Bluecasing: War Nibbling, Bluetooth and
Petty Theft 
Bluecasing* is the act of finding
devices to intrude or steal via Bluetooth (general scanning is sometimes know as
War Nibbling). For those who do not know, Bluetooth
is a wireless networking technology that is geared more towards PANs (Personal
Area Networks), while Wi-Fi (802.11a/b/g etc) is geared more towards LANs. An
over simplified way to look at it is that Bluetooth is meant to be a wireless
replacement for some of the functions USB fulfills, and Wi-Fi is more of a wireless
replacement for Ethernet. Many high-end phones, laptops, PDAs, car stereos and
other electronics are being shipped with Bluetooth capability so they can
communicate, either by sending audio or digital data to each other. For
example, your PDA tells your phone to dial a number and send the output to your
headset or car stereo. For more details on Bluetooth technology and its uses read the
following Wikipedia entry:
http://en.wikipedia.org/wiki/Bluetooth
You could see Bluecasing as being sort of like Wardriving, except
you are looking for Bluetooth devices instead of 802.11a/b/g/n access points. For
an example of thieves using Bluetooth signals to locate things to steal, read:
http://www.cambridge-news.co.uk/news/region_wide/2005/
08/17/06967453-8002-45f8-b520-66b9bed6f29f.lpf
This article is not intended to help
people learn to steal expensive toys, but to cover the basics of how Bluetooth
devices find one another. Bluecasing/War Nibbling does not
have to be for larceny. Someone could merely be curious what devices are
out there or they may be planning to test for known exploits to retrieve personal
information from the devices (Bluesnarfing). For more in depth technical information read Ollie
Whitehouse's article "War Nibbling: Bluetooth Insecurity" linked at the bottom
of this article. What follows is a brief synopsis of how Bluecasing is done, what
tools are used and what things can be done to make it harder for thieves to find
Bluetooth Devices.
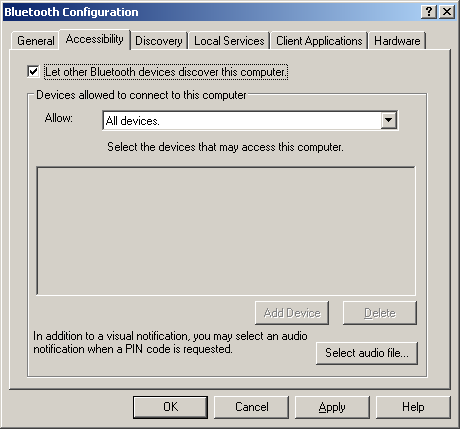
Most Bluetooth stacks for Windows (Microsoft's, Widcomm) and Linux
(Bluez) will support some
kind of discovery. Here are a few of the user interfaces you might be familiar
with when searching for Bluetooth devices:
Windows:

Windows (Using Widcomm Stack):

Linux (KDE GUI):

Linux Command Line:
| root@slax:~# hciconfig hci0 up root@slax:~# hciconfig hci0: Type: USB BD Address: 00:0A:3A:52:69:8C ACL MTU: 192:8 SCO MTU: 64:8 UP RUNNING PSCAN ISCAN RX bytes:148 acl:0 sco:0 events:17 errors:0 TX bytes:65 acl:0 sco:0 commands:17 errors:0 root@slax:~# root@slax:~# hcitool scan Scanning ... 00:02:72:CA:14:6D TestTop root@slax:~# |
Pocket PC:

For the built-in discovery methods to work "allow discovery" must be enabled.
Windows XP and Vista with the default Microsoft Bluetooth stack have discovery
turned off by default. Other operating systems and Bluetooth stacks will vary. A
lot of cell phones I've run into seem to have discovery on by default, making
them easier to connect to your PAN but also easier to locate. Most devices allow
you to turn off discovery if you wish.


There are also purpose-made tools like BlueScanner or BTScanner for Linux (command line) or Windows XP (GUI). These tools are nice because of the quick access they give you to information such as device type and available services. The MS Windows ones I have tested require you to use Microsoft's Bluetooth stack (NOT Widcomm). All of the Linux tools I've seen need the BlueZ stack. Below are a few screen shots from these software packages.
BTScanner for Linux:


BlueScanner For Windows:

As you have probably guessed, if you don't want your device to be found you will choose to disable "allow discovery", but in versions of Bluetooth before 1.2 (which introduced "anonymity mode" ) it was possible to find cloaked devices by trying to connect to them via their BADDR (a 48 bit which functions more or less like a MAC address does). Ollie Whitehouse wrote a tool called RedFang that will brute-force possible BADDRs and try to connect to them, thus finding them even if they don't reply to a discovery probe. Since then tools like BTScanner for Linux have implemented the same technique (use the b key instead of the i key to start your scan), though I don't think many thieves Bluecasing would use this technique because of the amount of time it takes to iterate through the possible address space. Then again, with multiple dongles and multithreading, the discovery speed could be massively increased. It took a couple of tweaks to get BTScanner to compile on my Linux box so you may just want to use the BackTrack Boot CD. To my knowledge no Windows tools exist that can brute-force the BADDRs, but you can run the BackTrack CD in VMWare Player and use a USB dongle. While BTScanner for Linux is not as pretty as its Windows counterpart it has worked more reliably for me.
Choosing a device
If your laptop already comes with Bluetooth
you will probably just want to use what you have, but if not you need to choose a good
Bluetooth dongle to test Bluecasing with. Bluetooth comes in three power classes:
| Class | Power | Power | Range (approximate) |
| Class 1 | 100 mW | 20 dBm | 100 meters |
| Class 2 | 2.5 mW | 4 dBm | 10 meters |
| Class 3 | 1 mW | 0 dBm | 1 meter |
Obviously, we want to select a device with as much oomph as we can get. I use a
MSI Star Key 2.0 USB Bluetooth 2.0 Transceiver because it's power class 1,
support Bluetooth 2.0, gives you access to the Widcomm Bluetooth stack if you
need it and it runs great under Linux with the BlueZ stack. You may also want to
Google
around for directions on making directional antennas you can solder on to your
Bluetooth dongle, thus increasing it's range.
Keep in mind that just because someone can find a device does not mean they can exploit it, bonding pins and other security features will most likely keep data intruders at bay (if implemented correctly). However, some phones are susceptible to Bluesnarfing attacks (see the video in the links section) and social engineering via Bluejacking.
Special thanks go out to Nick84 at
Rootsecure.net for providing some of the pictures in this article.
Tools and Links
Ollie Whitehouse's article "War Nibbling: Bluetooth Insecurity" kindly
mirrored by RootSecure.net
http://www.rootsecure.net/content/downloads/pdf/atstake_war_nibbling.pdf
Intro To Bluesnarfing By Williamc and Twinvega
http://www.irongeek.com/i.php?page=videos/bluesnarf1
BlueScanner
http://www.bluescanner.org/
BTScanner for Linux (command line) or Windows XP (GUI)
http://www.pentest.co.uk/cgi-bin/viewcat.cgi?cat=downloads
Trifinite, the best site out there for Bluetooth security information
http://trifinite.org/
BlueZ – The official Bluetooth stack for Linux
http://www.bluez.org/
MSI Star Key 2.0 USB Bluetooth 2.0 Transceiver on New Egg
http://www.newegg.com/Product/Product.asp?Item=N82E16833158122
RedFang
http://www.securiteam.com/tools/5JP0I1FAAE.html
BackTrack Boot CD
http://www.remote-exploit.org/index.php/Main_Page
*Bluecasing is a concatenation of Blue (as in Blootooth) and Casing (as in
"Casing the joint"). Yes, it's a term I just made up, but it sure does sound
good does it not?


 Printable version of this article
Printable version of this article