now posted:
PHUKD/Keylogger
Hybrid.
The code has been updated in the following ways:
On the PIC side: Updated Firmware for the USB Host Module - PIC24FJ256GB106
to work with more keyboards.
On the Teensy side:
0.04:
* If a keyboard was plugged in after the keylogger was already
powered on, it would type "i7-". I added code
to fix this problem.
* Fixed RAW serial debug mode not to print key
* Changed name of variable "lasttenletters" to "lastfewletters" and
expanded it to 60.
* Ctrl+Alt+Y is now used for typing more debugging details.
* Implemented likely to fail code for unlocking workstation using
captured password.
* I had some problems with running out of SRAM because of all of my
static strings. I started using the F()
function to pull these strings from flash memory to solve this
issue.
* Fixed a case issue with lastfewletters. I did not know the method
changed it in place.
* Fixed a bug in HIDtoASCII that made it top row of number keys not
work right. |
| 12/08/2011 |
DIY USB And PS/2 Hardware Keyloggers/PHUKD Hybrids Updated
I've updated my Do It Yourself Keylogger's project site with the following
information.
I've uploaded improved code,
Just PS/2:
* Converted ints to bytes in many places. Why take the extra space? :)
Both USB and PS/2:
* Made sure it worked with Arduino 1.0.
* Switched to using the SD library that comes with Teensyduino (from the
comments, it looks like
it's a wrapper by SparkFun Electronics around William Greiman's work).
* Changed the variables "file" to "logfile" and "filename" to "logfilename" to
be less ambiguous.
I also embedded my talk from Skydogcon and pasted my class project report on
the end which gives a lot more details about how this hardware keylogger was
created and why. |
| 12/05/2011 |
Programmable HID USB Keystroke Dongle Library Updated With OS X Functionality
I updated the PHUKD library to 0.4. There are some new function. OS X Spotlight
and Terminal code was provided by Adam Baldwin and Aaron Howell
ngenuity-is.com /
evilpacket.net.
jp (.ronin) http://www.hackfromacave.com also
provide some source code for the OS X side, but I ended up using Adam and
Aaron's. The functions added were:extern void CommandAtRunBarOSX(char *SomeCommand);
extern void CommandAtNewTerminal(char *SomeCommand);
extern void ShrinkCurWinOSX();
I also tested to make sure it worked with Arduino 1.0. |
| 12/03/2011 |
NetworkMiner Professional for Network Forensics
This video was made to show some of the extra features of NetworkMiner
Professional, like Pcap-over-IP, running on OS X under Mono, Export results to
CSV / Excel, Geo IP localization, Host coloring support, and Command line
scripting support. |
| 11/30/2011 |
Mutillidae 2.1.7 Deliberately Vulnerable Web App Updated (a lot) Jeremy
Druin has been doing a lot of work on Mutillidae since I last posted to the
front page/rss about it. Here is the change long since the last time I mentioned
it:
Change Log for Mutillidae 2.1.7:
Added a new page for HTML5 storage. The page is meant to show how to both use
and attack HTML5 storage. The page supports Local and Session storage types. The
user can attack the storage in two contexts. They can act as if they want to
read to contents of their own browsers session storage to see if the developer
put authorization tokens or other items into the storage. They can also try to
use XSS to steal the session storage. In this use-case the user would be acting
as if they wanted to read someone elses storage. A large number of hints has
been added to the page. The page name is "html5-storage.php" and can be accessed
from the Cross Site Scripting menu and information leakage menu. In security
level zero, the page has no defenses. In level 1, the page will use trivial
JavaScript validation. In security level 5, the page will refuse to put the
secrets in client side storage.
11/13/2011: Jeremy Druin / Kenny Kurtz
Change Log for Mutillidae 2.1.6:
Enhanced the .htaccess file to automatically disable magic quotes on systems
which enable them by default (such as some OSX versions of PHP)
Fixed some bugs in the phpinfo.php file that made the page display weird.
Enhanced the hidden PHPINFO page so that it would work if the user browsed to
http://localhost/mutillidae/index.php?page=phpinfo.php or to http://localhost/mutillidae/phpinfo.php.
This example assumes Mutillidae is running on localhost.
Fixed a bug in index.php that kept the log-visit page from being included.
Fixed a bug in log-visit.php that kept the page from working.
Fixed installation instructions format for IE 8 not in compatibility mode.
11/10/2011: Jeremy Druin
Change Log for Mutillidae 2.1.5:
Added vuln to login sequence. Now a cookie is created with username. Students
should try to XSS the cookie and see what happens. Also try a response splitting
attack because a cookie is an HTTP header.
Created new twitter feed to make Mutillidae announcements and other web
vulnerability tweaks. @webpwnized
Fixed installation instructions format for IE 8 not in compatibility mode
10/14/2011: Jeremy Druin
Change Log for Mutillidae 2.1.4:
Moved usage instructions and php errors from the home page to their own pages.
In insecure mode, changed the method of the user-info.php page to GET in order
to make it easier to use sqlmap against Mutillidae. sqlmap supports POST but it
is easier to use with GET.
Added hints about sqlmap to sql injection tutorial and to the easter egg file
Added a credit card table as a target in the database
Confirmed that the view-blog table can be attacked with sqlmap. The answer is in
the Easter Egg file.
10/13/2011: Jeremy Druin
Change Log for Mutillidae 2.1.3:
Fix a bug. If the user was on the home page, without having clicked any link to
this point (such as when using a bookmark), then the user clicked the "change
security level", the page would redirect to page not found.
Increased the slide time for the ddsmoothmenu to make it slow down a little bit
Added a NEW vulnerability. Many sites have crazy pages that show server
settings, expose admin functionality, allow configuration, or other features a
user should not be able to see. The problem is not the pages themselves so much
as the fact that developers think no one will guess the name and browse to them.
Shoulder surfing, guessing, brute-forcing, etc can be used to find these pages.
Mutillidae now has such a page. It is in the "Server Misconfiguration" category.
See secret-administrative-pages.php for hints.
Augmented the installation instructions
Added link to ihackcharities to front page
Added a new security level. Now there is security level 1. The only difference
in this release between level 0 and level 1 is that level 1 has JS validation.
The JS validation has been in place for a while to allow but was activated in
level 0. Since level 0 is supposed to be very easy, the decision was made to
create level 1 and move JS validation to level 1. The JS validation is trivial
to bypass. Simply disable JS or use a proxy such as Tamper Data, Paros, Burp,
WebScarab, or others.
Page homenotes.php has been merged with home.php.
Page home.html has been renamed home.php
Added protection for SQL injection to add to your blog.php output of the current
users blog entries. Prior to this patch, you could SQL inject in security level
5 by putting your injection in the current users login name because the query
uses the current users login name as the input to the query.
Improved the DNS lookup page to add JS validation in security level 1 mode.
Changed padding for BACK button to use styles rather than HTML BR tags.
Changed the password generator password length to 15 to set a better example.
Some refactoring on user-info.php and login.php to clean up code
Added CSRF Protection to page add to your blog. This only works in secure mode.
Added more scripts to the easter egg file (Mutillidae Test Scripts)
Bug fix: The setupandreset.php errors were not printing out.
Stupid bug fix: Removed the "open DB" that was firing before the database was
actually created.
Created output on page setupandreset.php to show what happened
Added try/catch and more error handling to setupandreset.php
|
| 11/26/1011 |
Jamison Scheeres � "Social Engineering is a Fraud" Talk from Derbycon
Jamison gave me the go ahead to post his video from Derbycon. Now I just have to
get off my lazy butt and do the video for the updated/professional version of
NetworkMiner. |
| 11/06/2011 |
SkyDogCon 2011 Videos
Here are the videos from SkyDogCon.
Thanks to all of the SkyDogCon crew.SkyDog - Conference Opening Remarks
Curtis Koenig - The Neurobiology of Decision Making
Chris Anderson - Corporate Evil
Rious - Making of the SkyDogCon Electronic Badge
IronGeek - More PHUKED Than Ever
Nick Levay - Counter Espionage Strategy and Tactics
Karlo Arozquerta - Windows Command Line Forensics
Brian Wilson - DOCSIS Networks
Brent Baldwin/Robert Jason - Brewing Coffee the Soft Brew Way
Sonny Mounicou - Hackerspace Technology 101
Pat McCoy/Mike McGilvray - Hook, Line and Syncer: A Liar for
Hire's Ultimate Tackle Box
James Ruffer - Information gathering and social media attacks to
gain physical and electronic access to companies
Bart Hopper - Avoiding the Landmines in Your Own Backyard
HackerSpace Panel
Ben Feinstein - Morto Kombat: Understanding the Morto Worm |
| 11/04/2011 |
Updates To Homemade Hardware Keylogger/PHUKD Hybrid
Fixed some bugs, added
some features.Change logs:
PS/2 Hardware Keylogger/PHUKD:
0.01:
* Holding mod keys did not always work for multi select. Got it working (at
least I think I did).
* Nulls were getting into the logs, so I made an unhandled keycode exception.
USB Hardware Keylogger/PHUKD:
0.01:
* Holding mod keys did not always work for multi select. Got it working by
taking out the key replay code,
and made held keys function better in the process. Also, it made the code
simpler to read as I got rid
of a bunch of unneeded cruft code. :)
* Nulls were getting into the logs, so I made an unhandled keycode exception.
*Changed log brackets from <> to [].
0.02:
* Fixed bug in logging unknown keys.
* Added logging for keys [KEY_TAB] and [KEY_NON_US_NUM].
* Ctrl+Alt+S toggles the typing of raw bytes as they come in the serial
connection.
* Converted ints to bytes in many places. I think their was a type casting
problem causing weird issues.
* Fixed a buffer overflow issue caused by IncomingHIDReportIndex going over 18.
* Many other tiny changes.
|
| 11/02/2011 |
Homemade Hardware Keylogger/PHUKD Hybrid
I've been doing some work recently on making homemade keyloggers of both the USB
and PS/2 persuasion that will take keystrokes, record/replay them, and modify
programmable HID payloads accordingly. This hardware and software is not exactly
ready for prime time, but I figured I'd share it with you. On this page you will
find rough schematics, source code and links that may help you build your own. I
plan to put a video up that demos the devices right after
Skydogcon.
For related work see:
Hardware Key Logging Part 1: An Overview Of USB Hardware Keyloggers, And A
Review Of The KeyCarbon USB Home Mini (Text)
Hardware Key Logging Part 2: A Review Of Products From KeeLog and KeyGhost
(Text)
Hardware Key Logging Part 3: A Review Of The KeyLlama USB and PS/2 Keyloggers
(Text)
Irongeek - Hardware Keyloggers: Use, Review, and Stealth Presentation (Phreaknic
12) (Video)
Hardware Keyloggers In Action 1: The KeyLlama 2MB PS/2 Keylogger (Video)
Hardware Keyloggers In Action 2: The KeyLlama 2GB USB Keylogger (Video)
Bluetooth Wireless Hardware Keylogger Review (Video)
Programmable
HID USB Keystroke Dongle: Using the Teensy as a pen testing device (Defcon 18)
(Video)
Programmable HID USB Keystroke Dongle: Using the Teensy as a pen testing device
(Text)
Plug and Prey: Malicious USB Devices (Text)
Malicious USB Devices: Is that an attack vector in your pocket or are you just
happy to see me? (Video) |
| 10/24/2011 |
Hack3rcon II Videos Posted
Contents are as follows:
Opening Ceremony - Johnny Long - Keynote (via Skype)
Chris Silvers and Pat McCoy Hook Line and Syncer A Liar for Hires Ultimate Tackle Box
Boris Sverdlik Your Perimeter Sucks
Joshua Perry OSINT
Gus Fristschie Getting f***ed on the river
Eric Milam Automating MiTM for Winning
Keith Pachulski Common Project Issues with Technical Assessments
Tim Tomes and Mark Baggett Lurking in the Shadows
Martin Bos Your Password Policy Sucks
James Macgregor Watson Online Time OF cRIME
Charlie Vedaa
F*** the Penetration Testing Execution Standard
Stephan Looney Up and Running with Backtrack Workshop
Thomas Hoffecker Exploiting PKI for Fun & Profit or The Next Yellow Padlock Icon
@grecs How to Win Followers and Influence Friends Hacking Twitter to Boost Your Security Career
Jon Schipp Knowing What's Under Your Hood Implementing a Network Monitoring System
|
| 10/15/2011 |
Downloads
for Derbycon 2011 Posted
For those wanting to download copies of the videos from Derbycon 2011, I have
them all uploaded to Archive.org. You can find the link at the bottom of the
Derbycon
1 page. Archive.org's automated process should be generating smaller OGG and
MP4 versions.Also, since we had problems with the audio rig in Joff Thyer's
talk he sent me slides and demo videos for his
Covert Channels using IP Packet Headers presentation. Enjoy. |
| 10/08/2011 |
Derbycon
Videos
2011: The rest of them
In this wave are the last of the videos from
the Derbycon conference (tracks 2 and 3 of day 3 plus closing). Unfortunately,
there were a few losses.Day 3, Track 2
Jason n00bz � Advanced Penetration Techniques for the non-technical n00b
(Not Recorded)
Jayson E. Street � Steal Everything, Kill Everyone, Cause Total Financial Ruin! (Or How I Walked In And Misbehaved)
James Lee (egypt) � State of the Framework Address (Sound came out as just ground noise)
Ron Bowes � Advanced Nmap Scripting: Make Nmap work for you!"
(Sound came out as just ground noise)
Deviant Ollam � Distinguishing Lockpicks: Raking vs Lifting vs Jiggling and More
Raphael Mudge � Dirty Red Team tricks
Day 3, Track 3
Note: Some of these had weird ambient noise that I could not remove without
making all of the audio sound weird. I did the fix to JDuck's, but the rest I
left alone.
Chris Roberts � A Tribute to Dr. Strangelove
Kyle Osborne (kos) � The Hidden XSS � Attacking the Desktop
Mick Douglas � Blue team is sexy � refocusing on defense � Part II � All you baseline are belong to us
Garrett Gee � Typo-squatting Just Got A Lot More Dangerous
(Not Recorded)
Thomas d�Otreppe (mister_x) � OpenWIPS-ng
Joshua Drake (jduck) � Exploiting Java Memory Corruption Vulnerabilities
I have ideas for Derbycon 2 to make the recording a bit more reliable. See
you next year! |
| 10/07/2011 |
Derbycon
2011, Day 2 Track 3 and Day 3 Track 1 Talks Posted
In this wave are the videos from the 2nd day 3rd track and 3rd day 1st track of
the Derbycon conference. Please note that some videos were lost because of audio
issues or are awaiting approval. In this wave:
Day 2, Track 3:
Georgia Weidman � Throw It in the River? Towards Real Live Actual Smartphone Security
Rob Simon � Pentesting over Powerlines
Larry Pesce � You are the Smart Meter: Making (and hacking) of the 2011 MA-CCDC electronic badges
Bill Sempf � Is locksport
a sport?
Infojanitor � Virtual trust, Virtual Permission and the Illusion of Security
Ben Feinstein & Jeff Jarmoc � Get Off of My Cloud": Cloud Credential Compromise and Exposure
Jimmy Shah � Mobile App Moolah: Profit taking with Mobile Malware
McCorkle & Rios � 100 bugs in 100 days: An analysis of ICS (SCADA) software
Scott Ullrich + Chris Buechler � Open source firewalling with pfSense
(Sound came out as just fuzz)
Spiky Geek � How I learned to roll my own:Building custom pen testing platforms on the fly
(Sound came out as just fuzz)
Brent Huston � Realize Your Hacker Heritage: Do The Needful
Day 3, Track 1
Charlie Miller � Battery Firmware Hacking
Peter Van Eeckhoutte & Elliot Cutright � Win32 Exploit Development With Mona and the Metasploit Framework
Ryan Linn � collecting Underpants To Win Your Network
Jamison Scheeres � Social Engineering is a Fraud
(Awaiting approval)
Josh Kelley (winfang98) � Infectious Media � Bypassing AutoRun once and for
all
Kevin Johnson & Tom Eston � Desktop Betrayal: Exploiting Clients through the Features They Demand
Enjoy! |
| 10/06/2011 |
Derbycon
2011, Day 2, Track 2 Talks Posted
In this wave are the videos from the 2nd day of the conference that took place
in track two. In this wave:
Brian Baskin � Walking the Green Mile: How to Get Fired After a Security
Incident
Joe Schorr � �Rule 1: Cardio� (and 9 other rules to keep intruders out)
Thomas Hoffecker � Exploiting PKI for Fun & Profit or The Next Yellow
Padlock Icon?
Matthew Becker � 73o7\/\/@\/\/Ki � Survival Hacking your way out of
Armageddon
Bart Hopper � Avoiding the Landmines in your own Backyard
Chris Gates and Rob Fuller � The Dirty Little Secrets They Didn�t Teach You
In Pentesting Class
Boris Sverdlik � Your perimeter sucks
Evan Booth � Hide yo kids, hide yo wife: Residential security and
monitoring the bottom line
Rick Farina � Free Floating Hostility
Jack Daniel � Surviving a Teleporter Accident (It could happen to you)
Adrian Crenshaw � Building a Svartkast: Cheap hardware to leave behind on
someone else�s network
Had to do some work on the audio to raise the voices and lower the noise.
Choke up on the mic folks. :) Next year maybe we can get some lavalier
microphones. |
| 10/05/2011 |
Derbycon
2011, Day 2, Track 1 Talks Posted
In this wave are the videos from the 2nd day of the conference that took place
in track one. In this wave:
Dennis Kuntz � Mining Sensitive Information From Images Using Command-Line
OCR
Michael Arpaia � Beat to 1337: Creating A Successful University Cyber
Defense Organization
Carlos Perez (darkoperator) � Tactical Post Exploitation
Paul Asadoorian + John Strand: Offensive Countermeasures: Still trying to
bring sexy back
Tony Huffman (Myne-us) � When Fuzzers Miss: The no Hanging Fruit.
Rafal Los � You�re Going to Need a Bigger Shovel � A Critical Look at
Software Security Assurance
Rick Hayes + Karthik Rangarajan � OSINT Beyond the Basics
int0x80 (of Dual Core) � Anti-Forensics for the Louise
Rick Redman � Tomorrow you can patch that 0day � but your users will still
get you p0wn3d
Tottenkoph � Data Mining for (Neuro) hackers
Unfortunately, the audio buzz on Joff Thyer's "Covert Channels using IP
Packet Headers" talk is pretty catastrophic. I'll look at it again, but I don't
have high hopes. Also, I know some of the later videos have this audio issue as
well. |
| 10/04/2011 |
Derbycon
2011, Day 1 Talks Posted
Remember, these are coming out in waves. In this wave are all of the videos from
the first day of the conference. In this wave:
Adrian, Dave, Martin: Welcome to DerbyCon 2011 � Intro to the con and events
KEYNOTE ~ HD MOORE � Acoustic Intrusions
Johnny Long � Hackers for Charity Update
Kevin Mitnick + Dave Kennedy � Adaptive Penetration Testing
The Penetration Testing Execution Standard (PTES) Panel
Bruce Potter � The Details Don�t Matter
Chris Nickerson � Compliance: An Assault on Reason
Pat McCoy & Chris Silvers � Hook, Line and Syncer: The Liar for Hire�s
Ultimate Tacklebox
atlas � sploit me if you can
Jason Scott � Jason Scott�s Shareware Calvacade
Vlad Gostom & Joshua Marpet � Smile for the Grenade! Camera go Bang!
|
| 10/03/2011 |
Derbycon Thank Yous
Thanks for making Derbycon a huge successes guys. Be sure to hit up
@purehate_,
@dave_rel1k or myself (@irongeek_adc)
for suggestions on making next year even better. Next up for me are
Hack3rcon and
Skydogcon. Also, the videos from
Derbycon will be coming out in waves soon.
DigiP is working on the
splash and title card art, and after I have that I can start rendering out the
split screen versions. Thanks again. |
| 09/26/2011 |
Derbycon
Area Map
Putting this up to help attendees, speakers and sponsors find food, supplies,
booze, ATMs, shipping and sites near the
Derbycon hotel. |
| 09/25/2011 |
Programmable HID USB Keyboard/Mouse Dongle Library Updated
I put up the version 0.3 of the Programmable HID USB Keyboard/Mouse Dongle
Library. It should now work with newer versions of the Arduino and the
Teensyduino environments. |
| 09/18/2011 |
Defcon 19: Cipherspaces/Darknets An Overview Of Attack Strategies
This is the talk I gave at Defcon 19, this time as recorded in front of a live
studio audience (as oppose to the canned version I posted before). The canned
one may be more polished, but the Defcon 19 one looks cooler. Here is the
description:Darknets/Cipherspaces such as Tor and I2P have been covered
before in great detail. Sometimes it can be hard to follow attack strategies
that have been used against them as the papers written on the topic have been
academic and abstract. What this talk will attempt to do is step back and give
an overview of the topic in a manner hopefully more conducive to the
understanding of security practitioners, giving more concrete examples. While
little to nothing in this talk will be "new and groundbreaking" it should lead
to a better understanding of how encrypted anonymizing networks can be subverted
to reveal identities. |
| 09/16/2011 |
Pilfering Local Data: Things an Attacker Would Want to Grab with Short Term
Local Access
Here's my talk from the 2011 Nashville Infosec. This is more or less the
description I sent them: "This talk will cover core items an attacker would want
to locate and copy off of a Windows system, as well as what tools they would use
to bypass weak security precautions like file system permissions and OS/BIOs
passwords. Core date in this case would be things like stored passwords and
wireless keys, but could also include network paths and the like. It will
underscore the importance of physical security and hard drive encryption." |
| 09/13/2011 |
MAN
Pages From BackTrack 5 R1 List
I converted a bunch of the MAN pages from BackTrack 5 R1 into HTML. I did
this for BackTrack 3 back in the day, so I figured I'd do an update for the
tools in BackTrack 5 R1. I made this in a somewhat automated fashion, so please
excuse the errors and dead links. It may still be helpful for those that just
Google for the MAN pages.
List Includes:
acct_users,
affcat,
airbase-ng,
aircrack-ng,
airdecap-ng,
airdecloak-ng,
airdriver-ng,
aireplay-ng,
airgraph-ng,
airmon-ng,
airodump-ng,
airolib-ng,
airoscript-ng,
airserv-ng,
airtun-ng,
amap,
arping,
arpspoof,
bombardment,
buddy-ng,
bulk_extractor,
capinfos,
clientsconf,
crunch,
dc3dd,
dff,
dftest,
dictionary,
dmitry,
dnsspoof,
dnstracer,
dsniff,
dumpcap,
dupemap,
easside-ng,
editcap,
fatback,
fcrackzip,
fiked,
filesnarf,
fping,
fragroute,
fragrouter,
fragtest
genlistp,
giskismetp,
gpshell,
greenbone-nvt-sync,
gsad,
gsd,
gsmtprc,
hashdeep,
hexedit,
honeyd,
honeydctl,
hydra,
idl2wrs,
ike-scan,
ivstools,
kismet,
kismetconf,
kismet_drone,
kismet_droneconf,
kstats,
layingsiege,
lspst,
macchanger,
macof,
magicrescue,
magicsort,
mailsnarf,
makeivs-ng,
md5deep,
medusa,
mergecap,
miredo-checkconf,
miredo-server,
miredo-serverconf,
miredo,
miredoconf,
missidentify,
msgsnarf,
ncat,
ncrack,
ndiff,
netdiscover,
netmask,
nmap,
nping
omp,
openvas-adduser,
openvas-mkcert,
openvas-nasl,
openvas-nvt-sync,
openvas-rmuser,
openvasad,
openvasmd,
openvassd,
outlookpst,
outputpbnjp,
packetforge-ng,
psk-crack,
pst2dii,
pst2ldif,
pw-inspector,
radclient,
raddebug,
radeapclient,
radiusd,
radiusdconf,
radlast,
radmin,
radrelay,
radrelayconf,
radsqlrelay,
radtest,
radwatch,
radwho,
radzap,
randpkt,
rawshark,
readpst,
recoverjpeg,
recovermov,
rlm_acct_unique,
rlm_always,
rlm_attr_filter,
rlm_attr_rewrite,
rlm_chap,
rlm_counter,
rlm_detail,
rlm_digest,
rlm_expr,
rlm_files,
rlm_mschap,
rlm_pap,
rlm_passwd,
rlm_policy,
rlm_realm,
rlm_sql,
rlm_sql_log,
rlm_unix
safecopy,
scalpel,
scanpbnjp,
scapy,
scrounge-ntfs,
sha1deep,
sha256deep,
siege,
siege2csv,
siegeconfig,
sipsak,
smtprc,
smtpscan,
sort-pictures,
sshmitm,
sshow,
ssidsniff,
ssldump,
sslh,
tcpdump,
tcpkill,
tcpnice,
tcptraceroute,
teredo-mire,
text2pcap,
thc-ipv6,
tigerdeep,
tkiptun-ng,
traceroute,
tshark,
unicornscan,
unlang,
urlsnarf,
urls_txt,
users,
webmitm,
webspy,
wesside-ng,
whirlpooldeep,
wireshark-filter,
wireshark,
xhydra,
xprobe2,
yersinia,
zenmap |
| 09/12/2011 |
Building a Svartkast with a pretty pink Pogoplug: Cheap hardware to leave on
someone else's network
The first obvious question is what the hell is a Svartkast? Well, it�s a term I
picked up from Telecomix. Before I would have just referred to it as a �drop
box� (too much name collision there now), but some also call it a kamikaze box
or a Blackthrow (which is English for the Swedish term Svartkast). The core idea
is to have a cheap host you can leave on someone else�s network that you can
remote into but that can�t easily be tied back to you. The Svartkast does this
one better by using a cipher-space like Tor or I2P to further obfuscate where
communications to the box are coming from (though slowing down communications of
course, anonymity isn�t �free�). |
| 09/05/2011 |
Mutillidae 2.1.0 release
Jeremy Druin has been at it again, with more upgrades to the webapp security
teaching tool Mutillidae. In his words:
Well. Its finally here for better or worse. This version of Mutillidae has
nearly every vulnerability known. And they come in bulk. There is all of the OWASP Top 10 plus another ten categories at least. The documentation has been
upgraded extensively including the hints and installation instructions. The menu
system has been redesigned again to make it easier for users to find the exploit
they want to try. Current vulns that are not OWASP top 10 have been added
including click-jacking, parameter pollution, cross site framing, and arbitrary
file inclusion. I ripped out the MYSQL interface and replaced it with the new
object oriented version that comes with PHP 5.3.0 called MYSQLi. The "i" is
supposidly for improved. I also enhanced the presentation and output on many
pages. Hopefully it is enterprise grade now. My goal is for pros to use this in
training developers.
I added test scripts in the documentation folder. You might like some of them.
Some are more fun than monkeys with bubble-gum. |
| 09/03/2011 |
Curriculum Vitae added to my
about page
I've had some academics ask for it, so I decided to add my
Curriculum Vitae to the about
page. It's mostly teaching an presentation experience. I'll need to update
it again soon since I have a lot of conferences I'm speaking/working at this
fall (copied from ISDPodcast):
Nashville Infosec
When: Sept 15, 2011
Where: Nashville, TN
http://www.technologycouncil.com/connect/infosec-2011/
Louisville Infosec
When: September 29th
Where: Louisville, KY
http://louisvilleinfosec.com/
DerbyCon
When: September 30th � October 2, 2011
Where: Louisville, KY
http://www.derbycon.com/
Hack3rCon 2011
When: October 21-23rd, 2011
Where: the Charleston House Hotel and Conference Center
http://www.hack3rcon.org/
SkyDogCon
When: Nov 4th � Nov 6th
Where: Holiday Inn Airport, Nashville, TN
http://www.skydogcon.com
Phreaknic
When: Nov 4th � Nov 6th
Where: Days Inn Stadium, Nashville, TN
http://www.phreaknic.info
Subjects to be announced later. |
| 08/23/2011 |
Louisville Infosec Discount Code
If you registered for DerbyCon and want to go to the LouisvilleInfosec the day
before email chair (at) LouisvilleInfoSec.com for a $50 off discount code. |
| 08/20/2011 |
Security Tips For The Small Business From 70,000 Feet - Joseph Hollingsworth and
Adrian Crenshaw
A little while back Joe Hollingsworth and I were interviewed for an article in
the
Southern Indiana Business Source. The local Kiwanis club asked for a 25 min
talk on the subject of the article, so we came up with this mandate:
Given only 25 minutes, tell us what a small business could do to help their
security posture.
Well, it ended up being almost 40min and we did not get through all of the
slides. The live video camera failed, so the audio in this video is what the
laptop recorded. It may not be something most of my readers will be interested
in, but it may help you present on a similar topic. |
| 08/09/2011 |
Cipherspaces/Darknets An Overview Of Attack Strategies
This is essentially the talk I gave at Defcon 19, but I had a little more time
to cover the topic in this canned video:Darknets/Cipherspaces such as Tor and
I2P have been covered before in great detail. Sometimes it can be hard to follow
attack strategies that have been used against them as the papers written on the
topic have been academic and abstract. What this talk will attempt to do is step
back and give an overview of the topic in a manner hopefully more conducive to
the understanding of security practitioners, giving more concrete examples.
While little to nothing in this talk will be "new and groundbreaking" it should
lead to a better understanding of how encrypted anonymizing networks can be
subverted to reveal identities. |
| 08/08/2011 |
I2P/Tor Workshop Notes Updated
After running the I2P and Tor workshop
at Defcon 19, I've decided to make some tweaks before
Hack3rcon. I've fixed some typos, and now
have an index:Places to go, data to see
I2P eepSites
I2P Services/Apps
Tor Hidden Service Websites
Tor Hidden Service IRC
I2P Install
Install I2P In Windows
Install I2P in Linux (Standard
Method)
Install I2P in Linux using APT Method
Proxy Settings for I2P
Tor Install
Install Tor in Windows
Install Tor in Linux
Proxy Settings for Tor
I2P Tweaks
I2P, connection and Firewall
settings
Name Service subscripts to add
To Make I2P accessible to your
network
Run I2P as a service
Tor Tweaks
Tor IRC
Specify an Exit Node in Tor
Make Tor accessible to your
network
Run Tor as service in Windows
To
make Vidalia work again in Window after making Tor a service
Run Tor as service in Linux (Ubuntu)
To
make Vidalia work again in Linux after making Tor a service
Torify vs Torsock (hint:use
Torsocks) in Linux
Tor Hidden Services
Just a simple Tor Hidden Service
Backing up Tor Hidden Server Key
Working with I2PTunnels
Using the built in
web server (Jetty) I2P Tunnel
Make SSH Server and SOCKS Tunnel
Naming and announcing your eepSite
Encrypted Lease Set
Extra
Other Notes
I also plan to make videos for each of these short text guides. |
| 08/02/2011 |
I2P/Tor Workshop Notes
These are the rough notes and recipes I'll be using in my I2P and Tor workshop
at Defcon 19. It gives truncated steps to do things like host a hidden service,
make an encrypted lease set, back up your eepSite and hidden service keys, etc,
etc. Hope it helps. |
| 07/27/2011 |
Mini-DisplayPort on New Dells: Resolving issues with output to projectors in
Windows 7
Ok, this is not security related, but I know a lot of people who do
presentations and may run into these issues when they try to use an Apple Min-DisplayPort
adapter with their new Windows 7 laptop. Hope it helps. |
| 07/21/2011 |
Hack3rcon II Call For Papers
We all had a great time last year, so we are doing it again. Dave Kennedy
(Re1ik) and myself are set to speak. The CFP is open, so submit away:
http://hack3rcon.org/call.html
You can also check out
videos from
last year's Hack3rcon. |
| 07/19/2011 |
Ohio Information Security Forum (OISF) Anniversary Event Videos
These are the presentations from the Ohio Information Security (OISF)
Anniversary Event. The descriptions are largely Ligatted from the
OISF website.
Endpoint Security Decisions - Kurt Roemer
Defending against XSS - Jason Montgomery
Project Ubertooth: Building a Better Bluetooth Adapter - Michael Ossmann
Making Windows 7 SP1 32/64bit Boot CD/DVD/USBs with Winbuilder - Adrian Crenshaw
Cloud Computing Security - Dr. James Walden |
| 07/18/2011 |
AIDE 2011 Conference Videos
These are the presentations from the AIDE
2011 conference at Marshall University. We had some issues early on with the
schedule not matching the talks, so descriptions are incomplete. The
descriptions I do have are largely Ligatted from the
AIDE website.
Social Networks - Evan Patterson
Who are you going to call? - Evan Patterson
WV Crimes requiring
Electronic & Digital Evidence - Philip Morrison
Professionalism on the Witness
Stand - Phillip Morrison
Common Darknet Weaknesses - Adrian "Irongeek"
Crenshaw
Recent HIPAA/HITECH Changes - Caleb
Knight
Hacking A Mature Security Program -
David "ReL1K" Kennedy |
| 07/08/2011 |
Dual booting Winbuilder/Win7PE SE and Backtrack 5 on a USB flash drive with
XBOOT
This is a quick and dirty video to show how to make a multiboot thumbdrive with
XBOOT. You can also create a multiboot CD/DVD by combining other ISOs. Operating
Systems loaded on mine include: Backtrack 5, Winbuilder/Win7PE SE, DBAN,
UBCD4Win, TAILS, Gparted, Ubuntu 11.04, etc.
|
| 07/02/2011 |
Upcoming Irongeek Speaking Engagements
I figured I'd take a little time to announce a few places I'll be speaking at
shortly. This is not a complete list, there are a few more I've not confirmed
yet.AIDE:
July 15th, 2011
Cipherspaces/Darknets: An Overview Of Attack Strategies
Ohio Information Security
Forum: July 16th, 2011
Making Windows 7 SP1 32/64bit Boot CD/DVD/USBs with Winbuilder
Defcon/B-Sides: Aug 2-7th, 2011
Only speaking at Defcon, but I plan to hang around B-Sides while I�m in Vegas
that week.
Talk: Cipherspaces/Darknets: An Overview Of Attack Strategies
Workshop (in 2 parts): "Getting up and running with I2P and Tor" & "Hosting sites as I2P eepSites and Tor hidden services"
Louisville Infosec: Sept 29th,
2011
As some of you know, the Louisville Infosec is happening the day before Derbycon,
so if you are already in town you might as well come out. I'm running the
Network King Of The Hill (NetKotH)
game there, and to get more players they gave me a special reg code to get the
first 15 people in for free who promise to compete in the game. The code is:
koth2011
Last year the first prize was an iPod touch, not sure what it will be this year.
Derbycon: Sept 30th-Oct 2nd
I'm one of the organizers for the event. Most likely I'll not be speaking (we
had so many submissions for talks, and we wanted to fit in as many as possible),
but I will be doing a workshop along with the other founders
Dave Kennedy and
Martin Bos.
|
| 07/01/2011 |
Building a boot USB, DVD or CD based on Windows 7 with WinBuilder and Win7PE SE
Tutorial
As many of you know, I�m a big fan of Bart's PeBuilder and derivative works
based on it like UBDC4Win. Having a bootable USB drive or CD I can run Windows
tools from just comes in hand so often for task like malware/spyware removal,
system recovery and harvesting locked files for �pro bono pen-test purposes�.
Unfortunately, the Bart�s PE project has not been updated in awhile, and Windows
XP is getting kind of long in the tooth, so I went looking for a replacement.
For those wanting to build something a little newer, check out WinBuilder.
|
| 06/21/2011 |
Mutillidae 2.0.8: More vulnerable web app fun
Jeremy Druin has been at it again. :) New changes for Mutillidae 2.0.8 include:
- Added more comments to the code to explain how defenses work
- Added support for the <u></u> tag to the blog. In secure mode Mutillidae
will allow this tag but still safely encode output and stop XSS.
- Added JavaScript filtering to prevent single quotes from being entered
in blog entries. This give practice bypassing JavaScript "security" and
helps the user understand JavaScript cannot provide security.
- Added lots of JS filtering to login.php. Nearly all characters are
filtered. Users are encouraged to understand that JavaScript and filtering
are useless for security.
- Added autofocus to login.php and add-to-blog.php
- Added more "allowed dangerous HTML tags" to the blog. Until now only the
bold HTML tag was supported. Also the output was not HTML5 compliant. For
example, if the user entered a bold tag, then a bold tag was output however
the bold tag is depreciated. Styles must be used. So Mutillidae allows the
user to input a bold tag but will correctly encode this as a sytle upon
output. The italic tag is now supported as a dangerous input which is safely
output without fear of Cross Site Scripting. These defenses only operate in
secure mode of course. In insecure mode, the site allows any input and
simply outputs whatever is input without any encoding.
- Changed menu for OWASP A1 - Injection to differentiate between SQL,
HTML, and Command Injection. This should make it more clear which pages
exhibit vulnerabilities with the specific injecton sub-types. Also added new
link for Blind SQL Injection.
- Changed menu for OWASP A2 - Cross Site Scripting to differentiate
between XSS coming in via user supplied fields (GET/POST) and values within
HTTP Request Headers.
- Added tutorials feature.
- Added SQL Injection Totorial
- Added Cross Site Scripting tutorial
- Added Command Injection tutorial
- Added new feature. Hints can now be at different levels. Each time the
user clicks Hints, the level increases by 1 until rolling over.
- Removed the installation instructions from the home page. A new page for
instructions is created and linked from the menu.
- Augmented the installation instructions to include running from Samurai,
creating a custom ISO, installing to XAMPP, and running in virutal machines.
- Reformatted install instructions and main home page to be compliant with
HTML 5.
|
| 06/10/2011 |
Altruism: EFF Fund Raiser / Self-interest: Help the ISDPodcast Team win!
Largely quoted from the ISD Podcast
site:
The ISD Podcast has entered entered into a contest to see who can raise the most
money for the Electronic Frontier Foundation. For those who don�t know, the EFF
is a non-profit group of lawyers, policy analysts, activists, and technologists
who fight for digital rights and have helped countless hackers and security
researchers get out of hot water as well as exposing injustices caused by
ignorant legislation and bad judgments. Please click the following link to
donate to a vitally important cause:
http://action.eff.org/site/TR/Contest/Advocacy?team_id=1730&pg=team&fr_id=1060
Please help if you can.
Obligatory Robert A. Heinlein/Lazarus Long quote:
'If tempted by something that feels "altruistic," examine your motives and
root out that self-deception. Then, if you still want to do it, wallow in it!' |
| 06/04/2011 |
Portable Boot Devices (USB/CD/DVD): Or in Canadian, what is this all aboot?
This is a talk I did on making bootable USB drives/CDs/DVDs for my local ISSA.
Think of it as a braindump and starting point for making your own. |
| 05/31/2011 |
Konboot
from a USB flash drive files and instructions updated
People kept complaining because my old config did not work with newer versions
of Unetbootin. Changed the syslinux.cfg file since Unetbootin now uses menu.c32
instead of vesamenu.c32. Also put in a newer chain.c32 and updated the
instructions. Works fine with Win 7 SP1 32bit. |
| 05/23/2011 |
OSInt, Cyberstalking, Footprinting and Recon: Getting to know you
The following are videos from the Footprinting/OSInt/Recon/Cyberstalking
class I did up in Fort Wayne Indiana for the
Northeast Indiana Chapter of ISSA.
I've split the class into three videos by subtopic, and included the text from
the presentation for quick linking.
DNS, Whois and Domain Tools
Finding general Information about an organization via the web
Anti-social networks
Google Hacking
Metadata
Other odds and ends
|
| 05/22/2011 |
Mutillidae 2.0.7: More vulnerable web app fun
Jeremy Druin has been at it again. :) New changes for Mutillidae 2.0.7 include:
- Added a new page rene-magritte.php to explore click-jacking. In
secure mode, Mutillidae will send the X-FRAME-OPTIONS: DENY header. In
modern browsers, this will cause the browser to throw an error rather
than allow the page rene-magritte.php to be framed.
- Added a resources link to the main menu. Links are to information or
tools that can help with testing Mutillidae.
- Added new class LogHandler to take over logging. Previously logging
statements has to be copied to each spot that logging was needed. With
the new class, logging requires only one line of code and the logger
automatically logs based on the current security level. If in insecure
mode, no attempt to stop XSS or SQLi is made. With the new class, many
less lines of code are needed and many more places log. With more places
logging, there is a much better chance of finding a log exploit and
taking advantage (insecure mode). Logging added to pages:
add-to-your-blog, dns-lookup, text-file-viewer, source-viewer.php,
register.php, redirectandlog.php, and user-info.php
- Added more default users to initial setup to give more targets.
|
| 05/16/2011 |
"Cyberstalking, Footprinting and Recon: Getting to
know you" class in Fort Wayne, Saturday May 21, 2011 from 8:30 AM until 5 PM
From the Northeast Indiana Chapter of ISSA: The workshop, entitled "Cyberstalking,
Footprinting and Recon: Getting to know you" will be held on Saturday May 21,
2011 from 8:30 AM until 5 PM. Computers will be provided by Orthopedics NE and
will be held at their location of 5050 N. Clinton St., Fort Wayne, IN 46825 (
http://tinyurl.com/43tqu7n ). Lunch
will be provided by Splunk; designed to
collect, index and harness the fast moving machine data generated by all your
applications, servers and devices - physical, virtual and in the cloud. Search
and analyze all your real-time and historical data from one place. A donation of
$10 will be appreciated and passed on to the chapter charity; Toys for Tots. Do not bring cash. Make
checks out to "TOYS FOR TOTS". We will also have membership information for
anyone interested. This is an OPEN event to anyone in the community but we have
a limited number of seats so please email an RSVP to me and I will send you a
seat confirmation. Computers will be provided by ONE but feel free to bring your
trusty laptop. Adrian will be working with Backtrack and we will have it loaded
as a VM on your machine when you show up. |
| 05/15/2011 |
Videos
from Central Ohio InfoSec Summit While I was at the Central Ohio InfoSec
Summit I recorded Dave's and Tom's talks, as well as my own. Hope you enjoy
them.
Attacking and Defending Apple iOS Devices - Tom Eston
http://www.spylogic.net
Leveraging Social-Engineering in your INFOSEC Program - David Kennedy
http://www.secmaniac.com
Crude, Inconsistent Threat: Understanding Anonymous - Adrian Crenshaw |
| 05/11/2011 |
Mutillidae 2.0.6.1: Learn to hack vulnerable web apps
Jeremy Druin has been busy doing lots of updates to the Mutillidae training
package. Enjoy testing your web app pen-testing skills and tools against it. |
| 05/06/2011 |
Update to Economics of Information Security Paper Reviews and Notes
Awhile back I posted my write-ups and notes for the papers I've been reading in the
"Economics of Information Security" class I'm enrolled in. I've now
posted weeks 9 to 15. I'm guessing most of
my readers won't get much out of them unless they have read, or plan to read,
the same papers. Hell, they may not get much out of them even then, but I'm
posting them. :)Also, I'll be speaking here next week in Columbus Ohio:
http://infosecsummit.org/
Looks like the event is sold out, but maybe I can convince them to let me
record some talks. Dave Kennedy will
also be there, and hopefully I'll have some
Derbycon stickers for anyone that wants them. |
| 04/28/2011 |
Links for Doxing, Personal OSInt, Profiling, Footprinting, Cyberstalking
A general collection of resources that can help you profile someone before a
pentest. If you have more high quality, low noise resources, please contact me.
I'd eventually like to add some of the links to the
Pentest Standard. |
| 04/27/2011 |
Derbycon Tickets On Sale This Friday (April 29th) at 12:01AM EST
Title says it all. Here are some of our speakers: Scott Angelo, James Arlen (myrcurial),
Paul Asadoorian (pauldotcom), Martin Bos (PureHate), Chris Buechler, Int0x80 �
Dual Core, Adrian Crenshaw (IronGeek), Elliott Cutright (Nullthreat), Thomas
d�Otreppe (Mister_X), Peter Van Eeckhoutte (corelanc0d3r), Tom Eston (agent0x0),
Rick Farina (Zero_Chaos), Rob Fuller (mubix), Chris Gates (Carnal0wnage), Chris
Hadnagy (loganWHD), Rick Hayes, Kevin Johnson (secureideas), Dave Kennedy
(ReL1K), James Lee (egypt), Johnny Long, Rafal Los (WhiteRabbit), Kevin Mitnick,
H.D Moore (hdm), Chris Nickerson, Jim O�Gorman (elwood), Deviant Ollam (TOOOL),
Carlos Perez (darkoperator), Larry Pesce (haxorthematrix), Bruce Potter (gdead),
Jason Scott, Ed Skoudis, Eric Smith (infosecmafia), John Strand, Jayson E.
Street and Scott Ullrich. |
| 04/18/2011 |
Funnypots and Skiddy Baiting: Screwing with those that screw with you - Notacon
2011
This is the presentation I did for Notacon 2011. Honeypots might be ok for
research, but they don�t allow you to have fun at an attacker�s expense the same
way funnypot and skiddy baiting does. In this talk I�ll be covering techniques
you can use to scar the psyche or to have fun at the expense of attackers or
people invading your privacy. Sorry about the subpar sound, I had a bit of echo
from where my camera was positioned. |
| 04/13/2011 |
Pauldotcom Podcast,
Thursday April 14th, Derbycon and USB naughtiness
On April 14th at 19:15 EDT (23:15 UTC) I and the other founders of
Derbycon will be on the
Pauldotcom podcast to talk about the
conference. After that I'll be doing a tech segment about
malicious USB devices. Hope you can tune in for the live stream. |
| 04/08/2011 |
Identifying the true IP/Network identity of I2P service hosts talk - Adrian
Crenshaw, Blackhat DC 2011
This is the talk I did at Blackhat DC 2011 about de-anonymizing I2P darknet
services. |
| 04/02/2011 |
Computer Forensics & Electronic Discovery - Andy Cobb, PhD
Recorded at the April 2011 Louisville ISSA meeting. |
| 03/28/2011 |
Crude, Inconsistent Threat: Understanding Anonymous
Just a little something to help explain Anonymous to the media and other
organizations. I'm working on a presentation for the
Central Ohio Infosec Summit. |
| 03/24/2011 |
Mutillidae 2.0.1 Beta: A few little fixes
Jeremy Druin and I have got a slightly newer version for you:
- Replaced root relative links with local relative links to allow more
freedom in root folder name
- Added email address for Jeremy
- Added change log to site
- Added Toggle Hints into core menu but link disappears in secure mode
- Added new failure to restrict URL access vuln
|
| 03/23/2011 |
Mutillidae 2.0 Beta Posted
Jeremy Druin, a professional developer (unlike me), added sooooooo many new
features to the project. If you want to play around with web hacking techniques
check out this deliberately vulnerable webapp. Jeremy has added a prettier
interface, "completely hosed" and "more secure" modes, added the OWASP ESAPI API
and tons of other features you can read about in the change log. |
| 03/21/2011 |
Outerz0ne 2011 Hacker Con
The following are videos of the presentations from the
Outerzone 2011 hacker conference. Thanks to Skydog, Robin, Scott,
SomeNinjaMaster and the Hacker Consortium
crew for the con. Also thanks to Seeblind and others
for doing AV. I'm looking forward to
Skydogcon and working with the guys again at
Derbycon.
List:
SkyDog - Opening
Ceremonies/etc.
SkyDog - The Modern Day Hacker
IronGeek -
Rendering Hacker Con Videos with AviSynth
MadMex -
Windows Command Line Incident Response
HalfJack -Building your
Own Green Home
Beau Woods - What Companies and Vendors must know about securing mobile
devices, mobile applications, access and data.
Rick Hayes -
Assessing and Pen-Testing IPv6 Networks
Pure Hate - Why your
password policy sucks
Billy Hoffman -
Advice on starting a start-up
Contest Prize
Giveaway, Awards, Closing Ceremonies
|
| 03/14/2011 |
Network Sniffers Class for the Kentuckiana ISSA 2011
We decided to put on another sniffers class. This time Gary Hampton joins me to
impart his knowledge of using Wireshark to diagnose problems on wireless
networks. I cover the usual suspects: TCPDump, Metasploit sniffing with
Meterpreter, ARP Poisoning, Ettercap, Cain, NetworkMinor, Firesheep and Xplico. |
| 03/03/2011 |
Infosec Daily Podcast
Mailing List
Hi all, as some of you know, I'm on the ISD
Podcast every Thursday night. We also have a
mailing list you can
sign up for now. For those that wish to ask me pentest questions, you may be
better off asking there as they have more experienced pentesters. You can check out the
ISD live stream
every weekday at 8PM EST if you don't want to wait for the MP3s. Connect to the
#isdpodcast IRC channel on
freenode to comment while we record.
For other security podcasts I recommend, check out my
security podcast feed
aggregator. |
| 03/02/2011 |
Economics of Information Security Paper Reviews and Notes
These are my write-ups and notes for the papers I've been reading in the
"Economics of Information Security" class I'm enrolled in. I'm guessing most of
my readers won't get much out of them unless they have read, or plan to read,
the same papers.Also, don't forget Outerz0ne (March 18-19, 2011 Atlanta, GA) is coming up! |
| 02/22/2011 |
Talks from
the AIDE Winter Meeting 2011 Bill Gardner (@oncee) invited me out to
Marshall University to speak and record videos at the AIDE Winter Meeting 2011.
Below are the results.
List:
Opening
Remarks & Security Enabler, Bill Gardner & Rob Dixon
Where
we at? A look at Information Security, David Kennedy (ReL1K)
Radio
Reconnaissance in Penetration Testing, Matt Neely
Social
Engineering In-Depth, Chris Criswell & Wayne Porter
Penetration
Testing - The Continuing Failures of an Industry, Keith Pachulski
Blue
team is sexy - refocusing on defense, Mick Douglas
DDoS:
Defending Against an Internet Mob, Kenneth Scott
Cipherspace/Darknets:
anonymizing private networks, Adrian Crenshaw
Hackers
Trail Mix, Elliott Cutright |
| 02/20/2011 |
Sniffers Class, March 12
2011
Hello all, the Kentuckiana ISSA
is sponsoring a class
Gary Hampton and I will be putting on concerning network sniffers. We plan to
cover Wireshark, as well as TCPdump, Cain, Ettercap, NetworkMiner and some
others. The details are as follows:
When:
Saturday March 12, 2011 from 10:00 AM to 4:00 PM EST
Where:
Sullivan College of Technology & Design
3901 Atkinson Square Drive
Energy Technology Building auditorium Room ETB 6/7
Louisville, KY 40218
You need to register
via this link. All you need to bring is your laptop, but be careful what you
send across the class's network. :) |
| 02/20/2011 |
Unlock Indy Open Registration, March 19, 2011 4pm-8pm
IndySec is putting on a charity event:
"Unlock Indy is the 2011 IndySec charity event. In exchange for a $30 or more
donation to the Hoosier Veterans' Assistance Foundation of Indiana (www.hvaf.org),
participants will receive a seat in a class on defeating locks and security
devices (lockpicking). Participants will get hands on practice in lock picking
and bumping many common and not so common locks. A sponsor will be providing
pizza and soda."
Register
Flyer |
| 02/08/2011 |
WiGLE WiFi Database to Google Earth Client for Wardrive Mapping Tool Updated
Uploaded version 0.95 after Dippo pointed out the older version stopped working.
Wigle.net changed the way I had to parse their data, so I had to fix IGiGLE so
it worked again. Enjoy mapping your wardrives. |
| 02/01/2011 |
FireTalks from Shmoocon 2011
Grecs and the folks at Shmoo were kind enough to let me record the FireTalks
from Shmoocon 2011.
Next up, see you at
AIDE (Febuary
17-18, 2011 Huntington, WV) and
Outerz0ne (March 18-19, 2011 Atlanta, GA)! |
| 01/27/2011 |
Plug and Prey: Malicious USB Devices
A little paper I wrote for my masters in
security informatics, and will present at
Shmoocon 2011.Sections:
1. Introduction
2. Background
2.1 USB mass storage containing malware
2.2 U3 thumb drives with "evil" autorun payloads
2.3 Why this paper will focus on the last two categories
2.4 Hardware key loggers
2.5 Programmable HID USB Keyboard Dongle Devices
3. Locking down Windows and Linux against Malicious USB devices
3.1 Locking down Windows Vista and Windows 7 against Malicious USB devices
3.2 Locking down Linux using UDEV
4. Tracking and scanning for malicious USB devices in Windows environments
5. Possible extensions to the USB standards
6. Conclusions
|
| 01/26/2011 |
Irongeek's streaming page
for the FireTalks at Shmoocon
I don't intend to stream often but for some special events, like the
FireTalks at Shmoocon, I plan to have this feed up and running. It's
obviously not up right at the moment but come check it out this weekend,
1/28/2011, 8:00 PM & 1/29/2011, 8:00 PM EST. Just bookmark it for later. |
| 01/23/2011 |
Barcode Laser Emitter: Evil checks-out at a distance
If you read my article "Barcode
Fuzzer, Bruteforcer, SQL/XSS Injector using a flashing LED", or watched
my video on the same subject, you know I've been playing around with
barcodes. Now I have two new units to show off. The core code and device (Teensy
2.0) is the same in these units as the previous one, so please read the first
article for the relevant details if you want to make one. This will be an entry
in the Shmoocon 2011 Barcode
Shmarcode contest. |
| 01/17/2011 |
Hosting Hidden Services in I2P: eepSites and SSH
Here is another foray into Cipherspace. In this video I'll show how to get your
eepSite up and running, along with pointing an HTTP tunnel to another web server
besides the build in Jetty, and also how to host SSH inside of the I2P network.
Before you watch this video, you may want to check out my videos on
Installing I2P under Windows
Installing I2P under Linux
and you will want to read the article on
application level de-anonymizing techniques that can be used against I2P hosted
services for some background information.
I apologize for it being somewhat meandering, I was doing the video largely
off the cuff. Also be aware that "Hidden Services" is more of Tor's terminology
for much the same concept, in I2P you set up "I2P Server Tunnels". I'll be
talking about de-anonymizing I2P services in my
Black Hat
DC 2011 talk shortly. |
| 01/13/2011 |
HTC Evo Shift 4g (or any Android Phone) on Sprint SERO plans
For those on SERO plans from Sprint, figured I'd relate this story. May help you
figure out what you need to do if you want a new phone and are on an old plan.
The phone itself I like, support is more of the issue. Seems that no mater what
they tell you in chat, don't trust it. I was told I could keep my old plan,
twice, but that was not the case. See link for the chat/email logs. |
| 01/12/2011 |
Windows 7: Copy A Modified User Profile Over The Default Profile page updated
Thanks to Troy and Mikey for showing me a better way. |
| 01/10/2011 |
DerbyCon website is live!
DerbyCon isn't just another security conference. We've taken the best elements
from all of the conferences we've ever been to and put them into one. DerbyCon
is a place you can call home, where you can meet each other, party, and learn.
It's located in the heart of Louisville, Kentucky right on 4th Street Live at
the Hyatt Regency.
Our goal is create a fun environment where the security community can come
together to share ideas and concepts. Conferences like this are where
friendships as well as some of the best ideas are born. Even before we released
the Call for Papers (CFP), our speaker list is full of some of the industry's
best and brightest minds. Whether you know Linux, how to program, are
established in security, or a hobbyist, the ideal of DerbyCon is to promote
learning and strengthening the community.
Tickets to this event are very limited - Registration begins Friday, April 29,
2011. Mark your calendar, tell your friends, and get ready for a new era in
hacker cons - http://www.derbycon.com. |
| 01/10/2011 |
Darknets and hidden servers: Identifying the true IP/network identity of I2P
service hosts
This is the paper I will be presenting at
Black Hat
DC 2011. While it focuses on finding web servers hidden in the I2P darknet,
the same ideas should be applicable to Tor and other privacy systems. The
primary motivation for this project is to help secure the identity of I2P
eepSite (web servers hidden in the I2P network) hosts by finding weaknesses in
the implementation of these systems at higher application layers that can lead
to their real IP or the identity of the administrator of a service being
revealed. We also wish to find vulnerabilities that may lead to the anonymity
set being greatly reduced, and compensate for them. Exposing these weaknesses
will allow the administrators of I2P eepSite services to avoid these pitfalls
when they implement their I2P web applications. A secondary objective would be
to allow the identification of certain groups that law enforcement might be
interested in locating, specifically pedophiles. |
| 01/08/2011 |
Installing the I2P darknet software in Linux
This video is intended to get you started with the I2P darknet software under
Linux (Ubuntu 10.10 in this case). I've done a
previous version that details
installing I2P under Windows. I2P (originally standing for Invisible Internet Project) can be seen as a
networking layer sitting on top of IP that uses cryptography to keep messages
confidential, and multiple peer to peer network tunnels for anonymity and
plausible deniability. While Tor is focused more for hiding your identity while
surfing the public Internet, I2P is geared more toward networking multiple I2P
users together. While you can surf to the public Internet using one of the I2P
out proxies, it's meant more for hiding the identity of the providers of
services (for example eepSites), sort of like Tor's concept of Hidden Services,
but much faster. Another advantage I2P has is NetDB, a distributed way to let
peers know about each other once initial seeding has occurred. Tor on the other
hand uses it's own directory to identify servers, which in theory could be more
easily blocked. Both networks have their advantages and trade offs. This video
won't cover the details of I2P's peering or encryption systems, and may seem
kind of rambling, but it should be enough to get you up and running on the
darknet.
Welcome to Cipherspace.
I'll be covering my work on de-anonymizing I2P services in my
Black Hat
DC 2011 talk. |
| 01/03/2011 |
Derbycon 2011 Teaser Video
Dave Kennedy put together a teaser video
for Derbycon. Blurb from Dave: About a year ago Adrian Crenshaw, Martin Bos, and myself were sitting around in Louisville and talking about one day creating one amazing hackercon. We never imagined it would have came to light, but it did. We are happy to announce that we have done some pre-selection of some speakers which we think you'll be impressed by. Our goal is to create a hackercon that is unique, top notch, and a place where we all come together as one and share. If any of you know us personally, you know that we steer clear from a persona of an elitist. We are all in this world we call security together and none of us are better than one another. All of us are learning everyday... DerbyCon is a con where we are all in it together, where you can approach anyone, share with anyone, and have a ton of fun doing it. Our official website launch with all the relevant information about the conference will be posted January 10, 2011 (sometime during the morning/afternoon). This teaser video was released to show you a taste of some of the speakers we have. It's truly inspirational to us that we have such a great speaker list already even before CFP has officially opened.
A couple of important topics that we will leak ahead of time: The ticketing system will be straight forward, tickets will open officially to purchase April 29, 2011. The tickets will be $125.00 that weekend, and go up to $150.00 on that Monday until DerbyCon day. On the day itself tickets will be $175. I will admit there is limited spacing, we rented the entire second floor of the Hyatt and tickets will go fast.
The second leak: The con will run from 9:00am to 5:00pm Friday and Saturday and Sunday from 9:00am until 3:00pm. There will be training provided at night from 5:30pm to 10:30pm after conference hours. We will also have BSIDES KY going on at the same time from 5:30pm to 10:30pm, so regardless if your in training or BSIDES, your covered.
Sit back and relax and enjoy this 1 minute 47 second video of DerbyCon and some of the speakers and be sure to check out http://www.derbycon.com.
|
| 01/03/2011 |
ARPFreezeNG: A tool for Windows to protect against ARP poisoning by setting up
static ARP entries, now with a pretty GUI
As many of you know, I've created quite a bit of content about ARP poisoning,
such as:
A
Quick Intro to Sniffers
Intro to ARP
poisoning
Using Cain to do a man in the middle attack by ARP poisoningI've even
done some work on detection:
Decaffeinatid: A Simple IDS/arpwatch for Windows
Finding promiscuous and ARP poisoners and sniffers on your network with Ettercap
This tool is for prevention.
ARPFreezeNG lets you setup static ARP tables so that attackers (using
Cain, Ettercap, Arpspoof or some other tool) can't pull off an ARP poisoning
attack against you. It has the same core functionality as my older ARPFreeze
script, but is easier to use since it utilizes a Treeview GUI. |
| 12/26/2010 |
Irongeek In Print Updated
I've updated the page to reflect new references to my site in books. |
| 12/25/2010 |
Privacy
Papers Write-up
I was enrolled in a privacy class for my masters degree recently. As part of
this class we had to read a metric buttload of papers (but at least not an old
English buttload) and then write a short review of each, trying to find at least
three critical points we could make or at least points of interest. These are my
write-ups (with a few spelling fixes) and links to the papers in question.
Sometimes I may come off as overly critical, but we were asked to find perceived
weak points. Sometimes I just did not understand what the author was trying to
get at, either because of my lack of background or a lack of explaining. Mostly
what you will get out of this page is me being a curmudgeon about academic
papers vs. hackers/infosec practitioners. Enjoy, or don't. :)
Low-Cost Traffic Analysis of Tor
Crowds
Tor: The Second-Generation Onion Router
Untraceable Electronic Mail, Return Addresses, and Digital Pseudonyms
Chord: A Scalable Peer-to-peer Lookup Protocol for Internet Applications
Kademlia: A Peer-to-peer Information System Based on the XOR Metric
Why Kad Lookup Fails
ShadowWalker: Peer-to-peer Anonymous Communication Using Redundant Structured
Topologies
Anonymity, Unlinkability, Undetectability, Unobservability, Pseudonymity, and
Identity Management � A Consolidated Proposal for Terminology
SybilGuard: defending against sybil attacks via social networks
SybilLimit: A Near-Optimal Social Network Defense against Sybil Attacks
SybilInfer: Detecting Sybil Nodes using Social Networks
The Ephemerizer: Making Data Disappear
Vanish: Increasing Data Privacy with Self-Destructing Data
Defeating Vanish with Low-Cost Sybil Attacks Against Large DHTs
Privacy-preserving P2P data sharing with OneSwarm
Drac An Architecture for Anonymous Low-Volume Communications
Privacy Preserving Social Networking Over Untrusted Networks
The Anatomy of a Large Scale Social Search Engine
Anonymous Opinion Exchange over Untrusted Social Networks
What Do People Ask Their Social Networks and Why A Survey Study of Status
Message Q&A Behavior
�I�ve Got Nothing to Hide" and Other Misunderstandings of Privacy
Saving Facebook
l-diversity: Privacy beyond k-anonymity
Privacy in the Clouds: Risks to Privacy and Confidentiality from Cloud Computing
|
| 12/16/2010 |
DOJOCON
2010 Videos
First, thanks to Marcus Carey for
inviting me out to DOJOCON. Be sure to check out the organizers
http://www.dojocon.org/ and
http://www.reversespace.com/ and
donate to the cause if you like the event. Below are the videos from the
conference, at least the ones I can show :), enjoy.
Index:
Tiffany Strauchs Rad, @tiffanyrad:
International Cyber Jurisdiction: "Kill Switching" Cyberspace, Cyber
Criminal Prosecution & Jurisdiction Hopping
John Strauchs, @strauchs:
Security and IT Convergence
Richard Goldberg, @GoldbergLawDC:
Rules of Engagment: Mitigating Risk in Information Security Work
Jon McCoy: Ninja Patching .NET
Marco Figueroa, @marcofigueroa
& Kevin Figueroa:
Detecting & Defending Your Network using Nepenthes/Shaolin Tools
Dave Marcus, @davemarcus:
Using
Social Networks To Profile, Find and 0wn Your Victims
Brian Baskin, @bbaskin:
P2P Forensics
Jonathan Abolins, @jabolins:
Internationalized Domain Names & Investigations in the Networked World
Deviant Ollam, @deviantollam:
Don't Punch My Junk
Michael Shearer, @theprez98:
How to 0wn an ISP in 10 Minutes
Christopher Witter, @mr_cwitter:
Enterprise Packet Capture
on Da'Cheap
Ben Smith: Printer Exploitation
Adrian Crenshaw, @irongeek_adc:
Malicious USB Devices: Is that an attack vector in your pocket or are you
just happy to see me?
Shyaam Sundhar, @EvilFingers
and John Fulmer, @DaKahuna2007:
Is the IDS Dead?
Chris Nickerson, @indi303:
The State of (In)Security
Gal Shpantzer, @shpantzer:
Security Outliers: Cultural Cues from High-Risk Professions
Michael Smith, @rybolov:
DDoS
I think this is the fourth conference I've done videos like this for. I
wonder if I should start offering a service where I help record/render videos
for free if the conference can take care of travel and lodging for me? That
would let me get to more hacker cons. :) |
| 12/02/2010 |
Mr. Irongeek goes to Washington
Or at least the DC metro area. I'll be speaking at the following two
conferences:DOJOCon, Dec 11-12th
Thanks for the invite Marcus! More
USB Maliciousness :)
Black Hat
DC, Jan 18-19th
I2P Fun with identifying eepSites' real IPs
As I mention on the Fed Watch
page, I'd love to get some FBI/CIA/NSA/ETC hats or challenge coins. |
| 12/02/2010 |
Dirty Diffie-Hellman
Calculator (Like dirty Santa, but geekier)
A little Christmas game I came up with for my local ISSA's holiday get together.
It illustrates how the Diffie-Hellman key exchange works, and has a calculator
to help with the math. |
| 11/23/2010 |
Unallocated Space, A new Hackerspace
in central Maryland
A message from C-P:
UAS, the newly formed Hackerspace in Severn Maryland, is now officially open.
Located near the BWI Airport, UAS has officially opened its doors to hackers,
tinkerers, makers, and all those who have that itch, that itch to understand and
modify the world around us all. With a flexible membership structure, ample work
and chill space, Unallocated space strives to provide the best possible work
and play environment possible. A detailed description of the space can be found
at here:
http://hackerspaces.org/wiki/Unallocated_Space
An already successful fund-raising event is towards its end currently, if you
would like to help support the space, please visit the Kickstarter page here:
http://www.kickstarter.com/projects/1895459557/unallocated-space-a-new-hackerspace
Founding members of the space include C-P of DC949, Jeff Yates, Nick Farr, Dave
Marcus, ThePrez98, Marco Figueroa, and Kevin Figueroa. |
| 11/14/2010 |
Security Podcast Feed
Page Fixed and Updated
Seems the 3rd party site I used to combine feeds failed, so I modified some of
Matt's code to make it work. Current feeds include:
Infosec Daily
Pauldotcom
SecurityJustice
Securabit
Exotic Liability
Cyberspeak
Forensic 4cast
Social Engineer Podcast
Cyber
Jungle |
| 10/27/2010 |
Hack3rcon 2010 Videos
Here are the videos of the presentations from
Hack3rcon 2010. If you like them, please consider
donating to Hackers For
Charity:
http://Hackersforcharity.org
Or at least send a thank you note to the sponsors:
Platinum Sponsors:
Tenacity Solutions
Gold Sponsors:
Enterasys Networks,
e-Forensic Services
Basic Sponsors:
The304Geeks,
CharCon,
Trasher Engineering,
Masters Lawfirm
Intro with Rob Dixon and Johnny Long
(in
case you don't like the sync issue, there is just Johnny's part)
Dennis Boas
Distributed IPS - An in depth look
http://enterasys.com
Keith Pachulski & Brian Martin, Digital Trust, LLC.
Physical Penetration Testing
http://digitaltrustllc.com
http://keithpachulski.securitytactics.com
http://www.isdpodcast.com
Zate Berg aka "Zate / MrUrbanity"
Nessus Bridge for Metasploit
Kenneth Scott a.k.a. pwrcycle
tcpdump > wireshark
http://cafecode.com/
Martin Bos a.k.a. purehate
The Weakest Link: Defeating passwords in 2010
http://question-defense.com
Carlos Perez a.k.a Darkoperator
Operating in the Shadows
http://darkoperator.com/
http://pauldotcom.com/
Adrian Crenshaw a.k.a. Irongeek
Taking a leak on the network: things intruders forget that could lead to their
identity
Joshua Perrymon CEO, Packetfocus
Attacking outside the Box
http://packetfocus.com
Dave Kennedy
Hacking your perimeter.../The Social-Engineer Toolkit (SET)
http://www.secmaniac.com/ |
| 10/21/2010 |
Here is the 2nd round of Shoecon videos:
Wi-Fi Basics for Geeks - How Wireless Really Works
Advice on Starting a Startup with the ever caffeinated Billy Hoffman
Economics of Security and Cybercrime with Beau Woods
Recent Threat Landscape with Ben Feinstein
Unfortunately, I've not been able to recover the live MP4 of Skydog's talk. I
may post the file later to see if anyone else can figure a way to recover it. |
| 10/19/2010 |
First round of Shoecon videos are done:
Shoecon Intro with Rick and Scott, then some SSL Cert Wildcards fun with Karthik
Hacking Green or Eco Conscious Stalking with Rick Hayes
Physical Penetration Testing with Keith Pachulski and Brian Martin
Building a barcode LED flasher, and why with Adrian Crenshaw
High Speed Data services over RF with Brian Wilson
Rest to come soon. |
| 10/18/2010 |
Malicious USB Devices: Is that an attack vector in your pocket
or are you just happy to see me?
In this presentation I talk about
the categories of malicious USB devices:
USB Mass Storage containing malware
U3 Thumb drives with "evil" autorun payloads
Hardware key loggers
Programmable HID USB Keyboard Dongle Devices
along with detection and mitigation techniques involving GPO (Windows) and
UDEV (Linux) settings. It was presented at Phreaknic 14. |
| 10/18/2010 |
Locating I2P services via Leaks on the Application Layer
Project Proposal
While at Phreaknic 14 I did a quick lightning talk
on my project to test the anonymity provided by
I2P. Mostly I'll be aiming at web server misconfigurations in eepSites. It
starts getting fast at the end because I was running out of time (10 min is kind
of short for the subject). Still, I hope it is a good intro to
I2P, and my plans. |
| 10/10/2010 |
Network King of the Hill Write-ups
I thought this might be of interest to those of you who like hacker war games,
and want to put on their own event. This contest happened at the
Louisville Infosec 2010. Martin from
Question-Defense
and I are polishing it up and plan to run the same sort of
NetKotH event at Hack3rcon. |
| 10/08/2010 |
Identifying the true IP/Network identity of I2P service hosts
This is my project proposal for the "Advanced Topics in Privacy" class I'm in.
Please share with me your thoughts and ideas. Or at the very least, try out I2P
and see how you can use it alongside Tor. |
| 10/05/2010 |
Adrian Hong: Hackers for Human Rights - HOPE 2010
Great talk about human rights, and how hackers can help. Also, there is a bit
about I2P at the end. Posted with Adrian Hong's permission. Us Adrian's have to
stick together. :) Check out their respective sites:
http://www.pegasusnk.org/
http://www.i2p2.de/ |
| 09/25/2010 |
Beyond Nmap: Other network scanners
This is a presentation I did for the Blugrass ISSA chapter. Tools covered, at
least lightly, are: Nmap, Hping, UnicornScan,
AutoScan, Netscan, Metasploit, NetworkMiner and of course BackTrack 4 R1. A few
minor flubs, and one spot where I deleted a demo fail. :) |
| 09/25/2010 |
Defcon 18 Videos
Torrent
Awhile back I found out via DC404 that the
Defcon 18 videos had been leaked onto
http://good.net/dl/bd/. Good.net is kind of a pain since the downloads are
slow, and you can only grab two at a time with a free account. Seems now
someone has put up a torrent. It's out there in the search engines, but most
Torrent sites are so spammy that I decided to just mirror the
Defcon 18 Torrent
file. There is also a magnet link:
magnet:?xt=urn:btih:Q6AJNTOWUKEQ4V5BV7WFDW4DFA6LY32S
Enjoy |
| 09/16/2010 |
Programmable
HID USB Keystroke Dongle: Using the Teensy as a pen testing device (Defcon 18)
The Programmable HID USB Keystroke Dongle (PHUKD) is a small device based around
the Teensy microcontroller development board. It allows users to program in
keystrokes and mouse macros that can execute when the device is plugged in,
after a set time, or when certain environmental conditions are met (light,
noise, temperature, etc.) This device can be used as a replacement for a U3
hacksaw, as a device left behind to execute commands when someone with elevated
privileges is likely to be logged in, or give as a Trojan device to unsuspecting
targets. Much pwnage should ensue.
I've added my
Defcon video to
the bottom of the
Videos and Pictures section of the PHUKD article.
Also checkout the "PowerShell OMFG Video" Dave Kennedy and Josh Kelley (winfang) did at Defcon 18
http://www.secmaniac.com/august-2010/powershell_omfg/
they used PHUKD devices for part of it. |
| 08/30/2010 |
Password Exploitation Class Videos Posted
This is a class we gave for the
Kentuckiana ISSA on the the subject of password exploitation. The Password
Exploitation Class was put on as a charity event for the Matthew Shoemaker
Memorial Fund ( http://www.shoecon.org/ ).
The speakers were Dakykilla, Purehate_ and myself. This is sort of the first
Question-Defense /
Irongeek joint video. Lots of password
finding and crack topics were covered: Hashcat, OCLHashcat, Cain, SAMDump2,
Nir's Password Recovery Tools, Password Renew, Backtrack 4 R1, UBCD4Win and much
more. About 4.5 hours of content. |
| 08/24/2010 |
Louisville Infosec, Discount code
information was wrong
I was sent the wrong blurb, the discount is for $30 off, not $50. Sorry. |
| 08/24/2010 |
Louisville Infosec, Oct 7th 2010
I posted yesterday about it, but Fritz asked me to point out the discount code
one more time:
You have one week left to take advantage of the
50% 29.30303031% discount for all IronGeek
Visitors! IronGeek visitors can purchase a ticket for
$49 $69 before September 1,
2010. After this date all tickets will be $99 until the conference is sold out.
We have an excellent technical track this year - Dave Kennedy, Adrian Crenshaw,
Nathan Hamiel, Jeremiah Grossman, Tom Cross from IBM X-Force. See more at
http://www.louisvilleinfosec.com/
Here are the terms:
Register before September 1, 2010 at
http://www.regonline.com/2010_lmic
Select the registration type - IronGeek Discount
Enter the code IGK-0726
Also, shout outs to LVL1, the Louisville
Hacker space. Brad and crew put on a great "Beyond Arduino" class, teaching
the basics of programming directly to an AVR. Fun stuff, which I plan to use in
the near future for some embedded device hacking projects. |
| 08/23/2010 |
Shoecon and other events
Looks like the next two months will be pretty busy for me.
Aug 28th 2010: I have the
Local Password Exploitation Class, 20 seats left last I checked. Details in
the post I made on the 14th of Aug.
Sept 18th 2010: Shoecon will be
happening. I will be speaking, along with Rick Hayes, Keith Pachulski, Karthik
Rangarajan, Brian Wilson, Stan Brooks, SkyDog, Scott Moulton, and Ben Feinstein.
This is a donation driven event where all the proceeds will go to the Shoemaker
Memorial Care Fund. Topic for me will be making a
Barcode Fuzzer, Bruteforcer, SQL/XSS Injector using a flashing LED.
Sept 24th 2010: I'll be speaking at the Bluegrass Chapter of the ISSA on my
favorite network scanners.
Oct 7th 2010: Louisville Infosec. My topic
will be Malicious USB devices. Be sure to check out my friends Nathan Hamiel,
Dave Kennedy, Deral Heiland and Matt Neely talks as well. I also plan to run a
"network king of the hill" event.
Oct 15th-17th: I'll be speaking at
Phreaknic in Nashville.
Oct 23rd-24th: I'll be at Hack3rcon in
Charleston WV, with my buddies
Purehate and Dave Kennedy. |
| 08/14/2010 |
Local Password Exploitation Class
The Kentuckiana ISSA will be putting on class on Aug
28th 2010 from 10am to 4:30pm at the Jeffersonville Public Library. The class
will cover the details of pulling passwords/hashes that are stored on a box
where the attacker has physical access to the system, or via network
vulnerabilities that can reveal the password/hash. Topics to be covered:
- Pulling stored passwords from web browsers/IM clients and other apps
- Hash cracking of Windows passwords, as well as other systems
- Sniffing plain text passwords off the network
- How passwords on one box can be used to worm though other hosts on a
network
Seating is limited to 50 people. The class is being
held as a charity event for the Matthew Shoemaker Memorial Care Fund. Matthew
was a fellow security professional and podcaster who left behind two children,
His colleagues have set up an account to help support his two children.
Donations can be made to the Shoemaker Memorial Care Fund at The Peoples Bank,
P.O. Box 788, Winder, GA 30680. Checks can either be mailed directly or
transfers via telephone (770) 867-9111. Please place the account 00133835 on the
check. A PayPal account has been established and you can find on the right hand
side of this ISD page (http://www.isdpodcast.com/goodbye-farewall-god-bless/).
Please show your receipt for donation of at least $10 at the door.
You can must register at the following URL:
https://events.constantcontact.com/register/eventReg?oeidk=a07e2znbzbs77edf8b6&oseq=
Also, I'd like to mention Shoecon, a
one day event in Atlanta on Sept 18th. I'll plan to make a larger posting about
it later. |
| 08/09/2010 |
Barcode Fuzzer, Bruteforcer, SQL/XSS Injector using a flashing LED
It's not a full function app exactly, but it may be useful to some of my readers
as a framework when testing systems that use barcodes as input. This is a
hardware/software implementation of the ideas I mentioned in my article "XSS,
SQL Injection and Fuzzing Barcode Cheat Sheet". Essentially, this code lets
you flash an LED connected to a Teensy/Arduino in the right sequences for most
barcode readers to scan. Now we have an easier way to do some of the things Mick
and I had been talking about. I tried to make a video to show it off better, but
by myself the camera moved too much. :) When I can get an E-book reader (Nook or
Kindle) I plan to make a more reliable E-Ink display using version.As a side
note, I'm looking forward to Derbycon, even
if it is more than a year away. |
| 08/08/2010 |
The Louisville Metro InfoSec
Conference
Thursday, October 7th, 2010 at Churchill Downs (
http://www.louisvilleinfosec.com
).
Use the Discount Code: IGK-0726 when you register for $30 off the $99 ticket
price ($69), until Sept. 1st. This discount will expire on that date.I'll be
speaking there, running a "Network King of the Hill" and a Forensics challenge. |
| 08/04/2010 |
Shoemaker
Memorial Care Fund
Yesterday I mentioned the passing of Matthew Shoemaker. His friends have
set up an account to help support his two children. Donations can be made to the
Shoemaker Memorial Care Fund at The Peoples Bank, P.O. Box 788, Winder, GA
30680. Checks can either be mailed directly or transfers via telephone (770)
867-9111. Please place the account 00133835 on the check. Rick has set up a
PayPal link, which you can find on the
right hand side
of this ISD page.There are also plans to set up some charity classes.
|
| 08/03/2010 |
Post Defcon 18 Updates
First, I regret to inform you of the death of my friend and fellow ISDPodcaster
Matthew
Shoemaker. Rick has made a
post with
information on how donations can be made to help Matthew's children.I've
added my Defcon
Slides to the bottom of the
Videos and Pictures section of the PHUKD article.
Monta Elkins gave a presentation as well using an
RF transmitter to activate the
Teensy.
Dave Kennedy and Josh Kelley also gave a
Powershell talk that did some more advanced things with the PHUKD concept. |
| 07/14/2010 |
Setting up the Teensy/Teensyduino Arduino Environment
This video will show you the basics of setting up the Teensyduino environment in
Windows so you can start developing PHUKD devices. |
| 07/12/2010 |
Mutillidae/Samurai WTF/OWASP Top 10
This is a presentation I did at the
Kentuckiana ISSA and then again at the
Ohio Security Forum on Mutillidae/Samurai WTF/OWASP Top 10. I chose to post
the Ohio version of the video as I think it came out better, but the slides are
the same. Plenty of information on XSS (Cross Site Scripting), CSRF (Cross Site
Request Forgery) and SQL/Command Injection. |
| 07/02/2010 |
Locking down Windows Vista and Windows 7 against Malicious USB devices
In this article I go into a lot of details about blocking malicious USB
devices, like the
PHUKD. I plan to present such material at the upcoming Louisville Infosec.
Speaking of which:The Louisville Metro InfoSec Conference
Thursday October 7th, 2010
at Churchill Downs!
http://www.louisvilleinfosec.com/
Registrations between now and July 16th, 2010 receive a
50% DISCOUNT on the $99 ticket price!
After July 16th the ticket price will go back to normal.
Current speakers include: Marcus J. Ranum, Dave Kennedy, Rafal Los, Jeremiah
Grossman and myself. |
| 06/29/2010 |
Update to the programmable HID project
I've updated the
PHUKD Library to 0.2.
The main changes are that I've added two functions for the Gnome desktop under
Linux:ShrinkCurWinGnome()
CommandAtRunBarGnome(char *SomeCommand)
you may also see something about OS X, but it does not work. Can anyone tell
me a run bar equivalent that works in OS X?
I've also changed the library so that it goes in the normal libraries folder,
and not the same folder as your sketch. |
| 06/24/2010 |
Ligatt / Gregory D. Evans Videos
It should be noted, I did not create these videos, my buddy Rick from the
ISDPodcast did (at least the first
two). Still, they are worth sharing.
I have some links below if you want more info on the Ligatt / Gregory D. Evans
controversy that has been going around. If nothing else, it will help with
people researching the person/company:
Ligatt / Gregory
D. Evans Fun Charlatan Entry at Attrition.org Follow all the Ligatt fun on
Twitter
The
Register has a good writeup on Ligatt / Gregory D. Evans
This
is probably the most concise writeup on Ligatt / Gregory D. Evans
If
you want to read the book "How To Become The Worlds No. 1 Hacker" for yourself,
but you don't want to pay Ligatt for plagiarizing, grab the PDF at this link |
| 06/16/2010 |
Mutillidae Vulnerable Web App Updated, ver 1.5
I changed it so that now, by default, Mutillidae only allows access from
localhost (127.*.*.*), assuming the .htaccess file I've written is honored.
Thanks for the suggestion Kevin.
I've also made the install instructions somewhat better.In other news, I'll
be speaking about Mutillidae at the following two events:
Kentuckiana ISSA July Meeting
July 9th from 11:30 AM to 1:00 PM
Ohio Information Security
Forum Anniversary Event July 10th, 2010 8:30AM-5:30PM
Both are free to the public, but you have to RSVP. |
| 06/03/2010 |
PHUKD Project Page Updated
I've updated the Programmable HID USB Keyboard Dongle project page with:
More pics of newer units.
A video of the
trojaned color changing mouse.
A
PHUKD Arduino library to help developers.
I've also made a bunch of anchor tags to help in navigating to the part you
want.
As a side note, I'll be speaking about the PHUKD project at Defcon! Thanks to
Paul for the help with the hardware, the
Kentuckian ISSA for helping to
get me to Defcon, and Tenacity Solutions
for their support on this project. |
| 05/13/2010 |
Metasploit
Class Videos
On May 8th 2010 the
Kentuckiana ISSA held a 7 hour Metasploit class at the Brown hotel in
Louisville Ky. Proceeds from the class went to the Hackers For Charity Food for
Work program. The instructors were David "ReL1K" Kennedy, Martin "PureHate" Bos,
Elliott "Nullthreat" Cutright, Pwrcycle and Adrian "Irongeek" Crenshaw. Below
are the videos of the event. I hope you enjoy them, and if you do please
consider donating to Johnny Longs' organization. This should be more Metasploit
than you can stand! |
| 05/09/2010 |
Steganographic Command and Control: Building a communication channel that
withstands hostile scrutiny
This is the final report I wrote for the Malware class I'm in. |
| 05/06/2010 |
WHAS
11 Webcam Exploit
This is a segment I did an interview for. They took very little of what I said,
and played up the voyeur aspect (I told them webcams were not that big a worry,
but drive by bot installs were). |
| 04/29/2010 |
Mutillidae Updated for OWASP Top 10 of 2010
I made some changes to Mutillidae (version 1.4) to make it compliant with the
2010 version of the OWASP Top 10. I also added some modules, and fixed a bug I
must have introduced at some point that keeps the user from inserting a single
quote into their blog. |
| 04/19/2010 |
Notacon Anti-Forensics Slides Posted
I put up the slides from my Notacon talk on the same page as the longer version
of the Anti-forensics/Occult Computing talk. Hope to have the video up later. |
| 04/15/2010 |
Office XML Steganography Tool
This is some relatively crappy code I wrote to hide files inside of Microsoft
Office 2007 (and I hope 2010, though I have yet to test) docs (DOCX, XLSX, PPTX,
etc). Since the newer Office docs are basically just zip files containing XML
and resources, it's fairly easy. |
| 04/07/2010 |
Louisville Metro Metasploit Class - May 8th 2010
The Kentuckiana ISSA will be putting on a 6.5 hour Metasploit class on May 8th
2010 from 10am to 4:30pm at the Jeffersonville Public Library.Instructors
include:
David "ReL1K" Kennedy
Martin "PureHate" Bos
Elliott "Nullthreat" Cutright
pwrcycle
Adrian "Irongeek" Crenshaw
The class is being held for charity, so it's not quite free, but all we ask is
that you donate $10 to the Hackers For Charity Kenya food for work program. More
details are available at the link above. |
| 04/01/2010 |
P.H.U.K.D. Device Project Page Updated
I've updated my Programmable HID USB Keyboard Dongle project page with:
Photos of a soldered, heat shrink packaged, thumbdrive sized unit.
Code example that demonstrates timer delays and using the light sensor.
Code for doing quick diagnostics on the PHUKED unit to see which pins are
connected and what the analog pin reads.
Added a comment about being able to use the 8 position DIP switch to choose
from 256 different options.
Hope you find the updates useful.
In other news, Scott Moulton still has open seats for his
Forensics & Data
Recovery class in Washington DC class April 12-16th.
You may remember Scott from some of his presentations that I've posted to my
site:
At Least TEN things you didn't know about your hard drive!
Reassembling RAID by SIGHT and SOUND!
Advanced Data Recovery Forensics
I've not taken his class yet, but I've heard great things and know that his
talks at conferences are awesome. If you have money in your training budget,
this class would be a good place to spend it. |
| 03/28/2010 |
Outerz0ne 2010 Videos
The following are videos of the presentations from the
Outerzone 2010 hacker conference. Thanks
to Skydog, Robin, Scott, SomeNinjaMaster and the
Hacker Consortium crew for the con.
Also thanks to Karlo, Keith, and Seeblind for doing AV. I'm looking forward to
Skydogcon. |
| 03/23/2010 |
Programmable HID USB Keystroke Dongle: Using the Teensy as a pen-testing device
The Programmable HID USB Keystroke Dongle (PHUKD for short) is kind of like a U3
thumbdrive alternative, but with sensor and timer abilities. Read the article,
and I think you will see the potential of the project. |
| 03/08/2010 |
Security Podcasts Page
Updated
I've updated my security podcast page to include the
Social-Engineer.org
Podcast. Also, there's real info up on the
Outerz0ne conference website now. It's
March 19th-20th 2010 in Atlanta, GA. Hope to see some of you there. |
| 03/06/2010 |
Attacking and Defending WPA Enterprise Networks - Matt Neely
Matt Neely of
SecureState came to the March
Kentuckiana ISSA meeting and gave
a great presentation on securing and hacking WPA Enterprise networks. If you are
confused by the acronym soup of "EAP-TLS, EAP-TTLS/MSCHAPv2,
PEAPv0/EAP-MSCHAPv2, PEAPv1/EAP-GTC, PEAP-TLS" and which are the better options,
this may be the video for you. Also, go check out the podcast Matt's on,
Security Justice, it's one of the
security/hacking
podcasts I regularly listen to. |
| 03/04/2010 |
InfoSec
Daily Podcast Episode 80
Episode 80 of the ISD Podcast is up. Besides current vulnerabilities of interest
and news topics, Rick, Matthew and I discussed
text based steganography. Which reminds me, I need to update the code a
little to fix some typos. :) |
| 03/01/2010 |
Steganography: The art of hiding stuff in stuff so others don't find your stuff
This is a presentation I was working on for the malware class I'm enrolled in.
For some reason my voice was cracking while recording it, but I guess it was
good practice for the live version I'll do tomorrow. Besides just an
introduction to Steganography, I'll also talk a little about my SnarlBot project
that will attempt to use stego in a command and control channel. |
| 02/24/2010 |
Unicode and LSB Steganography program examples
I wrote these Autoit3 code examples to illustrate some of the ways that
steganography (hiding data in other data, or as I like to call it "hiding your
stuff in other stuff so people can't find your stuff") can be done. These sorts
of techniques can be of great use in passing messages without others knowing, in
anti-forensics activities, or as covert command and control channels for botnets
(as I plan to study for my final project in the malware class I'm enrolled in).
Other items: I'll be at Outerz0ne 2010
in Atlanta. Also, tomorrow night I should be on the
InfoSec Daily Podcast with an update to
my
ZipIt Z2 project. |
| 02/22/2010 |
Side-Track: Security/Pen-testing distribution of Linux for the ZipIt Z2
Ok, I've got it working, and for those who have a ZipIt Z2 I'd love for you to
test it. It's based on the RootnNxus userland, and includes the following
additional packages: cron curl driftnet dsniff etherape ettercap hping3 locate
man netcat netdiscover netwox ngrep nikto nmap ntp openssh-server perl ptunnel
python rdesktop ruby samba-tools samba4-clients secure-delete socat sqlmap
tcpdump tcpreplay tcpxtract traceroute w3af w3af-console wget whois zenmap. I've
also tweaked some of the scripts, and put a newer wireless firmware on it.
|
| 02/10/2010 |
FireTalks from Shmoocon 2010
Grecs and the folks at
Shmoo were kind enough to let me
record the FireTalks from Shmoocon 2010. Here you will find the
presentations of David “ReL1K” Kennedy, Michael “theprez98″ Schearer, Marcus J. Carey, Adrian “IronGeek” Crenshaw, Nicholas “aricon” Berthaume, Zero Chaos, Benny
"security4all"
and Christian “cmlh” Heinrich.
|
| 02/04/2010 |
I'll be at Shmoocon tomorrow, may have a live
stream up some of the time
Don't know if I'll be able to manage it, but I may be streaming some of my
activities from Shmoocon using WebCamStudio for
Linux. If I can, you will see it below (or on the
Irongeek.com site if you read this via
RSS):
Stream no longer active |
| 02/03/2010 |
XSS, SQL Injection and Fuzzing Barcode Cheat Sheet Updated
I've added the ability to use any lower ASCII character you wish, you just have
to know its decimal equivalent. I've also constructed and
ASCII
barcode chart that should help. Let me know if you figure out how to type
Ctrl-Alt-Del with your keyboard wedge. :)Side note, tomorrow night I'll be on
the ISD Podcast, episode 61. See you at
Shmoocon. |
| 01/30/2010 |
Video:When
Web 2.0 Attacks - Rafal Los
Recorded at: Louisville OWASP Chapter - Fourth Meeting, Friday January 29th,
2010
Speaker: Rafal Los will be discussing Flash and Web 2.0 security
I used the same rig I hope to use for recording the Fireside talks at
Shmoocon. |
| 01/28/2010 |
Infosec Daily Podcast Episode
56
We are recording tonight, so it should be up by the morning. This time the tech
segment will be on the recent bar code hacking project, which at Mick's
suggestion now has
XSS/SQL Injection for QR 2d bar codes. |
| 01/28/2010 |
XSS, SQL Injection and Fuzzing Barcode Cheat Sheet
I was listening to an episode of
Pauldotcom, and Mick mentioned something about attacks on systems via
barcode. Because of the nature of barcodes, developers may not be expecting
attacks from that vector and thus don�t sanitize their inputs properly. I had
previously written "XSS,
Command and SQL Injection vectors: Beyond the Form" so this was right up my
alley. I constructed this page that lets you make barcodes in Code 93, Code 39,
Code 39ext and Code 128A, B and C. |
| 01/25/2010 |
Botnets Presentation For Malware Class
I have to present two papers for my malware class, so I figure I'd share my
practice video with my readers. Slides are available in
PDF and
PPTX
forms. |
| 01/21/2010 |
Infosec Daily Podcast Episode
51
We are recording tonight, so it should be up by the morning. This time the tech
segment will be on
Tracking users, malware and data leaks via the USB serial numbers on flash
drives, smart phones and MP3 players. |
| 01/19/2010 |
Setting up the HoneyBOT HoneyPot
HoneyPots are hosts meant to be attacked either to distract the attackers or to
research their techniques. This video will cover setting up a simple HoneyPot in
Windows using an application called HoneyBOT. I'll also talk a little about
capturing a pcap file with dumpcap for later analysis. |
| 01/12/2010 |
Sitting in on Infosec Daily Podcast Episode
44
We are recording tonight, so it should be up by the morning. They are letting me
do a tech segment on setting up an
Ethernet bridge in Linux and
network bridging
in Windows. Also, I hope we will cover a bit about Google's
reaction to China's attacks on human rights activist's Google accounts. |
| 01/09/2010 |
Speaking at the Shmoocon FireTalks
My presentation was not accepted for the normal Shmoocon talks, but I will be
doing a much shortened version for the
FireTalks at Shmoo. For those wondering what I'll be talking about:Title:
Funnypots and Skiddy Baiting
Desciption: Ever wanted to screw with those that screw with you? Honeypots might
be ok for research, but they don�t allow you to have fun at an attacker�s
expense the same way funnypot and skiddy baiting does. In this talk I�ll be
covering techniques you can use to scar the psyche or to have fun at the expense
of attackers or people invading your privacy. Some of the topics to be covered
are: Fun with DNS and Loopback, SWATing for Packets, Lemonwipe your drive,
Robots.txt trolling, And more�
I think there are still some slots open for Firetalks, so please submit
something on the site linked to above if you have an idea.
Grecs gave me the go ahead to record the
short FireTalks at Shmoocon 2010. I've been messing around with AVISynth, and I
plan to use it to make the Fireside talks look somewhat professional, like the
ones Defcon releases. I re-encoded my "Bulilding a Hacklab" video to test out
how well the script would work,
here are the results. Let me know what you think. |
| 01/05/2010 |
New Text Article:
Tracking users, malware and data leaks via the USB serial numbers on flash
drives, smart phones and MP3 players
In this article I talk about using the USB serial number some devices have for
security and forensics purposes. By the way, I'm starting to use Twitter more,
so feel free to follow me: @Irongeek_ADC |
| 01/01/2010 |
WiGLE WiFi Database to Google Earth Client for Wardrive Mapping Tool Updated
Uploaded version 0.90. Once again, Wigle.net changed the way I had to query
their database, so I had to fix IGiGLE so it worked again. I also changed how I
got the zip code to lat/long to work. It may also now work with NAC, UTM
or a Great Britain telephone area code, but this needs more testing so please
let me know. |
| 12/29/2009 |
Ethernet bridge in Ubuntu Linux video updated
I fixed the sound and frame size in the video I posted this morning.
As a side thing, check out Webcam Studio For
GNU/Linux (WS4GL). I'm hoping as it matures I'll be able to use it as a
poorman's tri-caster when I record/stream presentations at hacker cons. The live
picture in picture or split screen is an awesome feature. Toss Patrick Balleux
some cash to encourage further development. |
| 12/29/2009 |
Setting up an Ethernet bridge in Ubuntu Linux
In a previous video, I showed how to set up an
Ethernet bridge
in Windows XP. This is very useful for sniffing traffic leaving your LAN for
the purposes of IDS (Intrusion Detection System), network monitoring, statistics
or just plain snooping. In this video, I cover setting up an Ethernet bridge in
Linux. Other tools used in this video include Wireshark, TCPDump, Etherape and
Driftnet. |
| 12/27/2009 |
Need a ride to Shmoocon? See this blog
As I've wrote before, I'm going to Shmoocon 2010. I've got my travel
arrangements taken care of, but I know others have not. For those looking to
ride share, check out this blog
Mubix put up and find yourself a ride. |
| 12/25/2009 |
Xmas scan
with Nmap
Happy Hacking for the Holidays. I felt like making a gimmick video for the
occasion. :) |
| 12/24/2009 |
Ethics of full disclosure concerning security vulnerabilities
Hopefully this article will be helpful to some student out there.As a side
note, a friend from the Pauldotcom mailing list says he will let me crash with
him for Shmoocon, but it's about 40min
away from the con. If anyone will let me crash in their hotel room for cheap
please let me know. :) |
| 12/22/2009 |
Ethical Analysis of Network Neutrality
This is an article I wrote for a class a few months back. It's not exactly
security related, but it may help some students understand the concepts.As a
side note, looks like I'm going to Shmoocon,
though unfortunately my talk was not accepted (Skiddy Baiting and Funny Pots).
For the record, I'll speak at pretty much any conference that's willing to give
me a space to stay and pay for my way there (I'm like a security hobo). If anyone feels like helping me with the travel expenses to Shmoocon, please donate
using the link at the top of my site :). |
| 12/18/2009 |
SANS 504 Class in Bowling Green KY
Chris Sanders wrote to let me know
SANS will be putting on a "Hacker Techniques, Exploits & Incident Handling"
class in my neck of the woods. Figured I'd let the local folks know. |
| 12/14/2009 |
InfoSec Daily Podcast Episode 27
I sat in with the guys over at the InfoSec Daily Podcast and talked shop. Go
check out the episode. I've also added them to my
security podcast list.
Enjoy. |
| 12/13/2009 |
IndySec Metasploit Class Videos
When Steve invited me up to
Indianapolis to help with a Metasploit class I jumped at the opportunity.
We had a good time and IndySec puts
on a great event. They let me record the talks, unfortunately I was testing out
a new video rig and the audio failed on the first three parts (Intro/Welcome,
Network Setup, Getting started with Metasploit). The rig worked great for the
Social Engineering,
Meterpreter and
SQL Pwnage/Fast Track sections.
My presentation was just a rehash of the video I put up last week on
msfpayload/msfencoder/metasploit 3.3 so I decided not to post it on this
page.
If you find these videos useful,
consider going to the
Metasploit Unleashed page and donating to the Hackers For Charity Kenya food
for work program, or come to the
next IndySec event. For best viewing,
I recommend downloading the MP4 files below.
|
| 12/04/2009 |
Using msfpayload and msfencode from Metasploit 3.3 to bypass anti-virus
This subject has been covered before, but why not once more? Metasploit 3.3 adds
some new options, and better Windows support. As stated in the title, this video
will cover using msfpayload and msfencode from Metasploit 3.3 to bypass
anti-virus. I will also talk a little about using CWSandbox and VirusTotal to
examine malware. If you find this video useful, consider going to the
Metasploit Unleashed page and donating to the Hackers For Charity Kenya food
for work program, or come to the
IndySec charity event. By the way, I've put out two versions of this video,
one an SWF and the other a streaming video. Please let me know which you prefer. |
| 12/01/2009 |
Using FOCA to collect Metadata about an organization
Applications can add all sorts of data into the documents they create or edit.
DOC, PDF, XLS and other file types can contain all sorts of extra data, like
usernames, network paths, printers and application version numbers. This sort of
information is great for doing initial research about an organization before
doing a pen-test. This video with cover using FOCA, pointing it at a domain
name, and grabbing metadata from doc, ppt, pps, xls, docx, pptx, ppsx, xlsx, sxw,
sxc, sxi, odt, ods, odg, odp, pdf and wpd files. |
| 11/30/2009 |
IndySec Metasploit Unleashed Charity Event
For those in the Indiana area, the IndySec group in Indianapolis is having a
Metasploit Unleashed Charity Event. Details can be found at:
http://indysec.blogspot.com/
Here are the core details:
When: December 12th from 1:00 PM to 5:00 PM
How much: $30.00 all donated to
Hackers for Charity
food program
Where: BlueLock, 6325 Morenci Trail, Indianapolis, IN
What to bring: A laptop with Backtrack or the MSF installed.
To register, and for more details on what to bring,
check out their site. |
| 11/23/2009 |
Baby Bubba Zombie Children's Book
It's Thanksgiving time again, and that means zombies, at least to me. My
zombiefest tradition started sometime around 2000. There�s just something
about a family sitting around a table, eviscerating a turkey and then
stumbling around in a tryptophan induced stupor that makes me think of the
walking dead. For those that don't know me in person, and can't be at the
fest, I thought I would share some zombie goodness with you. First, there is
the
Zombie children's book
Pascalle and I created. I made a narrated video of it that I hope you
will enjoy. Also, there is the
WinZombies application. It's like XPenguins/WinPenguins, except instead
of arctic fowls it creates little undead minions that walk around your
desktop.
Now, on to security related happenings. A few weeks ago I posted my video on
Building a Hacklab. The guys over at
Pauldotcom did a tech section about the same topic in episode 176, so go
check it out. They point out Exploit-db
as a replacement for Milw0rm. I'd also like to point out that
VMPlayer now lets you
create VMs without having to use 3rd party applications. I said in the
presentation that it didn't, but the newly released version supports this
functionality.
And finally, while you are enjoying your turkey, go check out
http://www.social-engineer.org
. I'm reading through their framework right now, and am enjoying it quite a
lot. |
| 11/7/2009 |
Building a Hacklab, and a little about the Louisville CTF event
This is a presentation I gave for the local
Louisville ISSA. I took this
as an opportunity to learn a bit about AVISynth and do a split screen video.
Thanks to Gary for being my camera man. |
| 11/6/2009 |
DoJoCon Live Stream 2009
This is pretty neat. They are streaming the talks. Check it out today (Nov
6th) and tomorrow. |
| 11/2/2009 |
Darknets: anonymizing private networks talk from Phreaknic (Networks covered
include Tor, Freenet, AnoNet/DarkNET Conglomeration and I2P)
This is a quick and dirty version of my Darknets talk from Phreaknic 2009,
I hope to have a better version up soon. It covers the the basics of
semi-anonymous networks, their use (political dissidence, file sharing,
gaming and pr0n), how they were developed and what they mean to
organizations. The main focus will be on the Tor, I2P, Freenet and anoNet
Darknets, their uses and weaknesses. |
| 10/29/2009 |
Louisville Infosec 2009 Videos
The videos are up, the title link takes you to the index but here are the
individual videos:
Insider Attacks: The How's, Why's, and What to Do's Dr. Eugene Schultz
Louisville Infosec Conference Video
The Internet is Evil
John Strand Louisville Infosec Conference Video
The Seven Habits of a Successful Information Security Career Manager
Lee Kushner Louisville Infosec Conference Video
Attacking SSL PKI
Mike Zusman Louisville Infosec Conference Video
Blocking the Covert Channels Used for Malicious Data Theft
Alex Lanstein Louisville Infosec Conference Video
Darknets: Fun and games with anonymizing private networks
Adrian Crenshaw Louisville Infosec Conference
Video
Compliance Strategy and Planning
- Building an
Effective Application Security Program
John Pavone Louisville Infosec Conference Video
SAS 70 Compliance Auditing
Rick Taylor Louisville Infosec Conference Video
Virtualizing the Security Architecture: Defending Virtual Servers and
Applications Jason Wessel
Louisville Infosec Conference Video
Bob's Great Adventure: Attacking & Defending Web Applications
Paul Asadoorian Louisville Infosec Conference Video
Advanced Data Recovery Forensic
Scott Moulton Louisville Infosec Conference Video
Blending business and technical benefits together to achieve an
effective and streamlined compliance assessment.
Jim Czerwonka and Jimmy Noll Louisville Infosec Conference Video
Thanks to Lee Pfeiffer and the student volunteers for handling the video
the day of the conference, and Brian Blankenship for editing the videos. |
| 10/28/2009 |
Speaking at the November Louisville
ISSA meeting on setting up a "hack lab" From the invite email:
Our next meeting will be Friday, November 6th from 11:30 AM to 1:00 PM at
IPI. As always, we will have free lunch, raffle prizes, and CPE credits! We
continue to execute our primary mission at each function - to continue
learning, network with other Security Professionals, and have FUN!
Please RSVP no later than Tuesday, November 3rd - 5 PM to programs -at-
issa-kentuckiana.org.
The topic is "Setting up a "hack lab" for learning security concepts."
Adrian Crenshaw - Irongeek.com
Our speaker is Adrian Crenshaw, the geek behind Irongeek.com and the guy who
set up and ran our very successful Capture the Flag event at the Louisville
Metro InfoSec Conference!
Adrian will show how to set up tools and systems to best test and learn
security techniques. This knowledge is vital for any Information Security
professional who wants to stay on top of the latest risks. |
| 10/26/2009 |
Getting started with the I2P Darknet
I2P (originally standing for Invisible Internet Project) can be seen as a
networking layer sitting on top of IP that uses cryptography to keep messages
confidential, and multiple peer to peer network tunnels for anonymity and
plausible deniability. While Tor is focused more for hiding your identity while
surfing the public Internet, I2P is geared more toward networking multiple I2P
users together. While you can surf to the public Internet using one of the I2P
out proxies, it's meant more for hiding the identity of the providers of
services (for example eepSites), sort of like Tor's concept of Hidden Services,
but much faster. Another advantage I2P has is NetDB, a distributed way to let
peers know about each other once initial seeding has occurred. Tor on the other
hand uses it's own directory to identify servers, which in theory could be more
easily blocked. Both networks have their advantages and trade offs. This video
won't cover the details of I2P's peering or encryption systems, and may seem
kind of rambling, but it should be enough to get you up and running on the
darknet.
Please note, this video came out way larger than I
intended. |
| 10/21/2009 |
Phreaknic 13, Oct 30th to Nov 1st
It's that time of the year again, and that means it's time for my favorite
con: Phreaknic!!! This year I will be presenting a hopefully more refined
version of my
Darknets talk. Check out their site for
more speakers.
Some of the other speakers include Acidus (Billy Hoffman), Morgellon, Droops,
Tyler "Trip" Pitchford, Esq., Scott Moulton, DOSMan and SlimJim. Skydog has
posted some videos about the conference on the front page of
Phreaknic.info, like this one:
but if you want to get a better feel for what the conference is
like, check out my documentary video from the
Phreaknic 12 hacker con. |
| 10/12/2009 |
How to Cyberstalk Potential Employers Article Updated
I've added some sections at the end with useful links, tools and further
research. I also fixed some minor typos. If you have any ideas for additions
please email me.
|
| 10/11/2009 |
Louisville InfoSec CTF 2009
This video summarizes one possible way contestants could have completed the
Capture The Flag event at the 2009
Louisville Infosec. Tools and concepts used in the video include: Backtrack
4, Kismet Newcore, Nmap, Metasploit, Meterpreter, Firefox, SQL Injection, Cain,
Truecrypt and 7zip.The winning team was comprised of Rel1k (Dave Kennedy),
Pure-Hate, Archangel, and Titan. Yes, Dave did compromise my personal laptop
during the event, teaches me for not mitigating 0 days before the conference. :)
When Archangel told me he was bringing Dave in for his team, I knew which way
thing were going to go down. Rel1k and Purehate are Backtrack 4 developers, and
Archangel and Titan are no slouches either. Congrats guys. |
| 10/10/2009 |
Darknets: Fun and Games with Anonymizing Private Networks
Here are the slides from my Darknets talk. It was first delivered at the
2009 Louisville Infosec, and I will
be doing a more polished version at
Phreaknic 2009. Networks covered include Tor, Freenet, AnoNet/DarkNET
Conglomeration and I2P. I hope to have video up soon. |
| 09/29/2009 |
File Carving and File Recovery with DiskDigger
DiskDigger is a tool that allows you to recover deleted files off of a FAT or
NTFS drive. It has two modes of operation: In the first it merely looks in the
FAT/MFT to find files marked as deleted, in much the same way that the tool
called Restoration does. In the 2nd mode it does a file carve down the drive
looking at the raw bits and finding the know headers and footers of various file
types, much like PhotoRec. While PhotoRec seems a little more powerful,
DiskDigger is easier to use and its preview functionality is quite nice. This
video will cover the basics of recovering deleted files with DiskDigger. |
| 09/27/2009 |
Pin-hole Spy Video Camera Disguised as a Pen
I thought some of you might find this an interesting gadget, so I decide to
review it. It might be useful for reconnaissance before a pen-test, or as a
covert place to store files. |
| 09/25/2009 |
Phreaknic needs speakers
As many of you know, I'm a regular at the Phreaknic conference in Nashville
Tennessee. It's an awesome hacker con, my personal favorite. It's happening Oct
30rd through Nov 1st. They still have some speaker slots open, so please, if you
have an interesting topic email
phreaknic13@gmail.com and toss your name in the pot to be a speaker. More
information about the conference can be found at
http://www.phreaknic.info/ |
| 09/24/2009 |
Forensically interesting spots in the Windows 7, Vista and XP file system and
registry updated I worked on formatting and added entries for "Temp folder
for Outlook attachments", "Flash Cookies Location" and "Printer spool folder". I
also added a menu so you can quickly find the entry you are looking for:
Windows Explorer
Recently opened files from Windows Explorer
Network Shortcuts
Items recently ran from the "Run" bar
ComDlg32 recently opened/saved files
ComDlg32 recently opened/saved folders
Recent Docs
EXE to main window title cache
User Assist
Windows General
Temp folder
Recycle Bin
Last logged on user
Event logs
Last key edited by RegEdit
List of Installed USB devices, both connected and unconnected
List of installed USB storage devices
SetupAPI Device Log
Windows Prefetch Internet Explorer
Internet Explorer Temp Folder (IE Cache)
IE Cookies
Internet Explorer History
IE Typed URLs
Internet Explorer Forms AutoComplete
Internet Explorer Password AutoComplete
Printer spool folder
Firefox
Firefox Cached Pages
Firefox Form History File
Firefox Passwords File
Firefox Cookies
Other Apps
Recently Opened Office Docs
Files recently accessed by Windows Media Player
Offline Outlook Mailbox
Temp folder for Outlook attachments
Flash Cookies Location
|
| 09/23/2009 |
Deliberately Insecure Web Applications Page Updated
Added information on Vicnum and oldapps.com. More good stuff for setting up your
hacklab. |
| 09/19/2009 |
Rohyt Belani - Bad Cocktail: Application Hacks + Spear
Phishing
Mr. Rohyt Belani was kind enough to do
a presentation on combining web application attacks with spear phishing at the
Sept 2009 Louisville OWASP
meeting (our chapter's LinkedIn page can be found
here).
If you are interested in finding out more about some of the topics Rohyt
mentions in his presentation, check out these other videos on
Footprinting/Network Recon and
Exploiting Common Web App Vulnerabilities. |
| 09/09/2009 |
Capture The Flag At Louisville
Infosec Conference Details
As many of you know, I've been busy setting up a hacker war game for the
Louisville Infosec conference on
Oct 8th. The Louisville Infosec website has information about the
CTF event on their site, which should be updated shortly. If you would like
to compete please email the
Conference Chair. If you use the code "irongeek" you get $20 off the
admission fee for the conference. I believe the time frame is 9am to 3:30pm, but
the position of the event should allow you to watch the keynotes, eat the
included lunch and still, compete.
What are the prizes?
First prize is a Wi-Spy 2.4x Wireless Scanner!
The second prize is a WD 320GB USB Hard Drive
Third Prize is a Pico Mini USB 4GB (small enough to carry in your wallet)
Scenario (subject to some change):
The admins try to run their network as a tight ship, but you have been brought
in to do a pentest. You know the admins have a Truecrypt volume out there with
Personally Identifiable Information (PII). Your goal is to find it, and decrypt
its contents till you get a list of names and Social Security Numbers. Little
hints will be given via a comment wall on one of the web servers. To win points
bring proof to the judge that the particular flag task has be completed.These
are the "flags", and their point values:
0. Attach to the Wireless network (hint:CTF is in the name) and show the judge
how you got the SSID. 15 points
(Name will be given if you can't find it, but you won't be able to get points
for it.)
1. Find the IP of the of the Windows box named WinCTF owned by IronGCorp, and
list 3 or more open ports. 5 points
2. Find the IP of the x86 based Linux box ran by IronGCorp, and list 3 or more
open ports. 5 points
3. What box are the admins running their Intranet site on, and what is the web
server type/version? 5 point
4. What is the Windows box's (WinCTF) Administrator password? 10 points
5. What is the x86 Linux box's Root password? 5 points
6. Copy PII.tc (a true crypt volume) to your box. 10 points
7. Password to the PII.tc file. 10 points
8. Password to a non x86 based Linux box. 10 points
9. Password to a 7zip archive. 10 points
10 The decrypted PII.csv file. 25 points
Highest point score at the end of the game wins. If two contestants have the
same points at the end of the game, the first to accumulate their point total
wins. Obviously, if you play as part of a team you have to figure out amongst
yourselves how to split the prize. The winner will get up on stage and explain
what he did when he picks up his prize.
|
| 09/03/2009 |
Mutillidae Venerable Web App Updated
I found out that my little teaching app stopped working with new versions of
XAMPP. It seems I have to use <?php to start my PHP tags, using just <? no
longer worked. I've updated Mutillidae to 1.3 and made it work again. |
| 09/01/2009 |
WiGLE WiFi Database to Google Earth Client for Wardrive Mapping Tool Updated
I've uploaded version 0.80 of my wardrive mapping app IGiGLE. I had to
fix some things since Wigle.net added a field to their output, throwing off all
of my code. I've also added information to each entry regarding its network
type, either infrastructure or ad-hoc. |
| 08/24/2009 |
Anti-Forensics: Occult Computing Class
This is a class I gave for the
Kentuckiana ISSA on the the subject of Anti-forensics. It's about 3 hours
long, and sort of meandering, but I hope you find it handy. For the record,
Podge was operating the camera :) Apparently it was not on me during the opening
joke, but so be it, no one seemed to get it. I spend way to much time on the
Internet it seems. Also, I'm in need of finding video host to take these large
files. This class video is 3 hours, 7 min and 1.2GB as captured.Side Note: I
still have about 7 free passes to the
Louisville InfoSec to give away. If you want a
free pass, just email me at irongeek at irongeek.com and agree to be in the CTF
event. If you don't want to be in the CTF, you could instead use the code "irongeek" when you register
and you will get $20 off the cost ($79 instead of $99). |
| 08/18/2009 |
Fear and
loathing at the Riviera: A noobs guide to Defcon
This is a write up of my experiences getting to, and being at, Defcon 17. Also,
check out by comments on twitter. |
| 08/14/2009 |
Security and Forensics
Podcasts Irongeek Listens To
I got tired of going to a bunch of different sites to see if my favorite hacking
podcasts had a new episode out, so I made a site that puts them all together on
one page in chronological order. Let the XSS via RSS commence! |
| 08/13/2009 |
Forensically interesting spots in the Windows 7, Vista and XP file system and
registry (prep work for my anti-forensics class)
I've started work on a list of Windows registry keys and file systems spots that
would be of interest to forensics, anti-forensics and pen-test folks. If you
have additions, please
email me. |
| 08/12/2009 |
Anti-Forensics Class Near Louisville, Aug 22nd 2009 1-4:30PM
What: The ISSA Anti-Forensics Class
When: Aug 22nd 2009 1-4:30PM
Where: Jeffersonville Library
http://jefferson.lib.in.us
Details: This class will teach the basics of Anti-forensics, how people hide
data and events on their computer for both legitimate and illegitimate reasons.
We will cover data carving, disk wiping, encryption, steganography , timestamps,
clearing logs and other ways people may attempt to cover their digital tracks.
The subject matter should be of interest to many groups, it's "Not about just
hiding your stash from the Fuzz�". Some of the groups that may be interested
include:Companies that want to know how to clear boxes before donating them
Law/policy enforcement agents who want to know how folks hide computer
activities
Users who want to know how to hide their activities from invasive law/policy
enforcement
Things to bring if you want to be hands on, but not absolutely required:
1. A Windows XP/Vista/7 laptop. Having an extra laptop to wipe may also be
educationa.
2. An external drive/thumb drive you don't mind wiping.
3. Some software I'll be emailing a link to a few days before the class.
4. Energy drinks for the teacher.
As always, the class is free, even to non ISSA members. Please reserve a spot by
RSVPing to programs -at- issa-kentuckiana.org. |
| 08/09/2009 |
Louisville InfoSec:Free passes,
discounts and the CTF
As many of you know, I attend the local Louisville Infosec conference. This year
they have offered me some promotional stuff for the conference. If you use the
code "irongeek" when you register
you will get $20 off the cost. Also, they have given me 10 free passes to give
out, but here are my conditions: 1. You must participate in are CTF event. 2. I
want you to do a write up about the conference after you attend. If you want a
free pass, just email me at irongeek at irongeek.com. For those that want more
information about the con, check out the
Louisville InfoSec website. Here are some of our speakers this year:John
Strand
Paul Asadoorian
Scott Moulton
Alex Lanstein
Adrian Crenshaw
Dr. Eugene Schultz
John Pavone
Rick Taylor
Brian Long
John Maynor
Lee Kushner
Jason Wessel
Mark Maxey
If you want to see videos from the 2008 conference check out these links:
Adrian Crenshaw - "Intro to Sniffers" from Louisville Infosec 2008
Kevin Beaver - "Staying Ahead of the Security Curve" from Louisville Infosec
2008
Rohyt Belani - "State of the Hack" from Louisville Infosec 2008
John Strand - "Advanced Hacking Techniques and Defenses" (and demos of evilgrade/passing
the hash/msfpayload) from Louisville Infosec 2008
and here is my write up from the even two years ago:
http://www.irongeek.com/i.php?page=security/louisville-infosec-conference
Also, the complimentary lunch is good. :) |
| 07/31/2009 |
Follow me and #defcon on Twitter
I'm twittering my time at Defcon, for those that care:
http://twitter.com/Irongeek_adc |
| 07/25/2009 |
DD-WRT
v24-sp1: CSRF Example (Bugtraq ID: 35742 )
I was interested in giving a real world example of using a CSRF attack, similar
to the ones I mentioned in my
OWASP
Top 5 video, and maybe use it against a piece of internal equipment that is
behind a NAT box. Then I heard about
the
Carlos Perez write-up on using Metasploit against a vulnerability in the DD-WRT
v24-sp1 firmware. I thought this would be a great way to demo the concept of
using CSRF/XSS against hardware behind a NAT, especially since I've done a
video on installing DD-WRT before. |
| 07/25/2009 |
Phreaknic 12 Videos Posted
After much encoding work, I've got all of the talks from Phreaknic 2008 up. I've
posted some of the more security related videos in my RSS feed over the past
day, but if you follow the link there's video of the other talks as well. Hope
to see some of you at Phreaknic 2009,
and if you see me at Defcon hit me up for some stickers. |
| 07/25/2009 |
Lee Baird/John Skinner - JAIL: Get your iPhone out, and try NOT to get yourself
in!
A guide on how to jailbreak your iPhone, install & backup unauthorized apps, and
what to do with your iPhone once it's jailbroken. |
| 07/25/2009 |
Nathan Hamiel /Shawn Moyer - Satan is on my Friends List: Attacking Social
Networks
Social Networking is shaping up to be the perfect storm... An implicit trust of
those in one's network or social circle, a willingness to share information,
little or no validation of identity, the ability to run arbitrary code (in the
case of user-created apps) with minimal review, and a tag soup of client-side
user-generated HTML (Hello? MySpace? 1998 called. It wants its markup vulns
back). Yikes. But enough about pwning the kid from homeroom who copied your calc
homework. With the rise of business social networking sites, there are now
thousands of public profiles with real names and titles of people working for
major banks, the defense and aerospace industry, federal agencies, the US
Senate... A target-rich and trusting environment for custom-tailored,
laser-focused attacks. Our talk will show the results of a series of public
experiments aimed at pointing out the security and privacy ramifications of
everyone's increasingly open, increasingly connected online personae and the
interesting new attack vectors they've created. |
| 07/24/2009 |
Handgrip/Buttstock - Open Source AK-47's
Ensuring freedom through greater firepower. How to build yourself a legal,
paperwork-free AK47 from salvage parts. |
| 07/24/2009 |
Darren Kitchen - Lessons Learned in Hacker Media
From e-zine to podcast the world of hacking has been filled with media of all
sorts. In this talk I will speak about my experiences and lessons learned in
"new media". In particular how they relate to underground culture and our social
responsibility to the next generation of security enthusiasts. |
| 07/24/2009 |
Daniel Hooper - An Introduction to Software Defined Radio by Cowboy Dan
Software Defined Radio (SDR) is the latest (and possibly last) iteration of
radio communication technology. Traditional radio technology is very
hardware-oriented, and somewhat inaccessible to the software-hacking community.
NO LONGER! With a fixed piece of hardware such as the Universal Software Radio
Peripheral (USRP), we can emulate many different kinds of traditional hardware,
from CW Morse-code type transmissions, all the way up to digital QAM, HDTV, and
beyond. This presentation will demonstrate how to get set up with GNU Radio and
the USRP hardware. We will perform a few simple tasks such as receiving radio
and TV. The goal is to get most people in the audience comfortable with the
setup process so that they can start experimenting. |
| 07/24/2009 |
SkyDog & Crew - Starting your own Hackerspace (Panel Talk)
Got a bunch of hacker/maker friends and wanna do some projects? Start a
hackerspace! We'll take you on an adventure as we look back over the last year
and reflect on the progress we have made getting our hackerspace started, and
share some pitfalls and triumphs along the way. Skydog will be joined by
Seeblind, the VP of the HC, Mudflap, the Secretary, and Someninjamaster, a
devoted, hardworking member. |
| 07/24/2009 |
Irongeek - Hardware Keyloggers: Use, Review, and Stealth (Phreaknic 12)
This talk will cover hardware keyloggers and their use. About six will be
presented in person for folks to try hands on, with a few others referenced in
the slide show (mini-pci ones for example) . I'll cover the advantages and
disadvantages of the current crop on the market and how they work. Also covered
will be possible ways to detect hardware keyloggers via physical inspection an
software. |
| 07/24/2009 |
TRiP - Discussion of the legality of wardriving (Phreaknic 12)
This talk is to provide a "current" legal status of wardriving throughout the
US. The talk will include an overview of wardriving and it's history (wardialing),
the statues regulating all 50 states and how courts have interrupted such
statutes, recent arrests for wardriving/related activities, and a brief overview
of the international statues. |
| 07/24/2009 |
Scott Moulton - At Least TEN things you didn't know about your hard drive!
(Phreaknic 12)
This speech comprises at least 10 things that are 2+2=5 type situations people
do not realize about hard drives. For Example, Data is written in Cylinders on
hard drives, all partitions are created on Cylinder Boundaries and that leaves
an offset from the end of one partition to the next which leaves a gap between
partitions that is unusable or free space at the end of the disk. In addition to
that, the point would be, since the outer edge of a drive starting at Track 0 is
the fastest location on the drive, and the first partition is created on a
cylinder boundary at the outside edge, then each and every partition you create
on the disk has to be at a cylinder boundary into the disk. This means the
second partition is on a slower part of the drive than the first. So for Mac
Users that create a 32 gig Fat32 partition on their drive (actually the 6th/7th
partition on the drive) is 32 gigs from the end of the drive on a Cylinder
boundary and they just installed Windows on the slowest part of the drive. No it
will not be animated! |
| 07/24/2009 |
Scott Milliken/Erin Shelton - Beer Hacking - Real World Examples (Phreaknic 12)
You build your own computers from the bare parts. You'd die before paying
someone else to actually write a basic HTML page for you. So why is it that you
pay up to 10x the actual cost of making beer for something of lesser quality?
This presentation will cover the various methods of making your own alcoholic
beverages (beer, cider, wine), including the equipment required and approximate
setup costs for each. Even if your skill in the kitchen is limited to the
microwave, there is a method of brewing that will work for you. Some
experimentation tricks will also be covered so that you can literally hack your
beer to create a new flavor. Samples of various batches made by the presenters
will be available during the presentation, assuming they haven't already drunk
all of it. |
| 07/24/2009 |
Bruce Potter - Three Cool Security Technologies You've Never Heard Of (Phreaknic
12)
This talk will introduce you to 3 cool security technologies that you've
probably never been exposed to. There is still innovation going on, and much of
the most useful tech isn't getting press time. So I'm going to try and rekindle
some of that love you've lost over the years by giving you the 20 minute
low-down on each one. Go get some wine, light the candles, sit back, and enjoy
security again. What are the 3 technologies? Well, you'll just have to attend
the talk to find out. |
| 07/24/2009 |
Russell Butturini - Using the Hak5 U3 Switchblade as an Incident Response and
Forensics Tool (Phreaknic 12)
This talk will explain how to adapt the Hak5 switchblade, originally conceived
as an attack/pen-testing tool into an incident response and forensics tool using
different utilities. Adaptations of the original solution using a non-U3 drive
and a more automated solution using U3 technology will be discussed. |
| 07/22/2009 |
Ncat
Tutorial: A modern Netcat from the Nmap team
For those not in the know, Netcat is a utility who's goal is to be like the Unix
cat command, but for network connections. It has been referred to as
a "Swiss-army knife for TCP/IP" for good reason, since it can do so many things.
This is the biggest Flash tutorial I've done in awhile at 41.2MB, so I plan to
relax some. See you at Defcon. |
| 07/18/2009 |
Compiling
Nmap form source on Ubuntu
Along the way to making a video on Ncat I needed to compile Nmap 5 from source,
so I figured I might as well do a video on that as well. There are many reasons
why you might want to compile Nmap from source instead of just using the package
manager, so enjoy. |
| 07/17/2009 |
Windows 7: Copy A Modified User Profile Over The Default Profile
While this is not directly security related, it should be helpful to those who
are testing Windows 7. I'm posting it to help those who are searching the
Internet for details on copying user profiles in Windows 7. |
| 07/16/2009 |
NDiff:
Comparing two Nmap 5 scans to find changes in your network
Fyodor gave me a heads up that Nmap 5 was coming out, so I figured I'd do a
couple of videos on useful new features that come with Nmap 5 and later. For a
better understanding of Nmap in general, check out my older videos which I will
link to after the presentation. In this video I will cover the basics of using
NDiff to compare two seperate Nmap scans. This is really useful for change
management, where you want to know what new devices have appeared on your
network or about ones that have disappeared for some reason. You could easily
schedule Nmap to run on your network weekly, and then compare the differences
with NDiff to see what has changed.As a side note, looks like I'm going to
Defcon. Thanks to Haxorthematrix,
Sereyna, Minoad, Mr. Bradshaw, George and anyone else who donated to my
Paypal so I could go. |
| 07/11/2009 |
Exotic Liability Episode 25: Irongeek
sits inNDiff:
Comparing two Nmap 5 scans to find changes in your network
Fyodor gave me a heads up that Nmap 5 was coming out, so I figured I'd do a
couple of videos on useful new features that come with Nmap 5 and later. For a
better understanding of Nmap in general, check out my older videos which I will
link to after the presentation. In this video I will cover the basics of using
NDiff to compare two seperate Nmap scans. This is really useful for change
management, where you want to know what new devices have appeared on your
network or about ones that have disappeared for some reason. You could easily
schedule Nmap to run on your network weekly, and then compare the differences
with NDiff to see what has changed.
I came in as a guest of the Exotic Liability podcast, episode 25. I've not
listened to it yet, hope I came off ok. Some of the things we discussed include:
Incident response switchblade, Tiger Team: The Whole Story, Our neighborhood
memories, Kon-boot, Cool tools for data collection, P/W cracker speed test
challenge, Look at my thumb, Olympic games, Louisville Info Sec Conference,
Anti-forensics and Legalities. Thanks for having me on.As a sidenote, I may
be going to Defcon after all but nothing is confirmed yet. I'll need to find
someone's floor to crash on Wednesday night as I think I'll be arriving a day
before the person I'm staying with the rest of the con. |
| 07/09/2009 |
Incident Response U3 Switchblade From TCSTool
In Russell's own words: "The U3 incident response switchblade is a tool designed
to gather forensic data from a machine in an automated, self-contained fashion
without user intervention for use in an investigation. The switchblade is
designed to be very modular, allowing the investigator/IR team to add their own
tools and modify the evidence collection process quickly." This video shows you
how to setup u3ir, and modify it. |
| 07/08/2009 |
Using
Kon-Boot from a USB Flash Drive: Bypass those pesky Windows and Linux login
passwords completely
Kon-Boot is a neat little tool that you can boot from a CD or a floppy, change
memory before booting a full OS, and then login to Windows or Linux without
knowing a proper password. The above link contains my notes and config files to
get Kon-Boot to work from a bootable USB drive. |
| 07/07/2009 |
PHPIDS Install Notes and Test Page
I've been playing around with PHPIDS and have posted my notes on installing it
as well as details on the kinds of attacks by web site gets. Interesting, I get
a lot of attacks, mostly RFI.As a side note, GFI was kind enough to sponsor
my site for two months, show our appreciation by trying out some of their
log and vulnerability
scanning software. |
| 06/29/2009 |
How to change
your MAC address article updated, added information on OS X 10.5.6 and latter
Apparently there are some problems changing your
MAC address in
versions of OS X 10.5.6 and latter. Stefan Person sent me a note about it,
so I added it to the article.
Also, Mubix recently did a presentation
for Dojo Sec on getting a job in
information security. In it he mentions my article on
how to cyber stalk potential employers. Thank much Rob! |
| 06/20/2009 |
OWASP
Top 5 and Mutillidae: Intro to common web vulnerabilities like Cross Site
Scripting (XSS), SQL/Command Injection Flaws, Malicious File Execution/RFI,
Insecure Direct Object Reference and Cross Site Request Forgery (CSRF/XSRF)
This is a recording of the presentation I gave to the Louisville Chapter of
OWASP about the Mutillidae project. A while back I wanted to start covering more
web application pen-testing tools and concepts in some of my videos and live
classes. Of course, I needed vulnerable web apps to illustrate common web
security problems. I like the WebGoat project, but sometimes it's a little hard
to figure out exactly what they want you to do to exploit a given web
application, and it's written in J2EE (not a layman friendly language). In an
attempt to have something simple to use as a demo in my videos and in class, I
started the Mutillidae project. This is a video covering the first 5 of the
OWASP Top 10. |
| 06/12/2009 |
Louisville Infosec Conference Looking
For Sponsors/Speakers
As many of you know, I'm involved with the local ISSA group here in the
Louisville area. They are looking for sponsors for the upcoming Louisville
Infosec conference (Thursday, October 8, 2009 at Churchill Downs). We had about
250 attendees last year, so it could be a good spot for advertising your company
via a booth. One of our keynotes this year is Johnny Long. John Strand and
Eugene Schultz should also be presenting. If you are interested in being a
sponsor email marketing (at) issa-kentuckiana.org and let them know Adrian sent
you. We also may have a few speaker slots open for the breakout sessions,
contact chair (at) louisvilleinfosec.com if you have a proposal. For more
information, check out the Louisville
Infosec Conference site. |
| 06/10/2009 |
Speaking at the OWASP
Louisville meeting, June 19th 2009
Hi all, the local OWASP chapter has asked me to speak about the
Mutillidae project. While I'd like to cover all of the OWASP Top 10 that it
implements, I think there will only be time for the top 5. The description as
posted on their site follows:
The second OWASP meeting will feature a presentation from Adrian Crenshaw
of Irongeek. Adrian is a Louisville based Security professional that has
worked in the IT industry for the last twelve years.
Adrian runs the information security website Irongeek.com, which specializes
in videos and articles that illustrate how to use various pen-testing and
security tools. He's currently working on an MBA, but is interested in
getting a network security/research/teaching job in academia. Please see the
description from Adrian on his presentation on the 19th.
Title: Mutillidae: Using a deliberately vulnerable set of PHP scripts to
illustrate the OWASP Top 10 Description: A while back I wanted to start
covering more web application pen-testing tools and concepts in some of my
videos and live classes. Of course, I needed vulnerable web apps to
illustrate common web security problems. I like the WebGoat project, but
sometimes it's a little hard to figure out exactly what they want you to do
to exploit a given web application, and it's written in J2EE (not a layman
friendly language). In an attempt to have something simple to use as a demo
in my videos and in class, I started the Mutillidae project.
Mutillidae is a deliberately vulnerable set of PHP scripts meant to
illustrate the OWASP Top 10. This talk will cover installing Mutillidae in a
test environment, and how to use it to illustrate the OWASP Top 10 web
vulnerabilities in easy to understand terms.
Our meeting location will be at Memorial Auditorium, located at 970 S. 4th
Street (Corner of 4th Street and Kentucky Street).
|
| 06/07/2009 |
ARPFreeze: A tool for Windows to protect against ARP poisoning by setting up
static ARP entries
As many of you know, I've created quite a bit of content about ARP poisoning,
such as:
A
Quick Intro to Sniffers
Intro to ARP
poisoning
Using Cain to do a man in the middle attack by ARP poisoningI've even
done some work on detection:
Decaffeinatid: A Simple IDS/arpwatch for Windows
Finding promiscuous and ARP poisoners and sniffers on your network with Ettercap
This tool is for prevention.
ARPFreeze lets you setup static ARP tables so that attackers (using
Cain, Ettercap, Arpspoof or some other tool) can't pull off an ARP poisoning
attack against you. |
| 06/03/2009 |
XSS, Command and SQL Injection vectors: Beyond the Form
We are all familiar with XSS via a form field in a web application, but what
about other vectors? The article talks about using User Agent strings, even
logs, object properties and other odd alternative vectors for XSS, SQL and
command injection. What other vectors can you think of? |
| 06/02/2009 |
Another book for the list
Looks like my site has been mentioned in another book, Security+ Guide to
Network Security Fundamentals by Mark Ciampa. Thanks Mark.
In other news, Irongeek.com was a nominee for
"Best Technical Blog' at
the recent RSA Conference. Congratulations to
PaulDotCom for winning the best
security podcast award. And while I'm on the subject of great podcasts for
infosec folks to listen to, check these out:
http://securabit.com/
http://securityjustice.com/
http://www.exoticliability.com/ |
| 05/24/2009 |
802.11 Wireless Security Class for the Louisville ISSA Part 1
Originally, this was going to be one 4hr class, but Jeff had something come up
so he could not cover WEP/WPA cracking, and my section took so long that Brian
never got a chance to present his material on DD-WRT. I'm hoping to get them
back to do a part 2 of this video. In this section I cover the basics of WiFi,
good chipsets, open file shares, monitor mode, war driving tools, testing
injection, deauth attacks and the evil twin attack. Some of this comes out as
kind of a stream of consciousness, but hopefully you can find some useful
nuggets from my brain dump of what I've learned about 802.11a/b/g/n hacking. As
far as classes goes this is the mostly complicated one I've set up, and for a
wireless class Brian and I had to run a lot of wires. :) |
| 05/20/2009 |
Moth added to the Deliberately Insecure Web Applications list
Mubix sent me another project for testing
your web app security skills against, so I added it to my list. Check out
Moth and let them
know what you think. It's a VMWare image, so it should be easy to get up and
running on your box. |
| 05/12/2009 |
Free WiFi Security Class Near Louisville
You are cordially invited to a FREE
WiFi Security Class. The class
will be delivered by three of our own: Adrian Crenshaw, Jeff Jarecki and Brian
Blankenship. This is a great opportunity to learn and network. In addition,
you can earn up to 4 CPE credits for attending! Please RSVP to
programs (at) issa-kentuckiana.org
no later than 5:00 PM May 20, 2009. Please note that seating is limited!
Class Information:
Title: WiFi Security Class
Place: Jeffersonville Library Small Conference Room (Seating for 27)
Date: May 23rd
Time: 10am to 2pm.
Detailed Information:
Session 1: "Basics of WiFi"
Instructor: Adrian Crenshaw
Abstract: Scanning for networks, and sniffing. Tools we will be
discussing include: Kismet, NetStumbler, IgIgle, Wireshark and others.
About Adrian: Adrian Crenshaw has worked in the IT industry for the
last twelve years. He runs the information security website Irongeek.com, which
specializes in videos and articles that illustrate how to use various
pen-testing and security tools. He did the cert paper chase for awhile (MCSE NT
4, CNE, A+, Network+. i-Net+) but stopped once he had to start paying for it
himself. He's currently working on an MBA, but is interested in getting a
network security/research/teaching job in academia.
Session 2: "Cracking WEP and WPA"
Instructor: Jeff Jarecki
Abstract: What specific equipment do you need? What software tools do
you need? What strategies exist to defend your own networks from these types of
attacks? How many attorneys and how much money you'll need for the legal
defense team needed to defend you if you try this on a network other than your
own.
About Jeff: Jeff Jarecki has worked in the IT field for over 12
years. His previous positions include working as a Software Developer and
Programming Analyst. He is currently employed at a major healthcare corporation
as an Information Security Analyst. His focus is in software automation. His
hobbies include writing bio's and writing about his hobbies.
Session 3: "Making a cheap WiFi router better with DD-WRT"
Instructor: Brian Blankenship
Abstract: What is DD-WRT? What hardware will it run on, and why would
you want to use it? Learn how to convert an inexpensive WiFi router into a
full-featured wireless access point. An overview of configuration options and
security will be covered, as well as how to configure VPN access.
About Brian: Brian has worked in Information security for 9 years, is
currently an internal security consultant for a major healthcare corporation,
and is a founding member of the local ISSA and OWASP
chapters.
Warmest regards,
Rod Kahl
Director of Member Relations
ISSA * Kentuckiana Chapter
www.issa-kentuckiana.org
www.issa.org |
| 05/10/2009 |
Outerz0ne and Notacon 2009 Hacker Cons Report
I did some recording of the goings on at the Notacon and
Outerz0ne 2009 hacker cons. If you want
to get a feel for these cons, check out the video. |
| 05/09/2009 |
New video:Hacker Con WiFi Hijinx
Video: Protecting Yourself On Potentially Hostile Networks
This is a presentation I gave for the
Kentuckiana ISSA on May 8th, 2009. It covers the basics of protecting
yourself when using open WiFi on a potentially hostile networks, most notable
Hacker cons, but also coffee shops, libraries, airports and so forth. Topics
include: open file shares, unneeded services, sniffing and evil twin attacks.
The talk is based on the
Hacker
Con HiJinx tri-fold I wrote awhile back. |
| 04/29/2009 |
Speaking at the
Louisville ISSA May 8th 2009
I'm giving a presentation for the ISSA on May 8th, based on my
Hacker
Con HiJinx tri-fold. Details on location and how to RSVP can be found below:
ISSA Kentuckiana Members,
The next meeting will be Friday, May 8, 2009, from 11:30 am to 1:00 pm @
Innovative Productivity / McConnell Technology, 401 Industry Rd, Louisville,
KY 40208
Please RSVP to programs (-at-) issa-kentuckiana.org
no later than 5:00 PM May 5.
Our speaker will be our
own Adrian Crenshaw. Adrian's topic will be "Hacker Con WiFi Hijinx:
Protecting Yourself On Potentially Hostile Networks."
Adrian's Bio:
Adrian Crenshaw has worked in the IT industry for the last twelve years. He
runs the information security website Irongeek.com, which specializes in
videos and articles that illustrate how to use various pen-testing and
security tools. He did the cert paper chase for awhile (MCSE NT 4, CNE, A+,
Network+. i-Net+) but stopped once he had to start paying for it himself.
He's currently working on an MBA, but is interested in getting a network
security/research/teaching job in academia.
Please take time from your busy schedule to join us in hearing Adrian's
perspective and for a networking opportunity with many of the area's
dedicated security professionals.
As
always, lunch will be FREE and we will give away a few raffle prizes! Hope
to see you there!
Warmest regards,
Rod Kahl
Director of Member Relations
ISSA * Kentuckiana Chapter
relations (-at-) issa-kentuckiana.org
www.issa-kentuckiana.org
|
| 04/29/2009 |
Mutillidae 1: Setup
Mutillidae is a deliberately vulnerable set of PHP scripts I wrote to implement
the OWASP Top 10 web vulnerabilities. I plan to use these scripts to illustrate
common web app attacks in a series of future videos. The easiest way to get up
and running with Mutillidae is to use XAMPP, an easy to install Apache
distribution containing MySQL, PHP and Perl. This first video covers setting up
Mutillidae, which can be downloaded from:
http://www.irongeek.com/i.php?page=security/mutillidae-deliberately-vulnerable-php-owasp-top-10 |
| 04/20/2009 |
Making Hacking Videos: Irongeek's Presentation from Notacon 2009
Over the years I've done a lot of video tutorials using screencasting software to teach folks new to hacking how various security
tools work. I'd like to share the tips and tricks I've learned so that others
can start to teach people about technology in the same way. Covered topics will
include: Screencasting software, free tools, getting the best video for the
least bandwidth, audio work, free hosting, animations and more. This is a presentation I did for
Notacon 2009. Thanks to Ted and crew for recording it. |
| 04/15/2009 |
New Video:Using SSLStrip to proxy an SSL connection and sniff it
John Strand of
Pauldotcom allowed me to post this
video that shows how to use SSLStrip to proxy an SSL connection and sniff it,
without those annoying warning messages about the cert that other tools give. From
John's description:
With SSLStrip we have the ability to strip SSL from a sessions. Using this tool
we have the capability to capture in clear text user IDs and passwords. |
| 04/03/2009 |
Mutillidae: A Deliberately Vulnerable Set Of PHP Scripts That Implement The
OWASP Top 10 Updated
Added the activity log section so I could show off stored user agent XSS, added
information on cookie stealing with XSS to the tips section, added catch.php to
show how to grab data after an XSS and did a few other minor little tweaks.
Also, I changed some of the text around to include the "Ate up with suck"
slogan.As a side note, I hope to see some of you at
Notacon this year. |
| 03/30/2009 |
Presentation Recording Rig Setup
I've been wanting to record some of my live classes, as well as the talks at the
upcoming Louisville Infosec.
This is the rig I plan to use to capture both the Power Point/computer screen
and live video of the presenter at the same time. Let me know if you have any
ideas for improvement. |
| 03/25/2009 |
Footprinting, scoping and recon with DNS, Google Hacking and Metadata
This class covers recon work, showing the student how a pen-tester/attacker can use public information to learn more about an organization before they compromise it's security. Covered topics will include DNS tools (like Whois, NSlookup/Dig, Nmap -sL), Google Hacking using advanced search terms and Metadata in images and documents. Recorded for the Kentuckiana ISSA on March 21, 2009.
It's about 3hr 7min long. |
| 03/20/2009 |
Joe McCray "Advanced SQL Injection"
Joe McCray of
Learn Security Online sent me a video of a presentation he gave on Advanced
SQL Injection. It's a great primer, and I love his presentation style. Someone
buy the man a VGA to composite converter, or a HD camcorder so he can keep
making these vids. |
| 03/19/2009 |
Robots.txt Honey-pot
Here is a list of folks who in the last 60 days were silly enough to look at my robots.txt file. I set this up as sort of a honey pot to see who was researching my site, looking for private files I might try to hide from search engines. As a side effect I wanted to scar their psyche as
punishment. :) Fun stuff. For the love of Cthulhu don't look in those
directories. For more information on this sort of thing, check out my article on The Joys Of Skiddy Baiting.
Also, I've been prepping up for mine and Brian's
recon class this Saturday, which is
one of the reasons I put up my new
about page (EXIF data and
all).
As a final note, I'd like to thank
Seth Misenar and
the Pauldotcom guys for giving me the
new tagline for my
Mutillidae Project: "Ate up with suck". |
| 03/12/2009 |
Free Class in Louisville, KY:
Footprinting, scoping and recon with DNS, Google and Metadata
I thought some of you might be interested in this free class the Louisville ISSA
and I are doing in Louisville Kentucky on March 21 2009. You will need to RSVP
to programs (at) issa-kentuckiana.org as seating is limited. Also, you don't
have to be an ISSA member, it's free to the public:
ISSA Member,
I write to inform you that Adrian Crenshaw is offering a security class on March
21st. Please take advantage of this opportunity for free training, CPE Hours and
a terrific learning opportunity. The class will be held from 9:00a until 12:00p
in the training room of Mountjoy & Bressler, LLP.
Class Information:
Footprinting, scoping and recon with DNS, Google and Metadata
This class will cover recon work, showing the student how a pen-tester/attacker
can use public information to learn more about an organization before they
compromise it's security. Covered topics will include DNS tools (like Whois,
NSlookup/Dig, Nmap -sL), Google Hacking using advanced search terms and Metadata
in images and documents.
Bio:
Adrian Crenshaw has worked in the IT industry for the last twelve years. He runs
the information security website Irongeek.com, which specializes in videos and
articles that illustrate how to use various pen-testing and security tools. He
did the cert paper chase for awhile (MCSE NT 4, CNE, A+, Network+. i-Net+) but
stopped once he had to start paying for it himself. He's currently working on an
MBA, but is interested in getting a network security/research/teaching job in
acedamia.
This is a hands on class; students need to bring their own laptops!
Please find directions to Mountjoy & Bressler attached. The training room is on
the 22nd floor and free street parking is available on the weekend.
Let me know if any questions.
Rod Kahl
Director of Member Relations
ISSA * Kentuckiana Chapter
relations(at)issa-kentuckiana.org
www.issa-kentuckiana.org
www.issa.org
Directions to Mountjoy & Bressler |
| 03/10/2009 |
Event in India
I get a fair number of readers from India, so Ravi wanted me to mention this
upcoming event:"FYODOR YAROCHKIN, the former
developer of SNORT IDS is coming to India.
From March 16th - 21st 2009, Fyodor will be discussing/offering courses on the
following topics at Fortune Katriya in Hyderabad, India:
* Advanced techniques of Computer Digital Crime scene Analysis and Forensics
* Advanced Hands-On Hacking techniques for a Penetration Tester
* Web and Application Security Advanced Training: looking at your applications
wearing the black and white hat. Looking at Application Security when the color
of your hat matters.
* Breaking networks with no wires: Attacking and securing WiFi networks, RFID
and Bluetooth implementations and more.
It's a great opportunity for beginners as well as advanced students to learn
from these courses and also to meet other corporate clients
he might be signing a MOU with E2-labs"
Just so you know, this is the Fyodor from the snort project, not Nmap. Two
different guys. |
| 03/09/2009 |
Video from Outerz0ne 5:
Outerz0ne 5 Closing
Prepare your liver for the apocalypse. |
| 03/09/2009 |
Video from Outerz0ne 5:
Acidus (Billy Hoffman) - Offline Apps: The Future of The Web is the Client?
Traditional web apps used the browser as a mere terminal to talk with the
application running on the web server. Ajax and Web 2.0 shifted the application
so that some was running on the client and some of the web server. Now,
so-called offline application are web application that work when they aren't
connected to the web! Confused? This talk will explore how to attack offline
apps with live demos of new attack techniques like client-side SQL Injection and
resource manifest hijacking.
BIO: Acidus is a Atlanta hacker who is not really sure why you keep listening to
him. |
| 03/09/2009 |
Video from Outerz0ne 5:
Rob Ragan - Filter Evasion - Houdini on the Wire
Today security filters can be found on our network perimeter, on our servers, in
our frameworks and applications. As our network perimeter becomes more secure,
applications become more of a target. Security filters such as IDS and WAF are
relied upon to protect applications. Intrusion detection evasion techniques were
pioneered over a decade ago. How are today's filters withstanding ever evolving
evasion tactics? The presentation will examine how evasion techniques worked in
the past and provide insight into how these techniques can still work today;
with a focus on HTTP attacks. A practical new way to bypass Snort will be
demonstrated. A tool to test other IDS for the vulnerability in Snort will be
demonstrated.
Bio: Background: While performing a pentest on a fortune 50 company I got
caught. My IP address was subsequently blocked. It was apparent that I was
causing way too much noise and they had triggered a network security filter that
blocked me. I came up with this presentation idea after implementing the evasion
techniques found here in a proxy application. I quickly realized none of them
work anymore on modern IDS. After some experimentation I eventually found
something that would let me sneak nearly any type of web attack past Snort. More
details on the attack can be found in my outline. I'm currently working on a
tool that will allow anyone to test their IDS/IPS for this vulnerability. |
| 03/09/2009 |
Video from Outerz0ne 5:
Scott Moulton - Reassembling RAID by SIGHT and SOUND!
RAID is a great technology and in many cases is suppose to keep our data safe.
What happens when it fails? RAID Arrays are one of the most painful things to
reassemble. RAID 0 and RAID 5 software reassemblies have problems with Slice
Sizes, and Drive Orders and in many cases, the user has no idea what the
settings are. What do you do when you don't know the Slice Size and Drive Orders
and you need the data from damaged drives? Well here is a demonstration of a way
to determine this using Sight and Sound. I crammed as much on the subject as I
can into a 50 minute presentation with Demos. |
| 03/09/2009 |
Video from Outerz0ne 5:
Makers Local 256 - A primer on hackerspaces
What they are, why they're important, where they are, and how you can start one
yourself. You may already have one close by. The talk will illustrate how
hackers are taking back the moniker and bringing the community back into the
light. |
| 03/09/2009 |
Video from Outerz0ne 5:
Presmike & Sippy - RETRI:Rapid Enterprise Triaging
The first part of this presentation presents a new paradigm for the Incident
Response process called Rapid Enterprise Triaging (RETRI), where the primary
objective is to isolate the infected network segment for analysis without
disrupting its availability. Part two of this presentation will introduce a new
Enterprise Incident Response tool that complements the RETRI paradigm. The tool
is a free, possibly open source, agent-based tool that is deployed to the
compromised segment to perform the traditional incident response tasks (detect,
diagnose, collect evidence, mitigate, prevent and report back). The tool will be
released at Blackhat 2009 / Defcon 2009 if all goes well.For now you get screen
shots. |
| 03/09/2009 |
Video from Outerz0ne 5:
Nick Chapman - Embedded Malicious Javascript
This talk will cover malicious JavaScript currently being used in the wild. It
will start with the big daddy of embedded malicious JavaScript, Asprox, which
last year gave rise to panicked headlines like "100,000s of websites
compromised" and continuing through more recent samples such as the fake Yahoo
Counter and the recent MS09-002 exploits. We will look at attack vectors,
obfuscation techniques, and multi-stage delivery systems, and exploits used.
This will feature the analysis of several samples harvest from the wilds of the
Internet.Bio: My name is Nick Chapman. I'm a security researcher with the
SecureWorks Counter-Threat Unit. Prior to focusing on security issues full time,
I worked as both a System Administrator and Network Engineer in the ISP world. |
| 03/09/2009 |
Video from Outerz0ne 5:
SlimJim100 - Live Demo of Cain & Able and the Man-in-the-middle-attack
This talk will present a live demo of a man-in-the-middle-attack, using Cain &
Able.
SlimJim100, also known as Brian Wilson, has presented at ChicagoCon 3 times in
the past. His resume is filled with 3, 4, and 5 letter certifications, and his
reputation reflects his skills.SlimJim100 - Live Demo of Cain & Able and the
Man-in-the-middle-attack. |
| 03/09/2009 |
Video from Outerz0ne 5:
SkyDog - Screen Printing Primer - Make your own Con Shirt!
A primer on silkscreening t-shirts and garments. This talk goes thru the process
of single color silkscreening, showing the steps necessary to produce the
artwork, burning a screen, and then screening a shirt. We'll be producing shirts
on stage, showing the techniques learned from much trial and error. Want to make
your own Outerz0ne 5 Con shirt? C'mon up and do it yourself. Want to see yours
made? We can do that too! Meant to be an interactive talk, to also raise
interest in graphic arts and a to try and bring back a bit of the old school
stuff.
Skydog currently works for a major university, while also holding down positions
as President for two non-profits. One is Nashville 2600, which is the group
responsible for Phreaknic, and the Hacker Consortium, a large non-profit
hackerspace in Nashville, TN. When he isn't doing all of that happiness, he's
trying to keep his son from cutting a finger off, and making sure he's not
surfing pron. |
| 03/09/2009 |
Video from Outerz0ne 5:
Tyler Pitchford - They took my laptop! - U.S. Search and Seizure Explained
An overview of recent developments impacting the Fourth Amendment and privacy
conscious computer professionals: including discussions on the United States
Constitution, Federal Statutes, Administrative decisions, and, most importantly,
the case laws that interpret and define the Fourth Amendment. Special attention
is given to topics affecting computer professionals, including border crossings,
foreign nationals, forced disclosures, and the October 2008, Crist decision.
Tyler holds degrees in Software Architecture from New College of Florida and a
Juris Doctor from the Stetson University College of Law. He co-founded the
Azureus Bittorrent client in 2003 and currently works as CTO for Digome, LLC in
Nashville, TN. His work experience includes Florida State Attorney's, Federal
Magistrate Richardson, and Justice Anstead of the Florida Supreme Court. Tyler
presented at PhreakNic 12 and has taught several courses on computer programming
and security. |
| 03/09/2009 |
Video from Outerz0ne 5:
Morgellon - *Duino-Punk! Manifesting Open Source in Physical Space from Outerz0ne 5
The goal is to promote the idea of open source hardware, and
expand the community. We will begin with an intro into what an "arduino micro
controller" is, how they work, and what you can do with them. You will see that
you don't need to be an electronics wizard to create amazing projects that
enhance your life! Whether a code ninja, hardware guru, enthusiast, a pro or
total n00b, the arduino offers amazing potential, community, and empowerment to
any who wish to grasp it.
Website: http://dailyduino.com (blog for
arduino projects and related electronics news.) |
| 03/05/2009 |
WiFiFoFum: Wardriving convenience in your pocket and uploading to Wigle
As regular Irongeek readers know, I've covered
wardriving (the act of physically moving around in meatspace looking for WiFi access point) before. In this video, I want to cover another tool for wardriving: WiFiFoFum for the Windows Mobile platform. |
| 03/04/2009 |
Hacker
Con WiFi Hijinx: Protecting Yourself On Potentially Hostile Networks Hand Out
Updated
Since I was going to print some up for
Outerz0ne this week, I decided to update
it a little and do some spell/grammar checking (Thanks Nancy). I
also plan to bring them to hand out at Notacon 2009. I've put up OpenOffice and PDF versions of the tri-fold, so feel free
to modify it for your own conference as long as you leave the credit links
intact. |
| 03/02/2009 |
Deliberately Insecure Web Applications
List Updated With "Mutillidae" And "Damn Vulnerable Web App"
When I first posted Mutillidae, Ryan Dewhurst emailed me and told be about a
project he started a few months before mine called
Damn Vulnerable Web App. His is also PHP/MySQL based, and we may be
combining some of our code base in the future. I've added Ryan's app, as well as
my
OWASP Top 10
implementation "Mutillidae", to the
Deliberately Insecure Web Applications List. |
| 03/01/2009 |
Mutillidae: A Deliberately Vulnerable Set Of PHP Scripts That Implement The
OWASP Top 10
As most of you know, I make infosec tutorial videos for my site. I want to start
covering more web app pen-testing tools and concepts. Of course, I need a
vulnerable web app or two to use in my demos. I dig WebGoat, but sometimes it's
a little hard to figure out exactly what they want you to do to exploit a given
web application. Also, WebGoat may be a little too complex to use when
introducing a web programming newbie to web application security (it's easy to
get lost in the code, especially J2EE). In an attempt to have something to use
as a demo in my videos and in class, I started the Mutillidae project. What I'm
attempting to do is implement the OWASP Top 10 Web App Vulnerabilities in PHP,
and do it in such a way that it is easy to demonstrate common attacks to others
during live classes or video form. Please let me know what you think of what
I've implemented so far, and if you are interested in helping with the project.
Also, as a side note: I hope to see some of you at
Outerz0ne this week, remember it's a
free conference (with donations gladly accepted) so if you live within a couple
of hours of Atlanta GA you really should come by. Tell them Irongeek sent you.
:) |
| 02/18/2009 |
Hak5 mentions my tool
OSfuscate and my site in episode 5x01
Snubsie of Hak5 mentioned my tool
OSFuscate in episode 5x01.
Thanks Shannon! For those the don't know, OSFuscate is a tool I wrote to
change the TCP/IP fingerprint of your Windows Box. |
| 02/17/2009 |
Louisville KY has an OWASP
Chapter!
Too bad I can't go to this first meeting since I'm going to Outerz0ne, but I
plan to attend in the future. I'll
paste the details below for those that want to attend.
Louisville OWASP
Chapter � First Meeting Friday March 6, 2009
Hello all,
I am proud to announce that
we will be starting an OWASP chapter in Louisville, with our first meeting
coming on Friday March 6!
For those not familiar with
OWASP (or the Open Web Application Security Project), it is a worldwide free and
open community focused on improving the security of application software. The
OWASP mission is to make application security
"visible," so that people and organizations can make informed decisions
about application security risks. Everyone is free to participate in OWASP and
all of the OWASP materials are available under a free and open software license.
Around the world, OWASP
sponsors local chapters that are FREE
and
OPEN to anyone interested in learning more about application security. The
chapter groups encourage individuals to provide knowledge transfer via hands-on
training and
presentations of specific
OWASP projects and research topics and sharing SDLC knowledge. The chapters
encourage vendor-agnostic presentations from both local and national application
security professionals on various topics, pertaining to application security and
more specifically the OWASP Top 10.
The first Louisville OWASP
meeting will coincide with the Kentuckiana ISSA March meeting, on Friday March
6, 2009.
The Louisville OWASP chapter
is closely associated with the Kentuckiana ISSA chapter and our first meeting
will coincide with the ISSA March meeting on Friday March 6, 2009. This first
meeting will provide a presentation that describes the OWASP community, as well
as a technical presentation showing what SQL injection is and how it easily it
can be accomplished. This demo will strive to serve as a reference and overview
of the major vulnerability that can exist in a web application. If you have
never seen SQL injection in person this is a great chance to learn about it and
come ask any questions you have.
Curtis Koenig
and Mitch Greenfield, both from Humana, will be our presenters.
Following March's meeting,
we will meet quarterly on a different day and time. The information on future
meetings will be following soon. Please provide feedback to the board.
-
When: Friday, March 6,
2009, from 11:30 am to 1:00 pm @ Innovative Productivity / McConnell
Technology, 401 Industry Rd, Louisville, KY 40208
Our initial sponsor is
Accuvant, and we are very interested in other interested parties that would be
interested in sponsoring the chapter.
If you plan to attend the
meeting please RSVP by email to
Kristen Sullivan.
Everyone is welcome to join
us at our chapter meetings. Please check out our website at
http://www.owasp.org/index.php/Louisville
Thanks and we hope to see you
on March 6th!
Chris
Parker
Named Account Manager
|
| 02/14/2009 |
Outerz0ne: Hacker Con in Atlanta, March 6-7,
2009
I and some of my friends will be attending Outerz0ne 5 next month in Atlanta
Georgia. It's organized by SkyDog and crew, who also now organizes Phreaknic so
it should be an awesome con. It's also inexpensive since the attendance fee is
donation based and the hotel is reasonable. Hope to see some of you there.  |
| 02/13/2009 |
Obfuscated 4chan.gif/Invasion.gif/SYS.JSE Decoded and Removal
Those that follow me on the various forums/mailing lists I post on know I've be
interested in how the 4chan.gif/jse was encoded. The above link is my write up
on the subject. Thanks to Byte_Bucket for pointing me in the right direction. |
| 02/13/2009 |
Bluetooth Wireless Hardware Keylogger Review
The folks over at Wirelesskeylogger.com
were kind enough to send me a review unit. For more info on hardware keyloggers
in general, check out some of my other articles and videos on the topic which I
will link to at the end of this presentation. The core idea of a wireless
hardwarekeylogger is that you only have to get physical access to the computer
once to install it. From then on you just have to get close enough to the box
with a bluetooth device to grab the logs, at least in theory. |
| 02/03/2009 |
Mobile
Pen-testing/Hacking tools section created, along with some other updates
Since it's been so long since I've updated my Zaurus section I decided to
replace it in the top menu with a
Mobile Device
Hacking section that collects all of my work with the Nokia n810, Windows
Mobile and Zaurus platforms. I'm getting an HTC Touch Pro, so if you have any
pen-testing/network apps you think I should mention for the Windows Mobile
platform please let me know.
Eric over at
http://www.isyougeekedup.com/ has already pointed some stuff out to
me.In other news, I'm playing with using the robots.txt file for
trolling/honey-potting people who recon my site (and damaging their psyche in
the process). More details on what
robots.txt is
can be found at Wikipedia, I maw write an article about it later. Also, I've
added a store section where
folks can order Irongeek.com
t-shirts if they want (with Bushibyte's
buff penguin logo) , I only make a $2 commission but it's better than nothing
and Printfection's stuff comes out pretty good. Also,
ISSA Louisville is having their
monthly meeting Feb 6th, don't forget to RSVP. |
| 02/01/2009 |
Tor or not Tor: How to tell if someone is coming from a Tor exit node, in PHP
Awhile back I was thinking it would be cool to make my page look different for
people that are using the Tor anonymizing network. Also, I though it might
useful to some administrators to be able to block Tor users from certain
functions on their sites. I'm not in favor of censorship, but for certain
practical reasons it can be useful to detect Tor exit nodes and keep them from
accessing certain resources. I found some example code in Python, but I wanted
to code it in PHP for my site. I looked at the documentation on TorDNSEL and
came up with the code available at the link above. The example output is in the
image below.  |
| 01/29/2009 |
New Video:
Setting Up Tor Hidden Services
In a previous video I covered using the Tor anonymity network to browse the web anonymously. In this one I'll cover the basics of setting up a Tor hidden service. With a Tor hidden service, the true host IP of the service is hidden by the Tor network. Instead of having to hand out the true IP of the server, a service creator can hand out a *.onion hostname that's not linked directly to them. By setting up a Tor hidden service it becomes much harder for an adversary to figure out where the service is really being hosted from, and thus much harder to shutdown. This is a great thing for people like whistle blowers and political dissidents that want to share information anonymously, unfortunately it's also useful to pedos so be careful what links you choose to click on the onion network.
Also, I got Fed Watch to
work again and added to the menu system. To all of the United State Goverment
folks that use my site: I'm honored you use my resources, please let me know if
there are any training videos you would like for me to create. And send me a NSA/FBI/DHS
hat or t-shirt. :) |
| 01/24/2009 |
Irongeek's Signature
Image and Logo updated
I noticed that my
Signature Image and the logo in the top left of my site was not loading
correctly for users at certain ISPs. After contacting my hosting provider (see my
Dreamhost review)
I figured out my Whois query was failing for some ISP's IPs. Luckily I found some code from
Andrew Pociu
that showed me how to do the Whois in PHP without using the "whois" command at the shell.
Now it should work fine: 
Complete source
code for my Sig is included. I also updated my "What
is my IP and user agent" page to use the new Whois function so you can find
out who owns the IP range you are coming from. Now if I can just figure out why
my FedWatch page is taking
so long to load.
As a side note, sorry I'm not posting as much as I use to. I'm taking one MBA
class and two SANS @Home courses
right now, which takes up a far bit of my time. I may also be prepping up some
more live talks for the Tech
Exchange and Louisville ISSA
events. Hope to see some of you at the
Louisville Geek Dinner, Jan 26th
2009. |
| 01/22/2009 |
DecaffeinatID Intrusion Detection System ver. 0.09
I made a few minor changes to DecaffinatID: v0.09 I fixed reverse DNS name
resolution so it actually works, compiled with the newest stable version of
AutoIT3 and straightened up some inconsistent coding concerning the ini file. |
| 01/17/2009 |
1337 in the Library: Obtaining your information security education on the cheap
People keep asking me "How do I get started in security". Well, if you're asking
for career advice I'm not your man, but on the learning side of things I think I
have a few tips I can give you. This article gives you tips on getting more out
of your local public or academic library. |
| 01/05/2009 |
Help Irongeek With Hacking
Security Video Surveillance Cameras Research
Ok, this comes down to me begging for donated or loaner hardware. I've developed
an interest in testing out the security of IP surveillance cameras, but I lack
the resources to do it. If you know anyone who would donate/loan me some
hardware that would be great. Barring that, if someone could let me test at
their facility in the Louisville KY area that would also work. I don't have
money to offer for shipping, but the vendor will get free advertisement on a
site with a high Alexa rank that makes about 6000 impressions per day (I can
email you a link to the stats page). If you can help, please
contact me. |
| 01/05/2009 |
ISSA Kentuckiana Meeting,
Friday January 9th, 2009, from 11:30 am to 1:00 pm
Christmas break is over, so it's back to the monthly ISSA meetings in Louisville
Kentucky. Details are below:ISSA Kentuckiana Members,
The next meeting will be THIS FRIDAY, January 9th, 2009, from 11:30 am to 1:00
pm. Please RSVP to me no later than tomorrow 5 PM if you haven't already.
At the meeting we will vote on the 2009 ISSA Kentuckiana Officers and our
speaker will be Lee Booth from the US Mint Police. Lee will be speaking on "IT
and Life". Lee will do a few minutes on current internet scams, a few minutes on
new technologies and a few on "Deep Life Subjects".
Here is Lee's Bio:
Lee Booth currently serves as a Police Lieutenant with the U.S. Mint Police at
Fort Knox. He retired from the U.S. Army in 1998 and joined the Department of
the Treasury's Police unit. In his current position he serves as the Chief of
Operations, responsible for Patrol, Investigations, Intelligence, Special
Operations, Training and Administration Divisions. He serves as the principal
agent for strategic planning, anti-terrorism operations, vulnerability
assessment, threat mitigation, policy development, police operations, and
staffing. Lee also serves on several Anti-Terrorism Advisory Councils for DoD
and other agencies. Lee holds a Master's Degree in Criminology from the
University of Louisville, and is currently pursuing a doctoral degree in
Organizational Leadership. He is a graduate of the Southern Police Institute.
As always, lunch will be FREE and we will give away a few raffle prizes! Hope to
see you there!!
Warmest regards,
Randall Frietzsche
If you are interested is showing up as a guest, RSVP via
http://www.issa-kentuckiana.org/contactus.html
|
| 12/29/2008 |
Hacker
Con WiFi Hijinx: Protecting Yourself On Potentially Hostile Networks Hand Out
I just finished updating a pamphlet on keeping your laptop secure at hacker and
security conferences. Hopefully the information will be useful to some of you. I
plan to bring them to hand out at Notacon 2009. I've put up OpenOffice and PDF versions of the tri-fold, so feel free
to modify it for your own conference as long as you leave the credit links
intact. |
| 12/29/2008 |
SANS @Home, Network Penetration Testing
and Ethical Hacking
 The
folks at SANS are offering the
Irongeek.com community a 10% discount on the tuition fee for the new Ed
Skoudis course taught via SANS @Home, Network Penetration Testing and Ethical
Hacking, starting January 13. For full course details and to register, visit
http://www.sans.org/info/33899 and when registering, use the group discount
code: IGAH-10 The
folks at SANS are offering the
Irongeek.com community a 10% discount on the tuition fee for the new Ed
Skoudis course taught via SANS @Home, Network Penetration Testing and Ethical
Hacking, starting January 13. For full course details and to register, visit
http://www.sans.org/info/33899 and when registering, use the group discount
code: IGAH-10
I'm actually planning on sitting in on this one. It should be fun.
|
| 12/27/2008 |
Louisville Geek Dinner, Jan 26th
2009
The 6th Louisville Geek dinner is coming up in about a month. I and a few of my
information security buddies from the Louisville Kentucky area plan to attend.
If you are interested in attending, go to their page to
sign up.
There's no cost (other than what you order to eat/drink) and it gives you a
chance to network with locals. Tell them Irongeek sent you. :) |
| 12/22/2008 |
Deliberately Insecure Web Applications For Learning Web App Security (WebGoat,
WebMaven, Hacme Series, etc.)
I was looking to find some insecure web apps for a pen-testing class I hope to
give. Let me know if there are more I should add to my list. |
| 12/20/2008 |
Paros Proxy Without Changed User Agent
I recompiled the Paros proxy to remove the "Paros/3.2.13" string it adds to the
end of your user agent. Now you can pen-test applications that blacklist user
agents with Paros in them. |
| 12/17/2008 |
New Video:
NetworkMiner for Network Forensics
NetworkMiner is a cool little sniffer app by Erik Hjelmvik. Described as a
Network Forensic Analysis Tool (NFAT), it allows you to parse libpcap files or
to do a live capture of the network and find out various things passively. The
main uses I like it for are file reconstruction of FTP, SMB, HTTP and TFTP
streams as well as passive OS fingerprinting, but it can do a lot more.
NetworkMinor uses the Satori, p0f and Ettercap OS fingerprints, and can be run
from a thumb drive without having to install it. It's designed to run under
Windows, but you can also use it under Linux with Wine. |
| 12/15/2008 |
Nmap Network Scanning: The Official Nmap Project Guide to Network Discovery and Security Scanning
As many of you know, I regularly use Nmap in my tutorials. A few examples are:
Nmap video 1,
Nmap video 2 and
Nmap
presentation for the ISSA in Louisville Kentucky. Gordon "Fyodor" Lyon was
kind enough to send me a signed copy of his new Nmap book. I've been reading the
drafts as they've come out and it's some good stuff if you want to know the
details of how the TCP/IP stack works, and the hardcore details of using Nmap to
scan your network. Good luck with the book Fyodor.
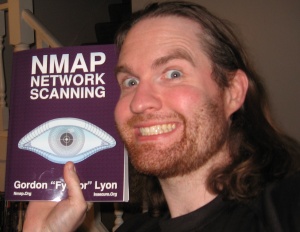
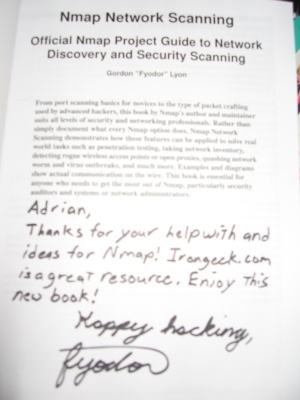 |
| 12/14/2008 |
A note on modems and wardialing from a Zaurus
I know it's been a long time since I did anything with my Zaurus pages, but
Knightmare was kind enough to send me his notes on modems and wardialing from
the Zaurus. |
| 12/05/2008 |
New Video:
Intro to
Wireshark
Wireshark is an awesome open source general purpose network analyzer (AKA: a
Sniffer). Before you continue on with this video, I recommend that you check out
my article
A
Quick Intro to Sniffers
so you understand the background information. In this video I'll cover the following topics:
Running Wireshark, starting a capture with options, drilling down the OSI model, capture filter options, popping out a single packet, sorting by columns, following TCP streams, exporting HTTP objects, simple display filters, the filter builder, applying filters from different panes , saving filters, opening a Wiki page, Edit-> Find packet, sniffing an HTTP Basic Authentication password, Analyzers ->Expert Info, Analyzers ->Firewall ACLs, stats, editing color rules and saving the capture. |
| 11/30/2008 |
New Video:
Hacking Your SOX Off: Sarbanes-Oxley, Fraud, and Fraudulent Financial Reporting
I had to do a presentation for one of my MBA courses, and one of the topic
choices was the Sarbanes-Oxley act. I chose it because I thought I could relate
it to computer security, but as it turns out the connection is somewhat tenuous
as you will see if you watch the presentation. |
| 11/22/2008 |
Bypassing Anti-Virus with Metasploit
This video from John Strand shows how to bypass anti virus tools utilizing the
new tricks in Metasploit 3.2 |
| 11/22/2008 |
Deploying Metasploit's Meterpreter with MITM and an Ettercap filter
In this video, Bigmac shows how to redirect web traffic and trick users into
downloading Meterpreter and running it on their box. |
| 11/16/2008 |
Sniffers Class for the Louisville ISSA
The video quality of this lecture is not very good, but it should give you an
idea of what my ISSA classes are like. Covered topics include Wireshark,
Ettercap, Cain and the slightest bit of NetworkMiner before the camera cut out.
Pardon the blue tint, it was the projectors fault and not the Aiptek Action
HD's. I shrunk it down from the original 720p, so the screen is not all that
readable. I also experimented in cleaning up the audio in Audacity. I hope to
cover Wireshark and NetworkMiner again shortly in higher quality videos.Also,
check out the
Securabit podcast I was a part of. |
| 11/05/2008 |
Hak5 Episode
10: Phreaknic, and a short interview of me :)
I met the Hak5 folks at Phreaknic this year, it was a great time. Check out
their footage at the link above. |
| 11/04/2008 |
Securabit security podcast guest appearance
Securabit will be streaming somewhere around 7:30pm EST on Wed, November 5th and
have tentatively scheduled me to come on the show. Join them on IRC or Skype:
IRC: irc://irc.freenode.net/securabit
Skype: (469) 277-2248Should be fun, and I hope not to embarrass myself live. |
| 10/29/2008 |
Extraordinary Journey from Fundamental Electronics to Fabulous Enchanted Systems
with Arduino's and Magical Potions
This is Morgellon and Droop's talks about hacking the
Arduino micro controller platform from
Phreaknic 12. Droops and Morgellon will
take you from basic electronics to building embedded systems. Learn how to build
a standalone RFID tag reader with a fancy LCD display or your own oscilloscope
or children's toys that speak to you or how to solar power a geothermal heat
pump. There may even be some giveaways and contests. Magical Potions will be
consumed but not provided.
Check out the following sites by Droops and Morgellon:
http://dailyduino.com/
http://www.hackermedia.org/
I've done a little work to pull some noise out of the audio, but I may have
made it worse in some spots. Thanks go out to the Phreaknic 12 A/V team
SomeNinjaMaster, Night Carnage, Greg, Brimstone, Poiu Poiu, Mudflap, and Drunken
Pirate for setting up the rigs and capturing the video. |
| 10/29/2008 |
Phreaknic 12 (2008) Hacker Con
This is a quick and dirty video documentary of the things
that when on around the talks and event at
Phreaknic 12 (2008). Don't watch if you get sick at shaky cam movies like
Blair Witch or Cloverfield. A rough timeline of the content in the video is as
follows:
Intro and leaving Louisville with Brian. Morgellon talks
about hacking the Arduino micro controller
platform. Sorteal talks about the LiVes Open Source video editor. AT&T Batman
building by night. Mojo-JoJo soldering some stuff for the shooting range. The
patron gods of hackerdom. Registration. Con swag overview. Morgellon gets
his discreet logic on. AK-47 building with HandGrip and Buttstock. Froggy talks
up Notacon, which I plan to go to next year. Skydog explains the Jware chair
toss event, and then we compete. Rootwars hacker wargames. I ask
Int80 about using his nerdcore
music in some of my videos. NotLarry explains rootwars. Some iPhone hacking with
Lee Baird and John Skinner. I
do a little
Bluecaseing/Warnibbling with the Bluetooth on my Nokia n810. John, Lee,
Brian and I go to the German restaurant. I blind DOSman with the light from my
camera and check out what folks are doing with the
Arduinos Droops brought for folks to play
with. I check back in on R00tW4rz. I blind Droops. I talk Ettercap filters with
operat0r. USB door key fun with the
Arduino. More breadboard fun. Nokia n810 +
Ettercap Filter + Lemon-part = win.
Int80 gets down with his own bad self, and the rest of Phreaknic. I find an
energy drink with protein. Folks play with the hardware keyloggers I brought,
and we have some epic fail with the IBM Model M + USB adapter + Mac OS 10.5.
Winn Schwartau joins in on the
keylogger fun. DOSman and Zack use
a directional antenna from the 9th floor to search downtown Nashville for WiFi
access points. Zoom in on Al. John and Lee eat jerky.
Daren and Shannon from Hak5 blind me this
time. :) Then they do a quick interview. I interview
TRiP about the legalities of wardriving,
sniffing and leaving your access point open so you have plausible deniability of
copyright infringement (most likely it won't hold water in court if you are a
computer geek). I give Hak5 Daren beef jerky.
Ziplock had more con badges
than God. I meet up with Iridium. I talk with Nightcarnage about the audio/video
setup at Phreaknic. As I predicted, the
Potters won the WiFi
Race. I say why this was the best Phreaknic ever. Using green lasers on crack
dealers. Techno in the dark, the Aiptek action HD does not do well in low light.
Nicodemius shows off his Minority Report like multi-touch table. Hula hoop
contest. I check back in with Jeff Cotton and his USB keyed door. I strap on my
gear to leave the con. Brian and I do a wrap up of our thoughts on Phreaknic
2008. |
| 10/27/2008 |
Sniffers class for the ISSA Kentuckiana
I'm teaching another free class for the ISSA, hope some of my readers can make
it. Here are the details:
Who: Presented by Adrian Crenshaw of IronGeek.com
What: "Using Sniffers Effectively" - hands-on workshop with network analyzers
such as Wireshark and Cain.
When: Sat, November 8, 2008 9:00 AM - 12:30 PM
Where: Louisville Technical Institute - Room 364, 3901 Atkinson Square Drive,
Louisville KY 402018 (502) 456-6509
Directions: From 264 East get off on 1st Newburg Rd exit, Turn RIGHT at Bishop
Lane, Turn RIGHT at Atkinson Dr./Atkinson Square Dr., Go .2 miles, Turn right at
LOUISVILLE TECHNICAL/INTERIOR DESIGN INSTITUTE. Park in front parking lot. Go in
Main Lobby to sign in.
Why: ISSA Kentuckiana's mission is to be the Louisville Leader in Information
Security and Awareness. We want to provide relevant educational opportunities to
members that enable learning, career growth, and should enable certification and
technical advancement.
Cost: FREE! - Bring your own laptop or use one of the classroom PC's
How to sign up: send email to education (at) issa-kentuckiana (dot) org |
| 10/26/2008 |
Hardware Keyloggers
use detection and mitigation Phreaknic Presentation slides posted
Phreaknic was a great time this year, as
always. I've posted the slides from my hardware key loggers presentation at the
above link.
I'd like to thank the following people:Sky Dog and crew for making it happen.
Droops/Morgellon for their presentation on
Arduino, time for some hardware hacking.
Sorteal for showing me the LiVes Open Source video editor.
Marie for the dance and conversation.
TRiP for an excellent talk on the
legalities of wardriving.
HandGrip/Buttstock for the Open Source AK-47 talk.
All the folks who let me interview them.
DOSman and Zack form being DOSman and Zack.
Lee Baird and John Skinner for
comparing mobile hacking notes with me (Yippy
hacking with the iPhone / iPwn).
Ziplock for the encouragement.
Int 80 for the
Nerdcore entertainment.
Scott Moulton for the talk "At Least TEN things you didn't know about your hard
drive!" Go check out his
forensics and hard
drive recovery videos.
Nathan Hamiel/Shawn Moyer for "Satan is on
my Friends List: Attacking Social Networks", looks like I need to get into some
CSRF.
Darren, Shannon and Mubix of Hak5 for the
interview.
operat0r for the Ettercap ideas.
Brian for driving me down.
And everyone else I'm forgetting. It was a great weekend. |
| 10/20/2008 |
Using Cain to sniff RDP/Remote Desktop/Terminal Server traffic via "Man in the Middle"
In this video I'll be showing how Cain can pull off a "Man in the Middle" attack against the Remote Desktop Protocol. While RDP
versions 6.0 and later are less susceptible to these attacks because of the
verification schemes added, there is still a risk since so many users just click
yes to all warning messages. |
| 10/18/2008 |
Network Printer
Hacking: Irongeek's Presentation at Notacon 2006 now on Vimeo
This is a presentation I did for
Notacon 2006 based on my
Network Printer Hacking Article.
I decided to make it an embedded Vimeo page since that's a lot easier to view
than to have to download the AVI. I've got a presentation coming up for
Phreaknic next weekend on "Hardware
Keyloggers: Use, detection and mitigation". If you are in Nashville TN, come on
by and play with the keyloggers I'm bringing. For more info on the subject check
out these articles/videos of mine:
Hardware Key Logging Part 1: An Overview Of USB Hardware Keyloggers, And A
Review Of The KeyCarbon USB Home Mini
Hardware Key Logging Part 2:A Review Of Products From KeeLog and KeyGhost
Hardware Key Logging Part 3: A Review Of The KeyLlama USB and PS/2 Keyloggers
Hardware Keyloggers In Action 1: The KeyLlama 2MB PS/2 Keylogger
Hardware Keyloggers In Action 2: The KeyLlama 2GB USB Keylogger
|
| 10/16/2008 |
Irongeek needs hats, black
or white does not matter
I know this seems like and odd request, but I'm in need of some hats to wear at
the gym and to cons. If you are a vendor or owner of some security product or
site please contact me
and I can send you my snail mail address (not that it's hard to Google for it, I
dropped my docs long ago). |
| 10/16/2008 |
BeEF: Browser Exploitation Framework XSS Fun
John Strand of
Black Hills Security sent me
another awesome video on using BeEF, cross site scripting and other fun. |
| 10/15/2008 |
Using Metasploit to create a reverse Meterpreter payload EXE by John Strand
John Strand of Black Hills Security sent me an awesome video on using Metasploit to create an EXE with the Meterpreter payload that creates a reverse TCP connection outbound, blowing through many NAT boxes and firewalls. This goes great with a previous video I did on EXE Binders/Joiners. |
| 10/14/2008 |
Using Cain to do a "Man in the Middle" attack by ARP poisoning
I'm creating this video for three reasons:
1. While I've done a lot of videos on Cain, most of them are more advanced and assume you know the basics.
2. The last video I did on ARP poisoning with Cain was more than four years ago, Cain looks quite a bit different now.
3. I wanted a reference for the classes I'll be teaching for the Kentuckiana ISSA.
Before you watch this video, read my article "The
Basics of Arp spoofing/Arp poisoning"
so you will have a better grasp of the concept. |
| 10/11/2008 |
John Strand - "Advanced Hacking Techniques and Defenses" (and demos
of evilgrade/passing the hash/msfpayload) from
Louisville Infosec 2008
John Strand gave this presentation for the
Kentuckiana ISSA at the Louisville Infosec 2008 conference. He gives a
fascinating talk about why "security in depth" is dead, and lives again. John
then goes on to demo Evilgrade, using msfpayload and obscuring it against
signature based malware detection, dumping SAM hashes with the Metasploit
Meterpreter and using a patched Samba client to pass the hash and compromise a
system. I'd like to thank John for letting me record his talk. |
| 10/11/2008 |
Rohyt Belani - "State of the Hack" from
Louisville Infosec 2008
Rohyt Belani gave this presentation for the
Kentuckiana ISSA at the Louisville Infosec 2008 conference. Rohyt shows new
ways to think about hacking, going into how and why simple things work on the
people element. Why hack a system when a quick Google search can reveal so much?
Rohyt's talk was humorous and informative, and I'd like to thank him for letting me record his
it.
|
| 10/11/2008 |
Adrian Crenshaw - "Intro to Sniffers" from
Louisville Infosec 2008
I gave this presentation for the
Kentuckiana ISSA at the Louisville Infosec 2008 conference. I cover the
basics of how network sniffers work, and specifically talk about Wireshark,
Cain, Ettercap and NetworkMiner. I came up with the presentation on short order,
so please be forgiving of the stumbles. :) You can
download the slides
from here.
|
| 10/11/2008 |
Kevin Beaver - "Staying Ahead of the Security Curve" from
Louisville Infosec 2008
Kevin Beaver gave this presentation for the
Kentuckiana ISSA at the Louisville Infosec 2008 conference. There's a lot of
great advice in this video on how to approach an infosec career in the right
way. Kevin endorses being a security "renaissance man", expanding your knowledge
outside of the tech side to understand the business, people and legal sides as
well. At the same time he also points out that sometimes specialization is good,
so focus on your strengths. I'd like to thank Kevin for letting me record his talk. |
| 10/09/2008 |
Slides from my
"Sniffers" presentation posted
Well, LouisvilleInfosec
is over and it was even better this year that last. I met a lot of good folks,
and I hope to have the videos up shortly. For those that were there and want my
slides, they can be found
here. Hope some of
you can make it to the free Louisville Tech class in November. |
| 10/08/2008 |
John Strand's videos
on Evilgrade, Samurai, Hacker Defender and other topics (Blackhills Security)
I had the pleasure to meet John Strand tonight at the pre-LouisvilleInfosec
dinner. Great guy, and fun to talk to. Made me realize there's a lot of stuff I
need to learn about. Check out his videos at the link above. I hope to
have his keynote from the conference up at my site shortly. |
| 10/08/2008 |
New Video:Finding listening ports on your Windows box using Netstat, Fport, Tcpview, IceSword and Current Ports
Host based firewalls are fine and dandy, but I'd rather turn off services I
don't need than to just block them. Host based firewalls are sort of a bandage,
and while they can be useful for knowing what is connecting out (see egress
filtering), it's better just not to have unneeded network services running in
the first place. This video can be seen as a supplement to my article "What
can you find out from an IP?" |
| 10/07/2008 |
Update:Sniffers presentation at 2008 Louisville Metro InfoSec
Conference Thursday, October 9th, 2008
Looks like I will be presenting at the upcoming
Louisville InfoSec Conference
put on by the ISSA, Thursday, October 9th, 2008 at Churchhill Downs. The person
they had set do do the live hacking demo had to drop out, so they asked me to
fill in on short notice. |
| 10/03/2008 |
OSfuscate: Change your Windows OS TCP/IP Fingerprint to confuse P0f,
NetworkMiner, Ettercap, Nmap and other OS detection tools
I was wondering awhile back how one could go about changing the OS fingerprint
of a Windows box to confuse tools like Nmap, P0f, Ettercap and NetworkMiner. I
knew there were registry setting you could change in Windows XP/Vista that would
let you reconfigure how the TCP/IP stack works, thus changing how the above
tools would detect the OS. I wasn't sure what all registry changes to make, but
luckily I found Craig Heffner's work on the subject. In this post I cover the
issue of passive/active OS fingerprint detection, as well as release my tool
OSfuscate. |
| 10/01/2008 |
Weak Hashing Algorithms: Outlook PST file CRC32 password cracking example
In a previous video I explained the basics of cryptographic hashes. Go watch "A Brief Intro To Cryptographic Hashes/MD5"
before this video. In this tutorial, I'll be giving an example of why weak
hashes are bad. The example I'll be using is the CRC32 hash that Outlook uses to
store a PST archive's password with. The CRC32 algorithm as implemented by
Microsoft Outlook is easy to generate hash collisions for, so even if you can't
find the original password you can find an alternate one that works just as
well. |
| 09/27/2008 |
2008 Louisville Metro InfoSec Conference Schedule Posted
Cindy was kind enough to send me the schedule for the upcoming ISSA conference
in Louisville. While I'm not speaking, I did receive permission to record the
keynotes from Kevin Beaver, Rohyt Belani and John Strand which I will be posting
to this page. While not recording expect to see me in the technical track. Maybe
I'll be able to convince some of the local ISSA guys to come down to
Phreaknic with me this
year. |
| 09/25/2008 |
I'll be speaking at Phreaknic
this year
My talk proposal has been accepted, so I'll be giving a presentation on
hardware keyloggers and their detection at this year's Phreaknic. It runs
from October 24th - 25th, 2008 in Nashville, TN. It's a great event if you can
make it. |
| 09/24/2008 |
Irongeek's Hacking Lab and a review of the Aiptek Action HD 1080p
An overview of how may lab is set up, as well as a review of the Aiptek Action
HD 1080p |
| 09/23/2008 |
Teaching Hacking at College by Sam Bowne
This was a DefCon 15 presentation (August 3-5, 2007) by Sam Bowne. Sam does a
great job explaining how to teach ethical hacking at a university, and since he
gave me a shout out in the video I figured I'd post it up here. Definitely a
must watch if you are trying to convince your college's administration that it's
a good idea to teach such a course. Check out Sam's site at
http://www.samsclass.info/ if you want
to use his teaching curriculum. |
| 09/20/2008 |
DecaffeinatID Intrusion Detection System ver. 0.08
I changed how DecaffeinatID checks for file changes in the firewall log. It
seems the under Vista Autoit does not return the correct information about when
the log file has changed its size or its time stamp, so I look for line count
changes instead. This really is not the best way to do things, but it's a
workaround for the moment. DecaffeinatID now also tries to detect if you are
running Vista, and if so set's the default path to the firewall log in the ini
to "<WindowsDir>\System32\LogFiles\Firewall\pfirewall.log" instead of "<WindowsDir>\pfirewall.log". |
| 09/17/2008 |
How Sarah Palin's Email got "Hacked"
This is a quick video reconstruction I did of how Sarah Palin's Yahoo account
got "hacked". You will see it's more about insecure design and easy to find
information than anything really technical. I made a test account at Yahoo and
this video traces the steps the attacker took. I'm hoping it will be useful to
journalists who don't really seem to have a grasp on the story. Feel free to
link it anyplace you like. |
| 09/13/2008 |
New Video:
Intro to DD-WRT: Mod your wireless router to do more
DD-WRT is a Linux firmware available for many Linksys, NetGear, Belkin, D-Link,
Fon, Dell, Asus and other vendor's wireless routers. DD-WRT is far more feature
rich than the stock firmware that comes with most routers. This video covers the
basics of installing and configuring DD-WRT.Two side notes: My Nmap class
will be held at Ivy Tech in Sellersburg Indiana at 1PM on Sat Sept 20th 2008 in
room P5. If this one goes well the next presentation will be on sniffers. Also,
thanks to all of the folks who have signed up for
Dreamhost using
my discount code, it's really helped support the site with extra revenue. |
| 09/13/2008 |
Books page updated with
"Kismet Hacking" from Syngress
I did some surfing on Amazon yesterday and found out my IGiGLE tool was
mentioned in Syngress publishing's new book "Kismet Hacking" (Page 227), so I
added it to my bibliography page. Thanks for the mention guys. |
| 09/09/2008 |
2008 Louisville Metro InfoSec
Conference Thursday, October 9th, 2008
Looks like I will be attending the upcoming
Louisville InfoSec Conference
put on by the ISSA, Thursday, October 9th, 2008 at Churchhill Downs. Speakers
include Kevin Beaver, Rohyt Belani and John Strand. Read my review of
last year's Louisville InfoSec Conference. Hope to see some of you there. |
| 09/07/2008 |
IGiGLE: Irongeek's WiGLE WiFi Database to Google Earth Client for Wardrive Mapping
Updated
I've uploaded version IGiGLE 0.75. This fixes the "$WS_EX_CLIENTEDGE:
undeclared global variable." error when you try to compile with the newer
versions of Autoit3. Also, I've added a feature so IGiGLE saves your last
used settings to an ini file so you don't have to keep entering them over
and over again. |
| 09/06/2008 |
Nmap
presentation for the ISSA in Louisville Kentucky
This is a presentation I gave for the
Kentuckiana ISSA on the security tool Nmap. I've also posted the
slides and other media
so you can follow along if you like. Topics covered include: port scanning
concepts, TCP three way handshake, stealth scans, idle scans, bounce scans,
version detection, OS detection, NSE/LUA scripting and firewall logs. Hope some
of you can make it to the free class we will be holding at Ivy Tech Sellersburg
on Sept 20th, 2008 at 1pm.
Contact me to RSVP. The video is about an hour long. Enjoy. |
| 09/04/2008 |
Louisville ISSA
Nmap presentation slides and media posted
I've posted the slides and related media for the Nmap presentation I'm
giving Friday (Sept 5) for the
Kentuckiana ISSA. You should be able to find the codec for the videos in
the zip file. If you plan to come to the free class at Ivy Tech
(Sellersburg Indiana) on the 20th please contact me. |
| 09/03/2008 |
Quick Notes On Getting Bart's PE/Ultimate Boot CD For Windows To Boot From A
Thumb Drive
Just what the title says, it's just a lot easier to carry around a UFD on
you keychain than it is a CD. I use mine for password resets, removing
spyware and other odds and ends.Also, on other security topics check out
my buddy Lee's page on hacking
apps for the iPhone / iPod Touch. |
| 08/31/2008 |
MadMACs seems to have an issue with the Intel Wireless WiFi Link 4965AGN
chipset
I've added the following note to the MadMACs page: A patron of my website
pointed out that MadMACs, and other similar tools, seem to have a problem
randomizing the MAC address under Windows Vista if you are using the Intel
Wireless WiFi Link 4965AGN chipset. It will work with the 4965AGN if you
randomize only the last two digits, and start it with the prefix 1234567890. It
will also let you set the whole MAC address to DEADBEEFCAFE, or even let you
randomize all 12 hex digits. However, if you take the default prefix of 00,
MadMACs will make a random address up and put it in the NetworkAddress registry
value, but the 4965AGN chipset drivers will not honor it. If anyone knows why,
please contact me. |
| 08/28/2008 |
Nmap presentation and class in Louisville area
Hi all, my GRE test went well and I'm back to working on the site. I've been
invited by the Kentuckiana ISSA
chapter to give a presentation on
Nmap and its use.
The event happens Sept 5, 11:30AM at the following location:
Innovative Productivity / McConnell Technology
401 Industry Rd, Louisville, KY 40208
The ISSA would like to have an RSVP. Also, I'll be giving a longer hands on
demonstration and lab later on in September where people can bring their own
laptops and use a private network to get some hands on experience with Nmap. We
are not sure of all of the details yet, but it will likely be held Sept 20th at
the Ivy Tech campus in Sellersburg, IN.Also, this month's Louisville 2600 meeting is coming up on Thursday, Sept
24th. More details can be found here:
http://louisville2600.org/ |
| 08/07/2008 |
MadMACs Ver. 1.2: Update to my MAC address and host name changer /
randomizer / spoofer
Qwasty let me know that if
host name randomization is used with MacMACs, and the host name is over 15
characters (or has certain bad illegal characters) it can cause all sorts of
lsass.exe errors on boot up. To fix this, I've updated the code to do some
sanity checks on the possible hostnames given to it in dic.txt. Hopefully
this fixes the problem. I also compiled it with the newer
Autoit3 v3.2.12.1. |
| 08/04/2008 |
Cain RDP (Remote Desktop Protocol) Sniffing Log Parser
This is a quick script I wrote to easy the process of interpreting the logs
that Cain makes when you do a man in the middle against the RDP protocol. I
hope to use it in a video tutorial shortly. My GRE studies are still
ongoing, so please excuse the lack of updates to this site. As a side note,
the Louisville 2600 group now has
it's own site, and the ISSA
Kentuckiana chapter's site is back up. |
| 07/23/2008 |
Baby Bubba Finds A New Mummy: A
Zombie Children's Book
Ok, this one is not security related, but those of you who know me know I
have a thing for zombie movies. See my
LAN Of
The Dead article on computer zombies to see what I mean. Pascalle
Ballard and I started to work on our own children's book, with a baby zombie
as the lead character. Follow the link, I hope you will enjoy it. |
| 07/08/2008 |
Small amendment to my Ironkey Review
Marc Luo from Ironkey emailed me his thoughts on my video, so I attached the
text to the end of the page. Marc reveals some of Ironkey's future plans,
why some design decisions were made and what he sees as some of the
advantages of the Ironkey. I hope it clarifies some of the points I made in
the video. |
| 07/08/2008 |
New 2600 Meet in Louisville, KY
Announcing the forming of a new 2600 meeting in the
Louisville, KY, New Albany/Jeffersonville/Clarksville, IN and the
surrounding area. We are looking for old faces and new faces to come and
join us in discussion and hopefully projects in all things hacking. From
computer security, to programming, to penetration testing and exploiting. It
has been far too long since Louisville and its surrounding area have seen a
group of security talent and we want to change that. If you want to be a
regular, have a general interest or just want to converse with fellow
techies please join us for our inaugural meeting.
When: Thursday July 31, 2008 @ 6:30pm
Where: Highland Coffee behind the Blockbuster near Bardstown road and Grindstead in Louisville, KY.
Google Map Link
Contact me if you think
you can attend. |
| 07/07/2008 |
New Video:Ironkey
High Security Flash Drive: Use and Review
The Ironkey is a high security thumb drive designed to provide strong AES
encryption, tamper resistance and other security services. I'd seen the Ironkey
advertised quite a bit, and even read about its crypto systems and ruggedness,
but was left wondering about how it works in operation. Since the hardcore tech
side has been covered elsewhere, I'll concentrate on the Ironkey's usability and
features. Some of the topics covered will include: How is the drive mounted
without admin privileges in Windows? How is it mounted in Linux? How does the
"Self Destruct" feature work? What is Secure Sessions? How is the Ironkey better
than just using Truecrypt? I made this video to answer those sorts of questions
for myself and others. If you want more details on the crypto involved, see the
links section at the end of this video. The model I will be working with is the
1GB Ironkey Personal. I'll show its use and give my opinions on the device.By
the way, you may notice that I'm making fewer posts over the next month or so.
I'll be busy studying for the GRE, wish me luck. |
| 07/04/2008 |
Web Bug Article
Updated With PHP/MySQL Source Code
I've updated my very old article on
web bugs/web
beacons to straighten out some bad formatting and to add an example of a web
bug that uses PHP and MySQL. For those that don't know, Web Bugs are images
(Gifs, Jpegs, PNGs, etc.) that companies and organizations put into web pages,
e-mails and other HTML supporting documents to track information about the
viewer. These images are sometime know by other names such as tracking bugs,
pixel tags, web beacons or clear gifs. What ever the name, their function is
largely the same. |
| 07/04/2008 |
Dreamhost Review
Updated
It came to my attention that my Dreamhost review was a bit dated and had wrong
information based on changes that Dreamhost has made over the last year. I've
updated it to reflect some of Dreamhost's new polices, my experiences and how the
discount codes differ from when I last updated it (1/31/2007). I've also have
five limited discount codes to give away that grant the following: 2TB disk and
20TB bandwidth, gives $150 off a 5-year signup or $200 off a 10-year signup.
Contact me if you want
one of my five one time use codes. |
| 06/26/2008 |
New Video:Setting
up a Tarpit (Teergrube) to slow worms and network scanners using LaBrea (The
"Sticky" Honeypot and IDS)
A network Tarpit, sometimes know by the German word Teergrube, is a service or
set of hosts that deliberately try to slow malicious network connections down to
a crawl. The idea is to put up unused hosts or services on the network that
respond to an attacker, but do things to waste their time and greatly slow their
scanning (or spreading in the case of Worms). For this video I'll be using a
package called LaBrea by Tom Liston and tarpitting unused IP addresses on my
home LAN.
Also,
DecaffeinatID Intrusion Detection System ver. 0.07 is out. |
| 06/24/2008 |
Ironkey
at the Kentuckiana ISSA meeting on June 27th 2008
Steve Tonkovich from Ironkey will be
giving a talk at the ISSA-Kentuckiana Chapter Meeting on Friday June 27, from
11:30 am to 1:00 pm. Ironkey's discussion will be on securing mobile data. The
meeting will be held at their new location:
Innovative Productivity / McConnell Technology
Hopefully I can convince Steve to give me a demo unit of the Ironkey thumb drive
to test for a review on my website.
As a side note,
DecaffeinatID ver. 0.06 is out. |
| 06/23/2008 |
DecaffeinatID Updated to ver. 0.05
Several major improvements have been implemented. The various monitoring
functions are now set off via a timer. This allows the event loop to be looser,
the GUI more responsive and DecaffeinatID to be less of a hog on the CPU. This
caused a change in the way that the sleep parameter in the INI file is
interpreted. Now the sleep parameter specifies the amount of time in
milliseconds between each monitor function (ARP cache, Firewall and Event Log).
For example, with the new default of "sleep=1000", DecaffeinatID waits about one
second between each monitor function, so to go through one cycle takes about
three second with the default setting (I've taken it down to "sleep=100"
without major problems). The only downside to this is that some alerts may be
skipped if several happen at nearly the same time, but since DecaffeinatID's
main function is just to alert you of network shenanigans this is a worthwhile
compromise (when DecaffeinatID warns you about something, you really should
check your logs for more details anyway). I've also fixed a problem with ARP
cache parsing that was caused by the word "invalid" in the output of the "arp
-a" command. |
| 06/22/2008 |
New Video:Compiling
and Configuring DHCPD from Source
Devil2005 has created a video on compiling and configuring dhcpd from source.
He's using the Fedora 9 distro of Linux for the video, but the lessons learned
should be applicable to other distros. For that matter, even if you are not
interested in installing dhcp in this way it's still a good lesson on how to
download and compile various applications from source. |
| 06/21/2008 |
Doktor
Kaboom's Smoke Ring Cannon
Even though this is not computer security related, it was such a cool display I
had to share it with my hacker buddies. I guess you could call it hardware
hacking of sorts, with cool science principles. Make sure you re-watch the first
few seconds a couple of times to get the full effect. I saw Doktor Kaboom's
Smoke Ring Cannon at this years Kentucky Renaissance Faire. Now it's time to
make one of these things for myself. Check out Doktor Kaboom's site at:
http://www.doktorkaboom.com/ |
| 06/20/2008 |
DecaffeinatID: Simple IDS/ ARPWatch For Windows Updated
Jabzor
was the first major contributor to the project. He did
some major rewriting, making a better GUI, making my code
prettier/easier to maintain and laying out the INI file better. I made
further changes to Jabzor's GUI and made the ARP Watching function a little more
efficient (Still needs much work). |
| 06/19/2008 |
DecaffeinatID: A Very Simple IDS / Log Watching App / ARPWatch For Windows
DecaffeinatID started because I wanted a simple ARP Watch like application for
Windows. In a short matter of time, feature creep set in. DecaffeinatID is a
simple little app that acts as an Intrusion Detection System (more of a log
watcher really) to notify the user whenever fellow users at their local WiFi
hotspot/ LAN are up to the kind of "reindeer games" that often happen at coffee
shops and hacker cons. |
| 06/11/2008 |
PEBKAC Attack Script: Finding passwords in event logs
Ever wanted to quickly search a Windows Event Log to find passwords users
inadvertently typed into the user name field? Well, this script should make it
easy to do such audits. Read the rest of the article for details. Also, if you
are interested in using BackTrack for pen-testing, check out my friend
Lee Baird's collection of videos
and documentation on BackTrack and other hacking topics. |
| 06/09/2008 |
New Video:Using
Data
Execution Prevention (DEP) in Windows XP and Vista: Fighting back against buffer
overflows and memory corruption
I've recently become interested in measures that modern CPUs can take to
prevent various types of memory corruption attacks. One such feature is the NX
bit (as AMD calls it, XD is Intel's term), which allows for memory pages to me
marked as not executable. Microsoft Windows started using this ability with XP
SP2 as part of their Data Execution Prevention (DEP) feature. Unfortunately, to
get most out of DEP you have to configure it. This video will show how to
configure DEP protection in Windows XP and Vista. |
| 06/07/2008 |
New Video:
DNS Spoofing with Ettercap
In my previous two videos I showed how to use Ettercap plugins for various
pen-testing and security evaluation functions. In this video I'll show how to
use the Ettercap plugin dns_spoof to set up DNS spoofing on the local area
network.
|
| 06/04/2008 |
A Review of
"Building Secure Products and Solutions"
This is a little article I wrote for the Operations Management class I'm in.
Most Irongeek readers may not be interested in it, but I wrote it so I might as
well post it.
|
| 05/29/2008 |
New Video:
More Useful Ettercap Plugins For Pen-testing
In my previous video I showed how to use Ettercap plugins to find sniffers on
the network. In this video I'll show three more useful Ettercap plugins: find_ip,
gw_discover and isolate. |
| 05/26/2008 |
How To Cyber Stalk Potential Employers Article Updated
I updated the "Social Networking Sites" section with information about
RapLeaf. I also updated the "Mail Headers"
section with information on the *nix command line whois and Nirsoft's Windows
tools IPNetInfo and
WhoIsThisDomain. |
| 05/24/2008 |
Fed Watch
I was curious to see what government agencies might me using my site for
training. I also wanted to learn PHP + MySQL a little better, so I wrote this
project. It takes my logs and shows all of the hosts names ending in .mil or .gov,
and what pages they visited. I obfuscated the first part of the host names, and
the last two octets of the IPs so as to not "drop their docs" so to speak. |
| 05/20/2008 |
Detecting Sniffers Video Updated
PurpleJesus
from Binrev informed me that my last video was having weird audio issues with
some versions of the Flash plugin. I did some Flash-VooDoo and it seems to be ok
now. Let me know if there are any problems. |
| 05/20/2008 |
New Video:Finding
Promiscuous Sniffers and ARP Poisoners on your Network with Ettercap
Most of you are familiar with using Ettercap for attacking systems, but what
about using it to find attackers? This tutorial will cover using Ettercap to
find people sniffing on your network. The plug-ins we will be using are
search_promisc, arp_cop and scan_poisoner. |
| 05/19/2008 |
BackTrack Beta 3
Man Pages
I've decide to covert the man pages that come with the BackTrack Beta 3 Live CD
to HTML and post them to my site. I've just done the ones in /usr/local/man, so
expect a few bad links. This will make it easier for me to link to the man pages
from my other videos and articles. Tools include in the list are:
aircrack-ng,
airdecap-ng,
airdriver-ng,
aireplay-ng,
airmon-ng,
airodump-ng,
airolib-ng,
airpwn,
airsev-ng,
airsnort,
airtun-ng,
amap,
ascii-xfr,
atftp,
bison,
bsqldb,
buddy-ng,
cabextract,
catdoc,
catppt,
datacopy,
dcfldd,
decrypt,
defncopy,
dhcpdump,
dmitry,
dos2unix,
dupemap,
easside-ng,
etherape,
flex,
foremost,
freebcp,
gencases,
getattach.pl,
hexedit,
httpcapture,
ike-scan,
ivstools,
kstats,
mac2unix,
macchanger,
magicrescue,
magicsort,
makeivs-ng,
mboxgrep,
minicom,
nemesis-arp,
nemesis-dns,
nemesis-ethernet,
nemesis-icmp,
nemesis-igmp,
nemesis-ip,
nemesis-ospf,
nemesis-rip,
nemesis-tcp,
nemesis-udp,
nemesis,
netcat,
nmap,
nmapfe,
obexftp,
obexftpd,
p0f,
packetforge-ng,
psk-crack,
rain,
runscript,
scrollkeeper-config,
scrollkeeper-gen-seriesid,
sipsak,
socat,
tcptraceroute,
truecrypt,
tsql,
unicornscan,
vomit,
wesside-ng,
wordview,
xls2csv,
xminicom,
xnmap, gdbm,
etter.conf,
scrollkeeper.conf,
sudoers,
scrollkeeper, 80211debug,
80211stats,
arpspoof,
atftpd,
athchans,
athctrl,
athdebug,
athkey,
athstats,
ath_info,
dnsspoof,
dnstracer,
dsniff,
ettercap,
ettercap_curses,
ettercap_plugins,
etterfilter,
etterlog,
filesnarf,
fping,
fragroute,
fragtest,
hping2,
hping3,
in.tftpd,
macof,
mailsnarf,
msgsnarf,
netdiscover,
packit,
scrollkeeper-preinstall,
scrollkeeper-rebuilddb,
scrollkeeper-update,
sing,
sshmitm,
sshow,
sudo,
sudoedit,
tcpick,
tcpick_italian,
tcpkill,
tcpnice,
tinyproxy,
urlsnarf,
visudo,
webmitm,
webspy,
wlanconfig
Enjoy. |
| 05/14/2008 |
Physical Security, Locking Picking,
and more: Bloomington Fraternal Order Of LockSport
Normally I cover electronic security, but as we all know if someone has physical
access to your box they OWN your box. One reason to look into high security
locks and lock bypassing is to increase the physical security of your assets my
knowing what works and what doesn't. My friend
DOSMan gave a presentation recently at
Notacon 5 called Lock
Picking in the New Frontier - From Mechanical to Electrical Locks you should
check out if you are interested in physical security. Also check out the
Bloomington FOOL organization if
you are interested in Locksport in general. |
| 05/10/2008 |
New Video:
A Brief
Intro To Cryptographic Hashes/MD5
A cryptographic hash function takes an input and returns a fixed size string
that corresponds to it, called a hash. Cryptographic hashes have a lot of uses,
some of which are: detecting data changes, storing or generating passwords,
making unique keys in databases and ensuring message integrity. This video will
mostly cover detecting file changes, but I hope it gets your mind going in the
right direction for how hashes can be used. Specifically covered will be tools
for creating MD5 hashes in Windows and Linux. |
| 05/04/2008 |
Irongeek In Print: Books that
mention Irongeek.com
I did some looking around and it seems my site is mentioned in a few books. I've
decided so start this page to keep track of book references to Irongeek.com. If
I'm missing any please let me know, I found these first few via Google Books. |
| 04/30/2008 |
I've updated my
A
Quick Intro To Sniffers article to fix a stupid error I made where I
mistyped 801.11 instead of 802.11. |
| 04/24/2008 |
New Video:Text
to Speech to MP3 with the freeware program DSpeech
This video is on Dspeech, a freeware tool that uses Microsoft's SAPI (Speech
Application Programming Interface) to convert text to spoken word. What's
special about it is it lets you make an MP3 of the text, so you can listen to it
on your computer, in you car or on your MP3 player. It's great for listening to
study notes.
As an unrelated side note, a friend of mine want's me to mention his
humor page on celebrities, politics and gadgets.
Hope you enjoy it. |
| 04/18/2008 |
IGiGLE: Irongeek's WiGLE WiFi Database to Google Earth Client for Wardrive Mapping
Updated
IGiGLE is a little app I wrote that lets you directly import data from the online WiGLE WiFi Wardrive database into a KML
file, then view it in Google Earth. I've made sure it works with the
newest version of Google Earth 4.3, and recompiled it with the newest stable
version of Autoit. If you want more details on how to use it, check out my video
Wardrive Mapping With IGiGLE And WiGLE. |
| 04/10/2008 |
Getting Ubuntu Linux to connect to a PPTP Cisco VPN 3000 Concentrator
Just a quick notes page to help others that have the same problems I did. By the
way, I plan to be at Conglomeration
April 18th-20th. While it's not a Hacker/Security con, it's still a fun little
Sci-Fi/Fantasy convention with plenty of geeky types running around. Let me know
if you're a reader of Irongeek.com and plan to be there. |
| 04/06/2008 |
Irongeek's Infosec Wargame Servers
Explained
I updated my post to explain that it was an April 1st joke, and link off to real
ways to test your computer security skills. By the way, did anyone decode the QR
Code I posted? |
| 04/01/2008 |
Irongeek's Infosec Wargame Servers
I'd like to announce the
launch of my
own wargame servers for testing out your computer security skills. The host
names are:
hackme1.irongeek.com
hackme2.irongeek.com
dosme1.irongeek.com
Try out Nmap,
Nessus,
Metasploit and other tools on these boxes. Please let me
know your findings. Thanks to my hosting provider Dreamhost. If you want to know
more about
Dreamhost check out my review (and coupon codes), they have been pretty
good to me.
 |
| 03/18/2008 |
New Video:Hardware
Keyloggers In Action 2: The KeyLlama 2GB USB Keylogger
This video will demonstrate one of the
KeyLlama brand of hardware keyloggers in action, specifically the 2GB
USB model. I know some of you are getting sick of me talking about hardware
keyloggers, so I plan on this being my last entry on them for awhile. |
| 03/14/2008 |
I've updated the
Irongeek Campuses page with a few new schools, please contact me if your
university uses my materials for teaching information security. Also, I've
started to help out the
The Mitzvah Group with their charity work. Check out and join their
Myspace page, especially if you live in the Southern Indiana/Louisville
Kentucky area. |
| 03/05/2008 |
Ghost 11 Plugin
for Bart's PE Builder (BartPE)
I took the on Ghost 8 plugin and modified it a bit to work with Ghost 11. |
| 03/04/2008 |
Hardware Key Logging Part 3: A Review Of The KeyLlama USB and PS/2 Keyloggers
This article is about the
KeyLlama brand of hardware keylogger, specifically the 2MB PS/2 model
and the 2GB USB model. |
| 02/20/2008 |
Update:I made a small note at the
top of my recent "Encrypting The Windows System Partition With Truecrypt 5.0"
video. I used
Photorec to do some file carving to see how secure Truecrypt's Windows
system partition encryption was. Photorec was only able to recover two files,
one ASP/TXT file and one PCX, but on closer examination both were false
positives. They just contained seemingly random data, which Photorec mistook as
real file headers. Truecrypt seems to do a very good job of securing the data on
your system drive. As a side note, if anyone else is using LinkedIn please
feel free to add me and give
me a recommendation for the work I've done on this site. Who knows, it may
help me find a good career opportunity in my area. |
| 02/11/2008 |
New Video:
Encrypting The Windows System Partition With Truecrypt 5.0
Truecrypt 5.0 adds many new features, most importantly Windows system partition
encryption. To put it in slightly inaccurate layman's terms, this means
encrypting your entire C: drive. Even if you already write your sensitive data
to an encrypted space, files are sometimes squirreled away in unencrypted temp
space or in the page file where they may be recovered. Using Truecrypt to
encrypt your Windows XP system partition will help eliminate this problem. |
| 02/05/2008 |
New Video:Hardware
Keyloggers In Action 1: The KeyLlama 2MB PS/2 Keylogger
This video will demonstrate one of the
KeyLlama brand of hardware keyloggers in action, specifically the 2MB PS/2 model. I hope this video will give the viewer a better grasp of how these hardware keyloggers work. |
| 01/28/2008 |
New Video:Encrypting
VoIP Traffic With Zfone To Protect Against Wiretapping
Some people worry about the easy with which their voice communications may be
spied upon. Laws like CALEA have made this simpler in some ways, and with
roaming wiretaps even those not under direct investigation may lose their
privacy. Phil Zimmermann , creator of PGP, has come up with a project called
Zfone which aims to do for VoIP what PGP did for email. Thanks to
DOSMan for his help with this video. |
| 01/16/2008 |
Hacking and Pen-Testing With The Nokia 770/800/810 Notes Updated
I've updated my notes with a little more info on the n810 and links to new
repositories (thanks to Andrew Lemay.) |
| 01/14/2008 |
New Video:Using GPG/PGP/FireGPG to Encrypt and Sign Email from Gmail
This tutorial will show how to use GPG and the FireGPG plug-in to encrypt and
decrypt messages in Gmail. GPG is an open source implementation of OpenPGP
(Pretty Good Privacy) , a public-key-encryption system. With public key
encryption you don't have to give away the secret key that decrypts data for
people to be able to send you messages. All senders need is the public key which
can only be used to encrypt, this way the secret key never has to be sent across
unsecured channels.
|
| 01/12/2008 |
Nuclear
War Survival Myths
I did not write this
article, and while it's not about computer security it is about security. My
interest in this subject was renewed after watching the TV series
Jericho
(watch it so it stays on the air). I thought this article was interesting enough
to warrant mirroring, and it seems to jive pretty well with what I have read
from other authors such as Duncan Long and Cresson H. Kearny on the subject.
Please don't think I'm a paranoid, tin-foil-hat wearing freak, but I am a child
of the 80's and a fan of post-apocalyptic fiction. Don't worry, my video on PGP/GPG
is on its way. |
| 01/07/2008 |
Personal Privacy Programs
Hi all. I've decided it's time to start focusing on software that helps users
maintain their privacy. I've already done videos on
DBAN,
Eraser,
CCleaner,
TrueCRYPT and Tor.
I hope to have one on PGP/GPG/FireGPG up soon. What other must have privacy
software do you recommend I cover? Let me know via my
contact page, to which
I've recently added my OpenPGP key. |
| 12/29/2007 |
Tennessee, Texas, Utah, Vermont, Virginia, Washington, West Virginia, Wisconsin
and Wyoming added to the state hacking laws page
That should be all 50 states, now I may add some federal stuff. |
| 12/26/2007 |
New Mexico, New York, North Carolina, North Dakota, Ohio, Oklahoma, Oregon,
Pennsylvania, Rhode Island, South Carolina and South Dakota added to the state
hacking laws page
More to come. |
| 12/25/2007 |
Massachusetts, Michigan, Minnesota, Mississippi, Missouri, Montana, Nebraska,
Nevada, New Hampshire and New Jersey added to the state hacking laws page
Happy Christmas. |
| 12/24/2007 |
Iowa,
Kansas, Louisiana, Maine and Maryland added to the state hacking laws page |
| 12/23/2007 |
California, Colorado, Connecticut, Delaware, Florida, Georgia, Hawaii, Idaho and
Illinois added to the state hacking laws page
As the link says, I've expanded the page on computer trespass laws. Expect more
tomorrow. |
| 12/23/2007 |
State
Hacking/Computer Security Laws
I thought it would be a cool project to collect all of the state
hacking/computer fraud laws I could find into one collapsible menu system. I
plan to add around 5 states per day until I get them all. If anyone wants to
help with the project drop me a line. So far I've done Alabama, Alaska,
Arizona, Arkansas and my home states of Indiana and Kentucky. |
| 12/18/2007 |
Hi all. Just posting to let you know I'm still around. I've be busy with school,
Christmas and other personal matters. I did not want anyone to think the site
was no longer active. It may be 2008 before the next update, but it's still an
active project of mine. |
| 11/13/2007 |
New Video:
WebGoat 1: SQL Injection Demonstration
SQL injection is a common web application attack that focuses on the database
backend. WebGoat is a deliberately insecure J2EE web application maintained by
OWASP designed to teach web application security lessons. I plan to use WebGoat
for a few future videos. This first WebGoat video will show the basics of
installing WebGoat and doing two of its SQL injection lessons. |
| 10/25/2007 |
New Video:
XAMPP: an easy to install Apache daemon containing MySQL, PHP and Perl By
devil2005 |
| 10/23/2007 |
Louisville InfoSec Conference Write-up
Just a quick write-up of my experiences at the event. |
| 10/22/2007 |
New Video:RFID
Show and Tell with Kn1ghtl0rd and lowtek mystik
While at PhreakNIC I got a chance to interview
Kn1ghtl0rd and lowtek mystik about their research into RFID, its hackabilty and
other information. |
| 10/21/2007 |
Well, I'm home from the Louisville InfoSec and PhreakNIC conferences, and
there's two cool projects I want to tell you about. The first is
WebGoat,
a deliberately insecure J2EE web application maintained by OWASP designed to
teach web application security lessons. The other is
De-Ice, a series of live CDs for presenting
pen-testing scenarios. Each CD has a scenario you have to pen-test against, so
you learn the process and not just the tools. I plan to do videos soon on each
project. Thanks to all of my fans who encouraged me at the con, too bad none of
you were female. :) |
| 10/17/2007 |
New Script:
Thumbscrew: Software USB Write Blocker
Thumbscrew is my attempt at a poor man's USB write blocker. When used it allows you to quickly enable or disable
writing to all USB mass storage devices on your Windows system. It may be of use
to some of you who are studying forensics. |
| 10/16/2007 |
New Script:
Thumb Sucking: Automatically copying data off of USB flash drives
Just a quick script I wrote for pen-testing. Think of it as the reverse of
Dosk3n's tutorial. By the way, two days till the
Louisville InfoSec 2007 Conference, and three till
PhreakNIC. |
| 10/15/2007 |
New Video:
Using Metagoofil to extract metadata from public documents found via Google
As many of my viewers know, I have an interest in metadata and how it can be
used in a pen-test. Thanks to PaulDotCom I found out about a tool called
Metagoofil that makes it easy to search for metadata related to a domain name. |
| 10/12/2007 |
New Video:Creating
An Auto Hack USB Drive Using Autorun and Batch Files. By Dosk3n
Dosk3n was kind enough to send me the video, text an narration for a new infosec
video. All I had to do was plug it into my template. If anyone else wants to
submit a video, read my page on
How I Make
The Hacking Illustrated Videos. My only stipulations are that it has to be
narrated and can't have copyrighted music in it. I also plan on changing the
InfoSec
videos page around to be easier to search. |
| 10/10/2007 |
Updated Article: What
can you find out from an IP?
I've done a few small updates to the article, see the
change log.
Thanks to PaulDotCom for telling me about "Moan
My IP". I think this FAQ needs some expanding, so if you have any ideas
email me. |
| 10/09/2007 |
New Video:How
To Burn An ISO Image To A Bootable CD
Ok, I know it does not seem a worth topic for the Hacking Illustrated series,
but you have to admit the question gets asked a lot. Now we have something to
point people to when they ask on forums how to burn an ISO using a free
application. Feel free to link to this when the question is asked. |
| 10/06/2007 |
File Systems and thumb drives: Choosing between FAT16, FAT32 and NTFS to get a
faster USB Flash Drive
What file system should you choose to speed up your thumb drive? Read on. |
| 10/04/2007 |
Itinerary For Louisville InfoSec 2007 Conference Posted
The schedule is up for the Metro Louisville InfoSec Conference happening Oct.
18th. If you are a reader of Irongeek.com please come by and say hello, you will
most likely find me sitting in on the technical track presentations. |
| 10/04/2007 |
Irongeek on Campus
It's come to my attention that some Universities and other educational
institutions are using my videos in their InfoSec classes. I think this is
great, but I'd like to
compile a list of such campuses. If your campus uses my videos, please send
me an email with the institutions name and a link to their web site. So far
Jackson Community College
is the only name on the list, but I know there's more to come. |
| 10/01/2007 |
New Video:
Wardrive Mapping With IGiGLE And WiGLE
For those that don't know, WiGLE is an online database of Wireless Access
Points (802.11A/B/G/N) that is contributed to by folks using Netstumbler, Kismet
and other wardriving tools. WiGLE has a web interface of its own, as well as
Java desktop client called JiGLE, but I thought that I should make my own
interface to the data to fit my needs. That's why I wrote a program called
IGiGLE to query WiGLE and turn the data into a KML (Keyhole Markup Language)
file that is easy to import into the Google Earth desktop application. With the
generated KML file and Google Earth it's easy to view and parse the access
points found by you and other WiGLE users. |
| 09/30/2007 |
Hacker Meets Hacker: Irongeek Meets Kane Hodder
Of course, I mean a different kind of hacker. If you don't know who Kane is,
then I guess you won't get the joke.

Check out the inscription:
|
| 09/26/2007 |
New Video:
Nokia 770/800 Pen-Testing Setup (Nmap, Kismet, Dsniff and other fun stuff)
This video introduces the viewer to using a Nokia Internet Tablet as a
pen-testing device. |
| 09/25/2007 |
Metro Louisville InfoSec
2007 Conference
It looks like there's going to be an information security conference in my neck
of the woods next month. The
ISSA-Kentuckiana is holding the Fifth Annual Metro Louisville Information
Security Conference Oct 18th at Churchill Downs. Considering the location, maybe
they should have called it "Hackers and Horses". From the event site:
The ISSA-Kentuckiana board
of directors is proud to announce the 5th Annual Metro Louisville
Information Security Conference. It is a full day event on October 18th,
2007 that will be held at Churchill Downs. Our keynote speaker is Marcus Ranum, a world-renowned expert on security system design and implementation.
In addition to the keynote, multiple technical, business/compliance, and
demonstration-oriented breakout sessions will be held. Up to 6-CPE credits
may be earned by attendance.
I'll be attending, hope to see some of you there. |
| 09/22/2007 |
Hacking and Pen-Testing With The Nokia 770/800 Notes
I've put up the first draft of my Nokia 770/800 notes. Hope you enjoy it. |
| 09/21/2007 |
My buddies Kn1ghtl0rd and lowtek mystik will be doing a presentation at this
years PhreakNIC about RFID. From the
presentations page:
Last year's presentation was high level functionality and basic knowledge
of what RFID is. The year they will present the low level technical specs on
different communication types, the physics behind RFID reading and
transmitting, and the actual circuitry of an RFID tag and what it takes to
make them operate more consistently. The presentation will also cover actual
tag data and coding schemes with standardization including EPC Gen 2 and
other ISO standards such as PayPass RFID enabled credit cards. There will be
reader/writer demonstrations as well as other proof of concept
demonstrations.
Watch last years presentation |
| 09/20/2007 |
New Video:
Forensic Metadata in Word Docs and Jpegs supporting Exif
Metadata is data about data. Different file formats store extra data about
themselves in different ways. This video will cover metadata that can be used
during a forensic investigation, namely MS Word doc metadata and the metadata
stored in a Jpeg's Exif data. Also, if you are an educational institution that
uses my videos in class, please let me know so I can add you to the
Irongeek Campuses page. |
| 09/12/2007 |
WinZombies: Desktop of the Living Dead
This is a little project I've been working on. It draws zombies that crawl
around your desktop and interact with the windows. It's based on WinPenguins by
Michael Vines (who did all of the hard work), with sprites from MSlugDB. I hope
you find it to be a fun desktop toy. |
| 09/10/2007 |
WinPenguins
Modified for Visual Studio 2005
A cute little desktop toy, slightly updated. |
| 09/01/2007 |
IGiGLE: Irongeek's WiGLE WiFi Database to Google Earth Client for Wardrive Mapping
Updated
IGiGLE is a little app I wrote that lets you directly import data from the online WiGLE WiFi Wardrive database into a KML file, then view it in Google Earth.
Jim Forster emailed me to let me know that "Query by ZIP" was not working, it
seems WiGLE changed their API on me. I've fixed it by using the US Census site
to get the LAT/LONG by querying the ZIP. Let me know if there are any problems. |
| 08/28/2007 |
My New Horror Blog
Sorry that it's been awhile since I've posted, I've been up to other things. If
you've read my
LAN Of The
Dead article on computer zombies, you know I dig horror movies. One new
project of mine, unrelated to security, is a
horror blog. It's mostly a blog
aggregator for now, but I do plan to post my own reviews there as well. This
should give me a chance to play around with Wordpress, its plugins and RSS/Atom
feeds. Don't worry, more security videos and articles are to come. |
| 08/08/2007 |
New Video:
Remote Password Auditing Using THC-Hydra: Or, why brute force/dictionary attacks
don't work (often). |
| 07/30/2007 |
I've updated my
A
Quick Intro To Sniffers article to flesh it out, fix a few links (Ethereal
to Wireshark) and of few other tweaks such as links to my videos. Let me know
what else you think I should add. |
| 07/25/2007 |
Using Darik's Boot and Nuke (DBAN) to totally wipe a drive
Another continuation of my
file carving video and
selective file shredding (DOD 5220.22-M) to thwart forensics tools video,
this video shows how to use Darik's Boot and Nuke (DBAN) to totally wipe a drive.
DBAN is a great tool to add to your anti-forensics tool box |
| 07/12/2007 |
New Video: Selective file shredding (DOD 5220.22-M) with Eraser and CCleaner to thwart forensics tools
A continuation of my
file carving video, this video shows how to use Eraser and CCleaner to help
thwart forensics tools. |
| 07/04/2007 |
How To Cyberstalk Potential Employers
This article is not nearly as deviant as it sounds. It gives basic tips on how
to research an employer passively using social networks, DNS information, e-mail
headers and other tactics before an interview. |
| 07/02/2007 |
IGiGLE WiGLE to Google Earth Wardrive Mapping App Updated
I've updated my IGiGLE app so you can filter by the date that the WiFi access
points were found. I figured this was needed since a lot of the data in WiGLE
goes back a few years. This should make it easy to expunge old, no longer
existing WAPs from your maps. |
| 06/26/2007 |
New Video:
Setting
up a simple web proxy with CGIProxy
A quick guide to setting up James Marshall's CGIProxy Perl script and how
proxies are used to get around web content restrictions and stay anonymous. This
video also shows how to quickly find an open CGI proxy with a search engine. |
| 06/13/2007 |
New Video:
Data Carving with PhotoRec to retrieve deleted files from formatted drives for
forensics and disaster recovery
This video introduces the concept of data carving/file carving for recovering
deleted files, even after a drive has been formatted. |
| 06/11/2007 |
New Video:
Using Cain and the AirPcap USB adapter to crack WPA/WPA2
A follow up to the previous video, this one of course covers auditing the
security of a WPA protected WiFi network. |
| 06/06/2007 |
New Video:
Intro to the AirPcap USB adapter, Wireshark, and using Cain to crack WEP
This video introduces the viewer to the AirPcap USB adapter, and auditing WiFi
networks with it. |
| 06/04/2007 |
How I Make The
Hacking Illustrated Videos
Some people have contacted me about hosting their videos. I've updated my page
on how I create my "Hacking Illustrated" videos so the people have a better idea
how it's done. If you would like to submit a video please
contact me. You will of
course get full credit for your work an link off to your personal site. It might
be a good way to throw some traffic at your own InfoSec page. |
| 05/30/2007 |
UPnP Port Forwarding and Security
This video introduces the viewer to port forwarding with Universal Plug In Play,
and some of the associated security problems. |
| 05/23/2007 |
New Article:
Building an InfoSec lab, on the cheap |
| 05/21/2007 |
I've updated my Links
section, and have added two new sections:
Hire Me and Advertise
on Irongeek.com. |
| 05/17/2007 |
I updated my
review of the UT-41 GPS with some information from Jaku about getting it to
work in Mac OS X. |
| 05/15/2007 |
Mineral Oil Submerged
Computer aka "The 1337 Fleet"
My friend Glj12 wrote an article on cooling a computer in mineral oil. Go check
it out if you are into overclocking. |
| 05/03/2007 |
Video: Notacon
2007
Just some video I took while at Notacon 2007. Plenty of stuff for those with an
interest in hacking and digital arts. Radar, full motion video on an 8088, a
great Bluetooth discussion, shock sites, stun guns, Everclear, IPTV show hosts,
Demoparty/Demoscene, hacker condoms, Ethernet alternatives, fire staffs, laser
data links and more. |
| 04/26/2007 |
"Hardware
Key Logging Part 2:A Review Of Products From KeeLog and KeyGhost" is up. If
you see me at Notacon this weekend ask about them, I should have the keyloggers
with me and I plan to demonstrate them in one of the exhibit rooms. |
| 04/10/2007 |
I've updated the Wall of Social Science Majors Page.
It now has a link to my Slax based Live CD from which you can run the password logging wall. Thanks to Droops for introducing me to Slax. If you are at Notacon 4 you will hopefully see this code in action.
|
| 03/27/2007 |
About a month from now Notacon 4 will be
happening in Cleveland, OH, April 27th-29th. I'll be attending along with my
friends from The Packetsniffers and
Infonomicon.

I hope that some of you will be able to make it as well. It's a fun little
hacker/digital arts convention. We had a great time last year, and intend to do
the same this year. |
| 03/26/2007 |
I have a new article out titled "Hardware
Key Logging Part 1: An Overview Of USB Hardware Keyloggers, And A Review Of The
KeyCarbon USB Home Mini". I cover when and where a hardware keylogger maybe
be appropriate, along with ways it could be detected and defeated. This
installment also reviews the KeyCarbon unit from BitForensics, future articles
will cover the KeeLog and KeyGhost products. |
| 03/20/2007 |
ALT+NUMPAD ASCII Key Combos: The α and Ω of Creating Obscure Passwords
I've been "character encoding hell" just trying to get this article up. I doubt
even the title will render right in all of the RSS feeds/pages. Enjoy. |
| 03/19/2007 |
Updated Article:Fun with
Ettercap Filters
Jon.dmml emailed me to let me know about a technique Kev mentioned on the Ettercap forums. After implementing it, my web page image replacement filter works A LOT better. Try it out and have fun, but please be polite. |
| 03/18/2007 |
New Video:Remote
Access And Configuration: Setting Up SSH and VNC On Ubuntu Linux (SOHO Server
Series 3) |
| 03/16/2007 |
New Video:WEP
Cracking with VMplayer, BackTrack, Aircrack and the DLink DWL-G122 USB Adapter
This one is by Glj12, with a little intro by me. If you are wondering when I'm
going to have some more solo project out, the answer is soon. I've got a USB
hardware key logger review coming soon, and I'm working on a Live CD to run my "Wall
Of Social Science Majors" from for the next
Notacon. Hope to see some of you there,
feel free to buy me an energy drink. |
| 03/12/2007 |
Glj12 from Leetupload.com has released
his
tutorial on using BackTrack 2 to crack WEP. Enjoy. |
| 03/10/2007 |
As a lot of you know, BackTrack 2 final came out a few days ago. For those wanting to run it in VMWare Player, but are too lazy to configure your own VMX, you can download my BackTrack2Final.vmx . Just put it in the same directory as bt2final.iso and open it up in your VMWare Player/Server/Workstation software. |
| 03/10/2007 |
Announcing: http://www.leetupload.com/
Ever go searching for a security tool, only to find that the web page of its
creator no longer exists? Or maybe your looking for an old pen-testing app that
was free at one time, but has since gone closed sourced and the older, free
version with all of the features has disappeared. That's where
glj12's
LeetUpload comes in. Search around for
apps you can't find, or upload rare tools you have and make the collection
better. |
| 03/08/2007 |
An Introduction to Tor : This video serves
as a brief introduction to the use of the Tor anonymizing network in Windows. |
| 03/05/2007 |
I've made
a single page with links to all of my tutorials on SAM/SYSKEY Cracking,
visit it if you want more information on this topic. Now I hope not to get as
many question on it. |
| 02/28/2007 |
IGiGLE: Irongeek's WiGLE WiFi Database to Google Earth Client for Wardrive Mapping
A little app I wrote that lets you directly import data from the online WiGLE WiFi Wardrive database into a KML file, then view it in Google Earth.
|
| 02/25/2007 |
It seems that Mao has followed suit, as of
Cain & Abel v4.5 he has added Windows
Vista compatibility in NTLM Hashes Dumper, LSA Hashes Dumper and Syskey Dumper
for hive files. I updated my
Vista Password Cracking Tutorial
to reflect this. |
| 02/21/2007 |
New Video:
Cracking Windows Vista Passwords With Ophcrack And Cain
This time, using all free tools. |
| 02/19/2007 |
Cedric from the Ophcrack project emailed me to let me know that starting with
version 2.3.4, Ophcrack now supports Windows Vista. Download Ophcrack from
http://ophcrack.sourceforge.net/
if you want a free tool for SAM cracking. I updated my
Vista Password Cracking Tutorial
to reflect this. I hope to but up a video of it soon. |
| 02/19/2007 |
I've made a lot of updates to the site's template. Hope it make the site more
user-friendly. |
| 02/11/2007 |
New Video:Installing
Updates And New Software In Ubuntu Linux (SOHO Server Series 2) |
| 02/09/2007 |
Kn1ghtl0rd from Infonomicon.org has started
a grid computing project to crack MD5 hashes. He's using the Alchemi
distributed client and will be giving a talk about it at
Notacon 2007. If you want to help Kn1ghtl0rd
out with some spare CPU cycles, or would like to try it with your own MD5 hash
go to
http://www.infonomicon.org/grid/ and read the details. |
| 02/06/2007 |
I've updated the Network Printer Hacking article once again, this time with more
info on the fix for the
Pharos cached print job vulnerability. |
| 02/05/2007 |
New Video:Installing
Ubuntu Linux (SOHO Server Series 1)
The first part of my setting up a small office/home office server with Linux
series. |
| 01/31/2007 |
After listening to BinRev radio episode 184 I decided to write
a review of my current hosting provider,
DreamHost. It's covers both the good and the bad. Of all of the hosting
providers I've had for Irongeek.com it's been the best, even with some of its
bad points. I've also made a discount code for anyone who wants to use it:
IRONGEEKCODE
It's gives between $40 and $80 off (and I get a small cut to support the site :)
). |
| 01/20/2007 |
I've updated the
Printer DoSing
section with information on the fix HP has released for the exploit I
mentioned on 01/06/2007. |
| 01/14/2007 |
New Video: Using SysInternals' Process
Monitor to Analyze Apps and Malware |
| 01/06/2007 |
I've updated the
Printer DoSing
section of my Network Printer Security article with information on the Joxean Koret
attack. I've got to thank the
Pauldotcom pod cast
(episode 55) for pointing this flaw out to me. |
| 01/03/2007 |
Dirk Loss sent me a patch for the
Bart PE
Cain plugin that
will make it work with Cain 4.2. Also, check out Dirk's list of apps that
can be ran from a CD or USB drive without installing them:
http://www.dirk-loss.de/win-tools.htm |
| 12/27/2006 |
I did an update to my
MAC address
spoofing article. |
| 12/20/2006 |
An interstitial ad running on my site for IOSCO (oicu-IOSCO.com)
seems to be causing the web browser to ask to download a file from lawcons.info
called c.wmf that contains malware. I fear this is trying to use the previously
know Windows WMF vulnerabilities. I've contacted Adbrite to get the ad campaign
paused. Just wanted to let you know that this malware is not from my site. My
guess is someone defaced the "International Organization of Securities
Commissions" website and inserted the malware. |
| 12/12/2006 |
I've updated
MadMACs to give it beAn
interstitial ad running on my site for IOSCO (oicu-IOSCO.com) seems to be
causing the browser to ask to download a file from lawcons.info called c.wmf
that contains malware. I fear this is trying to use the previously know Windows
WMF vulnerabilities. I've contacted Adbrite to get the ad campaign paused.tter
Windows Vista support. |
| 12/10/2006 |
MadMACs: MAC Address
Spoofing And Host Name Randomizing App For Windows |
| 12/08/2006 |
Posted Glj12's
VBScript
to Randomize Host Name |
| 11/30/2006 |
New Video:
Dual Booting BackTack Linux And BartPE From A Thumbdrive |
| 11/22/2006 |
I've been dragging my feet in getting a new video or article out. In the mean
time, Yugal.ras has sent me a video on Ettercap to share, it can be found at the bottom of my "Videos
By Others" page. |
| 11/11/2006 |
Techcentric Episode 5
Episode 5 of Techcentric has been released. In this episode: "Laptop Painting:
Part 1, Steve reviews some freeware windows apps. Steve shows off a great font
website, Nick builds a drawer in a space drive bay for lugging stuff to and from
lan parties a breeze. A message from our friends at hte crappy asst podcast". I've
got nothing directly to do with this IPTV show, but I watch it and feel that not
enough people know about the show. Shouts to Linlin, keep the show going. |
| 11/09/2006 |
Today With A Techie 178: Model M
Keyboard Lovefest |
| 11/06/2006 |
I just released a new article:
Dual Booting Slax Linux and BartPE (Windows) from a USB Thumbdrive (UFD)
Enjoy. |
| 10/25/2006 |
Hackers On
Hackers Crow: A little "fan" commentary of the movie Hackers. Hack the
Planet. |
| 10/25/2006 |
HackLouisville's Newest release:
How Not
To Brew Beer with Hagbot |
| 10/25/2006 |
I've added a few links to Slimjim100's sites:
http://www.anti-hacker.info
http://www.middlegeorgia.org He's
also part or the Plain-text.info project. |
| 10/17/2006 |
New Video:
Creating a Windows Live CD for System Recovery and Pen-Testing with Bart's PE
Builder
I'm doing this presentation live at
PhreakNIC X. |
| 10/16/2006 |
Two quick things, My Today With A Techie on
using a cheap GPS for wardriving
came out today. Also, Yugal.ras sent me a video he wanted me to host
on Alternative Data Streams in NTFS, it can be found at the bottom of my "Videos
By Others" page. I have a text article called "Practical
Guide to Alternative Data Streams in NTFS" on much the same subject. |
| 10/07/2006 |
Updates to
Wall Of Social Science Majors and other stuff
Sorry it's been awhile since my last post, I've been busy studying for school
and getting a presentation together for
PhreakNIC. I've updated my Wall Of Social Science Majors site with some pics
taken by UNHOLY at
Notacon 3. I plan to put out a new video
soon, most likely on Bart's Pe Builder which is what my PhreakNIC presentation
is on. Also, you may have noticed a new "Printable version" link on the bottom
of some pages, this should make printed versions of my articles more readable.
Enjoy. |
| 09/25/2006 |
Updated Cain 2.9
Plugin for Bart's Pe Builder.
Added support for RunScanner, but it's very experimental. If you get a
chance, check out my presentation at
PhreakNIC in about a month. |
| 09/20/2006 |
Review of the
UT-41 GPS, and a little about getting it to work with Kismet in BackTrack Linux |
| 09/16/2006 |
Added DefCon 502 and
Ubermafia to the
Hoosier Hackers
section. Both are out of Louisville Kentucky (Across the river from me here in
Indiana). |
| 09/15/2006 |
Today With A Techie 151: Skiddy
Baiting, the audio version of the article I put out a few weeks ago. Hope
you enjoy it. Also, here is a quick video of my
iGlock, a lovely point and click interface. By the way, I'd like to make a
quick plug for PhreakNIC, hope to see
some of you at the con this year. |
| 09/12/2006 |
New video: Making Windows
Trojans with EXE Binders (AKA:Joiners), Splice and IExpress |
| 09/05/2006 |
A Collection Of Hacking Videos By
Others
Some of the sites that originally hosted them are gone. I'm just putting these
up so they are not lost forever. |
| 09/03/2006 |
New video: Hosts File and Ad
Blocking
Pretty general knowledge, but it may be of use to some. |
| 08/27/2006 |
New article: The Joys of Skiddy
Baiting
Messing with those as they try to mess with you. |
| 08/16/2006 |
New Video: Passive OS
Fingerprinting With P0f And Ettercap |
| 08/15/2006 |
Today With A Techie Episode 136:
This time around I cover some basic Denial of Service techniques. |
| 08/15/2006 |
New Hacker Media: The updated Hacker Media
site has been launched by Infonomicon. Now it uses RSS feeds for most of its
content so it's self updating. Mater of fact, this should show up on the page
because it pulls from my RSS feed as well. |
| 08/03/2006 |
PhreakNIC X: You may have noticed the new
banner. PhreakNIC X is coming up, October 20-22, 2006 in Nashville, TN. I had a
great time last year and I'm giving a presentation this year on Bart's PE
Builder. My buddies from HackLouisville and Infonomicon are coming as well.
Check out the schedule,
my friends Kn1ghtl0rd and Lowtek Mystik will also be giving a presentation on
RFID. If you want to see videos from last year's event visit
http://phreaknic.wilpig.org/ . Hope
to see you there. |
| 08/02/2006 |
New video: Cracking MD5
Password Hashes
A little about cracking MD5 password hashes. In this tutorial we take the hashes
from a phpbb2 database and crack them using online tools and Cain. |
| 07/31/2006 |
New video: Setting
Firefox's User Agent To Googlebot so you can access sites that allow
indexing by Google but require you to subscribe to view the content. |
| 07/30/2006 |
Ok, even more site changes are in effect. If you have comments leave them in the
forums. Yeah, I know there are a
lot of ads, I'm a whore what can I say. I push about 5 to 10 gigs per day and
may have to switch to a co-located box, so money helps. I enjoy creating
free security articles and videos, it would be great if I could do it full time. |
| 07/29/2006 |
Two quick updates. First, I've put up a forum at
http://irongeek.com/forum/index.php so I can show how to crack md5 hashes
and why it's a bad idea to use the same password everyplace. Please feel free to
sign up, but keep in mind I may use you as a test example for password cracking.
:) Also, for those interested in DoSing my site or trying exploits on it, please
feel free to attack the host name hackme.irongeek.com
. Enjoy. |
| 07/24/2006 |
Posted a new article: Cracking
Windows Vista Beta 2 Local Passwords (SAM and SYSKEY) |
| 07/19/2006 |
Posted a new video: Using TrueCrypt
With NTFS Alternate Data Streams. |
| 07/11/2006 |
Today With A Techie released the audio version of my Bluecasing Article today:
Bluecasing: War Nibbling, Bluetooth and Petty Theft
Enjoy. Also, they need more contributors, so make a show and send it in. |
| 06/26/2006 |
Just updated the
Keymail Key Logger source code. Thanks to TheVoidedLine for his
contribution. |
| 06/19/2006 |
Just posted an Intro To
TrueCrypt video. TrueCrypt is a useful encryption package with a lot of
features, check it out if you want to keep your data private. |
| 06/15/2006 |
I've updated the Wigle Data to
Google Earth script, and posted a KMZ file for the WiFi access points in the
Louisville Kentucky area. Happy Wardriving. |
| 06/12/2006 |
I put out a new article:
Bluecasing: War Nibbling, Bluetooth and Petty Theft |
| 06/10/2006 |
Hack Louisville: We are trying to get a bunch of local techies united in
the Louisville Kentucky area. To aid in that my buddy Cory put up the forum at
http://www.HackLouisville.com . If
you are a Louisville area geek that has an interest in hacking, security,
coding, electronics or related topics please stop by and join up. Besides our
own meetings we will be posting about local area events that may be of interest
to computer geeks, and it should serve as a great forum for getting local help
with tech issues. |
| 06/06/2006 |
I added an Apps/Scripts section to the
links in the header to make some of my coding projects easier to find. Also, I
fixed a mistake I made in Williamc and Twinvega's last video (I put some
sections out of order). |
| 06/05/2006 |
Intro To DD and Autopsy By Williamc and
Twinvega
Thanks to Williamc and Twinvega for submitting another video. |
| 05/25/2006 |
Intro To Bluesnarfing By Williamc and
Twinvega
Thanks to Williamc and Twinvega for submitting this cool Bluesnarfing (serepticiously
grabbing data off of Bluetooth devices) video for me to host. |
| 05/23/2006 |
Today With A Techie needs your help!
Since its a community based podcast it relies on user submissions for new
episodes. Feel like doing your own one-off podcast on a tech subject? Contact
P0rtrill0 or use
the submit form. |
| 05/22/2006 |
The Infonomicon crew and I were on TV in Canada. Droops had filmed a segment on
hacking an Airsoft gun to rapid fire for Hack
TV Underground Episode 1. Canada's G4TechTV broadcast the episode on their
show Torrent
which collect video podcasts from the Internet. Check out the
6th episode of Torrent. Pretty cool. |
| 05/11/2006 |
Riscphree and I came up with a Tri-fold
pamphlet to hand out at hacker and security conferences. We first released it at
Notacon 2006. Feel free to use it at your con as long as you don't change the
credit information. Download the
Hacker Con Wi-Fi
Hijinx PDF here. |
| 05/05/2006 |
I did an episode of Today With A Techie
recently, go check out episode 106
on the site. This time it was on
Alternative Data
Streams. |
| 05/05/2006 |
Added a link to the Kentuckiana
Chapter of the ISSA to the Hoosier Hackers page |
| 04/13/2006 |
I found out about Fiebig's show while up at Notacon 3. Basically, M0diphyd is about taking
old techno junk and turning it into cool projects and gadgets. In episode 1 the
projects are: Computer turntable, DeLorme Tripmate GPS review, Coilgun, and the
Overhead Laptop.
Check it out: M0diphyd
Enjoy. Fiebig said more episodes will be out soon. |
| 04/10/2006 |
I've put up the video from my presentation at Notacon 2006 on
Network Printer Hacking
and have also updated the associated text article. |
| 04/10/2006 |
We noticed a flaw in the Wall of Shame
code as it deals with refreshing. It should be fixed now. |
| 04/02/2006 |
Major updates to the Printer
Hacking article in prep for Notacon. |
| 03/26/2006 |
Puzzlepants created a great article on taking CacheDump hashes and putting them
into Cain. I've tacked his article on the end of my
Cracking Cached Domain/Active Directory
Passwords on Windows XP/2000/2003. |
| 03/25/2006 |
IPIterator: A quick little
multithreaded program for Linux and Windows to quickly iterate through a set of
IPs and execute a command. Source code is included. |
| 03/13/2006 |
Julien Goodwin made my Wall of Social Science Majors
prettier and added some functionality. |
| 03/10/2006 |
The videos are back up. Seems my Wall of Social Science Majors
was posted on http://hackaday.com which may
have causes some of the problems. The folks at DreamHost said it was not the
bandwidth but the number of connections (which is somewhat disingenuous since to
suck up the 1TB pf bandwidth the number of connections is likely to be high). I
took some measures to keep the connections down. If anyone else wants to mirror
the videos let me know. |
| 03/09/2006 |
The videos will be down for just a bit. I got this email from my hosting
provider: Hello,
Unfortunately, I was forced to temporarily disable your irongeek.com/videos
folder by renaming it to videos_disabledByDH. The connections to the files
inside were monopolizing the apache webservice, and other sites couldn't be
loaded.
Please don't re-enable it until you make check your code and restrict the
connections to your files.
Sorry about having to go this route, but we can't have this happen on our shared
machines. Please note, that repeated temporary disablement may result in
disabling your domain and your account, for violating our Terms of Service (dreamhost.com/tos.html).
Let us know if you have any questions.
Thanks!
Andrea
I'm paying for 1TB per-month transfer so I don't know what's up as I'm not
hitting that limit. I'm waiting to hear back from them. |
| 03/08/2006 |
New live action video: Irongeek's Guide to
Buying a Used Laptop |
| 03/03/2006 |
At the request of Riverside (the DefCON goon that runs the Wall of Sheep) I've
changed my projects name to Irongeek's
Wall of Social Science Majors. |
| 03/01/2006 |
Irongeek's Wall of Shame/Wall
of Sheep Code You know those plain-text password walls at DefCON and
PhreakNIC? Make your own. |
| 02/21/2006 |
New Video: Cracking Windows
Passwords with BackTrack and the Online Rainbow Tables at Plain-Text.info
Title says it all. |
| 02/18/2006 |
Irongeek.com reader Tony submitted the following that might be of interest to some
other readers: Tony's Ethernet Tap
If anyone else feels like submitting anything send it on in. |
| 02/17/2006 |
I switched hosting providers to DreamHost because ChaosNetworks are cum belching
felch monkeys. Read my
ChaosNetworks Review . If you can read this you are already using my new
host. Let me know if anything is missing from the site, or if you want discount
codes for DreamHost. |
| 02/15/2006 |
New article: Caffeinated Computer
Crackers: Coffee and Confidential Computer Communications |
| 02/08/2006 |
Indiana Higher Education Cybersecurity
Summit 2006
March 30-31, 2006
For those in the Indianapolis area, some of you may be interested in
this. Granted, most of it will be "Awareness" fluff, but the practitioners
sessions from last year were ok and it gives you a chance to network a bit (in
both meanings of the word). Last year I gave a talk on local password cracking,
don't know about this year but since they have not contacted me and I'd only get
20mins I'd doubt it. If you plan to show give me a yell and can will meet up and
talk shop. |
| 02/07/2006 |
Adding Modules to a Slax or Backtrack Live CD
from Windows
In this video I show how to add patches and extra modules to the Back|track
pen-testing Live CD using MySlax. By the way, I'm planning on switching to a new
hosting provider soon so hopefully I'll stop having bandwidth problems. |
| 01/30/2006 |
Anonym.OS: LiveCD with build in
Tor Onion routing and Privoxy
Just showing off this cool live CD recently released at ShmooCon 2006. Great for
surfing anonymously. |
| 01/28/2006 |
Added a section to my Hacking Network Printers page with details from Mr. Hinton
on how to
fix an HP 4100 MFP with a busted hard drive using Ghost. |
| 01/26/2006 |
New video that continues the last one:
Make your own VMs with hard drive for
free: VMware Player + VMX Builder
By the way, Irongeek.com has been up for almost 2 years, yippy!!! |
| 01/20/2006 |
Using VMware Player to
run Live CDs (Bootable ISOs)
In this video I show how to use the free VMware Player to run Live CDs like
Knoppix, Auditor or Bart's PE Builder from an ISO. |
| 01/20/2006 |
TWAT Episode 64
This one is on using the Cygwin environment in Windows to compile exploits meant
for *nix Systems. |
| 01/13/2006 |
Notacon
Looks like a bunch of my cohorts from Infonomicon and I will be giving talks at
Notacon in Cleveland, Ohio April 7th-9th. Check out the
speakers list. Mine will be
on
Hacking Network Printers. Should be a lot of BinRev folks there as well.
Should be a fun time. |
| 01/11/2006 |
SSH
Dynamic Port Forwarding
I set up a quick video tutorial to show how to set up an encrypted tunnel using
SSH's dynamic port forwarding (sort of a poor man's VPN) in both Linux and
Windows. The tools used are OpenSSH, PuTTY and Firefox, but it should be enough
info to allow you to figure out how to set up other clients. |
| 01/03/2006 |
Counter WMF
Exploit with the WMF Exploit
I used H D Moore's "Windows XP/2003/Vista Metafile Escape() SetAbortProc Code
Execution" revision 1.12 Metasploit module to create a WMF file that
automatically runs "regsvr32 -u shimgvw.dll" to counter the exploit. Clicking
the link may run code on your computer or crash your browser if you are using IE
so click with caution. More of a fun experiment than anything. |
| 01/02/2006 |
WMF File Code Execution Vulnerability
With Metasploit
This video covers the use of the recent (Jan 2006) WMF file code execution
vulnerability with Metasploit. It shows how to shovel a shell back to the
attacker with the WMF vulnerability. See
Microsoft Security Advisory 912840. Thanks to kn1ghtl0rd, AcidTonic,
Electroman and livinded for their help. |
| 12-20-2005 |
Keymail the KeyLogger:
An E-mailing Key Logger for Windows with C Source. |
| 12-20-2005 |
T.W.A.T Radio Episode 43 hosted by Irongeek
SAM file love. |
| 12-15-2005 |
Using VirtualDub and a cheap
webcam as a camcorder
I thought this might be of use to those that would like to submit something to
Infonomicon TV or
Hack TV but lack the cash for a
proper MiniDV camcorder. |
| 12-13-2005 |
T.W.A.T Radio Episode 39 hosted by Irongeek
This one is on changing your MAC address.12 |
| 11-16-2005 |
Firewalls with Sarah: Campus
Computer Security Series Episode 2
What the hell, I'll put both up today. |
| 11-16-2005 |
Updates and Patches with Anna: Campus
Computer Security Series Episode 1
I decide to lend my expertise to some young ladies at my campus and make some
videos. This first one is on using Windows and Mac OS X's updating features.
Granted, it's not as technical as most of the stuff on my site, but it seems
quite a few of you work in higher education IT departments and these video might
be useful to raise awareness in your campuses student population. Also, I think
you would rather look at these ladies than me. Enjoy. |
| 11-16-2005 |
I've been having a lot of car and plumbing problems recently, that's why I've
not posted in awhile. Don't worry, I've got new stuff coming soon. |
| 11-01-2005 |
I updated my
Zaurus Dsniff instructions for OZ 3.5.3. |
| 10-26-2005 |
T.W.A.T Radio Episode 27 Hosted by Irongeek
Securing your box for a hacker con. (Unsecure network) Mostly on SSH Dynamic
port forwarding in Linux and Windows.
download here:
http://twatech.org/eps/twat027.mp3
Show notes here: http://twatech.org/ |
| 10-25-2005 |
I've added my PhreakNIC 9 Photos. |
| 10-19-2005 |
I blew up my Zaurus 5500 last night, so don't expect me to update my Zaurus
section for awhile. Before it died, I did get the latest version of Dsniff to
work and maybe Ettercap (I fried it while I was testing). I think I hooked power
up to it backwards, be careful with those universal power supplies kiddies!
Anyone know where I can get a good deal on a Zaurus clamshell model? |
| 10-18-2005 |
This is a little Droop/Irongeek collaboration.
Infonomicon
TV Ep 7: HP printer hacking, building an old school phone handset for your
cell phone, collecting data in RF monitor mode and making cat5 cables. |
| 10-17-2005 |
Hope to see you all at PhreakNIC 9,
Oct 21-23. |
| 10-17-2005 |
Updated Zaurus
Nmap instructions to 3.93-1. |
| 10-12-2005 |
Metasploit Flash Tutorial: I created a new video that covers the use of Metasploit,
launched from the Auditor Boot CD, to compromise an unpatched Windows XP box by
using the RPC DCOM (MS03-026) vulnerability. It then sends back a VNC session to
the attacker. This is just one example of the many things Metasploit can do.
Check it out. |
| 10-06-2005 |
I just posted Nmap Video Tutorial 2: Port Scan Boogaloo.
This video covers some intermediate and advanced Nmap options and is a follow-up to my "Basic Nmap Usage" presentation.
|
| 10-03-2005 |
Network Sniffers Audio Presentation: I did an audio presentation on the basics
of how sniffers (network analyzers) work for "Today with a Techie."
Go to their download page and grab
episode 10. |
| 09-26-2005 |
I added a link with information about Contacting
Me. |
| 09-24-2005 |
I'm in the process of switching hosting providers so that I will have more
monthly transfer bandwidth. If you see this message you are on the new host. |
| 09-13-2005 |
Added "Coding
your own scripts with Perl and PJL" section to the Hacking Network
Printers article. |
| 09-11-2005 |
Posted my article on
Hacking Network Printers (Mostly HP JetDirects, but a little info on the
Ricoh Savins). |
| 09-02-2005 |
Posted my article and video on
Finding Rogue SMB File Shares On Your Network. |
| 08-25-2005 |
NeuTron sent me a version of
John compiled with Cygwin that
includes the MSCACHE patches. I updated my
Cracking
Cached Domain/Active Directory Passwords on Windows XP/2000/2003 page to
link to his version of John. |
| 08-22-2005 |
After attending Gencon 2005 I decide to start a ribbon awareness campaign for
Con Funk. I present to you
Ribbonthulhu. |
| 08-16-2005 |
I updated the Zaurus section of my site to show how to install
Nmap 3.81-2 and
Kismet 2005-06-R1 under OpenZaurus 3.5.3. |
| 08-15-2005 |
At Bruce Nelson's request I'm updating parts of the Zaurus section. I just added
details on installing
Wellenreiter_1.2.0-r1 with OZ 3.5.3. |
| 08-15-2005 |
Minion from the BinRev forums has been kind enough to host my videos. Thanks. |
| 08-11-2005 |
Information security in campus and
open environments: I wrote this article a few months back for [IN]Secure
magazine, but this time the article has detailed footnotes and links to the
tools mentioned. It covers the basics of information security in
environments like universities, schools and libraries. While it's meant to
help organizations figure out how to lock down their computer systems it
reads sort of like a "How to hack schools" booklet. I plan to expand
the article as time goes by, let me know of additions I should make. |
| 08-09-2005 |
Need another video host: Droops has been kind
enough to let me use his bandwidth for a few months now, but it's getting to
the point where my videos are sucking up too much of his bandwidth. I'm
looking for a new place to host the videos. Ideas? I'm more than willing to
let the host put a small ad at the bottom of each video page. I think it's
too the point where the videos are taking a few 100 gigs of transfer per
month (not sure of the exacts, but Droops will let me know soon). Thanks to
Droop for letting me host my videos for so long on his dime. |
| 08-08-2005 |
Put up the new mascot that BushiBytes made for me. |
| 08-02-2005 |
Added a new video: WiGLE, JiGLE and Google
Earth: Mapping out your wardrive. |
| 08-01-2005 |
I updated my My
Wigle-to-Google-Earth script to better handle characters that confuse
the XML. |
| 08-01-2005 |
On 07-27-2005 I over ran by monthly bandwidth allotment (40GB on Irongeek.com,
glad Droops helps with hosting the videos or I would be over every month).
By the time you can read this the site should be back up. |
| 07-26-2005 |
I wrote a PHP script to take WiGLE data and turn it into a KML file that can
be imported into Google Earth. My
Wigle-to-Google-Earth script is great for making pretty maps of WIFi Access Points, check it out. |
| 07-17-2005 |
New video: Droop's Box: Simple Pen-test
Using Nmap, Nikto, Bugtraq, Nslookup and Other Tools |
| 07-14-2005 |
Quick Tour of Irongeek's Office
and Security Lab As filmed with my crappy digital camera. |
| 07-06-2005 |
Added my new article:
LAN of
the Dead: Putting computer zombies back in their grave, Ash style. |
| 06-20-2005 |
I've update the Kismet section of my Zaurus page with information from Jake,
and the Zethereal section with info from M Delroy. |
| 06-16-2005 |
New Flash Video: Fun
with Ettercap Filters: The Movie The Flash version of my Ettercap
Filters tutorial. Like Airpwn, but easier. |
| 06-16-2005 |
(IN)Secure Magazine published my article "Information security in campus and
open environments". A pdf of it can be found at:
http://www.insecuremagazine.com/INSECURE-Mag-2.pdf
Looks like they took out the link section, but oh well. |
| 06-15-2005 |
Added the Flash video
MAC Bridging with Windows XP and
Sniffing (very useful with my Cain/VoIP tutorial). |
| 06-13-2005 |
I put up a new tutorial called
Fun with Ettercap Filters that shows you how to make a filter that does
much the same thing as the Airpwn application. What it does is filter web
traffic though itself using ARP poisoning, then modifies the traffic to
replace images in web pages with an arbitrary image that we select. Cool
stuff. |
| 06-07-2005 |
Folks ask me from time to time how I make my Hacking Illustrated videos so here is a short page
to give you the lowdown: How I
Make The Hacking Illustrated Videos |
| 05-26-2005 |
Added the Flash video
Sniffing VoIP Using Cain. |
| 05-25-2005 |
Added the Flash video
Installing Knoppix 3.8 to Your Hard Drive.
Hope it's useful to some of you. |
| 05-24-2005 |
Added the Flash video
A Quick and Dirty
Intro to Nessus
to the Hacking Illustrated section. It shows the basics of using the Nessus
Vulnerability Scanner from the Auditor Boot CD. |
| 05-13-2005 |
Added the
Hoosier Hackers
section for those looking for other computer geeks in Indiana or the
Louisville Kentucky area. |
| 05-09-2005 |
Douglas Steele wrote in to point out some typos and some update links in the
Zaurus
tools section. |
| 05-06-2005 |
I decided to put up a review of
Legend Micro. |
| 05-05-2005 |
Laptop Backpack Woes: I loved by buddy's Targus TSB215
and wanted a similar backpack for myself. I did some searching and found out
that the TSB212 was almost the same pack, and I compared it on Targus' site
(http://www.targus.com/us/product_details.asp?sku=TSB212) and Amazon (http://www.amazon.com/exec/obidos/tg/detail/-/B00005T3H5/102-5486756-5720110?v=glance
). When I did a Froogle search I found the cheapest price at Legend Micro (http://www.legendmicro.com/store/more_info.asp?product_ID=3059) but there was
only a thumbnail of the backpack there. I figured it's the same part number so
I ordered it. Well, what I got is labeled on the inside tag as a TSB212, but
it's not the same as what's on Targus' site. Maybe they changed something
about the model at some point and Legend Micro only has the old version. Next
time I think I'll spend the extra $10 and go to Amazon. I did not care much
for the attitude I got while I was on the phone with them about it so I
figured I'd write this review. While I guess I technically got what I ordered,
I'm not happy with it. |
| 05-03-2005 |
Posted a page for my network sniffing screensaver:
PacketFountain. |
| 05-03-2005 |
As posted in the
Anti-online Newsletter 13, here is my article on
Pen-testing Tools for the Pocket PC. |
| 05-02-2005 |
My
Local Password Cracking Presentation
last Friday seemed to go over will, feel free to mirror it now. Also, since
Droops has been kind enough to let me use some of his bandwidth I've posted
more links to his site:
http://www.infonomicon.org/ . News you need, like it or not. Give him a
visit and listen to his cool show. |
| 04-27-2005 |
I did a few more fixes in my
Local Password Cracking Presentation for the
Indiana Higher Education
Cybersecurity Summit 2005. Wish me luck. |
| 04-25-2005 |
Thanks to Droops from
http://www.infonomicon.org/ for the mirror. Hopefully it will keep
me up and running. |
| 04-25-2005 |
I've update many things in my
Local Password Cracking Presentation,
including adding a section on MSCache cracking with Cain v2.68 that was
released on Friday (April 22nd). I'm also starting to use a mirror site more
because I'm running out of bandwidth. |
| 04-20-2005 |
I've put up the Flash version of my
Local Password Cracking Presentation for the
Indiana Higher Education
Cybersecurity Summit 2005 . It covers cracking the SAM/Syskey, Cached
ADS/Domain Credentials, VNC stored passwords and Windows Protected Storage. Don't mirror it
anywhere yet as I may change it some before I present it live on the 29th. If
you have any feedback you would like to give me before the 29th email me. |
| 04-13-2005 |
Sorry it's be awhile since I posted new material. I've be
writing an article for the next
Antionline newsletter and preparing a presentation for the
Indiana Higher Education
Cybersecurity Summit (I hope to have a Flash version of the presentation
up on this site). More stuff will be coming shortly. |
| 04-04-2005 |
Nfotx was kind enough to let me host some of my files at his
site. The Nmap video was chewing up some serious bandwidth. |
| 03-31-2005 |
My Basic Nmap Usage
video tutorial is up. Let me know what you think. I'm having some problems
with file size to memory foot print so if there are any good Flash MX
developers out there please contact me. |
| 03-29-2005 |
I've moved the
Hacking Illustrated videos to their own page. Soon I will be releasing
my Nmap video so stay tuned. |
| 03-29-2005 |
I guest hosted an
episode of Infonomicon (Episode 32). You can get it from
http://www.infonomicon.org/episodes.html
I need to learn to speak slower, enunciate and take less caffeine before
talking on the radio. |
| 03-25-2005 |
Posted
Auditor security collection boot CD
notes compiled by Douglas Lancaster. Thanks Doug. |
| 03-24-2005 |
Added the
Newscat section. It's a PHP
script that shows my favorite RSS feeds. |
| 03-24-2005 |
I now have an RSS Feed, feel to use it. I'll be posting all of my news/articles/videos to it for other sites to link to. |
| 03-22-2005 |
Added a new Hacking
Illustrated Video: Cracking Syskey
and the SAM on Windows Using Samdump2 and John based on the article I
wrote below. |
| 03-21-2005 |
Added
Cracking Syskey and the SAM on
Windows XP, 2000 and NT 4 using Open Source Tools to the security section.
It's a continuation of an older
article of mine. |
| 03-19-2005: |
Changed some of the
menu and header system so that web pages like the
Zaurus
Security Tools section would render better in more browsers. I also
changed some of the layout on that page to get rid of white space. Soon as I
get my 256MB CF card I'll be updating more of the Zaurus instructions. |
| 03-18-2005: |
Added the "Your IP" webpage to the menu on the left. It also returns what information it can from Javascript. I changed the intro text
as well. |
| 03-18-2005: |
Added some Kanoodle ads to help pay the bills. Let me know if the placement is annoying. |
| 03-16-2005: |
Added some more links to the bottom of the Links page. I also added a small addition to the footer. |
| 03-10-2005: |
I changed the last sentence of the first paragraph of Cracking Cached Domain/Active Directory Passwords on Windows XP/2000/2003 to be more accurate about how LM Hashes work. |
| 03-08-2005: |
Posted the tutorial Cracking Cached Domain/Active Directory Passwords on Windows XP/2000/2003. |
| 02-18-2005: |
Posted my Using Bart's PE Builder to Make an Anti-Spyware and Rescue CD tutorial. |
| 02-16-2005: |
I added my MSConfig plugin to the PE Builder plugins page. |
| 02-15-2005: |
I added my HiJackThis plugin to the PE Builder plugins page. |
| 02-15-2005: |
Changed my PE Builder plugins page to just have plugins I've contributed to. I also added my plugin for Softperfect's Netscan. |
| 02-01-2005: |
I posted up the article I wrote for the IOLUG: A Quick Intro to Sniffers |
| 02-01-2005: |
Updated the Bart's PE Builder page with a newer version of Registry Editor PE. |
01-10-2005: Sorry it's been awhile since I put up any new content.
I've been moving to a new office. I'll try to get back to this site soon.
11-19-2004: Added a PHP script I wrote to grab a list of Zombie film
rankings from IMDB. It may take a bit of time to load, see it here:
Irongeek's Zombie Film Ranking Using IMDB
10-06-2004: I just found out about how to use ipkg-link so I updated the
General OS Info, Nmap and Nemesis sections on the Zaurus pages.
It should make my tutorials easier to follow. Soon I'll put up instructions for
Wellenreiter.
09-30-2004: Added links to a bunch of Hacker video and audio e-zines to
the bottom of my Links page.
08-20-2004: Kevin Milne has written a book about a hacker who creates the
magic bullet and uses it on the Zaurus.
Z4CK (Zaurus ACK)
should be coming out in late September, surf to
www.z4ck.org if you want to download the first half for free.
4-13-2004: Change Southern Indiana Deviant Computing Meetings page to reflect
modified date.
3-24-2004: Added "Random out of context RPG Quote" to the bottom of the page.
3-22-2004: I got a battery extender for my Zaurus and will be posting a review
soon (hope it significantly increases the time I can spend wardriving with the
Z). I also ordered some NiMh batteries for it but someone took them out of the
package before it got to me, I wrote the company I ordered them from and if I
don't get them soon I'll let you all know to never order from them. I also have
a "Change your MAC address" article and more on workouts coming soon.
3-19-2004: Added PayPal donation button.
3-16-2004: ReadySetConnect finally got it set up so I can use SFTP and
SSL so I don't have to pass my password in plain text across the Internet Yippy!
3-16-2004: Added Daren's 2nd rant under humor.
3-15-2004: I did some massive directory rearranging to make the site
easier to maintain. Please let me know about broken links.
3-12-2004: Added Links section and straightened out HTML tables so things
would display better.
3-11-2004: I've been getting a large increase in traffic since Fyodor sent his e-mail on the 9th (see
here). Anyone know a good, noninvasive ad service I can use to offset the
cost of bandwidth?
03-10-2004: I got an E-mail from Fyodor, the main guy in charge of Nmap.
He sent a link to my website out to the 17000 people on his mailing list and my
site may get mentioned in a book he is writing. Kick Ass!!! Here is a link to
what he sent to his mailing list:
http://seclists.org/lists/nmap-hackers/2004/Jan-Mar/0003.html
03-10-2004: Jeff Nathan of the Nemesis project asked for me to change the link
on my Zaurus Nemesis how-to to
http://nemesis.sourceforge.net
03-07-2004: Looks like someone using an anonymous proxy at 200.252.72.9
is trying to crack the box my site runs on, it looks like they were trying to
get the passwd file and maybe try a buffer overflow. So far it would appear that
they have had no luck :)
03-05-2004: Updated Wellenreiter II entry with info from Mark Lachniet.
02-28-2004: Fixed some broken links in security section.
02-23-2004: Added Daren's first rant under humor.
02-09-2004: Updated the supplement section with reviews of new bars and a
little info about Ephedra. I'm trying to get my
buddy Jaden to write a few things for this section.
02-06-2004: Updated Ettercap entry an made the page look better in IE. Still
looks best in Mozilla.
02-05-2004: Fixing some link problems, email me if you find any.
02-04-2004: Moved to ReadySetConnect.com.
02-02-2004: Ok, I just combined all of the Irongeek pages, please email me
if there are any broken links.
01-31-2004: New instructions on how to get nmap 3.50-1 working.
01-30-2004: I just bought a domain name, more to come soon.
01-29-2004: Added TCPDump to Sniffers.
01-29-2004: I'm getting hit a lot. Thanks to everyone who linked to me. Hope the T3 line can take it.
Keep checking back, I plan to keep updating at least once per week.
01-29-2004: Big change to page layout, let me know if you like it better or not.
01-28-2004: Just got my 10/100 Ethernet card and it seems to work fine.
01-28-2004: Another small change to Zethereal instructions (in case of IPK install problems)
01-27-2004: small change to ettercap instructions and a few other minor changes.
01-27-2004: Working on my own IPK (irongeek-pentest-dist) with all the security tools in one big package.
01-27-2004: Changed Zethereal entry to make it easier.







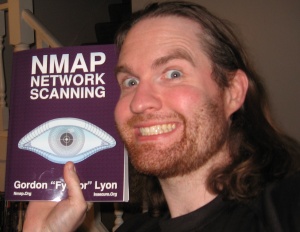
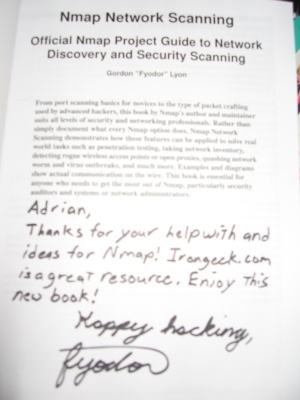


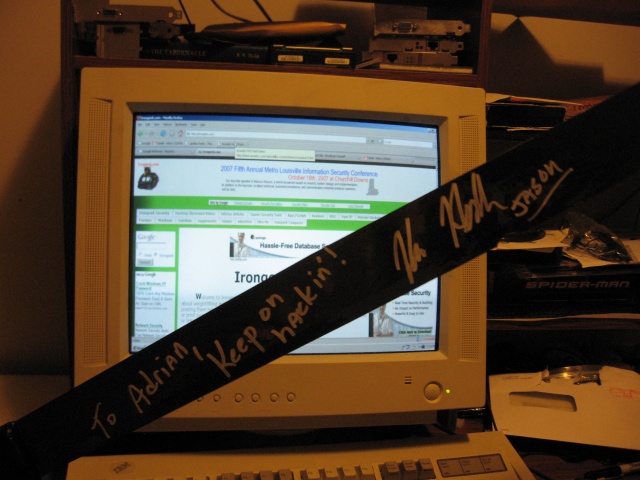

 Printable version of this article
Printable version of this article